* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Advances in Natural and Applied Sciences
Distributed operating system wikipedia , lookup
Computer network wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Backpressure routing wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Deep packet inspection wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Airborne Networking wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
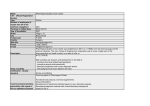
Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 AENSI Journals Advances in Natural and Applied Sciences ISSN:1995-0772 EISSN: 1998-1090 Journal home page: www.aensiweb.com/ANAS Certain Investigations for Improving the Performance by Reducing Overheads during Route Discovery in MANETs 1 1 2 S. Dinakar and 2Dr. J. Shanthini Assistant Professor, Department of Computer Science and Engineering, SNS College of Technology, Coimbatore, TamilNadu, India. Associate Professor, Department of Information Technology, SNS College of Technology, Coimbatore, TamilNadu, India. ARTICLE INFO Article history: Received 12 March 2015 Accepted 28 April 2015 Available online 1 June 2015 Keywords: Mobile Ad Hoc Networks, Link Breakages, Route Discoveries, Overhead, Rebroadcasts. ABSTRACT In mobile ad hoc networks multi-hop routing is performed in order to communicate the packets from the source to destination. The nodes within these networks are dynamic due which a frequent path change occurs which can cause frequent link breakages and route discoveries. These route discoveries can introduce overhead in terms of contention, collision and rebroadcasts which are non-negligible. The main focus of the paper deals with reducing overheads for which a hexagonal based clustering is proposed for avoiding frequent route discoveries and thus maximizing the lifetime of the networks. Eventually it provides additional coverage area and so it reduces end – end delays. © 2015 AENSI Publisher All rights reserved. To Cite This Article: S. Dinakar and Dr. J. Shanthini., Certain Investigations for Improving the Performance by Reducing Overheads during Route Discovery in MANETs. Adv. in Nat. Appl. Sci., 9(7): 57-62, 2015 INTRODUCTION The mobile ad hoc network consists of autonomous nodes communicating among themselves. They do not require any fixed infrastructure since, they are self – configuring networks and does not require any central administrator. Due to the unstable nature of nodes challenges occur during routing a packet from source to destination. As discussed previously the nodes are not stable in nature so the path between the nodes changes from time to time. For initiating a path to transmit data it is essential to identify (or) establish a path for transmission starting from the source to the destination using route discovery process. The mobile ad hoc network makes use of broadcasting for route discovery process. It involves flooding a message from one node to all other nodes within the network. The broadcasting technique forms the fundamental communication technique in MANETs. The process for identifying a route involves transmission of route request (RREQ) packets from source to destination through every outgoing links which is also known as blind flooding. The transmitted RREQ packets are received by all the surrounding nodes which try to find out whether these packets are already contained (or) not. If the packets are not contained already they are to be retransmitted and this is performed till all the nodes have received and transmitted the broadcast packets at least once. The broadcasting can happen through anyone of the below methods. a) Spontaneous: The broadcasting can be performed by a node at any time. Due to this uninformed generation it retards synchronization and no prior information about the connectivity is known. b) Unreliable: The broadcasting employs transmission of messages to all (or) some of the nodes within the network. It does not provide any acknowledgement due to, The host separates itself from the network. It causes repeated transmissions around the sender. Many applications do not need 100% broadcasting techniques. The route discovery process using broadcasting introduces redundant retransmissions while sending route request packet. It due to the fact that the source floods the route request blindly to all nodes when the request are been made without knowing the actual path to the destination. When a node decides to rebroadcast a message to its neighbors where it already holds that message introduces broadcast storm problem. Corresponding Author: S. Dinakar, Assistant Professor, Department of Computer Science and Engineering, SNS College of Technology, Coimbatore, TamilNadu, India. E-mail: [email protected]. 58 S. Dinakar and Dr. J. Shanthini, 2015 Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 2. Related Works: The main aim was to reduce the number of rebroadcasts of the route request packet (RREQ) and to improve the performance during routing. The dynamic nature of nodes in the mobile ad hoc networks (MANET) causes frequent link breakages thus leading to frequent path failures and route discoveries and reduces packet delivery ratio and increases the end – to – end delays. This creates overhead in terms of contention, collision and rebroadcasts during route discovery process which is non negligible. The ultimate aim is to reduce the overhead in route discovery process. The broadcasting technique is used for route discovery during which the mobile node blindly rebroadcasts the first received route request packets without knowing the route to the destination thus causing broadcast storm problem. 2.1 Methodologies Used: The neighbor knowledge based probabilistic rebroadcast protocol was employed in order to reduce the overhead during routing in mobile ad hoc networks (MANETs). The neighbor knowledge protocol is used along with proposed rebroadcast delay and rebroadcast probability which determines the packet forwarding order. a) Rebroadcast Delay: The nodes which have more common neighbor with the previous node will have lower delay. During packet transmission the common node will know this fact first. These rebroadcast delay enables the information, that these nodes have transmitted the packets to more neighbors which forms the key to success. b) Rebroadcast Probability: The scheme considers the uncovered neighbors (UCN). When a node receives a route request packet (RREQ) from its previous node it makes use of the neighbor list in the RREQ packet. This is done to estimate how many neighbors have not been covered by the RREQ packet of the previous node. In that case, the current node rebroadcasts the RREQ packet so that it can reach more additional coverage nodes. For calculating the rebroadcast probability each node needs its 1 hop neighborhood information. The scheme makes use of two factors described below, i) Additional Coverage Area: It is the ratio of the number of nodes that should be covered during a single broadcast to the total number of neighbors, and ii) Connectivity Factor: It represents the relationship between the numbers of neighbor of a given node within the network. 2.2 Routing Protocol: The routing protocols like Ad Hoc On – demand Distance Vector Routing (AODV) and Dynamic Source Routing (DSR) were used since these protocols are on – demand routing protocols. These protocols improve the scalability of MANETs by reducing the routing overheads during new route requests. 3 Statement of Problem: The existing system made use of 1 hop neighborhood information in order to attain additional coverage area. Here, the node verifies the neighbors covered by using the neighbor list maintained at the RREQ packet. In case, if there are any uncovered neighbors the broadcasting is made for attaining additional coverage area. The problem here is that the scheme does not work well in all the situations. This can also minimize the lifetime of the network since the broadcasting to uncovered neighbors can induce additional rebroadcasts thus consuming battery power of the nodes. 4 Proposed System: The main focus is to reduce the overhead caused during route discovery process. The existing makes use of probabilistic scheme which does not work well in all situations. In order to overcome the overhead area based clustering technique is used. In this scheme the receiver should be present at the sender’s transmission range thus increasing the coverage area of the network and extending the network lifetime. The below stated techniques and methods used in area based rebroadcasts (Fig. 3). 4.1 Hexagonal Clustering: The technique (Fig. 1) divides the network into group of nodes which are closely located to each other. Here, the hexagonal clustering is employed since MANET possesses bandwidth constraints. The bandwidth occupied by the entire system is Cb times the bandwidth occupied by a single cell where, Cb represents the bandwidth occupied by every single cell. The cell follows an orthogonal structure since it allows for frequency reuse and a single cell is considered as cluster and any node within the cell is able to communicate with other orthogonal neighbors. Here, the clustering allows the node within one cluster can cover one quarter of the adjacent cluster thus providing additional coverage area. This allows the node to obtain the information about the nodes present inside the adjacent orthogonal clusters. The sensing area of a cluster can be determined using, S min A T / 4 Where, Sa denotes the sensing area of a node into the adjacent cluster. Ac denotes the adjacent clusters. Tr represents the transmission range into the adjacent cluster. The shortest between the nodes a c r 59 S. Dinakar and Dr. J. Shanthini, 2015 Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 present at the boundary of sender transmission range from source is, i S d 1 d Sd Where Sd denotes shortest distance from source S to the distance. Did denotes the shortest distance from neighbor node i to the distance D. id / Sd denotes the clones of next node. Fig. 1: Hexagonal Clustering. Pseudocode for Cluster Formation: begin Generate initial node population Analyze Sa = min(Ac (Tr / 4)) Generate node with performance metrics if i ε Sa i S d 1 d Sd Analyze Assign node i as cluster head within the cell Formulate nc Update the chosen cluster head information into source end if end The clustering technique extends the network lifetime. The technique eliminates the need to assign random timers to reduce rebroadcasts. The technique reduces the overhead caused due to contention, collision and rebroadcasts. 4.2 Cluster Head Selection: After the formation of clusters, each cluster contains a set of independent nodes through which the communication has to progress since the packet should reach the destination. For which each cluster Fig. 2: Cluster Head Formation. chooses a cluster head (CH) (Fig. 2) which acts as a coordinator within that structure and tries to communicate with other cluster heads. The cluster heads (CH) acts as a temporary base station within its cluster and communicates with other clusters. The selected cluster head should possess low mobility and highest energy attribute. By this process the communication between the clusters happen through their respective cluster heads. This results in sending and receiving of data through the cluster heads in order to reach the destination. Each and every cluster head maintains a table into which all the details of neighbor cluster head information are stored. Within every cluster only one node is chosen as head which is present near to the boundary of every cluster and thus it covers one quarter of the adjacent orthogonal cells and this process continues for all the cluster heads and thus provides additional coverage area. The influence of the cluster head into adjacent clusters makes it possible for the cluster to obtain every information about the cluster head present in the adjacent clusters and this information are made during the failure of that cluster head for choosing a new cluster head. 60 S. Dinakar and Dr. J. Shanthini, 2015 Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 Pseudocode for Cluster Head Selection: begin Generate initial node population n clusters ni nodes (i = 1, 2, ….. , n) if ni ε n analyze the performance metrics assign a node as head within the cell else report the cell as worst cell and discard it in communication Keep all the best solutions into the source Rank the solutions and find the best Update the chosen cluster head information into adjacent cells cluster end if end 4.3 Message Acknowledgement: After selection of cluster head as mentioned above the remaining nodes are put in sleep state. Before the actual packet transmission, the source floods a HELLO message which will be received by the cluster head. Those received HELLO message will be forwarded to the adjacent cells cluster head since its information will be contained into the previous cluster head by using which the HELLO message finds a path to reach the destination using the cluster heads. After regular transmission of HELLO messages through the cluster heads the path to the destination is determined. Then the path confirmation is send back to the source node again through all these cluster heads called the acknowledgement. This acknowledgement tries to recover the cluster from flaws in order to transfer the packet from the source to destination. Pseudocode for Message Acknowledgement: begin ni choose ith node as cluster head assign other subset of nodes to sleep state while (path > 0) HELLO message is transferred to all cluster heads Acknowledgment is received else select another head from the table maintained at the source reconstruct connection between the heads to transfer packets end while end Fig. 3: Methodology. 4.4 Reassigning Cluster Head: The nodes within the network dies after its resources are exhausted. The cluster head dies after a certain time or move away from its range due to its mobility after some time. During which another node is to be chosen as head within that structure in order to continue communication. In case if there occurs a flaw within any of the cluster head the acknowledgement will not be received by the other cluster head which retards further communication. During which the cluster head present inside the cell which is adjacent to the flawed cluster sends a message to the source which assigns a new node as cluster head. After which this information will be stored into the adjacent cluster heads table and the communication takes place. 4.5 Routing Protocol: The technique makes use of proactive routing protocol (i.e.) open link state routing protocol (OLSR). These protocols require every node to maintain updated information about the every other node in the network. Here, only the cluster head communicates in order to transfer a packet from source to destination. When a source requests for route, the RREQ packets are flooded into the networks where these routing protocols after entering into a cluster makes use of the cluster head and delivers a HELLO message and upon accepting this 61 S. Dinakar and Dr. J. Shanthini, 2015 Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 message a LIVE message is sent back to the source via the cluster heads and this is performed by all the other cluster heads present inside the clusters. After receiving the updated information from clusters a path is chosen only by considering the cluster heads and thus the other subset of nodes are in sleep state. Here after the communication happens only between cluster heads. The routing algorithm discards all other links and it has a special ability to provide route immediately on demand. 5. Performance Evaluation: The evaluation of performance of the hexagonal clustering was evaluated (table 1) by comparing it with OLSR protocol using NS - 2 Simulator. The data dissemination mechanism in MANETs makes use of broadcasting. Here, the analysis is done for route request in route discovery. For comparing the routing performance of hexagonal clustering, is analyzed for reducing the overhead of RREQ packet during route discovery. The number of cluster heads is randomly chosen based on the CBR connections with a fixed packet rate and the number of nodes is Fig 4.1 MAC Collision Rate Fig. 4.3: End – End Delay set to 30. It is possible to vary the number of nodes form 30 to 250 in a fixed field to evaluate the impact of different node density. Here, the CBR is set to 2 i.e. a source and destination. The performances of routing protocols were evaluated using the following metrics. Figure 4.1 represents the MAC collision rate where the average numbers of packets are dropped as a result of collision occurred at the MAC layer in per second. Figure 4.2 represents the overhead caused due to routing thus representing the ratio of the total packet size of the control packets to the total packet size of data packets delivered to the destinations. Figure 4.3 depicts the packet delivery ratio which is the ratio of the number of data packets successfully received by the CBR destinations to the number of data packets generated by the CBR sources. Figure 4.4 depicts average end – to – end delays which represents the average delay of successfully delivered CBR packets from source to destination node. It comprises of all possible delays from the CBR sources to destinations. Fig. 4 Evaluating the Impact of Different Node Density by Varying the Number of Nodes Fig 4.2 Normalized Overhead Fig. 4.4: Packet Delivery Ratio. 62 S. Dinakar and Dr. J. Shanthini, 2015 Advances in Natural and Applied Sciences, 9(7) June 2015, Pages: 57-62 Table 1: Simulation Parameters. Simulation Parameter Simulator Topology Size Number of Nodes Transmission Range Bandwidth Interface Queue Length Traffic Type Number of CBR Connections Packet Size Packet Rate 6 Conclusion and Future Work: The main focus of the paper is to reduce the overhead caused due to broadcasting during route discovery process. Instead of 1 hop neighborhood information a clustering technique is utilized from which a head is chosen to communicate the packet from source to destination. The communication happen only between the cluster heads which inhibits the rebroadcasts to all other nodes within the clusters since, they are put to sleep to maximize the network lifetime thus increasing end – to – end delivery and packet delivery ratio. The work can be extended by considering the security factors. The networks are vulnerable due to which malicious node can act as trusted node and steal information from the source. Distributed approaches can be employed for electing cluster heads. REFERENCES Anju Gill, Chander Diwaker, Juky 2012, Comparitive Analysis of Routing in MANET’, International Journal of Advanced Research in Computer Science and Software Engineering, 2(7). Badarneh, S., Michel Kadoch, Multicast Routing Protocols in Mobile Ad Hoc Networks: A Comparative Survey and Taxonomy,EURASIP Journal on Wireless Communications and Networking volume, Article ID 764047,42 pages. Bellur, B., R.G. Ogier, F.L. Templin, 2003. Topology broadcast based on reverse-path forwarding routing protocol (tbrpf), in: Internet Draft, draft-ietf-manet-tbrpf-06.txt, work in progress. Brad Williams, Tracy Camo, March 2002, Comparison of Broadcasting Techniques for MANET. Chen, T.W., M. Gerla, 1998. Global state routing: a new routing scheme for ad-hoc wireless networks, in: Proceedings of the IEEE ICC. Chen-Che Huang, Shou-Chih Lo, A Comprehensive Survey of Multicast Routing Protocols for MANET. Das, S.K., B.S. Manoj and C.S.R. Murthy, 2002. A Dynamic Core Based Multicast Routing Protocol for Ad Hoc Wireless Networks, in Proc. ACM MOBIHOC, pp: 24-35. Deepa, S., Dr. D.M. Kadhar Nawaz, 2010. A Study on the Behaviour of MANET Routing Protocols with Varying Densisites and Dynamic Value Ns – 2 (v 2.30) 1000m x 1000 m 50, 100, 150, … 250 250m 2mbps 30 CBR 2,4,6,… 10 512 bytes 2 packets / sec Mobility Patterns, IJCA Special Issue on “Mobile Ad hoc Networks”, MANETs. Dinakar, S., Dr. J. Shanthini, 2014. A Study on Various Features of Multicast Routing Protocols in Mobile Ad hoc Networks, International Journal of Advanced Research in Computer Science and Software Engineering, 4(7). Dinakar, S., Dr. J. Shanthini, 2014. Study on Broadcastin Techniques and Characteristics in Mobile Ad Hoc Networks, International Journal of Computer Science Engineering, 3(5). Dinakar, S., Dr. J. Shanthini, 2014. Study on Characteristics of Ad hoc Netwroks and TCP/IP Mode, International Journal of Research in Information Technology, 2(7). Hui Zeng, Minming Li, Hai Lu, Xiaohua Jia, Efficient Flooding in MANET. Ji, L.S. and M.S. Corson, 2003. Explicit Multicasting for Ad Hoc Networks”, Mobile Networks and Applications, 8(5): 535-549. Justin Lipman, Hai Liu, Ivan Stojmenovic, Broadcast in Ad hoc Networks. Kamal Kant, Lalit K. Awasti, Unicast and Multicast Routing Protocols for MANETS: A Comparitive Survey. Lee, S.J., W. Su, J. Hsu, M. Gerla, R. Bagrodia, 2000. A Performance Comparison Study of Ad Hoc Wireless Multicast Protocols, in Proc. IEEE INFOCOM, 2: 565-574. Mehran Abolhasan, Tadeusz Wysocki, Eryk Dutkiewicz, 2004. A Review of Routing Protocols for Mobile and Ad hoc Networks, www.elsevier.com/locate/adhoc networks. Murthy, C.S.R. and B.S. Manoj, 2004. Ad Hoc Wireless Networks: Architectures and Protocol”, New Jersey: Prentice Hall. Wu, X., H.R. Sadjadpour, J.J. Garcia-LunaAceves, 2007. Routing Overhead a Function of Node Mobility: Modeling Framework and Implications on Proactive Routing, Proc. Of IEEE MASS’07, pp: 1-9. Yu-Chee Tseng, Sze-Yao Ni, Yuh-Shyan Chen, Jang-Ping Sheu, 2002. The broadcast storm problem in MANET, Wireless Networks, 8, Kluwer Academic Publishers.