dynamic metric in ospf networks
... I declare that I have elaborated my doctoral thesis on the theme of “Dynamic Metric in OSPF Networks” independently, under the supervision of the doctoral thesis supervisor and with the use of technical literature and other sources of information which are all quoted in the thesis and detailed in th ...
... I declare that I have elaborated my doctoral thesis on the theme of “Dynamic Metric in OSPF Networks” independently, under the supervision of the doctoral thesis supervisor and with the use of technical literature and other sources of information which are all quoted in the thesis and detailed in th ...
Routing Theory Part 2
... – Next-hop address – This would normally be the ip address of the interface from which the routing update was sent. ...
... – Next-hop address – This would normally be the ip address of the interface from which the routing update was sent. ...
Architectures and Algorithms for IPv4/IPv6
... algorithm. It is suitable to use in simulation as its behaviour tends to be closer to the behaviour of real networks since it does not overload unnecessarily some links more than others. It may also be used in machines where the computation of paths is Dijkstra based and situations of equal-cost rou ...
... algorithm. It is suitable to use in simulation as its behaviour tends to be closer to the behaviour of real networks since it does not overload unnecessarily some links more than others. It may also be used in machines where the computation of paths is Dijkstra based and situations of equal-cost rou ...
Putting BGP on the Right Path: Better Performance via Next-Hop Routing
... Rule III: Consistently export [11]. If a route P is exportable to a neighboring AS i, then so must be all routes that are more highly ranked than P . Intuitively, Consistent Export prevents undesirable phenomena as in Figure 1, where an AS disconnects a neighbor from a destination by selecting a bet ...
... Rule III: Consistently export [11]. If a route P is exportable to a neighboring AS i, then so must be all routes that are more highly ranked than P . Intuitively, Consistent Export prevents undesirable phenomena as in Figure 1, where an AS disconnects a neighbor from a destination by selecting a bet ...
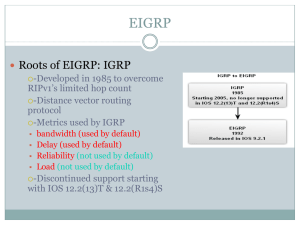
EIGRP
... 1) If feasible successor exists: If current successor route fails, feasible successor becomes the current successor, i.e. the current route. Routing of packets continue with little delay. 2) If no feasible successor exists: This may be because the Reported Distance is greater than the Feasible ...
... 1) If feasible successor exists: If current successor route fails, feasible successor becomes the current successor, i.e. the current route. Routing of packets continue with little delay. 2) If no feasible successor exists: This may be because the Reported Distance is greater than the Feasible ...
Offset Time-Emulated Architecture for Optical Burst Switching - Modelling and Performance Evaluation
... special treatment so that they could solve problems typical of data-centric networks. Contention resolution in optical domain together with quality of service (QoS) provisioning for quality demanding services are, among other things, the main designing issues when developing OBS networks. Another im ...
... special treatment so that they could solve problems typical of data-centric networks. Contention resolution in optical domain together with quality of service (QoS) provisioning for quality demanding services are, among other things, the main designing issues when developing OBS networks. Another im ...
Introduction to Dynamic Routing Protocols
... Figure 3-1 shows a timeline of IP routing protocols, with a chart that helps classify the various protocols. This chart will be referred to several times throughout this book. One of the earliest routing protocols was RIP. RIP has evolved into a newer version: RIPv2. However, the newer version of RI ...
... Figure 3-1 shows a timeline of IP routing protocols, with a chart that helps classify the various protocols. This chart will be referred to several times throughout this book. One of the earliest routing protocols was RIP. RIP has evolved into a newer version: RIPv2. However, the newer version of RI ...
Integrating Cisco Press Resources into the
... Single-Area OSPF Concepts Dijkstra’s Algorithm • Dijkstra’s algorithm places each router at the root of a tree – Calculates the shortest path to each node based on the cumulative cost to reach the destination – Each router has its own view of the topology – Each router uses the information in its t ...
... Single-Area OSPF Concepts Dijkstra’s Algorithm • Dijkstra’s algorithm places each router at the root of a tree – Calculates the shortest path to each node based on the cumulative cost to reach the destination – Each router has its own view of the topology – Each router uses the information in its t ...
Aalborg Universitet Adaptive Capacity Management in Bluetooth Networks Son, L.T.
... the global interconnection of all mobile devices. To implement Bluetooth network as a true mobile ad hoc wireless network operating in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operat ...
... the global interconnection of all mobile devices. To implement Bluetooth network as a true mobile ad hoc wireless network operating in short radio range, highly dynamic network environment, low power, and scarce resources, many new research challenges occur, such as limited wireless bandwidth operat ...
p2p
... Streaming live bandwidth-intensive media from a single source to a large quantity of receivers on the Internet. Solution: ...
... Streaming live bandwidth-intensive media from a single source to a large quantity of receivers on the Internet. Solution: ...
"Resilient Overlay Networks"
... This wide-area routing scalability comes at the cost of reduced fault-tolerance of end-to-end communication between Internet hosts. This cost arises because BGP hides many topological details in the interests of scalability and policy enforcement, has little information about traffic conditions, and ...
... This wide-area routing scalability comes at the cost of reduced fault-tolerance of end-to-end communication between Internet hosts. This cost arises because BGP hides many topological details in the interests of scalability and policy enforcement, has little information about traffic conditions, and ...
2. HBR Overview - Computer Science, Columbia University
... intersection of IP and wireless access. These developments will enhance the attractiveness of using IP in an array of network scenarios, such as commercial 3rd generation (3G) mobile networks, fixed broadband wireless access networks, enterprise and campus intranets, and tactical networks. Many new ...
... intersection of IP and wireless access. These developments will enhance the attractiveness of using IP in an array of network scenarios, such as commercial 3rd generation (3G) mobile networks, fixed broadband wireless access networks, enterprise and campus intranets, and tactical networks. Many new ...
Resilient Overlay Networks Abstract MIT Laboratory for Computer Science
... This wide-area routing scalability comes at the cost of reduced fault-tolerance of end-to-end communication between Internet hosts. This cost arises because BGP hides many topological details in the interests of scalability and policy enforcement, has little information about traffic conditions, and ...
... This wide-area routing scalability comes at the cost of reduced fault-tolerance of end-to-end communication between Internet hosts. This cost arises because BGP hides many topological details in the interests of scalability and policy enforcement, has little information about traffic conditions, and ...
Tema 1: Tecnologías LAN. - GRC
... Standardized by the IETF - currently in Draft stage. MPLS recommendations are done by IP players for IP services ...
... Standardized by the IETF - currently in Draft stage. MPLS recommendations are done by IP players for IP services ...
Querying Network Graphs with Recursive Queries
... • reachable(source, destination, ...). A reachable tuple represents that destination can be reached from source. Like links, these are typically keyed at the source node. • path(source,destination, path, cost). A path tuple represents that destination can be reached from source along the path indica ...
... • reachable(source, destination, ...). A reachable tuple represents that destination can be reached from source. Like links, these are typically keyed at the source node. • path(source,destination, path, cost). A path tuple represents that destination can be reached from source along the path indica ...
Chapter 6 - YSU Computer Science & Information Systems
... used to support reliable, sequenced delivery of packets • One field in each row of the table is populated with the last sequence number of the packet received from that neighbor • EIGRP uses this field for two purposes: – Sequence numbers are used to acknowledge specific packets that were delivered ...
... used to support reliable, sequenced delivery of packets • One field in each row of the table is populated with the last sequence number of the packet received from that neighbor • EIGRP uses this field for two purposes: – Sequence numbers are used to acknowledge specific packets that were delivered ...
PDF
... Migrating Your Network to Wide Metric Support .................................................................................................. 6 Impact on Configuration Commands ..................................................................................................................... 6 ...
... Migrating Your Network to Wide Metric Support .................................................................................................. 6 Impact on Configuration Commands ..................................................................................................................... 6 ...
Random Early Detection Gateways for Congestion Avoidance
... with FIFO scheduling. Not only is FIFO scheduling use- implemented in gateways with drop preference, where packful for sharing delay among connections, reducing delay ets are marked as either “essential” or “optional”, and “opfor a particular connection during its periods of burstiness tional” packe ...
... with FIFO scheduling. Not only is FIFO scheduling use- implemented in gateways with drop preference, where packful for sharing delay among connections, reducing delay ets are marked as either “essential” or “optional”, and “opfor a particular connection during its periods of burstiness tional” packe ...
IP: Addresses and Forwarding
... The link state (Dijkstra) approach is iterative, but it pivots around destinations j, and their predecessors k = p(j) Observe that an alternative version of the consistency condition holds for this case: D(i,j) = D(i,k) + c(k,j) ...
... The link state (Dijkstra) approach is iterative, but it pivots around destinations j, and their predecessors k = p(j) Observe that an alternative version of the consistency condition holds for this case: D(i,j) = D(i,k) + c(k,j) ...
lecture slides - CSE, IIT Bombay
... Recurrence of the probability of infection can be approximated by this linear form: ...
... Recurrence of the probability of infection can be approximated by this linear form: ...
(Backup) MDR
... there exists a bidirectional neighbor that does not satisfy condition (a) or (b). If a Backup MDR receives a new LSA, it waits BackupWaitInterval seconds, and then floods the LSA back out the receiving interface if there exists a bidirectional neighbor that does not satisfy condition (a) or (b). An ...
... there exists a bidirectional neighbor that does not satisfy condition (a) or (b). If a Backup MDR receives a new LSA, it waits BackupWaitInterval seconds, and then floods the LSA back out the receiving interface if there exists a bidirectional neighbor that does not satisfy condition (a) or (b). An ...