* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Active Networks
Zero-configuration networking wikipedia , lookup
TCP congestion control wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Network tap wikipedia , lookup
Computer network wikipedia , lookup
Wireless security wikipedia , lookup
Computer security wikipedia , lookup
Airborne Networking wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Packet switching wikipedia , lookup
Distributed firewall wikipedia , lookup
Peer-to-peer wikipedia , lookup
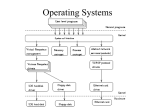
Active Networks – The Network Future By Samatha Gangapuram Prashant Shanti Kumar Harish Kumar Maringanti Assigned Unenviable task What Why How Where Active Networks – What ? No general agreement beyond buzz phrases. “Active networks explore the idea of allowing routing elements to be extensively programmed by the packets passing through them.” Legacy Vs Active Legacy Networks Active Networks Passive packet. Rely on agreement about protocols. Functionality built into each router. Change is a long and wrenching process. Active Packet. General agreement on model of computation. Functionality in each packet. Improved resilience to change. AN - Services Active Networks – Why ? Rapid deployment and development. Creating and Tailoring network services. Better performance. Open to deploy and administer. Active Networks – How ? AN Paradigms Programmable Switch Model Capsule Model Ad – hoc Model Active Networks – How ? Programmable Switch : Code is first transferred to the nodes, out – of – band. Packets are treated as data or input to the code. Active Networks – How ? Capsule Model : Each packet is a program. Each intermediate node executes the packet. Active Networks – How ? Ad – hoc Model : Packet contains flags. Node contains in-built routines. Based on flag, routines are executed. A N - Terminologies User Application (UA) Active Application (AA) Execution Environment (EE) Node Operating System (NodeOS) NodeOS The NodeOS is the base layer of any AN architecture. It manages the resources of the active node and co-ordinates the resource demands. NodeOS is also responsible for the enforcement of security policies. Examples SANE OS, JANOS, SCOUT, ExoKernel EE Nerve Center of the Active Node Responsible for all aspects of user-network interface. Nature of programming model and abstractions supported. Addressing and Naming facilities. Examples SmartPackets, ANTS, CANE AA AA is a program and associated state capable of executing one or more active activities in a node, to perform some particular service. AA is necessarily “portable” and dynamically installable or removable. Examples Active Reliable Multicasts, Protocol Boosters, Active Congestion Control. A N - Architecture App 1 App 2 Execution Environment A App 3 Execution Environment B App 1 App 4 Execution Environment A App 3 Execution Environment B Node OS Node OS Transmission Facilities Packet Transition I P UDP ANEP EE 1 ANEP UDP IP I P UDP UDP IP IP IP IP EE 2 ANEP ANEP IP IP IP IP TCP EE 3 TCP IP Implementation Challenges The network should be usable The network should have high flexibility The implementation should be secure The network should have high performance Killer Arguments Efficiency Resource Allocation Security Efficiency Hiccups: Bandwidth demand is growing faster than CPU speed – bad idea to execute arbitrary programs on packets. Most programming languages are interpreted – JAVA byte code, plain interpreter. Cure: Don’t propose AN for the core of the Internet. Use just-in-time compilation, native code. Hybrid architectures (high speed AN!) Resource Allocation Hiccups: Fairness in queuing is a problem. Cannot guarantee QoS. Cannot control Looping packets. Cure: Provide distributed control (Scaling). resource reservation in advance, resource preemption. Limit capabilities of the active packet. Security Security cannot be limited to peripheral nodes. Possible threats: Overload based Denial of Service Unauthorized access to the exposed control plane. Secure Node doesn’t mean Secure Network. Security at NodeOS Security Enforcement through Authorizations. Authorization policies are expressed in terms of Access Control Lists, which is a logical 3 - tuple of the form : <resource, user, permissions> NodeOS has a security policy database and a policy enforcement engine. Security at EE Each EE has it's own protection policy, possibly a security database and an enforcement engine. The programming model that an EE supports must also be restricted to ensure network security. No broad consensus on the division of responsibility for policy enforcement between the NodeOS and the EE. Security in SwitchWare Uses ALIEN active loader. Code Modules loaded on the fly. Restricts access using namespaces. Uses a language specification called CAML. AN – APPLICATIONS Network Management Multicasting Caching Active Congestion Control Security Network Management No polling required "Patrol" and "first-aid" packets can track a problem and rectify it respectively. Code moved to node rather than data to management center Example:Delegated Management. Decentralization helps in scalability, reducing delays from responses and effective bandwidth utilization. Multicasting Active internal nodes elegantly solve many current problems such as: NACK implosion. Concentrated load of retransmissions. Duplication of packets. Example: ARM Suppression of NACK & effective retransmission Active Congestion Control Selective dropping of units, packets or cells can be held very efficiently. Multi-stream interaction. Example: APCI Backward compatibility with non-active nodes & on the fly routing employed. Caching Tradeoff between network based storage & bandwidth. Location & time of storage crucial. Example: Self-organizing wide-Area Network caches: small number of caches within routers form large virtual cache. Security Node – Packet conflict. Node security by authentication of active packets & PCC(Proof Correct Code). Packet security by Fault-tolerance & Encryption. Example:SANE AN - Services Video on Demand VPN Multimedia Conferencing VoIP / IP Telephony Active Firewalling AN - Services New Content-type or Redirection Header Request Dynamic Proxy Server WebCache Proxylet Remote Method Invocation Call Dynamic Proxy Server Audio Transcoder RTP Streamed Audio Request Audio Response Audio File Response Audio File Request Proxylet Response Proxylet Request Request Web Browser Response Web Cache Web Server Proxylet Server “Retrofitting" AN to IP The Active IP Option: Option in the IP header alerts the router to look at the packet payload more closely. Active Network Encapsulation Protocol (ANEP): Adds a header that directs the router. AN & Legacy SmartPackets – A Case Study Uses Capsule model: Code with IP packet Programs must be completely self-contained. Operating environment provides security. Languages: Sprocket – A high level language Spanner – An assembly level language SmartPackets – A Case Study Uses ANEP to fit with Legacy Networks NodeOs – JanOs EE – CANES/ASP AA Network Management SmartPackets – A Case Study Network Management Defines 4 types of packets: Program Data Error Message SmartPackets – A Case Study Security For Nodes: Authentication of packet Cryptographic hash of non-mutable fields For packets: Redirection Encryption SmartPackets – A Case Study Limitations Packet size Applications adaptability Scope Extending for other applications Current Work Active Nets at DARPA ActiveNets at MIT ANTS at Washington SwitchWare at UPenn JANOS & OSkit at Utah Liquid Software at Arizona Panda at UCLA NetScript at Columbia CANES at Georgia Tech Smart Packets at BBN Conclusion Is Active Network really the future ? References Darpa http://www.darpa.mil/ito/psum1999/J044-0.html Switchware http://www.cis.upenn.edu/~switchware/ CANES http://www.cc.gatech.edu/projects/canes/ www.ieee.org www.citeseer.com