* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download ppt - The Fengs
Survey
Document related concepts
Cracking of wireless networks wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
Internet protocol suite wikipedia , lookup
Distributed operating system wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Network tap wikipedia , lookup
Computer network wikipedia , lookup
Backpressure routing wikipedia , lookup
Airborne Networking wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
IEEE 802.1aq wikipedia , lookup
Transcript
CSE524: Lecture 6
Network Layer (Part 1)
1
Administrative
• Reading assignment
– Chapter 4
• Homework #2 due Monday
• Homework #1
– Solutions will be handed out
2
Last classes
• Data-link layer
– Functions
– Specific implementations, devices
3
Next classes
• Network layer
– Functions
•
•
•
•
•
•
•
•
Addressing
Security
Fragmentation
Delivery semantics
Quality of service
Routing
Demux to upper layer
Error detection
– Specific implementations
• IP
• Router devices, implementations
4
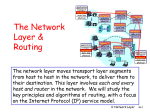
Network layer functions
• Transport packet from
sending to receiving hosts
• Network layer protocols in
every host, router
application
transport
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
network
data link
physical
application
transport
network
data link
physical
• Important functions:
– Addressing: address assignment
– Security: provide privacy,
authentication, etc. at the
network layer
– Fragmentation: break-up
packets based on data-link layer
properties
– Delivery semantics: unicast,
multicast, anycast, broadcast,
ordering
– Quality-of-service: provide
predictable performance
– Routing: path selection and
packet forwarding
5
NL: Addressing
• Hierarchical vs. flat
– Routing table size
• Global vs. local
– Applications (NAT)
– Processing speed
• Variable-length vs. fixed-length
– Flexibility
– Processing costs
– Header size
6
NL: Security
• Secrecy
– No eavesdropping
• Integrity
– No man-in-the-middle attacks
• Authenticity
– Ensure identity of source
• If time permits, we will look at network security
at the end of course…..
7
NL: Fragmentation
• Different link-layers have different MTUs
• Split packets into multiple fragments
• Where to do reassembly?
– End nodes – avoids unnecessary work
– Dangerous to do at intermediate nodes
• Buffer space
• Must assume single path through network
• May be re-fragmented later on in the route again
• Path MTU Discovery
– Network layer does no fragmentation
– Host does Path MTU discovery
8
NL: Fragmentation is Harmful
• Uses resources poorly
– Forwarding costs per packet
– Best if we can send large chunks of data
– Worst case: packet just bigger than MTU
• Poor end-to-end performance
– Loss of a fragment
• Reassembly is hard
– Buffering constraints
9
NL: Fragmentation
• References
– Characteristics of Fragmented IP Traffic on Internet Links.
Colleen Shannon, David Moore, and k claffy -- CAIDA, UC
San Diego. ACM SIGCOMM Internet Measurement
Workshop 2001. http://www.aciri.org/vern/sigcomm-imeas2001.program.html
– C. A. Kent and J. C. Mogul, "Fragmentation considered
harmful," in Proceedings of the ACM Workshop on
Frontiers in Computer Communications Technology, pp.
390--401, Aug. 1988.
http://www.research.compaq.com/wrl/techreports/abstracts/87
.3.html
10
NL: Delivery semantics
• Communication modes
–
–
–
–
Unicast (One source to one destination)
Anycast (One source to any of a set of destinations)
Multicast (One or more sources to a set of destinations)
Broadcast (One source to all destinations)
• Ordering
– In-order vs. out-of-order delivery
• If time permits, we will look at multicast at the end of
the course.
11
NL: Quality-of-Service
Q: What service model for
“channel” transporting
packets from sender to
receiver?
• guaranteed bandwidth?
• preservation of inter-packet
timing (no jitter)?
• loss-free delivery?
• in-order delivery?
• congestion feedback to
sender?
The most important
abstraction provided
by network layer:
? ?
?
virtual circuit
or
datagram?
12
NL: Virtual circuits
“source-to-dest path behaves much like telephone circuit”
– performance-wise
– network actions along source-to-dest path
• call setup, teardown for each call before data can flow
• each packet carries VC identifier (not destination host OD)
• every router on source-dest path s maintain “state” for each
passing connection
– transport-layer connection only involved two end systems
• link, router resources (bandwidth, buffers) may be allocated to
VC
– to get circuit-like perf.
13
NL: Virtual circuits: signaling protocols
• used to setup, maintain teardown VC
• used in ATM, frame-relay, X.25
• not used in today’s Internet on an end-to-end basis
application
transport 5. Data flow begins
network 4. Call connected
data link 1. Initiate call
physical
6. Receive data application
3. Accept call transport
2. incoming call network
data link
physical
14
NL: Datagram networks: the Internet model
• no call setup at network layer
• routers: no state about end-to-end connections
– no network-level concept of “connection”
• packets typically routed using destination host ID
– packets between same source-dest pair may take different paths
application
transport
network
data link 1. Send data
physical
application
transport
2. Receive data network
data link
physical
15
NL: Network layer service models:
Network
Architecture
Internet
Service
Model
Guarantees ?
Congestion
Bandwidth Loss Order Timing feedback
best effort none
ATM
CBR
ATM
VBR
ATM
ABR
ATM
UBR
constant
rate
guaranteed
rate
guaranteed
minimum
none
no
no
no
yes
yes
yes
yes
yes
yes
no
yes
no
no (inferred
via loss)
no
congestion
no
congestion
yes
no
yes
no
no
• Internet model being extended: Intserv, Diffserv
– Chapter 6
16
NL: Datagram or VC network: why?
Internet
ATM
• data exchange among computers • evolved from telephony
– “elastic” service, no strict
• human conversation:
timing req.
– strict timing, reliability
• “smart” end systems (computers)
requirements
– can adapt, perform control,
– need for guaranteed service
error recovery
• “dumb” end systems
– simple inside network,
– telephones
complexity at “edge”
– complexity inside network
• many link types
– different characteristics
– uniform service difficult
17
NL: Routing
• Routing algorithms and architectures
– Link state algorithms
– Distance vector algorithms
• Routing hierarchies
– Area routing
– Landmark routing
18
NL: Routing algorithms
Routing protocol
5
Goal: determine “good” path
(sequence of routers) thru
network from source to dest.
2
A
Graph abstraction for
routing algorithms:
• graph nodes are
routers
• graph edges are
physical links
– link cost: delay, $ cost,
or congestion level
B
2
1
D
3
C
3
1
5
F
1
E
2
• “good” path:
– typically means
minimum cost path
– other def’s possible
19
NL: Routing algorithms
Global or decentralized
information?
Global:
• all routers have complete
topology, link cost info
• “link state” algorithms
Decentralized:
• router knows physicallyconnected neighbors, link
costs to neighbors
• iterative process of
computation, exchange of
info with neighbors
• “distance vector”
algorithms
Static or dynamic?
Static:
• routes change slowly over
time
Dynamic:
• routes change more
quickly
– periodic update
– in response to link cost
changes
20
NL: What to look for in routing algorithms
•
•
•
•
Communication costs
Processing costs
Optimality
Stability
– Convergence time
– Loop freedom
– Oscillation damping
21
NL: Link state routing algorithms
• Used in OSPF (intra-domain routing protocol)
• Basic steps
• Start condition
– Each node assumed to know state of links to its neighbors
• Step 1
– Each node broadcasts its state to all other nodes
– Reliable flooding mechanism
• Step 2
– Each node locally computes shortest paths to all other nodes
from global state
– Dijkstra’s shortest path tree (SPT) algorithm
22
NL: Step 1
• Link State Packets (LSPs) to broadcast state to
all nodes
• Periodically, each node creates a link state
packet containing:
–
–
–
–
–
Node ID
List of neighbors and link cost
Sequence number
Time to live (TTL)
Node outputs LSP on all its links
23
NL: Step 1
• Reliable Flooding
– When node J receives LSP from node K
• If LSP is the most recent LSP from K that J has seen so far, J saves it
in database and forwards a copy on all links except link LSP was
received on
• Otherwise, discard LSP
– How to tell more recent
•
•
•
•
•
Use sequence numbers
Same method as sliding window protocols
Needed to avoid stale information from flood
Sequence number wrap-around
Lollipop sequence space
24
NL: Step 1 and wrapped sequence numbers
• Wrapped sequence numbers
– 0-N where N is large
– If difference between numbers is large, assume a
wrap
– A is older than B if….
• A < B and |A-B| < N/2 or…
• A > B and |A-B| > N/2
• What about new nodes out of sync with
sequence number space?
• Lollipop sequence (Perlman 1983)
25
NL: Step 1 and lollipop sequence numbers
• Divide sequence number space
• Special negative sequence for recovering from reboot
• When receiving an old number, nodes inform new node
of current sequence number
• A older than B if
– A < 0 and A < B
– A > 0, A < B and (B – A) < N/4
– A > 0, A > B and (A – B) > N/4
-N/2
0
N/2 - 1
26
NL: Step 2
A Link-state routing algorithm
Dijkstra’s algorithm
• all link costs on the network
are known
• all nodes have same info
• computes least cost paths
from one node (‘source”) to
all other nodes
– gives routing table for that
node
• iterative: after k iterations,
know least cost path to k
destinations
Notation:
• c(i,j): link cost from node i
to j. cost infinite if not direct
neighbors
• D(v): current value of cost
of path from source to dest. V
• p(v): predecessor node along
path from source to v, that is
next v
• N: set of nodes whose least
cost path definitively known
27
NL: Step 2 (Dijkstra’s algorithm example)
1 Initialization:
2 N = {A}
3 for all nodes v
4
if v adjacent to A
5
then D(v) = c(A,v)
6
else D(v) = infinity
7
8 Loop
9 find w not in N such that D(w) is a minimum
10 add w to N
11 update D(v) for all v adjacent to w and not in N:
12
D(v) = min( D(v), D(w) + c(w,v) )
13 /* new cost to v is either old cost to v or known
14 shortest path cost to w plus cost from w to v */
15 until all nodes in N
28
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
C
C
F
2
E
1
5
1
3
D
B
step
0
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
29
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
AD
C
C
F
2
E
1
5
1
3
D
B
step
0
1
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
2, A
4, D
2, D
~
30
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
AD
ADE
C
C
F
2
E
1
5
1
3
D
B
step
0
1
2
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
2, A
4, D
2, D
~
2, A
3, E
4, E
31
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
AD
ADE
ADEB
C
C
F
2
E
1
5
1
3
D
B
step
0
1
2
3
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
2, A
4, D
2, D
~
2, A
3, E
4, E
3, E
4, E
32
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
AD
ADE
ADEB
ADEBC
C
C
F
2
E
1
5
1
3
D
B
step
0
1
2
3
4
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
2, A
4, D
2, D
~
2, A
3, E
4, E
3, E
4, E
4, E
33
NL: Step 2 (Dijkstra’s algorithm example)
5
B
2
A
2
1
SPT
A
AD
ADE
ADEB
ADEBC
ADEBCF
C
C
F
2
E
1
5
1
3
D
B
step
0
1
2
3
4
5
3
D
E
F
D(b), P(b) D(c), P(c) D(d), P(d) D(e), P(e) D(f), P(f)
2, A
5, A
1, A
~
~
2, A
4, D
2, D
~
2, A
3, E
4, E
3, E
4, E
4, E
34
NL: Link State Characteristics
• With consistent LSDBs, all
nodes compute consistent
loop-free paths
• Limited by Dijkstra
computation overhead,
space requirements
• Can still have transient
loops
B
1
1
3
A
5
C
2
D
Packet from CA
may loop around BDC
if B knows about failure
and C & D do not
35
NL: Dijkstra’s algorithm, discussion
Algorithm complexity: n nodes
• each iteration: need to check all nodes, w, not in N
• n*(n+1)/2 comparisons: O(n**2)
• more efficient implementations possible: O(nlogn)
Oscillations possible:
• e.g., link cost = amount of carried traffic
D
1
1
0
A
0 0
C
e
1+e
e
initially
B
1
2+e
A
0
D 1+e 1 B
0
0
C
… recompute
routing
0
D
1
A
0 0
C
2+e
B
1+e
… recompute
2+e
A
0
D 1+e 1 B
e
0
C
… recompute
36
NL: Distance vector routing algorithms
• Variants used in
– Early ARPAnet
– RIP (intra-domain routing protocol)
– BGP (inter-domain routing protocol)
• Distributed next hop computation
• Unit of information exchange
– Vector of distances to destinations
37
NL: Distance vector routing algorithms
• Exchange known distance information iteratively
• Example (Bellman 1957)
– Start with link table (as with Dijkstra), calculate distance table
iteratively through table exchanges with adjacent nodes
– Distance table data structure
•
•
•
•
X
D (Y,Z)
table of known distances and next hops kept per node
row for each possible destination
column for each directly-attached neighbor to node
example: in node X, for dest. Y via neighbor Z:
distance from X to
= Y, via Z as next hop
Z
= c(X,Z) + minw{D (Y,w)}
X
Minimum known
D (Y,*) = distance from X to Y
X
Next hop node
H (Y) = from X to Y
38
NL: Distance Table: example
7
A
B
1
E
cost to destination via
D ()
A
B
D
A
1
14
5
B
7
8
5
C
6
9
4
D
4
11
2
2
8
1
C
E
2
D
E
D
D (C,D) = c(E,D) + minw {D (C,w)}
= 2+2 = 4
E
D
c(E,D)
+
min
{D
(A,w)}
D (A,D) =
w
= 2+3 = 5 loop!
E
B
D (A,B) = c(E,B) + minw{D (A,w)}
= 8+6 = 14
loop!
X
H (Y) =
39
NL: Distance table gives routing table
X
H (Y)
E
cost to destination via
Outgoing link
to use, cost
D ()
A
B
D
A
1
14
5
A
A,1
B
7
8
5
B
D,5
C
6
9
4
C
D,4
D
4
11
2
D
D,4
Distance table
Routing table
40
NL: Bellman algorithm
while there is a change in D {
for all k not neighbor of i {
for each j neighbor of i {
Di(k,j) = c(i,j) + Dj(k,*)
if Di(k,j) < Di(k,*) {
Di(k,*) = Di(k,j)
Hi(k) = j
}
}
}
}
Dj(k,*)
Di(k,*)
c(i,j)
i
k
j
c(i,j’)
j’
Dj’(k,*)
k’
41
NL: Distributed Bellman-Ford
• Make Bellman algorithm distributed (Ford-Fulkerson
1962)
– Each node i knows part of link table
– Iterative
• Each node sends around and recalculates D[i,*]
• continues until no nodes exchange info.
• self-terminating: no “signal” to stop
– Asynchronous
• nodes need not exchange info/iterate in lock step!
• “triggered updates”
– Distributed
• each node communicates only with directly-attached neighbors
42
NL: Distributed Bellman-Ford overview
Iterative, asynchronous:
each local iteration caused
by:
• local link cost change
• message from neighbor:
its least cost path change
from neighbor
Distributed:
• each node notifies
neighbors only when its
least cost path to any
destination changes
Each node:
wait for (change in local link
cost of msg from neighbor)
recompute distance table
if least cost path to any dest
has changed, notify
neighbors
– neighbors then notify their
neighbors if necessary
43
NL: Distributed Bellman-Ford algorithm
At all nodes, X:
1 Initialization:
2 for all adjacent nodes v:
3
D X(*,v) = infinity
/* the * operator means "for all rows" */
X
4
D (v,v) = c(X,v)
5 for all destinations, y
X
6
send min D (y,w) to each neighbor /* w over all X's neighbors */
w
44
NL: Distributed Bellman-Ford algorithm (cont.):
8 loop
9 wait (until I see a link cost change to neighbor V
10
or until I receive update from neighbor V)
11
12 if (c(X,V) changes by d)
13 /* change cost to all dest's via neighbor v by d */
14 /* note: d could be positive or negative */
15 for all destinations y: D X(y,V) = D X(y,V) + d
16
17 else if (update received from V wrt destination Y)
18 /* shortest path from V to some Y has changed */
19 /* V has sent a new value for its min w DV(Y,w) */
20 /* call this received new value is "newval" */
21 for the single destination y: D X(Y,V) = c(X,V) + newval
22
23 if we have a new minw DX(Y,w)for any destination Y
24
send new value of min w D X(Y,w) to all neighbors
25
26 forever
45
NL: DBF example
Initial Distance Vectors
1
B
C
7
8
A
1
2
2
E
D
Distance to Node
Info at
Node
A
B
C
D
E
A
0
7
~
~
1
B
7
0
1
~
8
C
~
1
0
2
~
D
~
~
2
0
2
E
1
8
~
2
0
46
NL: DBF example
E Receives D’s Routes; Updates Cost
1
B
C
7
8
A
1
2
2
E
D
Distance to Node
Info at
Node
A
B
C
D
E
A
0
7
~
~
1
B
7
0
1
~
8
C
~
1
0
2
~
D
~
~
2
0
2
E
1
8
4
2
0
47
NL: DBF example
A receives B’s; Updates Cost
1
B
C
7
8
A
1
2
2
E
D
Distance to Node
Info at
Node
A
B
C
D
E
A
0
7
8
~
1
B
7
0
1
~
8
C
~
1
0
2
~
D
~
~
2
0
2
E
1
8
4
2
0
48
NL: DBF example
A receives E’s routes; Updates Costs
1
B
C
7
8
A
1
2
2
E
D
Distance to Node
Info at
Node
A
B
C
D
E
A
0
7
5
3
1
B
7
0
1
~
8
C
~
1
0
2
~
D
~
~
2
0
2
E
1
8
4
2
0
49
NL: DBF example
Final Distances
1
B
C
7
8
A
1
2
2
E
D
Distance to Node
Info at
Node
A
B
C
D
E
A
0
6
5
3
1
B
6
0
1
3
5
C
5
1
0
2
4
D
3
3
2
0
2
E
1
5
4
2
0
50
NL: DBF example
E’s routing table
1
B
C
E’s routing table
Next hop
7
8
A
1
2
2
E
D
dest
A
B
D
A
1
14
5
B
7
8
5
C
6
9
4
D
4
11
2
51
NL: DBF (another example)
• See book for
explanation of this
example
X
2
Y
7
1
Z
52
NL: DBF (another example)
X
2
Y
7
1
Z
Z
X
D (Y,Z) = c(X,Z) + minw{D (Y,w)}
= 7+1 = 8
Y
X
D (Z,Y) = c(X,Y) + minw {D (Z,w)}
= 2+1 = 3
53
NL: DBF (good news example)
Link cost changes:
• node detects local link cost change
• updates distance table (line 15)
• if cost change in least cost path, notify
neighbors (lines 23,24)
• See book for explanation of this example
“good
news
travels
fast”
1
X
4
Y
50
1
Z
algorithm
terminates
54