* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download Firewalls
Parallel port wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Airborne Networking wikipedia , lookup
Computer security wikipedia , lookup
Computer network wikipedia , lookup
Asynchronous Transfer Mode wikipedia , lookup
Multiprotocol Label Switching wikipedia , lookup
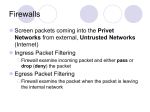
Wireless security wikipedia , lookup
Internet protocol suite wikipedia , lookup
TCP congestion control wikipedia , lookup
Serial digital interface wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Network tap wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Packet switching wikipedia , lookup
Wake-on-LAN wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Firewalls 1 References 1. Mark Stamp, Information Security: Principles and Practice, Wiley Interscience, 2006. 2. Robert Zalenski, Firewall Technologies, IEEE Potential, 2002, p 24 – 29. 3. Avishai Wool, A Quantitative Study of Firewall Configuration Errors, IEEE Computer, June 2004, p 62 – 67. 4. Steven Bellovin and William Cheswick, Network Firewalls, IEEE Communications Magazine, Sept 1994, p 50 – 57. 5. William Arbaugh, Firewalls: An Outdated Defense, IEEE Computer, June 2003, p 112 – 113. 6. Charles Zhang, Marianne Winslett, Carl Gunter, On the Safety and Efficiency of Firewall Policy Deployment, IEEE Symposium on Security and Privacy, 2007. 7. Mohamed Gouda and Alex Liu, A Model of Stateful Firewalls and its Properties, Proc of the 2005 International Conference on Dependable Systems and Networks, 2005. 2 Firewall as Network Access Control • Access Control – Authentication – Authorization • Single Sign On • Firewall – Interface between networks • Usually external (internet) and internal – Allows traffic flow in both directions 3 Firewall Internal Internet – Interface between networks • Usually external (internet) and internal – Allows traffic flow in both directions – Controls the traffic 4 Firewall as Secretary • A firewall is like a secretary • To meet with an executive – First contact the secretary – Secretary decides if meeting is reasonable – Secretary filters out many requests • You want to meet chair of CS department? – Secretary does some filtering • You want to meet President of US? – Secretary does lots of filtering! [1] 5 Security Strategies • Least privilege – Objects have the lowest privilege to perform assigned task • Defense in depth – Use multiple mechanism – Best if each is independent: minimal overlap • Choke point – Facilitates monitoring and control [2] 6 Security Strategies - 2 • Weakest link • Fail-safe – If firewall fails, it should go to fail-safe that denies access to avoid intrusions • Default deny • Default permit • Universal participation – Everyone has to accept the rules [2] 7 Security Strategies - 3 • Diversity of defense • Inherent weaknesses – Multiple technologies to compensate for inherent weakness of one technology • Common heritage – If systems configured by the same person, may have the same weakness • Simplicity • Security through obscurity [2] 8 Security Strategies - 4 • Configuration errors can be devastating • Testing is not perfect • Ongoing trial and error will identify weaknesses • Enforcing a sound policy is critical [2] 9 Types of Firewall • No Standard Terminology • Packet Filtering (network layer) – Simplest firewall – Filter packets based on specified criteria • IP addresses, subnets, TCP or UDP ports • Stateful inspection (transport layer) – In addition to packet inspection – Validate attributes of multi-packet flows [2] 10 Types of Firewall - 2 • Application Based Firewall (application layer) – SW package that allows or denies access across networks – Log access – attempted access and allowed access • Personal firewall – single user, home network [2] 11 Types of Firewall - 3 • Proxy – Intermediate connection between servers on internet and internal servers. – For incoming data • Proxy is server to internal network clients – For outgoing data • Proxy is client sending out data to the internet [2] 12 Types of Firewall - 4 • Network Address Translation – Hides internal network from external network – Private IP addresses – expands the IP address space – Creates a choke point • Virtual Private Network – Employs encryption and integrity protection – Use internet as part of a private network [2] 13 Packet Filter • Advantages – Simplest firewall architecture – Works at the Network layer – applies to all systems – One firewall for the entire network • Disadvantages – Can be compromised by many attacks • Source spoofing 14 Packet Filter - Example [2] 15 Packet Filter - Example [2] 16 Packet Filter - Example • Attack succeeds because of rules B and D • More secure to add source ports to rules 17 Packet Filter - Example [2] 18 Packet Filter - Example • These packets would be admitted. To avoid this add an ACK bit to the rule set [2] 19 Packet Filter - Example • Attack fails, because the ACK bit is not set. ACK bit is set if the connection originated from inside. • Incoming TCP packets must have ACK bit set. If this started outside, then no matching data, and packet will be rejected. [2] 20 TCP Ack for Port Scanning • Attacker sends packet with ACK set (without prior handshake) using port p – Violation of TCP/IP protocol • Packet filter firewall passes packet – Firewall considers it part of an ongoing connection • Receiver sends RST – Indicates to the sender that the connection should be terminated • Receiving RST indicates that port p is open!! [1] 21 TCP Ack Port Scan • RST confirms that port 1209 is open • Problem: packet filtering is stateless; the firewall should track the entire connection exchange [1] 22 Stateful Packet Filter • Remembers packets in the TCP connections (and flag bits) • Adds state info to the packet filter firewalls. • Operates at the transport layer. • Pro: Adds state to packet filter and keeps track of ongoing connection • Con: Slower, more over head. Packet content info not used application transport network link physical [1] 23 Application Proxy • A proxy acts on behalf the system being protected. • Application proxy examines incoming app data – verifies that data is safe before passing it to the system. • Pros – Complete view of the connections and app data – Filter bad data (viruses, Word macros) – Incoming packet is terminated and new packet is sent to internal network • Con – Speed [1] 24 Firewalk – Port Scanning • Scan ports through firewalls • Requires knowledge of – IP address of firewall – IP address of one system in internal network – Number of hops to the firewall • Set TTL (time to live) = Hops to firewall +1 • Set destination port to be p • If firewall does not pass data for port p, then no response • If data passes thru firewall on port p, then time exceeded error message [1] 25 Firewalk and Proxy Firewall Trudy Router Router Packet filter Router Dest port 12343, TTL=4 Dest port 12344, TTL=4 Dest port 12345, TTL=4 Time exceeded • Attack stopped by proxy firewall – Incoming packet destroyed (old TTL value also destroyed) – New outgoing packet will not exceed TTL. [1] 26 Firewalls and Defense in Depth • Example security architecture DMZ WWW server FTP server DNS server Internet Packet Filter Application Proxy Intranet with Personal Firewalls [1] 27 [1] 28