* Your assessment is very important for improving the workof artificial intelligence, which forms the content of this project
Download Unit 4 - NIST NACOL
Survey
Document related concepts
Wake-on-LAN wikipedia , lookup
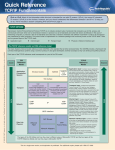
Airborne Networking wikipedia , lookup
Net neutrality wikipedia , lookup
Computer network wikipedia , lookup
Net neutrality law wikipedia , lookup
Deep packet inspection wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Zero-configuration networking wikipedia , lookup
Piggybacking (Internet access) wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Internet protocol suite wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Transcript
Internet Alternatively referred to as the net or web, the Internet was initially developed to aid in the progress of computing technology by linking all the best academic computer centers. The Internet as we know it today first started being developed in the late 1960's and transmitted its first message on Friday, October 29, 1969. In1993, the Internet experienced one of its largest growths to date and today is accessible by people all over the world. The Internet contains billions of web pages created by people and companies from around the world, making it a limitless place to locate information and entertainment. The Internet also has thousands of services that help make life more convenient. For example, many financial institutions offer online banking that enables a user to manage and view their account online. The Internet basics The Internet utilizes the TCP/IP protocol and is accessed using a computer modem, broadband, 3G or network that is connected through an ISP. The Internet is explored, which is more commonly referred to as surfing, using a browser. Finding information on the Internet is achieved by using a search engine. Users browse web pages by following hyperlinks. Files, pictures, songs, and video can be shared downloading (receiving) and uploading (sending). The Internet is also used for communicating with others through social networks, online games, forums, chat, e-mails, IM and VoIP. The Internet is a global network connecting millions of computers. More than 190 countries are linked into exchanges of data, news and opinions. History of Internet The Internet was the result of some visionary thinking by people in the early 1960s who saw great potential value in allowing computers to share information on research and development in scientific and military fields. J.C.R. Licklider of MIT first proposed a global network of computers in 1962, and moved over to the Defense Advanced Research Projects Agency (DARPA) in late 1962 to head the work to develop it. Leonard Kleinrock of MIT and later UCLA developed the theory of packet switching, which was to form the basis of Internet connections. Lawrence Roberts of MIT connected a Massachusetts computer with a California computer in 1965 over dialup telephone lines. It showed the feasibility of wide area networking, but also showed that the telephone line's circuit switching was inadequate. Kleinrock's packet switching theory was confirmed. Roberts moved over to DARPA in 1966 and developed his plan for ARPANET. These visionaries and many more left unnamed here are the real founders of the Internet. pg. 1 The Internet, then known as ARPANET, was brought online in 1969 under a contract let by the renamed Advanced Research Projects Agency (ARPA) which initially connected four major computers at universities in the southwestern US. E-mail was adapted for ARPANET by Ray Tomlinson of BBN in 1972. He picked the @ symbol from the available symbols on his teletype to link the username and address. The telnet protocol, enabling logging on to a remote computer, was published as a Request for Comments (RFC) in 1972. RFC's are a means of sharing developmental work throughout community. The ftp protocol, enabling file transfers between Internet sites, was published as an RFC in 1973, and from then on RFC's were available electronically to anyone who had use of the ftp protocol. The Internet matured in the 70's as a result of the TCP/IP architecture first proposed by Bob Kahn at BBN and further developed by Kahn and Vint Cerf at Stanford and others throughout the 70's. It was adopted by the Defense Department in 1980 replacing the earlier Network Control Protocol (NCP) and universally adopted by 1983. OSI (Open System Interconnection) Reference Model: Short for Open System Interconnection, OSI is a network model developed by ISO in1978 where peer-to-peer communications are divided into seven layers. Each layer performs a specific task or tasks and builds upon the preceding layer until pg. 2 the communications are complete. Below are the purposes of each of the seven layers. 1 - Physical layer - responsible for the electrical, mechanical, and timing across the link. 2 - Data link layer (also known as the link layer) - responsible for transmitting data across a link. 3 - Network layer - responsible for routing information through the network and allowing systems to communicate. 4 - Transport layer - responsible for transferring information between endpoints on the network and deals with errors such as lost or duplicate packets. 5 - Session layer - responsible for managing a session between two applications. 6 - Presentation layer - responsible for the data formatting and display, allowing for compatibility. 7 - Application layer - responsible for user interaction. pg. 3 In Detail (Please do not tell secret password anybody): PHYSICAL LAYER The physical layer, the lowest layer of the OSI model, is concerned with the transmission and reception of the unstructured raw bit stream over a physical medium. It describes the electrical/optical, mechanical, and functional interfaces to the physical medium, and carries the signals for all of the higher layers. It provides: Data encoding: modifies the simple digital signal pattern (1s and 0s) used by the PC to better accommodate the characteristics of the physical medium, and to aid in bit and frame synchronization. It determines: What signal state represents a binary 1 How the receiving station knows when a "bit-time" starts How the receiving station delimits a frame Physical medium attachment, accommodating various possibilities in the medium: Transmission technique: determines whether the encoded bits will be transmitted by baseband (digital) or broadband (analog) signaling. Physical medium transmission: transmits bits as electrical or optical signals appropriate for the physical medium, and determines: DATA LINK LAYER The data link layer provides error-free transfer of data frames from one node to another over the physical layer, allowing layers above it to assume virtually error-free transmission over the link. Link establishment and termination: establishes and terminates the logical link between two nodes. Frame traffic control: tells the transmitting node to "back-off" when no frame buffers are available. Frame sequencing: transmits/receives frames sequentially. Frame acknowledgment: provides/expects frame acknowledgments. Detects and recovers from errors that occur in the physical layer by retransmitting nonacknowledged frames and handling duplicate frame receipt. Frame delimiting: creates and recognizes frame boundaries. Frame error checking: checks received frames for integrity. NETWORK LAYER The network layer controls the operation of the subnet, deciding which physical path the data should take based on network conditions, priority of service, and other factors. It provides: pg. 4 Routing: routes frames among networks. Frame fragmentation: if it determines that a downstream router's maximum transmission unit (MTU) size is less than the frame size, a router can fragment a frame for transmission and re-assembly at the destination station. Logical-physical address mapping: translates logical addresses, or names, into physical addresses. TRANSPORT LAYER The transport layer ensures that messages are delivered error-free, in sequence, and with no losses or duplications. It relieves the higher layer protocols from any concern with the transfer of data between them and their peers. The size and complexity of a transport protocol depends on the type of service it can get from the network layer. For a reliable network layer with virtual circuit capability, a minimal transport layer is required. If the network layer is unreliable and/or only supports datagrams, the transport protocol should include extensive error detection and recovery. The transport layer provides: Message segmentation: accepts a message from the (session) layer above it, splits the message into smaller units (if not already small enough), and passes the smaller units down to the network layer. The transport layer at the destination station reassembles the message. Message acknowledgment: provides reliable end-to-end message delivery with acknowledgments. Message traffic control: tells the transmitting station to "back-off" when no message buffers are available. Session multiplexing: multiplexes several message streams, or sessions onto one logical link and keeps track of which messages belong to which sessions (see session layer). SESSION LAYER The session layer allows session establishment between processes running on different stations. It provides: Session establishment, maintenance and termination: allows two application processes on different machines to establish, use and terminate a connection, called a session. Session support: performs the functions that allow these processes to communicate over the network, performing security, name recognition, logging, and so on. PRESENTATION LAYER The presentation layer formats the data to be presented to the application layer. It can be viewed as the translator for the network. This layer may translate data from a format used by the application layer into a common format at the sending station, then translate the common format to a format known to the application layer at the pg. 5 receiving station. The presentation layer provides: Character code translation: for example, ASCII to EBCDIC. Data conversion: bit order, CR-CR/LF, integer-floating point, and so on. Data compression: reduces the number of bits that need to be transmitted on the network. Data encryption: encrypt data for security purposes. For example, password encryption. APPLICATION LAYER The application layer serves as the window for users and application processes to access network services. This layer contains a variety of commonly needed functions: Resource sharing and device redirection Remote file access Remote printer access Inter-process communication Network management Directory services Electronic messaging (such as mail) Network virtual terminals TCP/IP Reference Model “TCP/IP” is the acronym that is commonly used for the set of network protocols that compose the Internet Protocol suite. Many texts use the term “Internet” to describe both the protocol suite and the global wide area network. In this book, “TCP/IP” refers specifically to the Internet protocol suite. “Internet” refers to the wide area network and the bodies that govern the Internet. OSI Ref. Layer No. OSI Layer Equivalent TCP/IP Layer TCP/IP Protocol Examples 5,6,7 Application, session, presentation Transport Network Data link Physical Application NFS, NIS, DNS, LDAP, telnet, ftp, rlogin, rsh, rcp, RIP, RDISC, SNMP, and others TCP, UDP, SCTP IPv4, IPv6, ARP, ICMP PPP, IEEE 802.2 Ethernet (IEEE 802.3), Token Ring, RS-232, FDDI, and others 4 3 2 1 Transport Internet Data link Physical network Physical Network Layer The physical network layer specifies the characteristics of the hardware to be used for the network. For example, physical network layer specifies the physical characteristics of the communications media. The physical layer of TCP/IP describes pg. 6 hardware standards such as IEEE 802.3, the specification for Ethernet network media, and RS-232, the specification for standard pin connectors. Data-Link Layer The data-link layer identifies the network protocol type of the packet, in this instance TCP/IP. The data-link layer also provides error control and “framing.” Examples of data-link layer protocols are Ethernet IEEE 802.2 framing and Point-to-Point Protocol (PPP) framing. Internet Layer The Internet layer, also known as the network layer or IP layer, accepts and delivers packets for the network. This layer includes the powerful Internet Protocol (IP), the Address Resolution Protocol (ARP), and the Internet Control Message Protocol (ICMP). IP Protocol The IP protocol and its associated routing protocols are possibly the most significant of the entire TCP/IP suite. IP is responsible for the following: IP addressing – The IP addressing conventions are part of the IP protocol. Designing an IPv4 Addressing Scheme introduces IPv4 addressing and IPv6 Addressing Overview introduces IPv6 addressing. Host-to-host communications – IP determines the path a packet must take, based on the receiving system's IP address. Packet formatting – IP assembles packets into units that are known as datagrams. Datagrams are fully described in Internet Layer: Where Packets Are Prepared for Delivery. Fragmentation – If a packet is too large for transmission over the network media, IP on the sending system breaks the packet into smaller fragments. IP on the receiving system then reconstructs the fragments into the original packet. Transport Layer The TCP/IP transport layer ensures that packets arrive in sequence and without error, by swapping acknowledgments of data reception, and retransmitting lost packets. This type of communication is known as end-to-end. Transport layer protocols at this level are Transmission Control Protocol (TCP), User Datagram Protocol (UDP), and Stream Control Transmission Protocol (SCTP). TCP and SCTP provide reliable, end-toend service. UDP provides unreliable datagram service. pg. 7 Application Layer The application layer defines standard Internet services and network applications that anyone can use. These services work with the transport layer to send and receive data. Many application layer protocols exist. The following list shows examples of application layer protocols: Standard TCP/IP services such as the ftp, tftp, and telnet commands Name services, such as NIS and the domain name system (DNS) File services, such as the NFS service Simple Network Management Protocol (SNMP), which enables network management Router Discovery Server protocol (RDISC) and Routing Information Protocol (RIP) routing protocols TCP VS UDP TCP UDP Acronym for Transmission Control Protocol Connection TCP is a connection-oriented protocol. As a message makes its way across the internet from one computer to another. This is connection based. User Datagram Protocol or Universal Datagram Protocol UDP is a connectionless protocol. Function Usage TCP is suited for applications that require high reliability, and transmission time is relatively less critical. Use by other protocols Ordering of data packets HTTP, HTTPs, FTP, SMTP, Telnet Speed of transfer The speed for TCP is slower than UDP. Reliability There is absolute guarantee that the data transferred remains intact and arrives in the same order in which it was sent. TCP header size is 20 bytes Source port, Destination port, Check Sum Data is read as a byte stream, no distinguishing indications are transmitted to signal message (segment) boundaries. Header Size Common Header Fields Streaming of data pg. 8 TCP rearranges data packets in the order specified. UDP is also a protocol used in message transport or transfer. This is not connection based which means that one program can send a load of packets to another and that would be the end of the relationship. UDP is suitable for applications that need fast, efficient transmission, such as games. UDP's stateless nature is also useful for servers that answer small queries from huge numbers of clients. DNS, DHCP, TFTP, SNMP, RIP, VOIP. UDP has no inherent order as all packets are independent of each other. If ordering is required, it has to be managed by the application layer. UDP is faster because there is no errorchecking for packets. There is no guarantee that the messages or packets sent would reach at all. UDP Header size is 8 bytes. Source port, Destination port, Check Sum Packets are sent individually and are checked for integrity only if they arrive. Packets have definite boundaries which are honored upon receipt, meaning a read operation at the receiver socket will yield an entire message as it was originally sent. Weight Error Checking TCP is heavy-weight. TCP requires three packets to set up a socket connection, before any user data can be sent. TCP handles reliability and congestion control. TCP does Flow Control. TCP requires three packets to set up a socket connection, before any user data can be sent. TCP handles reliability and congestion control. TCP does error checking Acknowledgement Acknowledgement segments Data Flow Control UDP is lightweight. There is no ordering of messages, no tracking connections, etc. It is a small transport layer designed on top of IP. UDP does not have an option for flow control UDP does error checking, but no recovery options. No Acknowledgment Internet Architecture Fortunately, nobody owns the Internet, there is no centralized control, and nobody can turn it off. Its evolution depends on rough consensus about technical proposals, and on running code. Engineering feed-back from real implementations is more important than any architectural principles. Backbone: A portion of a computer network that is capable of carrying the majority of traffic on the network at high speeds. The backbone often connects large networks or companies together. The first Internet backbone was between UCLA and SLI on October 29, 1969 and today the Internet consists of dozens of large backbones that carry the majority of traffic throughout the world. In the United States, many of these backbones are run by telecommunication companies such as AT&T, Bell South, Congent, Qwest, Level 3, MCI/Worldcom, Sprint, and Time Warner. In the above image, done by Donna Cox and Robert Patterson of the NCSA, is a visual representation of what an Internet backbone in the United States. This picture is of the NSFNET T1 backbone and the volume of traffic going over that network backbone for the month of September 1991. The color purple represents zero bytes of data, and the white represents 100 billion bytes of data. pg. 9 Without a network backbone, you would need to pass through dozens or even hundreds of different computer's and routers to get access to the computer storing what you need. If a network backbone goes down your Internet connection speed can be drastically reduced or may not even be able to get to certain places in the world. Internet Service Providers (ISPs) Short for Internet Service Provider, an ISP is a company that provides Internet access to users or subscribers of its service. An ISP gives you an Internet account (access to the Internet), e-mail address, web space for a web page for around $20.00 U.S. dollars a month. Prices may vary in other countries. Other services such as commercial online services like AOL allow access to proprietary features such as chat rooms, stocks, software, more support, and accessibility globally. However, may cost additional money. AOL, Earthlink, and MSN are just a few of the largest and well-known Internet service providers in the United States. ISP History The first ISP is widely believed to be Telenet, which was the first commercial version ofARPANET introduced in 1974. The first ISP for the Internet we know and use today is considered to be "The World" who started serving customers in 1989. Clients These are the computers at home of offices that are connected to local ISP’s. Internet Management It is often said that there is no central control, administration, or management of the Internet while this is generally true, there are several well-known organizations that work together in a relatively well structured and roughly democratic environment to collectively participate in the research development, and management of the Internet. Inter-relationships between these organizations are shown in the chart given below: pg. 10 Internet Soceity (ISOC) Area Director Internet Architecture Board (IAB) Internet Engineering Steering Group IESG Internet Engineering Task Force (IETF) Area Director Area Director Figure 1Internet Governance Hierarchy Internet Society (ISOC) The ISOC oversees the other Internet management organizations described in the following pages, and in some cases provides financial and other support. It also holds an annual International Networking conference, and coordinates Internet related public policy and trade activities, regional and local chapters, standardization activities, and an international secretariat. One of the most important legal activities of the ISOC is a defense of the free use of the word Internet ensuring that it remains a generic term that is not trademarked or owned by any Individual or corporation. Internet Architecture Board (IAB): In June, 1992, the Internet Activities Board was renamed the Internet Architecture Board by the Internet Society. The roles and responsibilities of the IAB are: Provide oversight of the Internet architecture, protocols, procedures, and standards, RFC (Request for Comment) management, IESG (Internet Engineering Steering Group) selection, IETF oversight etc. Internet Engineering Task Force (IETF): The IETF studies operational and technical problems with the Internet, specifies protocols and architectural solutions, and makes recommendations to its steering committee. Each area has one or two area directors. When an area director considers a problem important enough to merit concern, the IETF sets up a working group for further investigation. Types of Internet Connections pg. 11 While technology changes at a rapid pace, so do internet connections. The type of internet connection will determine how much time is spent for uploading or downloading i.e internet access speed. Different types of internet connections are compared according to their speed, cost and availability. Dial-up Connection • Once the most standard form of internet. • Uses telephone lines by the connection taking over the wire preventing one from making calls. -The common speeds were 14.4 kbps,28.8 kbps & 33.6 kbps & currently the fastest speed is 56 kbps ISDN • Integrated Service Digital Network. • Uses full digital signals over copper phone wire • Allows simultaneous voice and data communication • Provides 2-3 times the performance of dial up • Offers 2 types of rates Basic Rate Interface Primary Rate Interface • -ISDN offers connections ranging from 64 Kbps to 128 Kbps • Isn’t available everywhere • More common in metropolitan area DSL Digital Subscriber Line, DSL is a method for home users and small businesses to have high-speed access to the Internet over standard copper lines. Capable of receiving up to 6.1 megabits per second, DSL is a great solution if it is available in your area. Because of the technology used, DSL's availability depends on the user being within a certain distance from your phone company's CO. One of the most commonly used internet connection. Provides fast internet using phone line Connection can be shared using wired or wireless Main categories are: ADSL Asymmetric Digital Subscriber Line, ADSL is a form of DSL Broadband. ADSL is asymmetric because of its two-way bandwidth devoted to the pg. 12 downstream and a small section devoted to upstream transfers. The smaller upstream resulting in a higher download transfer rate, often up to 6.1 megabits per second. DSL DSL technology provides high-speed, broadband network connections to homes and small businesses. DSL utilizes the same cabling used for normal telephones but it can offer higher data rates through use of the digital modem technology DSL modems comprise the heart of this technology and the lines themselves are actually just plain telephone lines. Its possible for DSL subscribers to share the same line for their digital and analog traffic, play web + receive a call. Wireless Internet Connection Wireless Internet Connection makes use of radio frequency bands to connect to the internet and offers a very high speed. The wireless internet connection can be obtained by either Wi-Fi or Bluetooth. Wi-Fi wireless technology is based on IEEE 802.11 Standards which allow the electronic device to connect to the internet. Bluetooth wireless technology makes use of short wavelength radio waves and helps to create personal area network (PAN) URL Short for Uniform Resource Locator, a URL or Internet address is a form of URI (Uniform Resource Identifier) and is a standardized naming convention for addressing documents accessible over the Internet or Intranet. An example of a URL is http://www.nist.edu.np, which is the URL for the NIST College website. The components of URL are briefly discussed below: (a) Protocol (http): The http:// stands for Hypertext Transfer Protocol and enables the browser to know what protocol it is going to use to access the information specified in the domain. (b) Sub domain (www): WWW stands for World Wide Web, is used to distinguish the content. The World Wide Web is an information system of interlinked hypertext documents that are accessed via the Internet. It has also commonly become known simply as the Web. (c) Domain (nist.edu.np): A domain or domain name is the location of a website. For example, the domain name "nist.edu.np" points to the IP address "69.72.169.241", but it is easier to remember the NIST website is niste.du.np instead of trying to remember the IP address. (d) Directory (home): Directory is the folder or location where your overall web files and sub directories are managed. (e) Web Page (index.html): index.html is the actual web page on the domain viewing. The .htm is the file extension of the web page that indicates the file is an HTML file. pg. 13 Other common file extensions on the Internet include .php, .asp, .cgi, .xml, .jpg, and .gif. Addresses in the Internet Every Device attached in the internet must be identifiable uniquely. For this, we need to provide addresses to the devices attached in the internet. IP Address An IP address is a numbered address provided to computers and other devices attached to the internet to identify them uniquely. Two versions of the Internet Protocol (IP) are in use : IP Version 4 (IPv4) and IP Version 6 (IPv6). Because of its prevalence, the generic term IP address typically still refers to the addresses defined by IPV4. The gap in version sequence between IPv4 and IPv6 resulted from the assignment of number 5 to the experimental Internet Stream Protocol in 1979, which however was never referred to as IPv5. IP address can also be classified as private IP address or Public IP address. An IP address that can be accessed over the Internet is called public IP address. We need to pay for public IP addresses. On the other hand, a private IP address is any number or address assigned to a device on a private TCP/IP Local Area Network that is accessible only within the Local Area Network. It is available free of cost. IP Version 4(IPV4) IPV4 address consists of 32 bits and often shown as 4 octets of numbers from 0-255 represented in decimal. For example, the IP address: 168.212.226.204. Every IP address has two parts, one identifying the network and one identifying the node, or host. The Class of the address determines which part belongs to the network address and which part belongs to the host address. We can divide networks into five classes: --> Class A Network: In a Class A Network decimal number in first octet can be anywhere from 1 to 126. The first 8 bits (the first octet) identify the network and the remaining 24 bits indicate the host within the network. An example of a Class A IP address is 102.168.212.226, where "102" identifies the network and "168.212.226" identifies the host on that network. —> Class B Network: In a Class B Network the decimal number in first octet can be anywhere from 128 to '191. The number 127 is reserved for loopback and is used for internal testing on the local machine. The first 16 bits (the first two octets) identify the network and the remaining 16 bits indicate the host within the network. An example of a Class B IP address is 168.212.226.204 where "168.212" identifies the network and "226.204" identifies the host on that network. —> Class C Network: In a Class B Network decimal number in first octet can be anywhere from 192 to 223. The first 24 bits (the first three octets) identify the network and the remaining 8 bits indicate the host within the network. An example of a Class C IP address is 200.168.212.226 where "200.168.212" identifies the network and "226" identifies the host on that network. pg. 14 —> Class D Network: In a Class D Network, decimal number in first octet can be anywhere from 224 to 239. Class D networks are used to support multicasting. --> Class E Network: In a Class E Network, decimal number in first octet can be anywhere from 240 to 255. Class E networks are reserved for future use. IPv4 is the most widely deployed Internet protocol used to connect devices to the Internet. IPv4 uses a 32-bit address scheme allowing for a total of 232 addresses (just over 4 billion addresses). With the growth of the Internet it is expected that the number of unused IPv4 addresses will eventually run out because every device -including computers, smartphones and game consoles -- that connects to the Internet requires an address. IPv6 (Internet Protocol Version 6) A new Internet addressing system Internet Protocol version 6 (IPv6) is being deployed to fulfill the need for more Internet addresses. IPv6 addresses are 128-bit IP address written in hexadecimal and separated by colons. An example IPv6 address could be written like this: 3ffe:1900:4545:3:200f8fffe21:67cf. With IPV6 we can have up to 2128 (approximately3.403x1038) addresses. This is deemed sufficient for the foreseeable future. It is the successor to Internet Protocol Version 4 (IPv4). It was designed as an evolutionary upgrade to the Internet Protocol and will, in fact, coexist with the older IPv4 for some time. IPv6 is designed to allow the Internet to grow steadily, both in terms of the number of hosts connected and the total amount of data traffic transmitted. Domain Names IP addresses are difficult to remember. Domain Names are named addressed provided to the devices attached to the network. For example, www.google.com is an example of domain name. Domain Name Server (DNS) helps to resolve the host name to an address. It uses a hierarchical naming scheme and distributed database of IP addresses and associated names. The Domain name system comprises of Domain Names, Domain Name Space, and Name Servers. Domain Name is a symbolic string associated with an IP address. There are several domain names available; some of them are generic such as com, edu, gov, net etc, while some country level domain names such as .np, .au, .in, .us etc. pg. 15 Name server contains the DNS database. This database comprises of various names and their corresponding IP addresses. Since it is not possible for a single server to maintain entire DNS database, therefore, the information is distributed among many DNS servers. Hierarchy of server is same as hierarchy of names. Working of DNS User program requests IP address for a domain name Resolver module in local computer or ISP formulates query for local name server Local name server checks DNS database and cache, if found returns IP address to the requestor. If not found, queries name servers at next hop. When response is received, local name server stores the name/address mapping in local cache User program receives IP address or error message Internet Services Internet Services allows us to access huge amount of information such as text, graphics, sound and software over the internet Some of the services provided by internet are a. b. c. d. World wide Web (www) Information Retrieval Service Communication Services Web Services Uses of Internet Research The internet is a fantastic place to research information for a project or piece of homework. It doesn't matter what topic you have been set, you can guarantee that you will find something on the subject. Communication The internet opens up many different possible ways to communicate with others. Here are some: • Email • Chat Rooms • Blogs • Forums • Social networking sites e.g. Facebook, Myspace, Bebo • Voip - internet telephone Shopping Whatever you want to buy, you can pretty much guarantee that you can find it for sale somewhere on the internet. Find out more about ecommerce by reading the ecommerce theory section. pg. 16 Entertainment There are many different ways that you can choose to spend your time online and amuse yourself. Here are a few: • Playing online games • Listening to music (mp3 download or live streaming) • Reading online books and e-books • Watching online videos e.g. YouTube • Looking for holidays or concert tickets • Reading about your hobbies • Keeping up-to-date with the news and sporting events • Watching 'catch up' television from the main channels Exploring the world The internet has many services that help you explore the world. • Satellite and mapping applications e.g. Google Earth • Travel sites providing details of other places • Live web cams showing other parts of the world • Almanacs and encyclopedias pg. 17 Extra…. Number of Worldwide Internet Users According to Internet Live Stats, as of August 07, 2015 there was an estimated 3,179,035,200 Internet users worldwide. The number of Internet users represents nearly 40 percent of the world's population. The largest number of Internet users by country is China, followed by the United States and India. In September 2014, the total number of websites with a unique hostname online exceeded 1 billion. This is an increase from one website (info.cern.ch) in 1991. The first billion Internet users worldwide was reached in 2005. The Internet is decentralized Unlike online services, which are centrally controlled, by design, the Internet is decentralized. Each Internet computer, called a host, is independent. Operators can choose which Internet services to use and which local services to make available to the global Internet community. Remarkably, this anarchy by design works exceedingly well. There are a variety of ways to access the Internet. Most online services offer access to some Internet services. It is also possible to gain access through a commercial Internet Service Provider (ISP). Is Web and Internet the Same? The Internet is not synonymous with World Wide Web. The Internet is a massive network of networks, a networking infrastructure. It connects millions of computers together globally, forming a network in which any computer can communicate with any other computer as long as they are both connected to the Internet. The World Wide Web, or simply Web, is a way of accessing information over the medium of the Internet. It is an information-sharing model that is built on top of the Internet. Recommended Reading: The Difference Between the Internet and World Wide Web. Who Owns the Internet? No one actually owns the Internet, and no single person or organization controls the Internet in its entirety. The Internet is more of a concept than an actual tangible entity, and it relies on a physical infrastructure that connects networks to other networks. Short Answer Questions: 1. What is internet? Which switching technique it employs? Discuss working and evolution of internet briefly. 2. How intranet is different from simply private network? Differentiate intranet from extranet. 3. How internet is different from WWW? Explain different components of internet architecture with suitable diagram. 4. What are the different organizations involved in managing internet? Explain with suitable hierarchical diagram. pg. 18 5. What are different ways of connecting to internet? Explain each of them in your own word. 6. What is domain name and DNS? Explain importance and working of Domain Name Server (DNS) briefly. Long Answer Questions: 1. What are the different types of internet connections? Explain each of them in detail with diagram. 2. What is URL? List out its components. Discuss different addressing strategies used to identify devices attached in the internet. pg. 19