* Your assessment is very important for improving the work of artificial intelligence, which forms the content of this project
Download wireless - CSE Buffalo
Wireless security wikipedia , lookup
Recursive InterNetwork Architecture (RINA) wikipedia , lookup
Internet protocol suite wikipedia , lookup
List of wireless community networks by region wikipedia , lookup
Cracking of wireless networks wikipedia , lookup
Cellular network wikipedia , lookup
IEEE 802.11 wikipedia , lookup
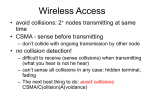
Introduction to Wireless Networking Dimitrios Koutsonikolas 02/01/2017 These slides contain material developed by Lili Qiu for CS386W at UT Austin and by J.F Kurose and K.W. Ross Internet Protocol Stack Application: supporting network applications FTP, SMTP, HTTP Transport: data transfer between processes TCP, UDP Network: routing of datagrams from source to destination IP, routing protocols Link: data transfer between neighboring network elements application transport network link physical Ethernet, WiFi Physical: bits “on the wire” Coaxial cable, optical fibers, radios 2 application transport Multiple Access Protocols network link physical Multiple Access protocols single shared broadcast channel two or more simultaneous transmissions by nodes: interference collision if node receives two or more signals at the same time multiple access protocol distributed algorithm that determines how nodes share channel, i.e., determine when node can transmit 4 Ideal Multiple Access Protocol Broadcast channel of rate R bps 1. when one node wants to transmit, it can send at rate R. 2. when M nodes want to transmit, each can send at average rate R/M 3. fully decentralized: no special node to coordinate transmissions no synchronization of clocks, slots 4. simple 5 MAC Protocols: a taxonomy Three broad classes: Channel Partitioning divide channel into smaller “pieces” (time slots, frequency, code) allocate piece to node for exclusive use Random Access channel not divided, allow collisions “recover” from collisions “Taking turns” nodes take turns, but nodes with more to send can take longer turns 6 Channel Partitioning MAC protocols: TDMA TDMA: time division multiple access access to channel in "rounds" each station gets fixed length slot (length = pkt trans time) in each round unused slots go idle example: 6-station LAN, 1,3,4 have pkt, slots 2,5,6 idle 6-slot frame 1 3 4 1 3 4 7 Channel Partitioning MAC protocols: FDMA FDMA: frequency division multiple access channel spectrum divided into frequency bands each station assigned fixed frequency band unused transmission time in frequency bands go idle example: 6-station LAN, 1,3,4 have pkt, frequency FDM cable frequency bands bands 2,5,6 idle 8 Random Access Protocols When node has packet to send transmit at full channel data rate. Two or more transmitting nodes ➜ “collision”, Random access MAC protocol specifies: how to detect collisions how to prevent collisions how to recover from collisions (e.g., via delayed retransmissions) Examples of random access MAC protocols: slotted ALOHA ALOHA CSMA, CSMA/CD, CSMA/CA 9 CSMA (Carrier Sense Multiple Access) CSMA: listen before transmit: If channel sensed idle: transmit entire frame If channel sensed busy, defer transmission human analogy: don’t interrupt others! 10 CSMA collisions spatial layout of nodes collisions can still occur: propagation delay means two nodes may not hear each other’s transmission collision: entire packet transmission time wasted note: role of distance & propagation delay in determining collision probability 11 CSMA/CD (Collision Detection) CSMA/CD: carrier sensing, deferral as in CSMA collisions detected within short time colliding transmissions aborted, reducing channel wastage Collision detection: easy in wired LANs: measure signal strengths, compare transmitted, received signals difficult in wireless LANs: received signal strength overwhelmed by local transmission strength 12 application transport PHY Layer network link physical 13 Wireless Link Characteristics Wireless is a broadcast medium! Differences from wired link …. signal strength: radio signal attenuates as it propagates through matter (path loss) interference from other sources: standardized wireless network frequencies (e.g., 2.4 GHz) shared by other devices (e.g., phone); devices (motors, microwaves) interfere as well space multipath propagation (fading): radio signal reflects off objects or ground, arriving at destination at slightly different times Signal Strength decreased • Reflection • Diffraction • Scattering 14 Impact of Multipath Propagation Direct signal Reflected signal Received signal 15 Wireless Link Characteristics (2) – Fading • Channel characteristics change over time and location – e.g., movement of sender, receiver and/or scatters • • quick changes in the power received (short term/fast fading) slow changes in the average power received (long term/slow fading) power short term fading long term fading t 16 Typical Picture Received Signal Power (dBm) path loss slow fading fast fading log (distance) 20 Signal Propagation Ranges • Transmission range – communication possible – low error rate • Detection range – detection of the signal possible – no communication possible • Interference range – signal may not be detected – signal adds to the background noise sender transmission distance detection interference 18 Signal, Noise, and Interference Signal (S) Noise (N) Includes thermal noise and background radiation Interference (I) Signals from other transmitting sources SINR = S/(N+I) (sometimes also denoted as SNR) Large SINR = easier to extract signal from noise 19 dB and Power conversion dB Denote the difference between two power levels (P2/P1)[dB] = 10 * log10 (P2/P1) 10dB: factor of 10 P2/P1 = 10^(A/10) 3dB: factor of 2 Example 1: P2 = 10 P1, P2/P1=10dB Example 2: P2/P1 = 33dB, P2 = 2000 P1 dBm and dBW Denote the power level relative to 1 mW or 1 W P[dBm] = 10*log10(P/1mW) P[dBW] = 10*log10(P/1W) Example: P = 0.001mW = -30dBm, P = 100W = 20dBW 20 Wireless Link Characteristics (3) SNR: signal-to-noise ratio larger SNR – easier to extract signal from noise 10-2 10-3 BER SNR versus BER tradeoffs given physical layer: increase power -> increase SNR>decrease BER given SNR: choose physical layer that meets BER requirement, giving highest throughput 10-1 10-4 10-5 10-6 10-7 10 20 30 40 SNR(dB) QAM256 (8 Mbps) QAM16 (4 Mbps) BPSK (1 Mbps) 21 Rate Adaptation base station, mobile 1. SNR decreases, BER increase as node moves away from base station 10-2 10-3 BER dynamically change transmission rate (physical layer modulation technique) as mobile moves, SNR varies 10-1 10-4 10-5 10-6 10-7 10 20 30 SNR(dB) 40 QAM256 (8 Mbps) QAM16 (4 Mbps) BPSK (1 Mbps) operating point 2. When BER becomes too high, switch to lower transmission rate but with lower BER 22 IEEE 802.11 multiple access 802.11: CSMA - sense before transmitting Differences from Ethernet No collision detection (CD)! • Difficult to receive (sense collisions) when transmitting due to weak received signals (fading) • Can’t sense all collisions in any case: hidden terminal, fading • Goal: avoid collisions: CSMA/C(ollision)A(voidance) Link layer ACKnowledgments/Retransmissions (ARQ) • High bit error rates A C A B B C C’s signal strength A’s signal strength space 23 IEEE 802.11 MAC Protocol: CSMA/CA 802.11 sender 1 if sense channel idle for DIFS then transmit entire frame (no CD) sender 2 if sense channel busy then 2.1 start random backoff time DIFS timer counts down while channel idle, freezes when busy, resumes if idle for DIFS transmit when timer expires (why?) 3 if ACK, wait for DIFS, then go to 2.1 (why?) 4 if no ACK, increase random backoff interval, goto 2.1 (why?) receiver data SIFS ACK 802.11 receiver - if frame received OK return ACK after SIFS (ACK needed due to hidden terminal problem) 24 802.11 Backoff Example 25 802.11 Backoff Example After 15 slot countdown 26 802.11 Backoff Example 27 802.11 Backoff Example 28 802.11 Backoff Example 29 802.11 Backoff Example 30 Avoiding collisions (more) idea: allow sender to “reserve” channel rather than random access of data frames: avoid collisions of long data frames sender first transmits small request-to-send (RTS) packets to BS using CSMA RTSs may still collide with each other (but they’re short) BS broadcasts clear-to-send CTS in response to RTS CTS heard by all nodes sender transmits data frame other stations defer transmissions avoid data frame collisions completely using small reservation packets! 31 Collision Avoidance: RTS-CTS exchange A AP B reservation collision DATA (A) defer time 32 Wireless, mobility: impact on higher layer protocols logically, impact should be minimal … best effort service model remains unchanged TCP and UDP can (and do) run over wireless, mobile … but performance-wise: packet loss/delay due to bit-errors (discarded packets, delays for link-layer retransmissions), and handoff TCP interprets loss as congestion, will decrease congestion window un-necessarily delay impairments for real-time traffic limited bandwidth of wireless links 33