GoldMine 6.7 Administrator Guide
... A remote user accessing the Licensed Software (via a web-enabled product) is considered to be utilizing one concurrent user license. Nothing in this paragraph shall limit Licensee from allowing its employees, agents or representatives or the employees, agents or representatives of Licensee’s parent, ...
... A remote user accessing the Licensed Software (via a web-enabled product) is considered to be utilizing one concurrent user license. Nothing in this paragraph shall limit Licensee from allowing its employees, agents or representatives or the employees, agents or representatives of Licensee’s parent, ...
Administrator Guide
... A remote user accessing the Licensed Software (via a web-enabled product) is considered to be utilizing one concurrent user license. Nothing in this paragraph shall limit Licensee from allowing its employees, agents or representatives or the employees, agents or representatives of Licensee’s parent, ...
... A remote user accessing the Licensed Software (via a web-enabled product) is considered to be utilizing one concurrent user license. Nothing in this paragraph shall limit Licensee from allowing its employees, agents or representatives or the employees, agents or representatives of Licensee’s parent, ...
Teradata Schema Workbench User Guide
... WebAnalyst, and Xkoto are trademarks or registered trademarks of Teradata Corporation or its affiliates in the United States and other countries. Adaptec and SCSISelect are trademarks or registered trademarks of Adaptec, Inc. AMD Opteron and Opteron are trademarks of Advanced Micro Devices, Inc. Apa ...
... WebAnalyst, and Xkoto are trademarks or registered trademarks of Teradata Corporation or its affiliates in the United States and other countries. Adaptec and SCSISelect are trademarks or registered trademarks of Adaptec, Inc. AMD Opteron and Opteron are trademarks of Advanced Micro Devices, Inc. Apa ...
Sistemas de Datos - Algebra relacional
... XML store. SQL/XML extensions enable publishing relational data in XML format based on data retrieved by embedding XPath or XQuery into SQL statements. XML applications typically use XQuery to access the XML store; yet XQuery queries can optionally contain SQL to combine and correlate XML with relat ...
... XML store. SQL/XML extensions enable publishing relational data in XML format based on data retrieved by embedding XPath or XQuery into SQL statements. XML applications typically use XQuery to access the XML store; yet XQuery queries can optionally contain SQL to combine and correlate XML with relat ...
Technical Standard DRDA, Version 2, Volume 1
... December 1999, The Open Group All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, without the prior permission of the copyright owners. This doc ...
... December 1999, The Open Group All rights reserved. No part of this publication may be reproduced, stored in a retrieval system, or transmitted, in any form or by any means, electronic, mechanical, photocopying, recording or otherwise, without the prior permission of the copyright owners. This doc ...
Oracle Database Administrator`s Reference for Linux and UNIX
... Swonger, Douglas Williams, Joseph Therrattil Koonen, Binoy Sukumaran, and Sumanta Chatterjee. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in ...
... Swonger, Douglas Williams, Joseph Therrattil Koonen, Binoy Sukumaran, and Sumanta Chatterjee. This software and related documentation are provided under a license agreement containing restrictions on use and disclosure and are protected by intellectual property laws. Except as expressly permitted in ...
IBM Lotus Enterprise Integrator for Domino (LEI) Activities and User
... Contents Preface . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi ...
... Contents Preface . . . . . . . . . . . . . . . . . . . . . . . . . . . . xi ...
DS-Client User Guide
... Correct Input: User enters the correct data (e.g. user names, passwords, etc.) when asked or required. If invalid data is entered, an error message will appear, and you will be forced to correct the error before you may proceed. Canceling activities: The option to cancel the current activity (in som ...
... Correct Input: User enters the correct data (e.g. user names, passwords, etc.) when asked or required. If invalid data is entered, an error message will appear, and you will be forced to correct the error before you may proceed. Canceling activities: The option to cancel the current activity (in som ...
A Practical Guide to DB2 UDB Data Replication V8 Front cover
... International Technical Support Organization A Practical Guide to DB2 UDB Data Replication V8 December 2002 ...
... International Technical Support Organization A Practical Guide to DB2 UDB Data Replication V8 December 2002 ...
DataStage DB2 Parallel Configuration
... The connectivity scenario for a DataStage DB2 Enterprise stage is: 1) The DataStage conductor node uses the DB2 environment variable APT_DB2INSTANCE_HOME as the location on the ETL and DB2 servers where the remote DB2 server's db2nodes.cfg is located (it needs to be copied to the DataStage conductor ...
... The connectivity scenario for a DataStage DB2 Enterprise stage is: 1) The DataStage conductor node uses the DB2 environment variable APT_DB2INSTANCE_HOME as the location on the ETL and DB2 servers where the remote DB2 server's db2nodes.cfg is located (it needs to be copied to the DataStage conductor ...
for IBM z/OS (OS/390)
... Backup and Recovery without Recovery Manager............................................................................ Recovery Manager on z/OS .................................................................................................................... ...
... Backup and Recovery without Recovery Manager............................................................................ Recovery Manager on z/OS .................................................................................................................... ...
SAP HANA Multitenant Database Containers
... When planning an SAP HANA MDC deployment, various options exist with regard to scale-up versus scale-out. In general, scaling up offers some performance advantages over scaling out, as memory access is local and minor overhead associated with inter-node network communication is avoided. Note the fol ...
... When planning an SAP HANA MDC deployment, various options exist with regard to scale-up versus scale-out. In general, scaling up offers some performance advantages over scaling out, as memory access is local and minor overhead associated with inter-node network communication is avoided. Note the fol ...
XML Extender Administration and Programming DB2 Universal Database for OS/390 and z/OS
... How to use this book This book is structured as follows: Part 1. Introduction This part provides an overview of the XML Extender and how you can use it in your business applications. It contains a getting-started scenario that helps you get up and running. Part 2. Administration This part describes ...
... How to use this book This book is structured as follows: Part 1. Introduction This part provides an overview of the XML Extender and how you can use it in your business applications. It contains a getting-started scenario that helps you get up and running. Part 2. Administration This part describes ...
DB2 UDB Evaluation Guide for Linux and Windows Front cover
... 5.5.6 Visual Basic (Windows only) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 188 5.5.7 Visual C++ and Visual J++ (Windows only) . . . . . . . . . . . . . . . . . . 189 5.5.8 Object REXX (Windows only) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 189 5.6 DB2 scripting in ...
... 5.5.6 Visual Basic (Windows only) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 188 5.5.7 Visual C++ and Visual J++ (Windows only) . . . . . . . . . . . . . . . . . . 189 5.5.8 Object REXX (Windows only) . . . . . . . . . . . . . . . . . . . . . . . . . . . . . 189 5.6 DB2 scripting in ...
[1 ] Oracle® GoldenGate
... 1.2.1 Memory Requirements The amount of memory that is required for Oracle GoldenGate depends on the number of concurrent processes that will be running. At minimum on the source system, there is a primary Extract process that captures source data and a secondary Extract data-pump process that trans ...
... 1.2.1 Memory Requirements The amount of memory that is required for Oracle GoldenGate depends on the number of concurrent processes that will be running. At minimum on the source system, there is a primary Extract process that captures source data and a secondary Extract data-pump process that trans ...
Oracle to DB2 Conversion Guide for Linux, UNIX, and Windows Front cover
... Conversion Guide for Linux, UNIX, and Windows Step-by-step guide to migrating from Oracle to DB2 9.1 ...
... Conversion Guide for Linux, UNIX, and Windows Step-by-step guide to migrating from Oracle to DB2 9.1 ...
Oracle Rdb™ SQL Reference Manual Volume 3
... A cache for a given sequence is populated at the first request for a number from that sequence, and whenever a value is requested when the cache is empty. If a system failure occurs, or when the cache is released any unfetched values will be discarded. The maximum number of lost values is equal to t ...
... A cache for a given sequence is populated at the first request for a number from that sequence, and whenever a value is requested when the cache is empty. If a system failure occurs, or when the cache is released any unfetched values will be discarded. The maximum number of lost values is equal to t ...
View this book as PDF
... This publication pertains to Sybase software and to any subsequent release until otherwise indicated in new editions or technical notes. Information in this document is subject to change without notice. The software described herein is furnished under a license agreement, and it may be used or copie ...
... This publication pertains to Sybase software and to any subsequent release until otherwise indicated in new editions or technical notes. Information in this document is subject to change without notice. The software described herein is furnished under a license agreement, and it may be used or copie ...
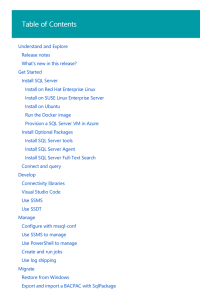
Install SQL Server on Linux
... The following limitations apply to SSMS on Windows connected to SQL Server on Linux. Maintenance plans are not supported. Management Data Warehouse (MDW) and the data collector in SSMS is not supported. SSMS UI components that have Windows Authentication or Windows event log options do not work with ...
... The following limitations apply to SSMS on Windows connected to SQL Server on Linux. Maintenance plans are not supported. Management Data Warehouse (MDW) and the data collector in SSMS is not supported. SSMS UI components that have Windows Authentication or Windows event log options do not work with ...
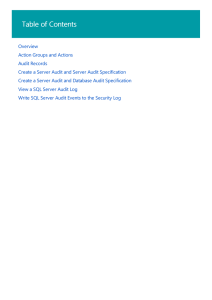
SQL Server Audit (Database Engine) | Microsoft Docs
... setting can be configured by using the security policy snap-in (secpol.msc). Additionally, the Audit object access security policy must be enabled for both Success and Failure. This setting can be configured by using the security policy snap-in (secpol.msc). In Windows Vista or Windows Server 2008, ...
... setting can be configured by using the security policy snap-in (secpol.msc). Additionally, the Audit object access security policy must be enabled for both Success and Failure. This setting can be configured by using the security policy snap-in (secpol.msc). In Windows Vista or Windows Server 2008, ...
Accessing External Databases from RPG
... • Provide a means for Java (and RPG!) code to access a database • Access is done through SQL statements • SQL statements can do most anything: • Read data bases (SELECT statement) • Update (UPDATE statement) • Add new records (INSERT statement) • Create new databases, tables, indexes, views (CREATE ...
... • Provide a means for Java (and RPG!) code to access a database • Access is done through SQL statements • SQL statements can do most anything: • Read data bases (SELECT statement) • Update (UPDATE statement) • Add new records (INSERT statement) • Create new databases, tables, indexes, views (CREATE ...
Web 2.0 samples for accessing DB2 on February 2009
... supplementary ISO image as software repositories. Also, the latest available security updates must have been applied to the system. As required by any application, a specific environment must be set up. Also for a database application, the setup of some components must be in place before installatio ...
... supplementary ISO image as software repositories. Also, the latest available security updates must have been applied to the system. As required by any application, a specific environment must be set up. Also for a database application, the setup of some components must be in place before installatio ...







![[1 ] Oracle® GoldenGate](http://s1.studyres.com/store/data/016247400_1-b9822c910f160907aa6f93e415358df1-300x300.png)