Chapter 20: Database System Architectures
... Distributed concurrency control (and deadlock detection) required ...
... Distributed concurrency control (and deadlock detection) required ...
Grid Database Projects Paul Watson, Newcastle Norman Paton, Manchester
... Goldrush & Polar Parallel Database Server Projects ...
... Goldrush & Polar Parallel Database Server Projects ...
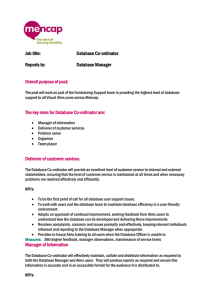
draft proposal for area services manager
... Makes recommendations of how the Alms database or processes could be improved or where cost saving might be made ...
... Makes recommendations of how the Alms database or processes could be improved or where cost saving might be made ...
September 2014 report
... Permission to access is determined by referencing group membership to building. Each unique logaccess monitors both success and denial based on an individual persons membership of a group. Hence :o Entity PIDCardReader – it would be useful to add an attribute say readertype or status. o The Rela ...
... Permission to access is determined by referencing group membership to building. Each unique logaccess monitors both success and denial based on an individual persons membership of a group. Hence :o Entity PIDCardReader – it would be useful to add an attribute say readertype or status. o The Rela ...
Chapter 4: Introduction to Transaction Processing Concepts and
... Come up with methods (protocols) to ensure serializability. It’s not possible to determine when a schedule begins and when it ends. Hence, we reduce the problem of checking the whole schedule to checking only a committed project of the schedule (i.e. operations from only the committed transactio ...
... Come up with methods (protocols) to ensure serializability. It’s not possible to determine when a schedule begins and when it ends. Hence, we reduce the problem of checking the whole schedule to checking only a committed project of the schedule (i.e. operations from only the committed transactio ...
Introduction to Transaction Processing Concepts and Theory
... The updated item is accessed by another transaction before it is changed back to its original value. ...
... The updated item is accessed by another transaction before it is changed back to its original value. ...
(A) write_item (B)
... Recovery in multidatabase system A multidatabase system is a special distributed database system where one node may be running relational database system under Unix, another may be running objectoriented system under window and so on. In this execution scenario the transaction commits only when ...
... Recovery in multidatabase system A multidatabase system is a special distributed database system where one node may be running relational database system under Unix, another may be running objectoriented system under window and so on. In this execution scenario the transaction commits only when ...
IsolationLevels_-_UnderstandingTransactionTemperTantrums
... Tempdb is affected by the version store RCSI provides a snapshot view of the committed data when the statement started This can be a problem in long running queries when comparisons need to be made on the data set, and an update to the data set occurs in another query ...
... Tempdb is affected by the version store RCSI provides a snapshot view of the committed data when the statement started This can be a problem in long running queries when comparisons need to be made on the data set, and an update to the data set occurs in another query ...
Distributed and Parallel Database Systems
... 3. The distribution (including fragmentation and replication) of data across multiple site/processors is not visible to the users. This is called transparency. The distributed/parallel database technology extends the concept of data independence, which is a central notion of database management, to ...
... 3. The distribution (including fragmentation and replication) of data across multiple site/processors is not visible to the users. This is called transparency. The distributed/parallel database technology extends the concept of data independence, which is a central notion of database management, to ...
Relational Databases - PersonalWebIWayanSW
... Data can be placed in many distributed databases. Databases can be found in the same or different computer systems. ...
... Data can be placed in many distributed databases. Databases can be found in the same or different computer systems. ...
Ch17: concurency control
... Each Xact must obtain a S (shared) lock on object before reading, and an X (exclusive) lock on object before writing. All locks held by a transaction are released when the transaction completes ...
... Each Xact must obtain a S (shared) lock on object before reading, and an X (exclusive) lock on object before writing. All locks held by a transaction are released when the transaction completes ...
Powerpoint slides - Dynamic Connectome Lab
... nightly is common The log is stored on a different disk to the database ...
... nightly is common The log is stored on a different disk to the database ...
ADM5 File
... The updated item is accessed by another transaction before it is changed back to its original value. ...
... The updated item is accessed by another transaction before it is changed back to its original value. ...
lecture06
... • Database systems are normally being accessed by many users or processes at the same time. – Both queries and modifications. • Unlike operating systems, which support interaction of processes, a DMBS needs to keep processes from troublesome interactions. ...
... • Database systems are normally being accessed by many users or processes at the same time. – Both queries and modifications. • Unlike operating systems, which support interaction of processes, a DMBS needs to keep processes from troublesome interactions. ...
Fault-Tolerance in Real
... Self-repair: If a node fails completely, data is copied from the complementary node to standby. This is also automatic and transparent. Limited failure effects ...
... Self-repair: If a node fails completely, data is copied from the complementary node to standby. This is also automatic and transparent. Limited failure effects ...
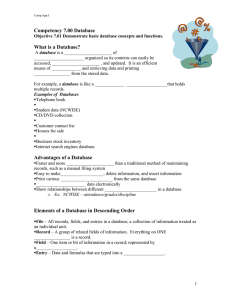
Competency 7.00 Database What is a Database? Advantages of a
... •Determine the _______________________ of fields. Step 1−Plan and Design the Database Determine the ____________________ of the database file. Include all fields necessary to ensure efficient _____________________- and retrieving of specified data. Project how the fields may be __________________ ...
... •Determine the _______________________ of fields. Step 1−Plan and Design the Database Determine the ____________________ of the database file. Include all fields necessary to ensure efficient _____________________- and retrieving of specified data. Project how the fields may be __________________ ...
Transaction Processing
... Suppose that transaction Ti tries to lock an item X but is not able to because X is locked by some other transaction Tj with a conflicting lock. Wait-die: if TS(Ti)
... Suppose that transaction Ti tries to lock an item X but is not able to because X is locked by some other transaction Tj with a conflicting lock. Wait-die: if TS(Ti)
Transaction Services - MicroStrategy Community
... After you map the query and transaction objects and define the user interface in the document or dashboard, you need to enable users to submit their changes to the back end system. You do this by creating a new selector – an Action selector button or an Action Selector Link When you define the new a ...
... After you map the query and transaction objects and define the user interface in the document or dashboard, you need to enable users to submit their changes to the back end system. You do this by creating a new selector – an Action selector button or an Action Selector Link When you define the new a ...
Chapter 14: Concurrency Control
... A transaction is structured such that its writes are all performed at the end of its processing All writes of a transaction form an atomic action; no transaction may execute while a transaction is being written A transaction that aborts is restarted with a new timestamp ...
... A transaction is structured such that its writes are all performed at the end of its processing All writes of a transaction form an atomic action; no transaction may execute while a transaction is being written A transaction that aborts is restarted with a new timestamp ...
Overview of the Benefits and Costs of Integrating
... by using countermeasures against the isolation anomalies. If there is no isolation and the atomicity property is implemented, the following isolation anomalies may occur [1 and 2]. The lost update anomaly is by definition a situation where a first transaction reads a record for update without usin ...
... by using countermeasures against the isolation anomalies. If there is no isolation and the atomicity property is implemented, the following isolation anomalies may occur [1 and 2]. The lost update anomaly is by definition a situation where a first transaction reads a record for update without usin ...
PGS99
... Software replication is considered a cheap way to increase data availability when compared to hardware based techniques [16]. However, designing a replication scheme that provides synchronous replication (i.e., all copies are kept consistent) at good performance is still an active area of research b ...
... Software replication is considered a cheap way to increase data availability when compared to hardware based techniques [16]. However, designing a replication scheme that provides synchronous replication (i.e., all copies are kept consistent) at good performance is still an active area of research b ...
Database System Concepts, 6 th Ed
... Durability requirement — once the user has been notified that the transaction has completed (i.e., the transfer of the $50 has taken place), the updates to the database by the transaction must persist even if there are software or hardware failures. ...
... Durability requirement — once the user has been notified that the transaction has completed (i.e., the transfer of the $50 has taken place), the updates to the database by the transaction must persist even if there are software or hardware failures. ...
Chapter 16: Concurrency Control Lock-Based Protocols Lock
... TimestampTimestamp-Based Protocols ! Each transaction is issued a timestamp when it enters the system. If ...
... TimestampTimestamp-Based Protocols ! Each transaction is issued a timestamp when it enters the system. If ...
Semantic Consistency in Information Exchange
... 1. Use two lists of transactions maintained by the system: the committed transactions since the last checkpoint and the active transactions. 2. Undo all the write_item operations of the active (uncommitted) transactions, using the UNDO procedure. The operations should be undone in the reverse of the ...
... 1. Use two lists of transactions maintained by the system: the committed transactions since the last checkpoint and the active transactions. 2. Undo all the write_item operations of the active (uncommitted) transactions, using the UNDO procedure. The operations should be undone in the reverse of the ...
DBCache: Database Caching For Web Application Servers*
... shallow parser to detect their types. If the query is read-only and the currency setting allows reading stale data, the query is executed locally. In this case, if the query involves nicknames, then existing federated query processing takes over and distributed query plans are selected based on cost ...
... shallow parser to detect their types. If the query is read-only and the currency setting allows reading stale data, the query is executed locally. In this case, if the query involves nicknames, then existing federated query processing takes over and distributed query plans are selected based on cost ...