![New Sample Questions for CS 6371 (APL) [added 11/1/08]](http://s1.studyres.com/store/data/008815993_1-c5313aea2b9de70fc6d06120eccb7a8a-300x300.png)
New Sample Questions for CS 6371 (APL) [added 11/1/08]
... Consider an SQL like relational database programming language. Programs in this language manipulate a relational database. A relational database (RDB) stores a table (collection of tuples) for each relation name. Thus, each relation can be regarded as a collection of tuples. (12 pts) Define a semant ...
... Consider an SQL like relational database programming language. Programs in this language manipulate a relational database. A relational database (RDB) stores a table (collection of tuples) for each relation name. Thus, each relation can be regarded as a collection of tuples. (12 pts) Define a semant ...
NVCC COLLEGE-WIDE COURSE CONTENT SUMMARY
... a) Explain how database principles may be applied as a part of the IT solution b) Draw an ERD to represent the pertinent user data c) Transform the ERD into a 3NF relational model d) Write the necessary SQL to create the database structures (CREATE and INSERT) e) Write the necessary SQL to manipulat ...
... a) Explain how database principles may be applied as a part of the IT solution b) Draw an ERD to represent the pertinent user data c) Transform the ERD into a 3NF relational model d) Write the necessary SQL to create the database structures (CREATE and INSERT) e) Write the necessary SQL to manipulat ...
(PPT, 183KB)
... databases, Microsoft favors the term distributed query, which it defines in protocol-specific manner as "[a]ny SELECT, INSERT, UPDATE, or DELETE statement that references tables and rowsets from one or more external OLE DB data sources". Oracle provides a more language-centric view in which distribu ...
... databases, Microsoft favors the term distributed query, which it defines in protocol-specific manner as "[a]ny SELECT, INSERT, UPDATE, or DELETE statement that references tables and rowsets from one or more external OLE DB data sources". Oracle provides a more language-centric view in which distribu ...
Enabling Database-as-a-Service (DBaaS) within Enterprises or
... architecture in which an application supports multi-tenancy and can scale with the addition of more application servers behind a web load balancer or Application Delivery Controller. Databases, in contrast, remain deployed in support of a single application. Building a DBaaS offering is extremely co ...
... architecture in which an application supports multi-tenancy and can scale with the addition of more application servers behind a web load balancer or Application Delivery Controller. Databases, in contrast, remain deployed in support of a single application. Building a DBaaS offering is extremely co ...
Distributed Databases
... Application makes request to distributed DBMS. Distributed DBMS checks distributed data repository for location of data. Finds that it is remote. Distributed DBMS routes request to remote site. Distributed DBMS at remote site translates request for its local DBMS if necessary, and sends request to l ...
... Application makes request to distributed DBMS. Distributed DBMS checks distributed data repository for location of data. Finds that it is remote. Distributed DBMS routes request to remote site. Distributed DBMS at remote site translates request for its local DBMS if necessary, and sends request to l ...
Chapter 6: Database Recovery Techniques.
... 10 Recovery in multidatabase system A multidatabase system is a special distributed database system where one node may be running relational database system under Unix, another may be running object-oriented system under Window and so on. A transaction may run in a distributed fashion at multiple no ...
... 10 Recovery in multidatabase system A multidatabase system is a special distributed database system where one node may be running relational database system under Unix, another may be running object-oriented system under Window and so on. A transaction may run in a distributed fashion at multiple no ...
Database Administration
... Submission: Drop Box by 11:59pm local time Return : within a week from due date Amended late policy: ...
... Submission: Drop Box by 11:59pm local time Return : within a week from due date Amended late policy: ...
PPT - Ajay Ardeshana
... changes in the database since the copy was taken, in the same order that these transactions were originally executed. This brings the database copy to the up-to-date level of the database that was destroyed. ...
... changes in the database since the copy was taken, in the same order that these transactions were originally executed. This brings the database copy to the up-to-date level of the database that was destroyed. ...
Chapter 2
... data types, and the constraints on the database. An illustrative display of (most aspects of) a database schema. ...
... data types, and the constraints on the database. An illustrative display of (most aspects of) a database schema. ...
Advanced Databases
... Distributed database management system (DDBMS) is a software system that manages a distributed database in such a way that the system of distributed systems transparent to users • DDBMS includes n local DBMS's. • Each local DBMS, labelled Si, (i = 1, ..., n) represents a single node (site, node) of ...
... Distributed database management system (DDBMS) is a software system that manages a distributed database in such a way that the system of distributed systems transparent to users • DDBMS includes n local DBMS's. • Each local DBMS, labelled Si, (i = 1, ..., n) represents a single node (site, node) of ...
EMES Course Plan
... records and report absences. Due to the interactive nature of this course, attendance is an essential part of the educational experience. JCC expects students to exercise good judgment regarding attendance. Students accept full responsibility for ensuring that work does not suffer from absence. Punc ...
... records and report absences. Due to the interactive nature of this course, attendance is an essential part of the educational experience. JCC expects students to exercise good judgment regarding attendance. Students accept full responsibility for ensuring that work does not suffer from absence. Punc ...
Download-6 PHYSICALDBtcss545A_9
... – updating a secondary index when corresponding tuple is updated; – increase in disk space needed to store the secondary index; – possible performance degradation during query optimization to consider all secondary indexes. ...
... – updating a secondary index when corresponding tuple is updated; – increase in disk space needed to store the secondary index; – possible performance degradation during query optimization to consider all secondary indexes. ...
Online transaction processing, or OLTP, refers to a class of systems
... for transactions that span a network and may include more than one company. For this reason, new OLTP software uses client/server processing and brokering software that allows transactions to run on different computer platforms in a network. A system consisting of interconnected computers that share ...
... for transactions that span a network and may include more than one company. For this reason, new OLTP software uses client/server processing and brokering software that allows transactions to run on different computer platforms in a network. A system consisting of interconnected computers that share ...
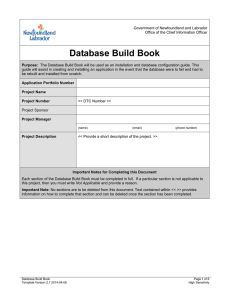
Database Build Book - Office of the Chief Information Officer
... guide will assist in creating and installing an application in the event that the database were to fail and had to be rebuilt and installed from scratch. Application Portfolio Number Project Name Project Number ...
... guide will assist in creating and installing an application in the event that the database were to fail and had to be rebuilt and installed from scratch. Application Portfolio Number Project Name Project Number ...
Chapter 4
... • Relationships – Primary key: a column or group of columns to identify a unique row in a table – Foreign key: a non-key column or field in one table that links to a primary key in another table ...
... • Relationships – Primary key: a column or group of columns to identify a unique row in a table – Foreign key: a non-key column or field in one table that links to a primary key in another table ...
Logical structure of a transaction
... Within ‘invoke’ chaincode, rich query can be used to identify keys (documents) to update Two limitations to be aware of: – Cannot Query/Write, and then Re-Query in the same transaction, since the simulation results are not in the DB yet. – The endorser/committer architecture cannot prevent phantom r ...
... Within ‘invoke’ chaincode, rich query can be used to identify keys (documents) to update Two limitations to be aware of: – Cannot Query/Write, and then Re-Query in the same transaction, since the simulation results are not in the DB yet. – The endorser/committer architecture cannot prevent phantom r ...
Chapter 3
... Chapter 3: Hands-on Activity – Relational Database System The database consists of a group of programs that can be used as an interface between a database and the user of the database and application programs. The software acts as a buffer between the application programs and the database itself. In ...
... Chapter 3: Hands-on Activity – Relational Database System The database consists of a group of programs that can be used as an interface between a database and the user of the database and application programs. The software acts as a buffer between the application programs and the database itself. In ...
Databases and Enterprise Java Beans
... – Not supported – if there is a transaction, don’t participate in it, do outside transactions – Required – use existing transaction, if no existing, create new – Requires new – create a separate transaction, even if there is ...
... – Not supported – if there is a transaction, don’t participate in it, do outside transactions – Required – use existing transaction, if no existing, create new – Requires new – create a separate transaction, even if there is ...
Here - Emunix Emich
... Redo phase: Starts from the point in the log up to where all dirty pages have been flushed, and move forward to the end of the log. Any change that appears in the dirty page table is redone. Undo phase: Starts from the end of the log and proceeds ...
... Redo phase: Starts from the point in the log up to where all dirty pages have been flushed, and move forward to the end of the log. Any change that appears in the dirty page table is redone. Undo phase: Starts from the end of the log and proceeds ...
CNAF Database Service - Indico
... MySql databases. Experience in development of MySql based applications (e.g. VOMS), exploiting innoDB tables and one-way replication. ...
... MySql databases. Experience in development of MySql based applications (e.g. VOMS), exploiting innoDB tables and one-way replication. ...
Document
... sites are down simultaneously) are possible, then every atomic protocol may cause processes to become blocked. Two exceptions: if we ignore communication failures, it is possible to design such a protocol (Skeen et. al. 83) If we impose some restrictions on transactions (I.e., what data they can rea ...
... sites are down simultaneously) are possible, then every atomic protocol may cause processes to become blocked. Two exceptions: if we ignore communication failures, it is possible to design such a protocol (Skeen et. al. 83) If we impose some restrictions on transactions (I.e., what data they can rea ...
database server
... Database Drivers • Database server does not understand Java/C# commands • Only understands its own DBMS protocols – Each server has its own DBMS ...
... Database Drivers • Database server does not understand Java/C# commands • Only understands its own DBMS protocols – Each server has its own DBMS ...