Quantum Mechanical Scattering using Path Integrals
... Harris, Allison Department of Physics, ISU The Path Integral technique is an alternative formulation of quantum mechanics that is completely equivalent to the more traditional Schrödinger equation approach. Developed by Feynman in the 1940’s, following inspiration from Dirac, the path integral appro ...
... Harris, Allison Department of Physics, ISU The Path Integral technique is an alternative formulation of quantum mechanics that is completely equivalent to the more traditional Schrödinger equation approach. Developed by Feynman in the 1940’s, following inspiration from Dirac, the path integral appro ...
PhD position: Quantum information processing with single electron spins
... A computer based on quantum information would be able to solve certain problems which are intractable with other types of computer. It is natural to use the spin of an electron as a quantum bit because spin down is ‘0’, spin up is ‘1’, and all possible superposition states can be accessed with magne ...
... A computer based on quantum information would be able to solve certain problems which are intractable with other types of computer. It is natural to use the spin of an electron as a quantum bit because spin down is ‘0’, spin up is ‘1’, and all possible superposition states can be accessed with magne ...
Buzek_Teheran_tutorials_abstract
... Quantum observations (Tutorial lectures) Vladimír Bužek Research Center for Quantum Information, Slovak Academy of Sciences, Bratislava In my tutorial lectures I will briefly outline some epistemological as well as operational problems associated with the quantum theory of measurement. I will addres ...
... Quantum observations (Tutorial lectures) Vladimír Bužek Research Center for Quantum Information, Slovak Academy of Sciences, Bratislava In my tutorial lectures I will briefly outline some epistemological as well as operational problems associated with the quantum theory of measurement. I will addres ...
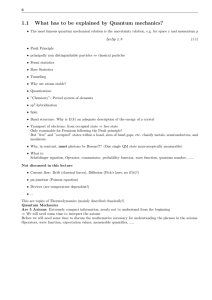
1.1 What has to be explained by Quantum mechanics?
... Only reasonable for Fermions following the Pauli principle! But ”free” and ”occupied” states within a band, sizes of band gaps, etc. classify metals, semiconductors, and insulators. • Why, in contrast, must photons be Bosons?!? (One single QM state macroscopically measurable) • What is: Schrödinger ...
... Only reasonable for Fermions following the Pauli principle! But ”free” and ”occupied” states within a band, sizes of band gaps, etc. classify metals, semiconductors, and insulators. • Why, in contrast, must photons be Bosons?!? (One single QM state macroscopically measurable) • What is: Schrödinger ...
Quantum Information (QI) - BYU Physics and Astronomy
... How do I pass this 513R class? What will we do? CP, HW, IP, MT, F How do you communicate? Sources for QI? (Linear Algebra prerequisite) What is Linear Algebra? ...
... How do I pass this 513R class? What will we do? CP, HW, IP, MT, F How do you communicate? Sources for QI? (Linear Algebra prerequisite) What is Linear Algebra? ...
Link between the hierarchy of fractional quantum Hall states and
... Link between the hierarchy of fractional quantum Hall states and Haldane’s conjecture for quantum spin chains Masaaki Nakamura Department of Physics, Tokyo Institute of Technology, Tokyo 152-8551, Japan ...
... Link between the hierarchy of fractional quantum Hall states and Haldane’s conjecture for quantum spin chains Masaaki Nakamura Department of Physics, Tokyo Institute of Technology, Tokyo 152-8551, Japan ...
Quantum Memories at Room-Temperature Supervisors: Dr Dylan
... in our lambda Raman quantum memory. This will be demonstration of a new protocol: a quantum Zeno noise suppression technique to kill a noise-process prohibits quantum operation, a process known as four-wave-mixing. We will suppress two-mode-squeezing via incoherent Hamiltonian engineering. This work ...
... in our lambda Raman quantum memory. This will be demonstration of a new protocol: a quantum Zeno noise suppression technique to kill a noise-process prohibits quantum operation, a process known as four-wave-mixing. We will suppress two-mode-squeezing via incoherent Hamiltonian engineering. This work ...
Linear Circuit Analysis with Reactive Components
... Solving the Schrödinger Equation on a 2D Lattice in Quantum Wave Interference (QWI) PhET Sam Reid Quantum Wave Interference allows the user to visualize the propagation of a wavefunction in the presence of potential barriers and detectors. We implement a 2D Richardson algorithm[1], a local propagati ...
... Solving the Schrödinger Equation on a 2D Lattice in Quantum Wave Interference (QWI) PhET Sam Reid Quantum Wave Interference allows the user to visualize the propagation of a wavefunction in the presence of potential barriers and detectors. We implement a 2D Richardson algorithm[1], a local propagati ...
David Williams (University of Cambridge)
... David Williams (University of Cambridge) Semiconductor Structures for Quantum Information Processing A number of new ways of manipulating information, generically known as quantum information processing, have been postulated in the last 15-20 years. Several have been demonstrated experimentally, but ...
... David Williams (University of Cambridge) Semiconductor Structures for Quantum Information Processing A number of new ways of manipulating information, generically known as quantum information processing, have been postulated in the last 15-20 years. Several have been demonstrated experimentally, but ...
powerpoint slides
... Computers are based on quantum devices transistors - which are getting smaller and smaller. Soon they will be so small that they will be directly subject to quantum rules. This is both a problem and an opportunity. We will be looking at the opportunity. ...
... Computers are based on quantum devices transistors - which are getting smaller and smaller. Soon they will be so small that they will be directly subject to quantum rules. This is both a problem and an opportunity. We will be looking at the opportunity. ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.