Document
... How to build a quantum computer Photons don't interact (good for transmission; bad for computation) ...
... How to build a quantum computer Photons don't interact (good for transmission; bad for computation) ...
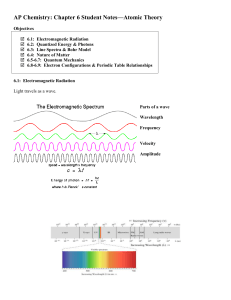
Ch. 6 notes
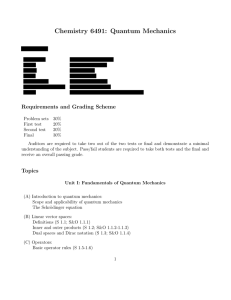
... 6.5-6.7: Quantum Mechanics Developed by Werner Heisenberg (1901-1976), Louis De Broglie (1892-1987), Erwin Schrodinger (1887-1961) This answers the question: Where is the _____________ in the atom? The answer is complex. We can’t say exactly where the atom is. We can only say where we think it _____ ...
... 6.5-6.7: Quantum Mechanics Developed by Werner Heisenberg (1901-1976), Louis De Broglie (1892-1987), Erwin Schrodinger (1887-1961) This answers the question: Where is the _____________ in the atom? The answer is complex. We can’t say exactly where the atom is. We can only say where we think it _____ ...
Physics 411: Introduction to Quantum Mechanics
... Comprehensive Final Exam: 40 points Maximum score: 100 points ...
... Comprehensive Final Exam: 40 points Maximum score: 100 points ...
influências da expansão do universo na evolução do - Cosmo-ufes
... What makes the role of a measurement in the early Universe? (we cannot collapse the wave function because we could not exist without stars!) ...
... What makes the role of a measurement in the early Universe? (we cannot collapse the wave function because we could not exist without stars!) ...
God Plays Dice
... • The mathematical predictions of quantum mechanics yield results that are in agreement with experimental findings. That is the reason we use quantum theory. That quantum theory fits experiment is what validates the theory, but why experiment should give such peculiar results is a mystery. This is t ...
... • The mathematical predictions of quantum mechanics yield results that are in agreement with experimental findings. That is the reason we use quantum theory. That quantum theory fits experiment is what validates the theory, but why experiment should give such peculiar results is a mystery. This is t ...
Document
... ” …not a mechanical influence … … an influence on the very conditions which define the possible types of predictions regarding the future behavior of the system.” ...
... ” …not a mechanical influence … … an influence on the very conditions which define the possible types of predictions regarding the future behavior of the system.” ...
Slide 1
... A laser separates individual photons and sends them to an instrument called a modulator. The modulator sends the photons to other network nodes via fiber-optic cable. The photons are encoded by sending them at different time intervals. ...
... A laser separates individual photons and sends them to an instrument called a modulator. The modulator sends the photons to other network nodes via fiber-optic cable. The photons are encoded by sending them at different time intervals. ...
motivation-to-quantum
... The two position states of a photon in a Mach-Zehnder apparatus is just one example of a quantum bit or qubit Except when addressing a particular physical implementation, we will simply talk about “basis” states 0 and 1 ...
... The two position states of a photon in a Mach-Zehnder apparatus is just one example of a quantum bit or qubit Except when addressing a particular physical implementation, we will simply talk about “basis” states 0 and 1 ...
Slide 1
... • PQN–the main E level occupied by the e• n values are positive • As n increases so does the distance from the nucleus • Angular momentum quantum number, l – the shape of the orbital • Values can be 0 and any # lower than what n = (if n=3, l can be 0, 1, and 2) ...
... • PQN–the main E level occupied by the e• n values are positive • As n increases so does the distance from the nucleus • Angular momentum quantum number, l – the shape of the orbital • Values can be 0 and any # lower than what n = (if n=3, l can be 0, 1, and 2) ...
Lecture 21
... Alice and Bob choose a random subset of their qubits to perform the test on (note that the states which they check become ruined for the purposes of generating the key, since their messurement outcoes are disclosed publicly) Moreover, for each pair tested, only one of the two measurements can be per ...
... Alice and Bob choose a random subset of their qubits to perform the test on (note that the states which they check become ruined for the purposes of generating the key, since their messurement outcoes are disclosed publicly) Moreover, for each pair tested, only one of the two measurements can be per ...
Many problems that take long time to solve on a deterministic Turing
... can be often be solved very quickly on a probabilistic Turing machine However there is a tradeoff between the time it takes to return an answer to a computation and the probability that the returned answer is correct ...
... can be often be solved very quickly on a probabilistic Turing machine However there is a tradeoff between the time it takes to return an answer to a computation and the probability that the returned answer is correct ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.