PhD Position:
... and computational drug screening because they allow the design work to be moved from physical reality into a virtual world inside a supercomputer that is set to evolve, just as the real world does, under the Schrödinger equation. The primary difficulty with such simulations used to be their exponent ...
... and computational drug screening because they allow the design work to be moved from physical reality into a virtual world inside a supercomputer that is set to evolve, just as the real world does, under the Schrödinger equation. The primary difficulty with such simulations used to be their exponent ...
Atomic and Molecular Physics for Physicists Ben-Gurion University of the Negev
... The theory was found to be extremely successful in describing nature (see rest of the course), but as two of its fathers put it: “To try and stop all attempts to pass beyond the present viewpoint of quantum physics could be very dangerous for the progress of science and would furthermore be contrary ...
... The theory was found to be extremely successful in describing nature (see rest of the course), but as two of its fathers put it: “To try and stop all attempts to pass beyond the present viewpoint of quantum physics could be very dangerous for the progress of science and would furthermore be contrary ...
Specialization: 010600/52 Program: Applied Mathematics and Physics Program director: prof. S.L. Yakovlev
... difference methods and finite element method (FEM). One of the available implementations of the FEM is Deal.ii library. Deal.ii is a powerful general purpose object oriented finite element differential equations analysis library, that provides a wide collection of tool classes such as adaptive meshe ...
... difference methods and finite element method (FEM). One of the available implementations of the FEM is Deal.ii library. Deal.ii is a powerful general purpose object oriented finite element differential equations analysis library, that provides a wide collection of tool classes such as adaptive meshe ...
Powerpoint handout
... proposing that electrons in atoms could have only certain energies, and that light was given off when an electron underwent a transition from a higher energy level to a lower one. ...
... proposing that electrons in atoms could have only certain energies, and that light was given off when an electron underwent a transition from a higher energy level to a lower one. ...
Holonomic quantum computation with neutral atoms
... a two-qubit gate that, along with the dynamically generated one-qubit gates, is universal. To achieve an all-geometrical implementation of quantum computation one is led to consider more sophisticated, i.e., non-Abelian, structures. This has been originally done in Ref. [6], where the so called holo ...
... a two-qubit gate that, along with the dynamically generated one-qubit gates, is universal. To achieve an all-geometrical implementation of quantum computation one is led to consider more sophisticated, i.e., non-Abelian, structures. This has been originally done in Ref. [6], where the so called holo ...
1 pt
... What is the name of the term given to the minimum quantity of energy that can be lost or gained by an atom? ...
... What is the name of the term given to the minimum quantity of energy that can be lost or gained by an atom? ...
Quantum dots and radio-frequency electrometers in silicon
... Cavendish Laboratory, University of Cambridge An important goal for solid-state quantum computing is to confine a single electron in silicon, then manipulate and subsequently determine its spin state. Silicon has a low nuclear spin density which, together with the low spin-orbit coupling in this mat ...
... Cavendish Laboratory, University of Cambridge An important goal for solid-state quantum computing is to confine a single electron in silicon, then manipulate and subsequently determine its spin state. Silicon has a low nuclear spin density which, together with the low spin-orbit coupling in this mat ...
Glasgow2004
... The main application of MUBs pertains to secure quantum key exchange (quantum cryptography). This is because any attempt by an eavesdropper (say Eve) to distinguish between two nonorthogonal quantum states shared by two remote parties (say Alice and Bob) will occur at the price of introducing a dist ...
... The main application of MUBs pertains to secure quantum key exchange (quantum cryptography). This is because any attempt by an eavesdropper (say Eve) to distinguish between two nonorthogonal quantum states shared by two remote parties (say Alice and Bob) will occur at the price of introducing a dist ...
Quantum Computing at the Speed of Light
... “Quantum Computing at the Speed of Light” ABSTRACT Harnessing quantum states for information storage and manipulation (in so called “qubits”) is the objective of quantum computing, with the potential to revolutionize technology in areas of great importance to society (e.g. cryptography, data base se ...
... “Quantum Computing at the Speed of Light” ABSTRACT Harnessing quantum states for information storage and manipulation (in so called “qubits”) is the objective of quantum computing, with the potential to revolutionize technology in areas of great importance to society (e.g. cryptography, data base se ...
Quantum computation communication theory
... – Obtain maximally entangled states suitable for teleportation in the presence of loss. – Compare efficiency of the two following schemes for establishing N shared ebits (entangled qubit pairs) in the presence of loss: • (a) N singlets: N single ebits with qubits encoded on polarization; • (b) 1 twi ...
... – Obtain maximally entangled states suitable for teleportation in the presence of loss. – Compare efficiency of the two following schemes for establishing N shared ebits (entangled qubit pairs) in the presence of loss: • (a) N singlets: N single ebits with qubits encoded on polarization; • (b) 1 twi ...
Atomic Spectroscopy and the Correspondence Principle
... required by classical electromagnetic principles. Initial speculation, however, suggested that the observed line spectrum of the hydrogen atom might be interpeted in terms of electromagnetic emissions related to orbital frequencies of the electron. Subsequently, Bohr achieved agreement with experime ...
... required by classical electromagnetic principles. Initial speculation, however, suggested that the observed line spectrum of the hydrogen atom might be interpeted in terms of electromagnetic emissions related to orbital frequencies of the electron. Subsequently, Bohr achieved agreement with experime ...
Quantum Mechanics
... is no longer apparent and there are no shapes. At the time of its condensation, can one say otherwise than that this is but temporary? But at the time of its dispersing, can one hastily say that it is then non-existent. The Great Void cannot but consist of ch’i; this ch’i cannot but condense to fo ...
... is no longer apparent and there are no shapes. At the time of its condensation, can one say otherwise than that this is but temporary? But at the time of its dispersing, can one hastily say that it is then non-existent. The Great Void cannot but consist of ch’i; this ch’i cannot but condense to fo ...
Lecture 26 - Purdue Physics
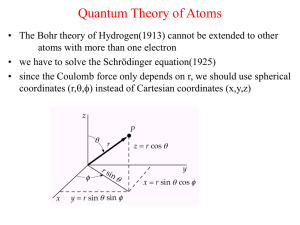
... Atomic Quantum Numbers • Sommerfeld extended the Bohr model to account for quantized angular momentum • A new quantum number, ℓ, known as the orbital quantum number, identifies the orbital angular momentum of a state. ...
... Atomic Quantum Numbers • Sommerfeld extended the Bohr model to account for quantized angular momentum • A new quantum number, ℓ, known as the orbital quantum number, identifies the orbital angular momentum of a state. ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.