Document
... • 1926 – Enrico Fermi & Paul Dirac – formulated (independently) the Fermi-Dirac statistics, which describes distribution of many identical particles obeying the Pauli exclusion principle (fermions with half-integer spins – contrary to bosons satisfying the Bose-Einstein statistics) • 1926 – Erwin Sc ...
... • 1926 – Enrico Fermi & Paul Dirac – formulated (independently) the Fermi-Dirac statistics, which describes distribution of many identical particles obeying the Pauli exclusion principle (fermions with half-integer spins – contrary to bosons satisfying the Bose-Einstein statistics) • 1926 – Erwin Sc ...
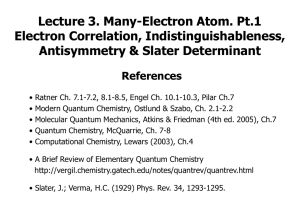
chapter 7 part 1
... no it is the ground state in idealized hydrogen atom with (3 quantum numbers) all energy levels are degenerate, in real hydrogen atom with 4 quantum numbers, there are tiny differences in energy between the levels lifting this degeneracy ...
... no it is the ground state in idealized hydrogen atom with (3 quantum numbers) all energy levels are degenerate, in real hydrogen atom with 4 quantum numbers, there are tiny differences in energy between the levels lifting this degeneracy ...
Quantum Computation with Neutral Atoms
... Back to the real world: What do we need to build a quantum computer? ...
... Back to the real world: What do we need to build a quantum computer? ...
Quantum Query Lower Bounds: The Adversary Method
... hamming weight ≤ k − 1. We return 1 in the first case and 0 in the second. Let’s look at Y = {x : x has hamming weight k} and Z = {x : x has hamming weight k− 1}. It is easy to see that ∀y ∈ Y, |Zy | = k, since for any y we can flip each of its k 1s to get something in Z). Similarly, ∀z ∈ Z, |Yz | = ...
... hamming weight ≤ k − 1. We return 1 in the first case and 0 in the second. Let’s look at Y = {x : x has hamming weight k} and Z = {x : x has hamming weight k− 1}. It is easy to see that ∀y ∈ Y, |Zy | = k, since for any y we can flip each of its k 1s to get something in Z). Similarly, ∀z ∈ Z, |Yz | = ...
Document
... treated independently of the other electrons. • This approach is called the independent particle approximation, or IPA. • This approximation allows the Schrödinger equation for the atom to be broken into Z separate equations, one for each electron. • A major consequence of the IPA is that each elect ...
... treated independently of the other electrons. • This approach is called the independent particle approximation, or IPA. • This approximation allows the Schrödinger equation for the atom to be broken into Z separate equations, one for each electron. • A major consequence of the IPA is that each elect ...
PPT
... length 1; i.e., |A| = 1. Vectors can be added together, multiplied by constants (including complex numbers), and multiplied together. Vector addition maps any pair of vectors onto another vector, specifically, the one you get by moving the second vector so that it’s tail coincides with the tip of th ...
... length 1; i.e., |A| = 1. Vectors can be added together, multiplied by constants (including complex numbers), and multiplied together. Vector addition maps any pair of vectors onto another vector, specifically, the one you get by moving the second vector so that it’s tail coincides with the tip of th ...
Response Time Distributions in Partially-Coherent Quantum Walk Models for
... decision processes unfold over time, it is plausible to suggest that an evolutionary advantage would accrue to decisionmakers that can make effective use of quantum mechanical effects. Of course, many questions need to be answered before we can determine with any confidence whether or not this advan ...
... decision processes unfold over time, it is plausible to suggest that an evolutionary advantage would accrue to decisionmakers that can make effective use of quantum mechanical effects. Of course, many questions need to be answered before we can determine with any confidence whether or not this advan ...
Nicholas Bigelow - University of Rochester
... • To date, the majority of quantum communications experiments on entanglement involve entangled states of light. • Unfortunately, entanglement is degraded exponentially with distance due to losses and channel noise. • Solutions protocols have been devised evoking concepts of entanglement purificatio ...
... • To date, the majority of quantum communications experiments on entanglement involve entangled states of light. • Unfortunately, entanglement is degraded exponentially with distance due to losses and channel noise. • Solutions protocols have been devised evoking concepts of entanglement purificatio ...
The Paradoxes of Quantum Mechanics
... that at least is larger than its wavelength. The standard answer is that light is either wave-like or particle-like depending on what measurements we choose to make on it. For example, if I tune my AM receiver to 550 kHz to listen to my favorite program, I am actually measuring the frequency (or equ ...
... that at least is larger than its wavelength. The standard answer is that light is either wave-like or particle-like depending on what measurements we choose to make on it. For example, if I tune my AM receiver to 550 kHz to listen to my favorite program, I am actually measuring the frequency (or equ ...
Persistent currents controlled by non-classical electromagnetic fields J. D
... of the Weyl function W(ζn) = Tr(ρD(nξexp(iωt))), with ζn = nξexp(iωt). We see that persistent currents calculated from Eq. (4) are influenced by the features of non-classical radiation contained in the Weyl function. The most popular “object” of quantum computing is the qubit described by: δ ...
... of the Weyl function W(ζn) = Tr(ρD(nξexp(iωt))), with ζn = nξexp(iωt). We see that persistent currents calculated from Eq. (4) are influenced by the features of non-classical radiation contained in the Weyl function. The most popular “object” of quantum computing is the qubit described by: δ ...
Reality Final: Why Ask Why?
... The fourth postulate states that if a system's state vector of a certain property is not an eigenvector of the associated operator, than the experimentally determined value of the property is governed by the laws of probability. The probability that a system in this situation will have a value x for ...
... The fourth postulate states that if a system's state vector of a certain property is not an eigenvector of the associated operator, than the experimentally determined value of the property is governed by the laws of probability. The probability that a system in this situation will have a value x for ...
Quantum key distribution
Quantum key distribution (QKD) uses quantum mechanics to guarantee secure communication. It enables two parties to produce a shared random secret key known only to them, which can then be used to encrypt and decrypt messages. It is often incorrectly called quantum cryptography, as it is the most well known example of the group of quantum cryptographic tasks.An important and unique property of quantum key distribution is the ability of the two communicating users to detect the presence of any third party trying to gain knowledge of the key. This results from a fundamental aspect of quantum mechanics: the process of measuring a quantum system in general disturbs the system. A third party trying to eavesdrop on the key must in some way measure it, thus introducing detectable anomalies. By using quantum superpositions or quantum entanglement and transmitting information in quantum states, a communication system can be implemented which detects eavesdropping. If the level of eavesdropping is below a certain threshold, a key can be produced that is guaranteed to be secure (i.e. the eavesdropper has no information about it), otherwise no secure key is possible and communication is aborted.The security of encryption that uses quantum key distribution relies on the foundations of quantum mechanics, in contrast to traditional public key cryptography which relies on the computational difficulty of certain mathematical functions, and cannot provide any indication of eavesdropping at any point in the communication process, or any mathematical proof as to the actual complexity of reversing the one-way functions used. QKD has provable security based on information theory, and forward secrecy.Quantum key distribution is only used to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel. The algorithm most commonly associated with QKD is the one-time pad, as it is provably secure when used with a secret, random key. In real world situations, it is often also used with encryption using symmetric key algorithms like the Advanced Encryption Standard algorithm. In the case of QKD this comparison is based on the assumption of perfect single-photon sources and detectors, that cannot be easily implemented.