Compressed Data Structures
... Succinct rank Now we will see how to implement rank and select operations on a bit vector B[0..u). Let us start with rank-1. We will describe a data structure that consists of B itself and additional data of o(u) bits. Such a data structure using a sublinear amount of additional space is called suc ...
... Succinct rank Now we will see how to implement rank and select operations on a bit vector B[0..u). Let us start with rank-1. We will describe a data structure that consists of B itself and additional data of o(u) bits. Such a data structure using a sublinear amount of additional space is called suc ...
the lecture notes from the Foundations of Computer Science module
... In this half-module we are going to look at designing algorithms. We will see how they depend on the design of suitable data structures, and how some structures and algorithms are more efficient than others for the same task. We’ll concentrate on a few basic tasks, such as sorting and search, that u ...
... In this half-module we are going to look at designing algorithms. We will see how they depend on the design of suitable data structures, and how some structures and algorithms are more efficient than others for the same task. We’ll concentrate on a few basic tasks, such as sorting and search, that u ...
DATA STRUCTURE
... 1. More memory : if the number of fields are more, then more memory space is needed. 2. Access to an arbitrary data item is little cumbersome and also time consuming. ...
... 1. More memory : if the number of fields are more, then more memory space is needed. 2. Access to an arbitrary data item is little cumbersome and also time consuming. ...
Elementary Data Structures and Hash Tables
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
... All direct-address table operations are O(1)! So why isn’t every set implemented with a direct-address table? The space complexity is Θ(`U`) ...
[2]Tigran Aivazian, Linux Kernel 2.4 Internals.
... Modern operating systems allow more than one process to exist at any given time. Processes do not need to be aware of each other unless they are designed so. This makes programs easier to develop, maintain and port. [5] For scheduler however it is important to distinguish between different types of ...
... Modern operating systems allow more than one process to exist at any given time. Processes do not need to be aware of each other unless they are designed so. This makes programs easier to develop, maintain and port. [5] For scheduler however it is important to distinguish between different types of ...
Practical Suffix Tree Construction
... character in the first character of each suffix, and copy the suffix pointers into the Temp array. We see that the count for A is 2 and the count for T is 1; the counts for G, C, and $ are 0. We can use these counts to determine the character group boundaries: group A will start at position 0 with t ...
... character in the first character of each suffix, and copy the suffix pointers into the Temp array. We see that the count for A is 2 and the count for T is 1; the counts for G, C, and $ are 0. We can use these counts to determine the character group boundaries: group A will start at position 0 with t ...
Sets, Maps and Hash tables
... Hash Tables • The implementations HashSet and HashMap are based on a Hash Table • A Hash Table is based on the below ideas: – Create an array of length N, which can store objects of some type T – Find a mapping from T to the interval [0; N-1] (a Hash Function f) – Store an object t of type T in the ...
... Hash Tables • The implementations HashSet and HashMap are based on a Hash Table • A Hash Table is based on the below ideas: – Create an array of length N, which can store objects of some type T – Find a mapping from T to the interval [0; N-1] (a Hash Function f) – Store an object t of type T in the ...
Practical Suffix Tree Construction
... character in the first character of each suffix, and copy the suffix pointers into the Temp array. We see that the count for A is 2 and the count for T is 1; the counts for G, C, and $ are 0. We can use these counts to determine the character group boundaries: group A will start at position 0 with t ...
... character in the first character of each suffix, and copy the suffix pointers into the Temp array. We see that the count for A is 2 and the count for T is 1; the counts for G, C, and $ are 0. We can use these counts to determine the character group boundaries: group A will start at position 0 with t ...
Lecture Notes- Data Structures
... These are some basic function growth classifications used in various notations. The list starts at the slowest growing function (logarithmic, fastest execution time) and goes on to the fastest growing (exponential, slowest execution time). Notice that as „n‟, or the input, increases in each of those ...
... These are some basic function growth classifications used in various notations. The list starts at the slowest growing function (logarithmic, fastest execution time) and goes on to the fastest growing (exponential, slowest execution time). Notice that as „n‟, or the input, increases in each of those ...
Structures - Computer Science
... Memory that contains a variety of objects over time Only contains one data member at a time Members of a union share space Conserves storage Only the last data member defined can be accessed ...
... Memory that contains a variety of objects over time Only contains one data member at a time Members of a union share space Conserves storage Only the last data member defined can be accessed ...
Chapter 3 Lists, Stacks, and Queues
... • All elements need not be adjacent in memory • Often require less memory space than array • printList, find and findPrevious take linear time O(N) • insert and remove take constant time O(1) 2110211 Intro. to Data Structures ...
... • All elements need not be adjacent in memory • Often require less memory space than array • printList, find and findPrevious take linear time O(N) • insert and remove take constant time O(1) 2110211 Intro. to Data Structures ...
The Specification of Array-Based Algorithms and the Automated
... the automated derivation through program transformation of efficient implementations for highperformance computer systems. Numerical mathematical algorithms are algorithms typically based upon linear algebra or discrete approximations. Such algorithms dominate the field of scientific computing and t ...
... the automated derivation through program transformation of efficient implementations for highperformance computer systems. Numerical mathematical algorithms are algorithms typically based upon linear algebra or discrete approximations. Such algorithms dominate the field of scientific computing and t ...
pptx - Electrical and Computer Engineering
... These slides are provided for the ECE 250 Algorithms and Data Structures course. The material in it reflects Douglas W. Harder’s best judgment in light of the information available to him at the time of preparation. Any reliance on these course slides by any party for any other purpose are the respo ...
... These slides are provided for the ECE 250 Algorithms and Data Structures course. The material in it reflects Douglas W. Harder’s best judgment in light of the information available to him at the time of preparation. Any reliance on these course slides by any party for any other purpose are the respo ...
Introduction to Data Structures and ADT
... item within a data structure. – Ex: 16/32 bit integers, overflow. ...
... item within a data structure. – Ex: 16/32 bit integers, overflow. ...
Graph Data Structure
... These slides are provided for the ECE 250 Algorithms and Data Structures course. The material in it reflects Douglas W. Harder’s best judgment in light of the information available to him at the time of preparation. Any reliance on these course slides by any party for any other purpose are the respo ...
... These slides are provided for the ECE 250 Algorithms and Data Structures course. The material in it reflects Douglas W. Harder’s best judgment in light of the information available to him at the time of preparation. Any reliance on these course slides by any party for any other purpose are the respo ...
CS163_Topic6
... organize the table in regard to one of the fields in the data's structure. • Generally this is used when insertion and deletion is rare and the typical operation is traversal (i.e., your data base has already been created and you want to print a list of all of the high priority items). Therefore, th ...
... organize the table in regard to one of the fields in the data's structure. • Generally this is used when insertion and deletion is rare and the typical operation is traversal (i.e., your data base has already been created and you want to print a list of all of the high priority items). Therefore, th ...
Median filtering is equivalent to sorting
... [18, 20, 22, 23, 25] and image processing [14, 15]; see Figure 1 for a simple example that demonstrates how efficiently a median filter can recover a corrupted signal. Contribution. This work gives a new, simple and efficient algorithm for median filtering. The new algorithm is based on sorting; the ...
... [18, 20, 22, 23, 25] and image processing [14, 15]; see Figure 1 for a simple example that demonstrates how efficiently a median filter can recover a corrupted signal. Contribution. This work gives a new, simple and efficient algorithm for median filtering. The new algorithm is based on sorting; the ...
Unit 03 - UniMAP Portal
... structure is to use another sequential data structure viz, arrays. However, queues have also been implemented using a linked data structure the array implementation puts a limitation on the capacity of the queue every insertion of an element into the queue has to necessarily test for a QUEUE-FULL co ...
... structure is to use another sequential data structure viz, arrays. However, queues have also been implemented using a linked data structure the array implementation puts a limitation on the capacity of the queue every insertion of an element into the queue has to necessarily test for a QUEUE-FULL co ...
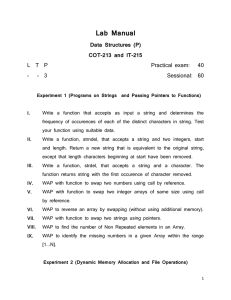
Lab Manual Data Structures (P) COT-213 and IT-215
... WAP to store an information in array of structure , dynamically, and also give a function to display the current information. The program should give user a choice for inserting a data or to display the current data. Implement the program for Student structures (contains student_name, ...
... WAP to store an information in array of structure , dynamically, and also give a function to display the current information. The program should give user a choice for inserting a data or to display the current data. Implement the program for Student structures (contains student_name, ...



![[2]Tigran Aivazian, Linux Kernel 2.4 Internals.](http://s1.studyres.com/store/data/000898666_1-04a31de80ac32be7fe2c9eea82db3a2b-300x300.png)