File concept
... Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can bring into memory & execute ...
... Object file – sequence of bytes organized into blocks understandable by system linker\ Executable file – series of code sections that the loader can bring into memory & execute ...
chapter 2: data mining using p-tree relational systems
... prevalent in this setting? Clearly, it is more likely that a new employee record will be inserted than that a new attribute will be added. It may also be more likely that the entire employee record has to be retrieved than a listing of, e.g., all employee names. These benefits should not, however, ...
... prevalent in this setting? Clearly, it is more likely that a new employee record will be inserted than that a new attribute will be added. It may also be more likely that the entire employee record has to be retrieved than a listing of, e.g., all employee names. These benefits should not, however, ...
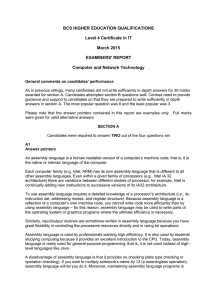
BCS HIGHER EDUCATION QUALIFICATIONS Level 4 Certificate in IT March 2015
... There is a remarkably wide variety of high-level languages; there are hundreds of them. Many are similar to each other although there are different classes of high-level language. Most programmers use C, Java, or Python. These are procedural languages that execute instructions sequentially and they ...
... There is a remarkably wide variety of high-level languages; there are hundreds of them. Many are similar to each other although there are different classes of high-level language. Most programmers use C, Java, or Python. These are procedural languages that execute instructions sequentially and they ...
Best Practices for Data Sharing in a Grid Distributed
... These types are Network Attached Storage, Clustered / Shared File Systems and Hybrid File Systems. ...
... These types are Network Attached Storage, Clustered / Shared File Systems and Hybrid File Systems. ...
RepliStor for XtenderSolutions
... At the heart of any enterprise content management environment is a critical component that ensures data protection and availability. LEGATO RepliStor for XtenderSolutions offers a simple and reliable asynchronous replication solution that geographically distributes identical sets of data to one or m ...
... At the heart of any enterprise content management environment is a critical component that ensures data protection and availability. LEGATO RepliStor for XtenderSolutions offers a simple and reliable asynchronous replication solution that geographically distributes identical sets of data to one or m ...
A Universal Framework for (nearly) Arbitrary Dynamic Languages
... One such feature that has become nearly ubiquitous in mainstream languages is polymorphism. In some cases static analysis can allow polymorphic statements to be optimized into one morphology, or some specific small number of possible morphologies, but it is now a common language feature to allow pro ...
... One such feature that has become nearly ubiquitous in mainstream languages is polymorphism. In some cases static analysis can allow polymorphic statements to be optimized into one morphology, or some specific small number of possible morphologies, but it is now a common language feature to allow pro ...
A Deduplication File System & Course Review Kai Li
... Do the following transactions behave the same? BeginTransaction C = C + $100; S = S - $100; Commit BeginTransaction S = S - $100; C = C + $100; Commit ...
... Do the following transactions behave the same? BeginTransaction C = C + $100; S = S - $100; Commit BeginTransaction S = S - $100; C = C + $100; Commit ...
Experiences with Content Addressable Storage and Virtual Disks Anthony Liguori
... templates for multiple logical instances which store perinstance modifications. We have previously experimented with both file and block-based copy-on-write technologies [9] for managing the life cycle of servers. While we found such “stackable” technologies to be very effective for initial installa ...
... templates for multiple logical instances which store perinstance modifications. We have previously experimented with both file and block-based copy-on-write technologies [9] for managing the life cycle of servers. While we found such “stackable” technologies to be very effective for initial installa ...
A: Process termination requires reclaim of any reusable resources
... • Proper management is of central importance • Entire speed of computer operation hinges on disk subsystem and its algorithms • OS activities Free-space management Storage allocation Disk scheduling • Some storage need not be fast Tertiary storage includes optical storage, magnetic tape Still must b ...
... • Proper management is of central importance • Entire speed of computer operation hinges on disk subsystem and its algorithms • OS activities Free-space management Storage allocation Disk scheduling • Some storage need not be fast Tertiary storage includes optical storage, magnetic tape Still must b ...
The Need for Backing Storage - it
... Backing storage allows data to be saved permanently. RAM is often not large enough to store large data files. Backing storage allows large quantities of data to be stored. It is most important that backups are made of important data in case it becomes lost or damaged. Backups will be saved on a back ...
... Backing storage allows data to be saved permanently. RAM is often not large enough to store large data files. Backing storage allows large quantities of data to be stored. It is most important that backups are made of important data in case it becomes lost or damaged. Backups will be saved on a back ...
Andrew`s slides - Computer Science at Rutgers
... (a collection of websites classified into categories – course, faculty staff, student, research project) Appx 4000 pages, 8000 hyperlinks DB contains attributes associated with each page/hyperlink (path/domain, direction of hyperlink) ...
... (a collection of websites classified into categories – course, faculty staff, student, research project) Appx 4000 pages, 8000 hyperlinks DB contains attributes associated with each page/hyperlink (path/domain, direction of hyperlink) ...
Objectives of KeyKOS
... Objects and Capabilities every object in the system is exclusively referred to by one or more capabilities capability gives its holder the authority to request a service from object it names; object has no intrinsic authority messages are the only form of interaction between objects ...
... Objects and Capabilities every object in the system is exclusively referred to by one or more capabilities capability gives its holder the authority to request a service from object it names; object has no intrinsic authority messages are the only form of interaction between objects ...
Topic 1: Introduction to Computers and Programming
... There are two primary types of storage in a computer: ...
... There are two primary types of storage in a computer: ...
資工系網媒所NEWS實驗室Chapter 13
... Overview of Mass Storage Structure Magnetic disks provide bulk of secondary storage of modern computers Drives rotate at 60 to 200 times per second Transfer rate is rate at which data flow between drive and computer Positioning time (random-access time) is time to move disk arm to desired cylinder ...
... Overview of Mass Storage Structure Magnetic disks provide bulk of secondary storage of modern computers Drives rotate at 60 to 200 times per second Transfer rate is rate at which data flow between drive and computer Positioning time (random-access time) is time to move disk arm to desired cylinder ...
Swap Space and Virtual Memory
... The two main jobs of a computer are I/O and processing. In many cases, the main job is I/O and the processing is merely incidental. For instance, when we browse a web page or edit a file, our immediate interest is to read or enter some information, and not to compute an answer. The role of the opera ...
... The two main jobs of a computer are I/O and processing. In many cases, the main job is I/O and the processing is merely incidental. For instance, when we browse a web page or edit a file, our immediate interest is to read or enter some information, and not to compute an answer. The role of the opera ...
h6909.3-EMC Database Performance Tiering Assessment Service
... • The data that has the most/least value to business users • Whether data access is different to what was planned or expected The assessment provides DBAs an ideal method for optimizing data models based on actual usage patterns, formulating intelligent indexing and aggregation strategies, and imple ...
... • The data that has the most/least value to business users • Whether data access is different to what was planned or expected The assessment provides DBAs an ideal method for optimizing data models based on actual usage patterns, formulating intelligent indexing and aggregation strategies, and imple ...
Part 2 - PPT
... Path together with leaf is encoded into string -> the Index Fabric „A Fast Index for Semistructured Data” - Brian F. Cooper et al. ...
... Path together with leaf is encoded into string -> the Index Fabric „A Fast Index for Semistructured Data” - Brian F. Cooper et al. ...
Collections in Java
... Java has defined "wrapper" classes which hold fundamental data type values within an Object These classes are defined in java.lang Each fundamental data type is represented by a wrapper class ...
... Java has defined "wrapper" classes which hold fundamental data type values within an Object These classes are defined in java.lang Each fundamental data type is represented by a wrapper class ...
Collections
... Java has defined "wrapper" classes which hold fundamental data type values within an Object These classes are defined in java.lang Each fundamental data type is represented by a wrapper class ...
... Java has defined "wrapper" classes which hold fundamental data type values within an Object These classes are defined in java.lang Each fundamental data type is represented by a wrapper class ...
Oracle ADF for Forms Developers
... Transactions: commit, rollback, save points Database interaction: queries and DML Middle-tier data caching and transactional integrity User interface generation Navigation Security Validation ...
... Transactions: commit, rollback, save points Database interaction: queries and DML Middle-tier data caching and transactional integrity User interface generation Navigation Security Validation ...
Hardware
... process where the user are partitioning a physical hard drive into two or more virtual units. One physical drive can be partition into drives C; D: E each representing a separate logical drive but all still part of the one pysical drive. ...
... process where the user are partitioning a physical hard drive into two or more virtual units. One physical drive can be partition into drives C; D: E each representing a separate logical drive but all still part of the one pysical drive. ...
ADO.NET Powerpoint Presentation
... object for accessing data sources. It provides a layer between programming languages and OLE DB (a means of accessing data stores, whether they be databases or otherwise, in a uniform manner), which allows a developer to write programs which access data, without knowing how the database is implement ...
... object for accessing data sources. It provides a layer between programming languages and OLE DB (a means of accessing data stores, whether they be databases or otherwise, in a uniform manner), which allows a developer to write programs which access data, without knowing how the database is implement ...
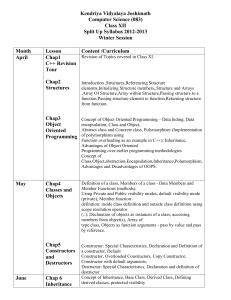
Split Up For Class XII
... Abstract class and Concrete class, Polymorphism (Implementation of polymorphism using Function overloading as an example in C++); Inheritance, Advantages of Object Oriented Programming over earlier programming methodologies Concept of Class,Object,abstraction,Encapsulation,Inheritance,Polumorphism, ...
... Abstract class and Concrete class, Polymorphism (Implementation of polymorphism using Function overloading as an example in C++); Inheritance, Advantages of Object Oriented Programming over earlier programming methodologies Concept of Class,Object,abstraction,Encapsulation,Inheritance,Polumorphism, ...
PDF
... • Brings locality and concurrency to IPC • A PPC is a call from a client object to a server object • Benefits • Client requests are always serviced on their local processor • Clients and servers share the CPU in a manner similar to handoff scheduling • The server has one thread of control for each c ...
... • Brings locality and concurrency to IPC • A PPC is a call from a client object to a server object • Benefits • Client requests are always serviced on their local processor • Clients and servers share the CPU in a manner similar to handoff scheduling • The server has one thread of control for each c ...
Data Access Patterns
... • Customer might include an id field. This would simplify certain routines: update(Customer) • There may be find methods that return more than one record. One option for implementing such methods is to return a collection of DTO’s: List find(criteria)
...
... • Customer might include an id field. This would simplify certain routines: update(Customer) • There may be find methods that return more than one record. One option for implementing such methods is to return a collection of DTO’s: List