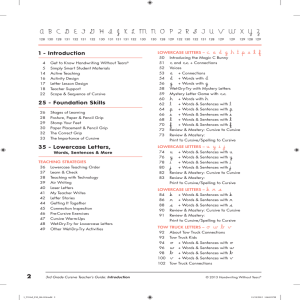
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z
... 3. As children trace the letter, say the parts of letter. We are going to trace a in their air. Say the parts of a with me, Magic c, bump the line, up like a helicopter, bump, back down, bump, travel away. ...
... 3. As children trace the letter, say the parts of letter. We are going to trace a in their air. Say the parts of a with me, Magic c, bump the line, up like a helicopter, bump, back down, bump, travel away. ...
Spear Phishing Attacks—Why They are Successful and How to Stop
... There’s been a rapid and dramatic shift from broad, scattershot attacks to advanced targeted attacks that have had serious consequences for victim organizations. Some of the most famous advanced targeted attacks, such as the attack on RSA, on HBGary Federal, and Operation Aurora all used spear phish ...
... There’s been a rapid and dramatic shift from broad, scattershot attacks to advanced targeted attacks that have had serious consequences for victim organizations. Some of the most famous advanced targeted attacks, such as the attack on RSA, on HBGary Federal, and Operation Aurora all used spear phish ...
Click Here
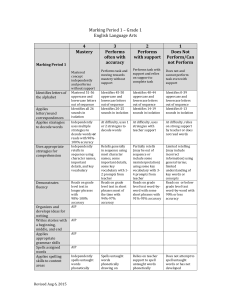
... applying English conventions including capitalization and punctuation with some support Averages 80%89% accuracy on assigned word study Spells untaught words phonetically drawing on phonemic awareness and spelling conventions with some teacher support Forms letters and numerals correctly without sup ...
... applying English conventions including capitalization and punctuation with some support Averages 80%89% accuracy on assigned word study Spells untaught words phonetically drawing on phonemic awareness and spelling conventions with some teacher support Forms letters and numerals correctly without sup ...
Spoofing Attacks
... source IP addresses used inside network Egress filtering-any packet having source IP address not in the network are dropped Avoiding trust relationship based on IP address Unicast Reverse Path Forwarding – discard IP packet that lack verifiable IP source address Idea is simple a reverse path ...
... source IP addresses used inside network Egress filtering-any packet having source IP address not in the network are dropped Avoiding trust relationship based on IP address Unicast Reverse Path Forwarding – discard IP packet that lack verifiable IP source address Idea is simple a reverse path ...
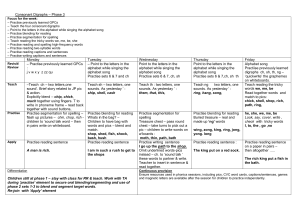
Focus for the week
... – Point to the letters in the alphabet while singing the alphabet song – Practise blending for reading – Practise segmentation for spelling – Teach reading the tricky words we, me, be, she – Practise reading and spelling high-frequency words – Practise reading two-syllable words – Practise reading c ...
... – Point to the letters in the alphabet while singing the alphabet song – Practise blending for reading – Practise segmentation for spelling – Teach reading the tricky words we, me, be, she – Practise reading and spelling high-frequency words – Practise reading two-syllable words – Practise reading c ...
Introduction (cont.)
... flux. With domain flux, each bot periodically (and independently) generates a list of domains that it contacts. The first host that sends a reply that identifies it as a valid C&C server is considered genuine, until the next period of domain generation is started. ...
... flux. With domain flux, each bot periodically (and independently) generates a list of domains that it contacts. The first host that sends a reply that identifies it as a valid C&C server is considered genuine, until the next period of domain generation is started. ...
Slide 1
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
... • Domain and forest functional levels are new features of Windows Server 2008. – The levels defined for each of these are based on the type of server operating systems that are required by the Active Directory design. – The Windows Server 2003 forest functional level is the highest functional level ...
Play Based Literacy Centres handout
... word web – print a word in the centre of a web, write related words around it ...
... word web – print a word in the centre of a web, write related words around it ...
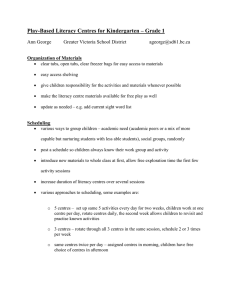
Handouts_files/Module 4 Literacy Centres handout
... o 5 centres – set up same 5 activities every day for two weeks, children work at one centre per day, rotate centres daily, the second week allows children to revisit and practise known activities o 3 centres – rotate through all 3 centres in the same session, schedule 2 or 3 times ...
... o 5 centres – set up same 5 activities every day for two weeks, children work at one centre per day, rotate centres daily, the second week allows children to revisit and practise known activities o 3 centres – rotate through all 3 centres in the same session, schedule 2 or 3 times ...
Handouts_files/Play Based Literacy Centres handout
... word web – print a word in the centre of a web, write related words around it ...
... word web – print a word in the centre of a web, write related words around it ...
Handouts_files/Play Based Literacy Centres handout
... o 5 centres – set up same 5 activities every day for two weeks, children work at one centre per day, rotate centres daily, the second week allows children to revisit and practise known activities o 3 centres – rotate through all 3 centres in the same session, schedule 2 or 3 times ...
... o 5 centres – set up same 5 activities every day for two weeks, children work at one centre per day, rotate centres daily, the second week allows children to revisit and practise known activities o 3 centres – rotate through all 3 centres in the same session, schedule 2 or 3 times ...
Public Presentation - Academic Conferences
... Vendor downloadable product subverted “Cracker gained user-level access to modify the download file. . . . you pray never happens, but it did.” – WordPress, reported on wordpress.org, March 2, 2007 ...
... Vendor downloadable product subverted “Cracker gained user-level access to modify the download file. . . . you pray never happens, but it did.” – WordPress, reported on wordpress.org, March 2, 2007 ...
CEH
... “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
... “looking for system administrator to manage Solaris 10 network” This means that the company has Solaris networks on site E.g., www.jobsdb.com ...
Module 7 Active Directory and Account Management
... • Defines the object classes and their attributes that can be contained in Active Directory • Each object class contains a globally unique identifier (GUID) – Unique number associated with an object name ...
... • Defines the object classes and their attributes that can be contained in Active Directory • Each object class contains a globally unique identifier (GUID) – Unique number associated with an object name ...
Differentiation made Easy: Low
... It’s kind of like a _______________________________________________. It looks like a __________________________________________________. It’s when you __________________________________________________. It’s where you go to ____________________________________________. It smells like _______________ ...
... It’s kind of like a _______________________________________________. It looks like a __________________________________________________. It’s when you __________________________________________________. It’s where you go to ____________________________________________. It smells like _______________ ...
greek and latin in medical terminology
... Many medical terms, while retaining their classical spelling, are pronounced in part as if they were English. Thus, although the final e of a Greek noun is usually pronounced, as in syncope and systole, it is sometimes silenced, as in hydrocele and syndrome. The Latin vowel sequence ie is often pron ...
... Many medical terms, while retaining their classical spelling, are pronounced in part as if they were English. Thus, although the final e of a Greek noun is usually pronounced, as in syncope and systole, it is sometimes silenced, as in hydrocele and syndrome. The Latin vowel sequence ie is often pron ...
Chap 3
... What are the goals of social engineering? A weak key in an encryption algorithm will always mean the text can be easily decrypted. (T/F) What are three strategies for cryptanalysis? The _____________ attack is used to find collisions of hash functions. complete A ______________ __________________ is ...
... What are the goals of social engineering? A weak key in an encryption algorithm will always mean the text can be easily decrypted. (T/F) What are three strategies for cryptanalysis? The _____________ attack is used to find collisions of hash functions. complete A ______________ __________________ is ...
Security+ Guide to Network Security Fundamentals
... Explain denial-of-service (DoS) attacks Explain and discuss ping-of-death attacks Identify major components used in a DDoS attack and how they are installed Understand major types of spoofing attacks Discuss man-in-the-middle attacks, replay attacks, and TCP session hijacking ...
... Explain denial-of-service (DoS) attacks Explain and discuss ping-of-death attacks Identify major components used in a DDoS attack and how they are installed Understand major types of spoofing attacks Discuss man-in-the-middle attacks, replay attacks, and TCP session hijacking ...
Spelling List for October 6th We have continued our study of Greek
... Spelling List for October 6th We have continued our study of Greek and Latin root words. Students will be given 10 words from the root words lists. They will be given all red words. Students will be given a compound sentence containing a simile that they must identify. Rules: ...
... Spelling List for October 6th We have continued our study of Greek and Latin root words. Students will be given 10 words from the root words lists. They will be given all red words. Students will be given a compound sentence containing a simile that they must identify. Rules: ...
Musical Alphabet Letters/Stories
... Musical Alphabet Letters and Stories Objective: For this activity you will be writing a letter to a classmate. Within the letter you need to include 10 or more words spelled using ONLY LETTERS FROM THE MUSICAL ALPHABET (A-G). You will write these words ON A MUSIC STAFF (5 lines/4 spaces), AS IF YOU ...
... Musical Alphabet Letters and Stories Objective: For this activity you will be writing a letter to a classmate. Within the letter you need to include 10 or more words spelled using ONLY LETTERS FROM THE MUSICAL ALPHABET (A-G). You will write these words ON A MUSIC STAFF (5 lines/4 spaces), AS IF YOU ...
IDN homograph attack
The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike, (i.e., they are homographs, hence the term for the attack). For example, a person frequenting citibank.com may be lured to click a link in which the Latin C is replaced with the Cyrillic С.This kind of spoofing attack is also known as script spoofing. Unicode incorporates numerous writing systems, and, for a number of reasons, similar-looking characters such as Greek Ο, Latin O, and Cyrillic О were not assigned the same code. Their incorrect or malicious usage is a possibility for security attacks.The registration of homographic domain names is akin to typosquatting. The major difference is that in typosquatting the perpetrator relies on natural human typos, while in homograph spoofing the perpetrator intentionally deceives the web surfer with visually indistinguishable names. Indeed, it would be a rare accident for a web user to type, e.g., a Cyrillic letter within an otherwise English word such as ""citibank"". There are cases in which a registration can be both typosquatting and homograph spoofing; the pairs of l/I/1, i/j, and 0/O are all both close together on keyboards and bear a certain amount of resemblance to each other.