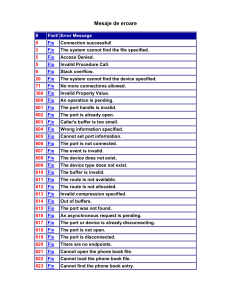
Mesaje de eroare
... Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disconnected from the network. Please ensure that the LAN adapter is connected before enabling Internet Connection Sharing You cannot dial using this connecti ...
... Internet Connection Sharing cannot be enabled. The LAN connection selected as the private network is either not 783 N/A present, or is disconnected from the network. Please ensure that the LAN adapter is connected before enabling Internet Connection Sharing You cannot dial using this connecti ...
Distilling Data in a SIM: A Strategy for the Analysis
... vulnerabilities. Relevance depends on whether the asset has been scanned or not and whether the target has the targeted port open or is vulnerable to the attack shown by the event. Asset criticality depends on whatever criticality was assigned when the asset was modeled. Severity depends on what is ...
... vulnerabilities. Relevance depends on whether the asset has been scanned or not and whether the target has the targeted port open or is vulnerable to the attack shown by the event. Asset criticality depends on whatever criticality was assigned when the asset was modeled. Severity depends on what is ...
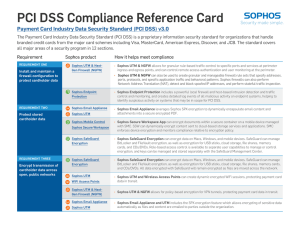
PCI DSS Compliance Reference Card
... ÌÌ Sophos UTM & NGFW can also be used to create granular and manageable firewall rule sets that specify addresses, ports, protocols, and specific application traffic and behavioral patterns. Sophos firewalls can also perform Network Address Translation (NAT), detect and block spoofed IP addresses, a ...
... ÌÌ Sophos UTM & NGFW can also be used to create granular and manageable firewall rule sets that specify addresses, ports, protocols, and specific application traffic and behavioral patterns. Sophos firewalls can also perform Network Address Translation (NAT), detect and block spoofed IP addresses, a ...
SNMP Vulnerabilities - Department of Computer Science
... The open nature and omnipresence of SNMP, combined with the recently discovered vulnerabilities, represent a widespread and comprehensive threat to security of networks everywhere. The limited security built into SNMP, when not enhanced by additional security technology and practices, has been a pot ...
... The open nature and omnipresence of SNMP, combined with the recently discovered vulnerabilities, represent a widespread and comprehensive threat to security of networks everywhere. The limited security built into SNMP, when not enhanced by additional security technology and practices, has been a pot ...
Mobile Agent Security - Indian Institute of Technology
... Agent System An agent system is a platform that can create, interpret, execute, transfer and terminate agents. Like an agent, an agent system is associated with an authority that identifies the person or organization for whom the agent system acts. For example, an agent system with authority Bob imp ...
... Agent System An agent system is a platform that can create, interpret, execute, transfer and terminate agents. Like an agent, an agent system is associated with an authority that identifies the person or organization for whom the agent system acts. For example, an agent system with authority Bob imp ...
Risk Analysis - University at Albany
... – determination of state of risk associated with a system based upon thorough analysis – includes recommendations to support subsequent security controls/decisions. – takes into account business, as well as legal constraints. ...
... – determination of state of risk associated with a system based upon thorough analysis – includes recommendations to support subsequent security controls/decisions. – takes into account business, as well as legal constraints. ...
Data Exfiltration and DNS
... • Active blocking of data exfiltration: Threat Insight not only detects but automatically blocks communications to destinations associated with data-exfiltration attempts. The engine adds destinations associated with data exfiltration automatically to the blacklist in Infoblox DNS Firewall. In addi ...
... • Active blocking of data exfiltration: Threat Insight not only detects but automatically blocks communications to destinations associated with data-exfiltration attempts. The engine adds destinations associated with data exfiltration automatically to the blacklist in Infoblox DNS Firewall. In addi ...
Project proposal
... Goals • Create an open-source, full JSR-82, all Java Bluetooth stack • Build a flexible solution for accessing Bluetooth hardware and harvesting its possibilities to the fullest, leaving enough space for customization • To provide a solution for using Bluetooth from Java with all ‘Java’ benefits – ...
... Goals • Create an open-source, full JSR-82, all Java Bluetooth stack • Build a flexible solution for accessing Bluetooth hardware and harvesting its possibilities to the fullest, leaving enough space for customization • To provide a solution for using Bluetooth from Java with all ‘Java’ benefits – ...
01 - Quick Heal
... The most notable botnet incident of 2013 was the birth of the CryptoLocker. While PC users are becoming more and more aware of fake anti-virus and alerts, CryptoLocker took all by surprise. Delivered by botnets and devised to extort money by encrypting files and holding them on ransom, this ransomwa ...
... The most notable botnet incident of 2013 was the birth of the CryptoLocker. While PC users are becoming more and more aware of fake anti-virus and alerts, CryptoLocker took all by surprise. Delivered by botnets and devised to extort money by encrypting files and holding them on ransom, this ransomwa ...
Malicious Threats - The University of Texas at Dallas
... A virus designed to attach itself to the OS in particular (rather than any application in general) and exhaust computer resources, especially CPU cycles ...
... A virus designed to attach itself to the OS in particular (rather than any application in general) and exhaust computer resources, especially CPU cycles ...
Malicious Threats - The University of Texas at Dallas
... A virus designed to attach itself to the OS in particular (rather than any application in general) and exhaust computer resources, especially CPU cycles ...
... A virus designed to attach itself to the OS in particular (rather than any application in general) and exhaust computer resources, especially CPU cycles ...
Collaborative Approaches to Medical Device Cybersecurity
... © 2016 The MITRE Corporation. All rights reserved. ...
... © 2016 The MITRE Corporation. All rights reserved. ...
Cardenas_Claudia_WorkShopSlides
... In terms of the PHY layer most of these attacks can be counteracted by using different signals and proper configuration of the protocol. Some of MAC flaws have been fixed by the enhanced security of IEEE 802.16e but not all of them. The lack of encryption of MAC management messages that can affect t ...
... In terms of the PHY layer most of these attacks can be counteracted by using different signals and proper configuration of the protocol. Some of MAC flaws have been fixed by the enhanced security of IEEE 802.16e but not all of them. The lack of encryption of MAC management messages that can affect t ...
Control Panel Security
... Securing an enclosure may be as simple as replacing a standard key hole with inserts that have alternative key shapes, such as square bits, triangular holes, and Daimler or Fiat shapes. Changing the shape of the key prevents entry with standard keys and tools, forcing the user to know what lock is i ...
... Securing an enclosure may be as simple as replacing a standard key hole with inserts that have alternative key shapes, such as square bits, triangular holes, and Daimler or Fiat shapes. Changing the shape of the key prevents entry with standard keys and tools, forcing the user to know what lock is i ...
Commiting a Rule Tree
... • Only a very small amount of code in UNIX is written in assembly language. This makes it relatively easy for a computer vendor to get. • The application program interface allows many different types of applications to be easily implemented under UNIX without writing assembly language. ...
... • Only a very small amount of code in UNIX is written in assembly language. This makes it relatively easy for a computer vendor to get. • The application program interface allows many different types of applications to be easily implemented under UNIX without writing assembly language. ...
Managed Network Anomaly Detection
... threats. This process includes analyzing traffic entering, leaving as well as within your network. Threat analysis of this kind is often like finding a needle in a hay stack and requires skills and understanding far beyond the normal abilities of most network professionals. No automated technology c ...
... threats. This process includes analyzing traffic entering, leaving as well as within your network. Threat analysis of this kind is often like finding a needle in a hay stack and requires skills and understanding far beyond the normal abilities of most network professionals. No automated technology c ...
white paper
... hackers. Vulnerabilities in WebKit[5] based browsers are not new. This attack will happen by sending a link to the victim followed by victim’s natural call to action (open the link) the attacker will gain the same permission as the browser. Most attackers will now chain an Elevation of Privileges (E ...
... hackers. Vulnerabilities in WebKit[5] based browsers are not new. This attack will happen by sending a link to the victim followed by victim’s natural call to action (open the link) the attacker will gain the same permission as the browser. Most attackers will now chain an Elevation of Privileges (E ...
PCI DSS glossary of terms - PCI Security Standards Council
... Process of using two or more separate entities (usually persons) operating in concert to protect sensitive functions or information. Both entities are equally responsible for the physical protection of materials involved in vulnerable transactions. No single person is permitted to access or use the ...
... Process of using two or more separate entities (usually persons) operating in concert to protect sensitive functions or information. Both entities are equally responsible for the physical protection of materials involved in vulnerable transactions. No single person is permitted to access or use the ...
Protecting the FPGA Design From Common Threats
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
... Though the definition of zeroization involves a clear plus verification that all data was cleared, most applications will benefit from a zeroization which clears all memory cells of the FPGA. The Cyclone III LS zeroization solution breaks out the clear function and the verification function to provi ...
Internet Vulnerabilities & Criminal Activity
... Shut down drop site Will only work with a hard coded site ...
... Shut down drop site Will only work with a hard coded site ...
From Russia with Love: Behind the Trend Micro
... Micro tools to help identify known command-and-control (C&C) servers and malicious binaries that can affect the devices. In addition to setting up a logging solution, we also connected an email account emulating Richard’s real inbox to the phone. The email address we used resided within the NBC News ...
... Micro tools to help identify known command-and-control (C&C) servers and malicious binaries that can affect the devices. In addition to setting up a logging solution, we also connected an email account emulating Richard’s real inbox to the phone. The email address we used resided within the NBC News ...
Acceptable Use Policy for IT
... colleague’s productivity and nor should it result in any direct costs being borne by
other than for trivial amounts (e.g., an occasional short telephone call).
trusts employees to be fair and sensible when judging what constitutes an acceptable
level of personal use of the comp ...
... colleague’s productivity and nor should it result in any direct costs being borne by
Topics
... Mobile malware: viruses designed for mobile devices Make sure all mobile devices, including tablets and smartphones, have mobile security software to prevent malware infections ...
... Mobile malware: viruses designed for mobile devices Make sure all mobile devices, including tablets and smartphones, have mobile security software to prevent malware infections ...
Mobile device forensics

Mobile device forensics is a branch of digital forensics relating to recovery of digital evidence or data from a mobile device under forensically sound conditions. The phrase mobile device usually refers to mobile phones; however, it can also relate to any digital device that has both internal memory and communication ability, including PDA devices, GPS devices and tablet computers.The use of phones in crime was widely recognised for some years, but the forensic study of mobile devices is a relatively new field, dating from the early 2000s. A proliferation of phones (particularly smartphones) on the consumer market caused a demand for forensic examination of the devices, which could not be met by existing computer forensics techniques.Mobile devices can be used to save several types of personal information such as contacts, photos, calendars and notes, SMS and MMS messages. Smartphones may additionally contain video, email, web browsing information, location information, and social networking messages and contacts.There is growing need for mobile forensics due to several reasons and some of the prominent reasons are: Use of mobile phones to store and transmit personal and corporate information Use of mobile phones in online transactions Law enforcement, criminals and mobile phone devices Mobile device forensics can be particularly challenging on a number of levels:Evidential and technical challenges exist. for example, cell site analysis following from the use of a mobile phone usage coverage, is not an exact science. Consequently, whilst it is possible to determine roughly the cell site zone from which a call was made or received, it is not yet possible to say with any degree of certainty, that a mobile phone call emanated from a specific location e.g. a residential address.To remain competitive, original equipment manufacturers frequently change mobile phone form factors, operating system file structures, data storage, services, peripherals, and even pin connectors and cables. As a result, forensic examiners must use a different forensic process compared to computer forensics.Storage capacity continues to grow thanks to demand for more powerful ""mini computer"" type devices.Not only the types of data but also the way mobile devices are used constantly evolve.Hibernation behaviour in which processes are suspended when the device is powered off or idle but at the same time, remaining active.As a result of these challenges, a wide variety of tools exist to extract evidence from mobile devices; no one tool or method can acquire all the evidence from all devices. It is therefore recommended that forensic examiners, especially those wishing to qualify as expert witnesses in court, undergo extensive training in order to understand how each tool and method acquires evidence; how it maintains standards for forensic soundness; and how it meets legal requirements such as the Daubert standard or Frye standard.