Data Confidentiality
... consist of data about each stage of any transaction, logs are maintained automatically by the system allow the network manager to examine patterns of use audit logs track: – who did what, – at which workstation, – when it occurred. ...
... consist of data about each stage of any transaction, logs are maintained automatically by the system allow the network manager to examine patterns of use audit logs track: – who did what, – at which workstation, – when it occurred. ...
Section for introduction % \section{Introduction} Over the last several
... modifying the startup configuration file to persist execution across reboots of the Android device. At this level of execution, it would be possible for such a process with root access to attain and transmit sensitive personal information including current GPS coordinates, call logs, the phone book, ...
... modifying the startup configuration file to persist execution across reboots of the Android device. At this level of execution, it would be possible for such a process with root access to attain and transmit sensitive personal information including current GPS coordinates, call logs, the phone book, ...
A Common Language for Computer Security Incidents
... An action directed at a target intended to change the state of that target* ...
... An action directed at a target intended to change the state of that target* ...
2003 Format - Google Project Hosting
... i.e. The desktop client is automatically updating upon launch, In cases of maintenance or version upgrade one's only need to update the server and the clients will be updated at launch without any manual intervention. (With exception to changes made at the mobile client code itself). ...
... i.e. The desktop client is automatically updating upon launch, In cases of maintenance or version upgrade one's only need to update the server and the clients will be updated at launch without any manual intervention. (With exception to changes made at the mobile client code itself). ...
COEN 152 Computer Forensics - Santa Clara University's
... Goal is to reconstruct modus operandi of intruder to ...
... Goal is to reconstruct modus operandi of intruder to ...
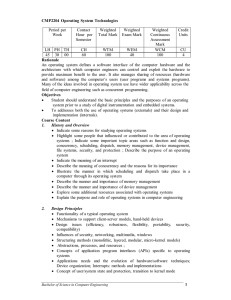
CMP2204 Operating System Technologies
... operation of many (possibly a dynamic number of) tasks; summarize the range of mechanisms (at an operating system level) that are useful to realize concurrent systems and be able to describe the benefits of each; explain the different states that a task may pass through and the data structures neede ...
... operation of many (possibly a dynamic number of) tasks; summarize the range of mechanisms (at an operating system level) that are useful to realize concurrent systems and be able to describe the benefits of each; explain the different states that a task may pass through and the data structures neede ...
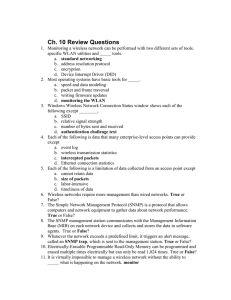
Ch10
... Without a policy that clearly outlines what needs to be protected, how it should be protected, and what users can—and cannot—do in support of the policy, there is no ...
... Without a policy that clearly outlines what needs to be protected, how it should be protected, and what users can—and cannot—do in support of the policy, there is no ...
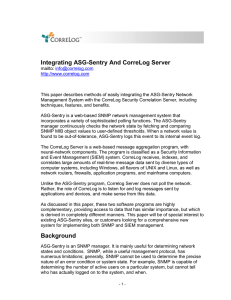
ASG-Sentry White Paper
... source, but far from the only type of data source in the enterprise. CorreLog acts as a higher-level manager, accepting data from a much more diverse (and larger) set of devices, possibly including multiple copies of ASG-Sentry, or other network managers and applications. Strategy: CorreLog Feeds Me ...
... source, but far from the only type of data source in the enterprise. CorreLog acts as a higher-level manager, accepting data from a much more diverse (and larger) set of devices, possibly including multiple copies of ASG-Sentry, or other network managers and applications. Strategy: CorreLog Feeds Me ...
Lecture 5 - The University of Texas at Dallas
... Internet Edition communicates in clear text. Neither employs an encrypted files system” ...
... Internet Edition communicates in clear text. Neither employs an encrypted files system” ...
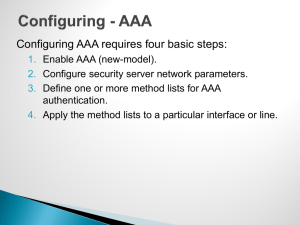
ACCESS CONTROL OPTIONS FOR WIRED NETWORKS
... (CDP), Windows Management Instrumentation (WMI), and more. For Windows laptops, you can perform basic assessments like seeing if required services exist and if they are running on each device. The advantage of using non-AAA enforcement is that there is minimal configuration, and it allows IT to quic ...
... (CDP), Windows Management Instrumentation (WMI), and more. For Windows laptops, you can perform basic assessments like seeing if required services exist and if they are running on each device. The advantage of using non-AAA enforcement is that there is minimal configuration, and it allows IT to quic ...
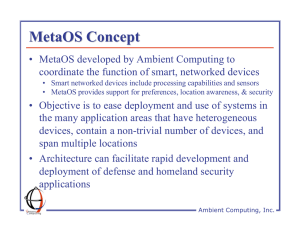
MetaOS Concept • MetaOS developed by Ambient Computing to
... distributed, network-embedded devices • Smart devices and standalone software are abstracted in the same way as resources and peripherals are in traditional operating systems • Supports easy deployment of new services by providing common way to integrate and coordinate devices as well as write appli ...
... distributed, network-embedded devices • Smart devices and standalone software are abstracted in the same way as resources and peripherals are in traditional operating systems • Supports easy deployment of new services by providing common way to integrate and coordinate devices as well as write appli ...
Router/Switch Security
... • Router has been configured to be a NTP client • The NTP source interface has been configured • One or more NTP servers have been configured. • ACL has been established to permit NTP to device. ...
... • Router has been configured to be a NTP client • The NTP source interface has been configured • One or more NTP servers have been configured. • ACL has been established to permit NTP to device. ...
DK1000 Smart Object
... This standards-based turnkey solution allows users, integrators, developers and OEMs to shorten the timeto-market of their IoT products. The Nivis DK1000 provides a complete development environment that helps engineers have our solution up and running in a matter of minutes and reduces R&D costs. ...
... This standards-based turnkey solution allows users, integrators, developers and OEMs to shorten the timeto-market of their IoT products. The Nivis DK1000 provides a complete development environment that helps engineers have our solution up and running in a matter of minutes and reduces R&D costs. ...
Comprehensive Security Protection for
... Some senior executives hope to keep their contact information secure to prevent undesirable calls, IMs, and emails. The Huawei UC2.0 solution classifies user information into personal and public information based on data sensitivity levels. Users (especially senior executives) can set refined and le ...
... Some senior executives hope to keep their contact information secure to prevent undesirable calls, IMs, and emails. The Huawei UC2.0 solution classifies user information into personal and public information based on data sensitivity levels. Users (especially senior executives) can set refined and le ...
Breach Detection in Healthcare
... regulations that are broader in reach than ever before. Today’s penalties for data breaches increase, notification requirements are more stringent, and enforcement agencies have new incentives for taking action against organizations that fail to protect healthcare privacy. Next to that, the require ...
... regulations that are broader in reach than ever before. Today’s penalties for data breaches increase, notification requirements are more stringent, and enforcement agencies have new incentives for taking action against organizations that fail to protect healthcare privacy. Next to that, the require ...
CompTIA Strata™ Fundamentals of IT Technology
... ▪ Tablet (touch screen) ▪ Numeric keypad ▪ Gamepad 1.6 Identify the risks associated with upgrading the following technologies and equipment: ▪ Operating systems (open source and commercial) o Compatibility issues ▪ Upgrade issues ▪ Data loss ▪ PC Speed/storage capability o Compatibility issues ▪ Up ...
... ▪ Tablet (touch screen) ▪ Numeric keypad ▪ Gamepad 1.6 Identify the risks associated with upgrading the following technologies and equipment: ▪ Operating systems (open source and commercial) o Compatibility issues ▪ Upgrade issues ▪ Data loss ▪ PC Speed/storage capability o Compatibility issues ▪ Up ...
網路犯罪案例 Cyber crime Case
... The use of Trojan horse programs, together with web site vulnerabilities against well-known Web sites were used to harvest intrusive information and then, to circumvent tracing, stored this data on a foreign hosted website. Xx telecom companies user accounts and password were compromised with more t ...
... The use of Trojan horse programs, together with web site vulnerabilities against well-known Web sites were used to harvest intrusive information and then, to circumvent tracing, stored this data on a foreign hosted website. Xx telecom companies user accounts and password were compromised with more t ...
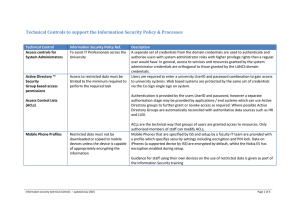
Technical Controls to support the Information
... Furthermore, when a user connects to the network, the PASS system makes an informed decision about what level of network access to allow them based on various criteria such as machine status (i.e. whether known to be virus infected user rights and departmental preference for access level.). With thi ...
... Furthermore, when a user connects to the network, the PASS system makes an informed decision about what level of network access to allow them based on various criteria such as machine status (i.e. whether known to be virus infected user rights and departmental preference for access level.). With thi ...
The Advanced Penetration Testing Boot Camp
... In late July, an interesting story came out of Chicago's suburbs: Hackers broke into a small medical practice's server, encrypted patients' electronic medical records (EMRs) and emails, and demanded a ransom. Instead of paying the ransom, the Surgeons of Lake County turned the server off and called ...
... In late July, an interesting story came out of Chicago's suburbs: Hackers broke into a small medical practice's server, encrypted patients' electronic medical records (EMRs) and emails, and demanded a ransom. Instead of paying the ransom, the Surgeons of Lake County turned the server off and called ...
Visualization
... Correlation uses software technology to analyze aggregated data, in real-time, to determine if specific patterns exist. These patterns of similar security events often correspond to specific securityattacks – whether denial of service,anti virus, or some other form of attack. Visualization, the fina ...
... Correlation uses software technology to analyze aggregated data, in real-time, to determine if specific patterns exist. These patterns of similar security events often correspond to specific securityattacks – whether denial of service,anti virus, or some other form of attack. Visualization, the fina ...
multimedia in mobile
... In order to meet the ever increasing demand by people using mobile technology and its associated service based on multimedia elements in addition to voice, mobile communication technologies has since evolved from analog to digital and 1G to 4G. Therefore, we should take the challenge to combine mobi ...
... In order to meet the ever increasing demand by people using mobile technology and its associated service based on multimedia elements in addition to voice, mobile communication technologies has since evolved from analog to digital and 1G to 4G. Therefore, we should take the challenge to combine mobi ...
Overview
... transaction control) embedded in a smart card. The application domain of PicoDBMS is the management of shared secured portable folders (medical folder, user profile, agenda, etc.). Its indexation and query engines implement new strategies required to cope with the smart card hardware constraints. A ...
... transaction control) embedded in a smart card. The application domain of PicoDBMS is the management of shared secured portable folders (medical folder, user profile, agenda, etc.). Its indexation and query engines implement new strategies required to cope with the smart card hardware constraints. A ...
Mobile device forensics

Mobile device forensics is a branch of digital forensics relating to recovery of digital evidence or data from a mobile device under forensically sound conditions. The phrase mobile device usually refers to mobile phones; however, it can also relate to any digital device that has both internal memory and communication ability, including PDA devices, GPS devices and tablet computers.The use of phones in crime was widely recognised for some years, but the forensic study of mobile devices is a relatively new field, dating from the early 2000s. A proliferation of phones (particularly smartphones) on the consumer market caused a demand for forensic examination of the devices, which could not be met by existing computer forensics techniques.Mobile devices can be used to save several types of personal information such as contacts, photos, calendars and notes, SMS and MMS messages. Smartphones may additionally contain video, email, web browsing information, location information, and social networking messages and contacts.There is growing need for mobile forensics due to several reasons and some of the prominent reasons are: Use of mobile phones to store and transmit personal and corporate information Use of mobile phones in online transactions Law enforcement, criminals and mobile phone devices Mobile device forensics can be particularly challenging on a number of levels:Evidential and technical challenges exist. for example, cell site analysis following from the use of a mobile phone usage coverage, is not an exact science. Consequently, whilst it is possible to determine roughly the cell site zone from which a call was made or received, it is not yet possible to say with any degree of certainty, that a mobile phone call emanated from a specific location e.g. a residential address.To remain competitive, original equipment manufacturers frequently change mobile phone form factors, operating system file structures, data storage, services, peripherals, and even pin connectors and cables. As a result, forensic examiners must use a different forensic process compared to computer forensics.Storage capacity continues to grow thanks to demand for more powerful ""mini computer"" type devices.Not only the types of data but also the way mobile devices are used constantly evolve.Hibernation behaviour in which processes are suspended when the device is powered off or idle but at the same time, remaining active.As a result of these challenges, a wide variety of tools exist to extract evidence from mobile devices; no one tool or method can acquire all the evidence from all devices. It is therefore recommended that forensic examiners, especially those wishing to qualify as expert witnesses in court, undergo extensive training in order to understand how each tool and method acquires evidence; how it maintains standards for forensic soundness; and how it meets legal requirements such as the Daubert standard or Frye standard.