Juniper Networks Secure Access 2000, 4000, and 6000 Appliances
... • Two-unit cluster of SA 6000s: Supports up to 8,000 concurrent users • Three-unit cluster of SA 6000s: Supports up to 12,000 concurrent users • Four-unit cluster of SA 6000s: Supports up to 15,000 concurrent users All performance testing is done based on real-world scenarios with simulation of t ...
... • Two-unit cluster of SA 6000s: Supports up to 8,000 concurrent users • Three-unit cluster of SA 6000s: Supports up to 12,000 concurrent users • Four-unit cluster of SA 6000s: Supports up to 15,000 concurrent users All performance testing is done based on real-world scenarios with simulation of t ...
CIS484-FIREWALL
... 95% of all viruses and Trojans are received via e-mail, through file sharing (like Kazaa or Gnucleus) or through direct download of a malicious program. Firewalls can't prevent this - only a good anti-virus software program can. ...
... 95% of all viruses and Trojans are received via e-mail, through file sharing (like Kazaa or Gnucleus) or through direct download of a malicious program. Firewalls can't prevent this - only a good anti-virus software program can. ...
Title Size 30PT
... become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
... become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
zombie. - People Search Directory
... • Today’s malware is all about stealth • Infected machines report back to attacker, its address, information…?? • Attacker uses backdoor to control the infected machine…. Make it a zombie. A collection of zombies is called a botnet Tanenbaum & Bo, Modern Operating Systems:4th ed., (c) 2013 Prentice- ...
... • Today’s malware is all about stealth • Infected machines report back to attacker, its address, information…?? • Attacker uses backdoor to control the infected machine…. Make it a zombie. A collection of zombies is called a botnet Tanenbaum & Bo, Modern Operating Systems:4th ed., (c) 2013 Prentice- ...
Page PDF - Utah Valley University
... managing hardware and component changes. Requires a community project and portfolio based on advanced server management skills. Lab access fee of $35 for computers applies. ...
... managing hardware and component changes. Requires a community project and portfolio based on advanced server management skills. Lab access fee of $35 for computers applies. ...
PowerPoint
... Often used in presentations The computer equivalent of transparencies Allow for dynamic presentations (pictures, animations, sound) – can be overdone 1 It is listed in Beekman under the name “Presentation graphics” James Tam ...
... Often used in presentations The computer equivalent of transparencies Allow for dynamic presentations (pictures, animations, sound) – can be overdone 1 It is listed in Beekman under the name “Presentation graphics” James Tam ...
Malicious Threats - The University of Texas at Dallas
... TSR scanner - a TSR (memory-resident program) that checks for viruses while other programs are running. It may have some of the characteristics of a monitor and/or behavior blocker. Heuristic scanners - scanners that inspect executable files for code using operations that might denote an unknown vir ...
... TSR scanner - a TSR (memory-resident program) that checks for viruses while other programs are running. It may have some of the characteristics of a monitor and/or behavior blocker. Heuristic scanners - scanners that inspect executable files for code using operations that might denote an unknown vir ...
Malicious Threats - The University of Texas at Dallas
... TSR scanner - a TSR (memory-resident program) that checks for viruses while other programs are running. It may have some of the characteristics of a monitor and/or behavior blocker. Heuristic scanners - scanners that inspect executable files for code using operations that might denote an unknown vir ...
... TSR scanner - a TSR (memory-resident program) that checks for viruses while other programs are running. It may have some of the characteristics of a monitor and/or behavior blocker. Heuristic scanners - scanners that inspect executable files for code using operations that might denote an unknown vir ...
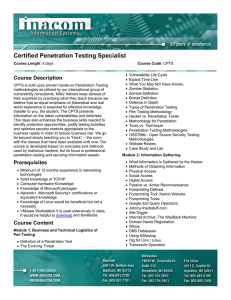
Certified Penetration Testing Specialist
... their expertise by practicing what they teach because we believe that an equal emphasis on theoretical and real world experience is essential for effective knowledge transfer to you, the student. The CPTS presents information on the latest vulnerabilities and defenses. This class also enhances the b ...
... their expertise by practicing what they teach because we believe that an equal emphasis on theoretical and real world experience is essential for effective knowledge transfer to you, the student. The CPTS presents information on the latest vulnerabilities and defenses. This class also enhances the b ...
Figure 9.1 Today`s de facto standard point-and
... Virus patterns/generators exist; script kiddies use these (but most anti-virus software does not!) ...
... Virus patterns/generators exist; script kiddies use these (but most anti-virus software does not!) ...
Active Worms - Computer Science and Engineering
... • Code Red, Nimda, etc. (buffer overflows) • Tricking users into opening malicious email attachments ...
... • Code Red, Nimda, etc. (buffer overflows) • Tricking users into opening malicious email attachments ...
The Inexact Science of Internet Filtering for the K
... “a collaboration of Georgia Tech researchers working with government and industry support to ensure universal K-12 technology access and effective use in Georgia…" "focus of F3 is to help accelerate the application of telecommunications technology for interconnecting K12 schools for collaborative le ...
... “a collaboration of Georgia Tech researchers working with government and industry support to ensure universal K-12 technology access and effective use in Georgia…" "focus of F3 is to help accelerate the application of telecommunications technology for interconnecting K12 schools for collaborative le ...
1 | I.C.T.C. “International Computer Training Center” www.ictc.gr info
... This class will immerse the student into an interactive environment where they will be shown how to scan, test, hack and secure their own systems. Students then learn how intruders escalate privileges and what steps can be taken to secure a system. Who Should Attend This course will significantly be ...
... This class will immerse the student into an interactive environment where they will be shown how to scan, test, hack and secure their own systems. Students then learn how intruders escalate privileges and what steps can be taken to secure a system. Who Should Attend This course will significantly be ...
chap1-slide - GEOCITIES.ws
... – Corruption of information - any unauthorised alteration of files stored on a host computer or data in transmit across the network – Disclosure of information - the dissemination of information to anyone who is not authorised to access that information – Theft of service - the unauthorised use of c ...
... – Corruption of information - any unauthorised alteration of files stored on a host computer or data in transmit across the network – Disclosure of information - the dissemination of information to anyone who is not authorised to access that information – Theft of service - the unauthorised use of c ...
CH09-CompSec2e - MCST-CS
... user is authenticated gateway contacts application on remote host and relays TCP segments between server and user must have proxy code for each application may restrict application features supported tend to be more secure than packet filters disadvantage is the additional processing ove ...
... user is authenticated gateway contacts application on remote host and relays TCP segments between server and user must have proxy code for each application may restrict application features supported tend to be more secure than packet filters disadvantage is the additional processing ove ...
Acceptable Use Policy for IT
... level of personal use of the company’s IT systems. If employees are uncertain they should consult their manager. Any information that is particularly sensitive or vulnerable must be encrypted and/or securely stored so that unauthorised access is prevented (or at least made extremely difficult). Howe ...
... level of personal use of the company’s IT systems. If employees are uncertain they should consult their manager. Any information that is particularly sensitive or vulnerable must be encrypted and/or securely stored so that unauthorised access is prevented (or at least made extremely difficult). Howe ...
Part I: Introduction - Computer Science and Engineering
... • Local subnet scanning – Preferentially scans targets that reside on the same subnet. (Code Red II & Nimda) ...
... • Local subnet scanning – Preferentially scans targets that reside on the same subnet. (Code Red II & Nimda) ...
windows and linux operating systems from a security perspective
... programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the most vital type of system software. An operating system runs u ...
... programs, tools, and utilities that manage computer hardware resources and offer common services for client application software [1]. The operating system is the first program to execute upon booting a computer and is thus considered the most vital type of system software. An operating system runs u ...
Multimedia Application Production
... Program that attaches itself to a file Spreads to other files, and delivers a destructive action called a payload Trojan horses Appear to be harmless programs When they run, install programs on the computer that can be harmful Worm Acts as a free agent, replicating itself numerous times in ...
... Program that attaches itself to a file Spreads to other files, and delivers a destructive action called a payload Trojan horses Appear to be harmless programs When they run, install programs on the computer that can be harmful Worm Acts as a free agent, replicating itself numerous times in ...
class16
... Trojan Horse Useful program that contains hidden code that when invoked performs some unwanted or harmful function Can be used to accomplish functions indirectly that an unauthorized user could not accomplish directly ...
... Trojan Horse Useful program that contains hidden code that when invoked performs some unwanted or harmful function Can be used to accomplish functions indirectly that an unauthorized user could not accomplish directly ...
Firewall Evolution
... The most damaging viruses are said to be “in the wild.” Typically they contain a payload that can wipe out all computer files and target the computer’s BIOS. To be considered “in the wild,” a virus must spread uncontained among infected computers in the general public as a result of normal daily ope ...
... The most damaging viruses are said to be “in the wild.” Typically they contain a payload that can wipe out all computer files and target the computer’s BIOS. To be considered “in the wild,” a virus must spread uncontained among infected computers in the general public as a result of normal daily ope ...
V-NetLab: An Approach for Realizing Logically Isolated Networks for Security Experiments
... host, but in reality, each physical host can support about 100 vmnet interfaces. In this figure, vm2, vm3 and vm4 are supposed to be on the same logical hub. Since vm2 and vm3 have been mapped to the same physical host, they can share a single vmnet interface, called vmnet1 in the figure. vm4 needs ...
... host, but in reality, each physical host can support about 100 vmnet interfaces. In this figure, vm2, vm3 and vm4 are supposed to be on the same logical hub. Since vm2 and vm3 have been mapped to the same physical host, they can share a single vmnet interface, called vmnet1 in the figure. vm4 needs ...
Taking on the Giant (anatomy of an attack)
... against An aggressive “default deny” host-based firewall config would have prevented infection (i.e., only allow specific hosts to connect to port 5168) ...
... against An aggressive “default deny” host-based firewall config would have prevented infection (i.e., only allow specific hosts to connect to port 5168) ...
Computer Security and Penetration Testing Chapter 17 Linux
... accounts are vulnerable to hacking attempts • Various networking services are available as part of some Linux operating systems; however, these services are highly vulnerable to unauthorized access • Weaknesses within some utilities in both Linux and UNIX-based operating systems allow hackers to bre ...
... accounts are vulnerable to hacking attempts • Various networking services are available as part of some Linux operating systems; however, these services are highly vulnerable to unauthorized access • Weaknesses within some utilities in both Linux and UNIX-based operating systems allow hackers to bre ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.