Principles of Computer Security
... • Describe various types of computer and network attacks, including denial-of-service, spoofing, hijacking, and password guessing. • Identify the different types of malicious software that exist, including viruses, worms, Trojan horses, logic bombs, time bombs, and rootkits. • Explain how social eng ...
... • Describe various types of computer and network attacks, including denial-of-service, spoofing, hijacking, and password guessing. • Identify the different types of malicious software that exist, including viruses, worms, Trojan horses, logic bombs, time bombs, and rootkits. • Explain how social eng ...
Network Vulnerability Scanning - Texas Tech University Departments
... – Automation is Crucial • Manual detection and remediation workflow is too slow, too expensive and ineffective ...
... – Automation is Crucial • Manual detection and remediation workflow is too slow, too expensive and ineffective ...
Spear Phishing Attacks—Why They are Successful and How to Stop
... tactics easily circumvent signature-based and reputation-based analysis. Further, to effectively defend corporate networks, organizations need systems that inspect across many protocols and throughout the protocol stack, including the network layer, operating systems, applications, browsers, and plu ...
... tactics easily circumvent signature-based and reputation-based analysis. Further, to effectively defend corporate networks, organizations need systems that inspect across many protocols and throughout the protocol stack, including the network layer, operating systems, applications, browsers, and plu ...
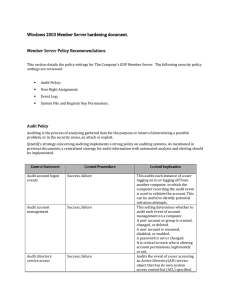
Server hardening - Cisco Security Solutions
... unauthorised activity. Anyone with this privilege could configure the settings of a hardware component, in such a way as to cause it to fail. A user with this privilege could delete a volume, leading to the loss of data or a DoS condition. An attacker with this privilege could monitor a computer's p ...
... unauthorised activity. Anyone with this privilege could configure the settings of a hardware component, in such a way as to cause it to fail. A user with this privilege could delete a volume, leading to the loss of data or a DoS condition. An attacker with this privilege could monitor a computer's p ...
Web Threats Challenges and Solutions
... convey information to the hacker. In 2007, fraudulent emails were sent purporting to be from the Federal Trade Commission. These emails claimed that a complaint had been filed against the company and contained an attachment. If the recipient opened the attachment, a keylogging Trojan was deployed th ...
... convey information to the hacker. In 2007, fraudulent emails were sent purporting to be from the Federal Trade Commission. These emails claimed that a complaint had been filed against the company and contained an attachment. If the recipient opened the attachment, a keylogging Trojan was deployed th ...
Commiting a Rule Tree
... • UNIX has several advantages as an operating system, such as portability, powerful utilities, device independence, being multitasking, allowing multi-user, low system requirements, and the availability of free software. • There are disadvantages of using the UNIX operating system. Some of them are ...
... • UNIX has several advantages as an operating system, such as portability, powerful utilities, device independence, being multitasking, allowing multi-user, low system requirements, and the availability of free software. • There are disadvantages of using the UNIX operating system. Some of them are ...
1. The Threat Environment: Attackers and their Attacks
... ◦ In addition, direct-propagation worms can jump from one computer to another without human intervention on the receiving computer ◦ Computer must have a vulnerability for direct propagation to work ...
... ◦ In addition, direct-propagation worms can jump from one computer to another without human intervention on the receiving computer ◦ Computer must have a vulnerability for direct propagation to work ...
A Specialization Toolkit to Increase the Diversity of Operating Systems
... security-related quasi-invariants and create mechanisms to guard these security faults. The key advantage of our approach is that the same tools developed for specialization can be and should be used towards the preservation and enhancement of all important system properties such as performance, rel ...
... security-related quasi-invariants and create mechanisms to guard these security faults. The key advantage of our approach is that the same tools developed for specialization can be and should be used towards the preservation and enhancement of all important system properties such as performance, rel ...
Synchronization of VM probes for observing P2P traffic and
... Windows (TM). As shown in Figure 5, on guest Windows(TM) OS, we apply three kinds of interruptive debugging techniques to detect the incidents and invoke capture (snapshot) functions of VMM. On VMM side, we modify debug register handler to execute snapshot routine of VMM. Receiving notification, prop ...
... Windows (TM). As shown in Figure 5, on guest Windows(TM) OS, we apply three kinds of interruptive debugging techniques to detect the incidents and invoke capture (snapshot) functions of VMM. On VMM side, we modify debug register handler to execute snapshot routine of VMM. Receiving notification, prop ...
faculty.elgin.edu
... • Stop logged-on users from accessing files and folders that they are not assigned read or write permission to • Relatively easy to work around NTFS permissions • When you have physical access to the computer • To secure data on desktop computers and laptops, ...
... • Stop logged-on users from accessing files and folders that they are not assigned read or write permission to • Relatively easy to work around NTFS permissions • When you have physical access to the computer • To secure data on desktop computers and laptops, ...
The Evolution of Malicious Agents - Cyber Defense
... The paper proceeds by analyzing features and limitations of remotely controlled agents such as Back Orifice and NetBus, as well as of distributed denial-of-service software such as Trinoo and TFN. These programs can provide attackers with the ability to remotely issue commands on the infected machin ...
... The paper proceeds by analyzing features and limitations of remotely controlled agents such as Back Orifice and NetBus, as well as of distributed denial-of-service software such as Trinoo and TFN. These programs can provide attackers with the ability to remotely issue commands on the infected machin ...
The Blaster Worm: Then and Now
... 1). A comparison of the number of US-based infections during the outbreak with its persistent population shows them to both to be roughly 55 percent. Overall, the top-level domain distribution across countries changed very little between outbreak and persistence. The number of infected systems in di ...
... 1). A comparison of the number of US-based infections during the outbreak with its persistent population shows them to both to be roughly 55 percent. Overall, the top-level domain distribution across countries changed very little between outbreak and persistence. The number of infected systems in di ...
Web Security Security+ Guide to Network Security Fundamentals
... • Buffer overflow attacks are common ways to gain unauthorized access to Web servers • SMTP relay attacks allow spammers to send thousands of e-mail messages to users • Web programming tools provide another foothold for Web attacks • Dynamic content can also be used by attackers – Sometimes called r ...
... • Buffer overflow attacks are common ways to gain unauthorized access to Web servers • SMTP relay attacks allow spammers to send thousands of e-mail messages to users • Web programming tools provide another foothold for Web attacks • Dynamic content can also be used by attackers – Sometimes called r ...
Secure_Email_and_Web_Browsing_SEC
... No credentials (login/password) over email No same password for different place/software/service No clicking on links sent by your contacts before confirmation. No use of untrusted media (USB stick, CD, DVD, Hard-drive) No use of Internet randomly downloaded software No forwarding of unverified info ...
... No credentials (login/password) over email No same password for different place/software/service No clicking on links sent by your contacts before confirmation. No use of untrusted media (USB stick, CD, DVD, Hard-drive) No use of Internet randomly downloaded software No forwarding of unverified info ...
Security
... it is left on the terminal for the next unsuspecting user this program reads the password and stores it © 2000 Franz Kurfess ...
... it is left on the terminal for the next unsuspecting user this program reads the password and stores it © 2000 Franz Kurfess ...
Chapter12-Security
... • While computer systems today have some of the best security systems ever, they are more vulnerable than ever before • This vulnerability stems from the world-wide access to computer systems via the Internet • Computer and network security comes in many forms, including encryption algorithms, acces ...
... • While computer systems today have some of the best security systems ever, they are more vulnerable than ever before • This vulnerability stems from the world-wide access to computer systems via the Internet • Computer and network security comes in many forms, including encryption algorithms, acces ...
Physical Security
... developers to ensure that they could gain access to an application even if something were to happen in the future to prevent normal access methods. – The term backdoor is also, and more commonly, used to refer to programs that attackers install after gaining unauthorized access to a system to ensure ...
... developers to ensure that they could gain access to an application even if something were to happen in the future to prevent normal access methods. – The term backdoor is also, and more commonly, used to refer to programs that attackers install after gaining unauthorized access to a system to ensure ...
Types of Attacks - Digital Locker and Personal Web Space
... Principles of Computer Security: CompTIA Security+® and Beyond, Second Edition ...
... Principles of Computer Security: CompTIA Security+® and Beyond, Second Edition ...
CounterACT: Powerful, Automated Network Protection
... When the recent Conficker outbreak wreaked havoc upon Windows-based LANs in enterprises worldwide, CounterACTTM customers called in to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” ...
... When the recent Conficker outbreak wreaked havoc upon Windows-based LANs in enterprises worldwide, CounterACTTM customers called in to say: “our network is perfectly safe – CounterACT’s automatic zero-day threat prevention provided us with the 24/7/365 protection we have come to expect and rely on!” ...
Chapter 12
... the best security systems ever, they are more vulnerable than ever before • This vulnerability stems from the worldwide access to computer systems via the Internet • Computer and network security comes in many forms, including encryption algorithms, access to facilities, digital signatures, and usin ...
... the best security systems ever, they are more vulnerable than ever before • This vulnerability stems from the worldwide access to computer systems via the Internet • Computer and network security comes in many forms, including encryption algorithms, access to facilities, digital signatures, and usin ...
12 things effective Page title appears here
... months ago can help you understand what is happening today. By exporting traffic analytics to an off-box collector, organizations can store historical information such as hidden communications, client/ server attacks, VPN usage, VoIP traffic or Internet application activity by user for as long as de ...
... months ago can help you understand what is happening today. By exporting traffic analytics to an off-box collector, organizations can store historical information such as hidden communications, client/ server attacks, VPN usage, VoIP traffic or Internet application activity by user for as long as de ...
Managed Network Anomaly Detection
... threats. This process includes analyzing traffic entering, leaving as well as within your network. Threat analysis of this kind is often like finding a needle in a hay stack and requires skills and understanding far beyond the normal abilities of most network professionals. No automated technology c ...
... threats. This process includes analyzing traffic entering, leaving as well as within your network. Threat analysis of this kind is often like finding a needle in a hay stack and requires skills and understanding far beyond the normal abilities of most network professionals. No automated technology c ...
Operating Systems
... Denial of service as long as virus runs Permanently damage hardware Target a competitor's computer do ...
... Denial of service as long as virus runs Permanently damage hardware Target a competitor's computer do ...
Malware

Malware, short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems. Malware is defined by its malicious intent, acting against the requirements of the computer user, and does not include software that causes unintentional harm due to some deficiency. The term badware is sometimes used, and applied to both true (malicious) malware and unintentionally harmful software.Malware may be stealthy, intended to steal information or spy on computer users for an extended period without their knowledge, as for example Regin, or it may be designed to cause harm, often as sabotage (e.g., Stuxnet), or to extort payment (CryptoLocker). 'Malware' is an umbrella term used to refer to a variety of forms of hostile or intrusive software, including computer viruses, worms, trojan horses, ransomware, spyware, adware, scareware, and other malicious programs. It can take the form of executable code, scripts, active content, and other software. Malware is often disguised as, or embedded in, non-malicious files. As of 2011 the majority of active malware threats were worms or trojans rather than viruses.In law, malware is sometimes known as a computer contaminant, as in the legal codes of several U.S. states.Spyware or other malware is sometimes found embedded in programs supplied officially by companies, e.g., downloadable from websites, that appear useful or attractive, but may have, for example, additional hidden tracking functionality that gathers marketing statistics. An example of such software, which was described as illegitimate, is the Sony rootkit, a Trojan embedded into CDs sold by Sony, which silently installed and concealed itself on purchasers' computers with the intention of preventing illicit copying; it also reported on users' listening habits, and unintentionally created vulnerabilities that were exploited by unrelated malware.Software such as anti-virus, anti-malware, and firewalls are used to protect against activity identified as malicious, and to recover from attacks.