操作系统
... 1. Windows temporarily keeps deleted files in Recycle Bin, while Linux rm delete them instantly. 2. Windows task manager allows us to kill processes with their program names, while Linux uses IDs to kill specific processes. 3. Windows starts an appropriate application for a file double-clicked, whil ...
... 1. Windows temporarily keeps deleted files in Recycle Bin, while Linux rm delete them instantly. 2. Windows task manager allows us to kill processes with their program names, while Linux uses IDs to kill specific processes. 3. Windows starts an appropriate application for a file double-clicked, whil ...
This course is an introduction to computer operating systems
... MAC230 Comparative Operating Systems 3 Credits; 4 Hours (3 lecture, 1 lab) ...
... MAC230 Comparative Operating Systems 3 Credits; 4 Hours (3 lecture, 1 lab) ...
Tutorail-two-with
... with at a very low level. The user need only specify the device and the operation to perform on it, while the system converts that request into device- or controllerspecific commands. User-level programs cannot be trusted to access only devices they should have access to and to access them only when ...
... with at a very low level. The user need only specify the device and the operation to perform on it, while the system converts that request into device- or controllerspecific commands. User-level programs cannot be trusted to access only devices they should have access to and to access them only when ...
Structure of Operating Systems
... computer as opposed to a virtual machine? – It can try to perform a protected operation… but a virtual machine monitor (VMM) could trap those requests and emulate them – It could measure timing very carefully… but modern hardware runs at variable speeds ...
... computer as opposed to a virtual machine? – It can try to perform a protected operation… but a virtual machine monitor (VMM) could trap those requests and emulate them – It could measure timing very carefully… but modern hardware runs at variable speeds ...
System Software - Computing Systems` Blog
... • is responsible for finding and organizing data, and applications on the disk. • It principally consists of only 4 parts: – A boot record, which activates the operating system. – IO.SYS file, which interfaced ROM BIOS with installation of device drivers. – MSDOS.SYS file, which handling the file sy ...
... • is responsible for finding and organizing data, and applications on the disk. • It principally consists of only 4 parts: – A boot record, which activates the operating system. – IO.SYS file, which interfaced ROM BIOS with installation of device drivers. – MSDOS.SYS file, which handling the file sy ...
Buzz Words
... a. POST test, activate BIOS, check settings, load OS into RAM b. Activate BIOS, POST test, load OS into RAM, check settings c. Check settings, load OS into RAM, activate BIOS, POST test d. Load OS into RAM, check settings, activate BIOS, POST test 7. When a computer is in Safe mode: a. only the esse ...
... a. POST test, activate BIOS, check settings, load OS into RAM b. Activate BIOS, POST test, load OS into RAM, check settings c. Check settings, load OS into RAM, activate BIOS, POST test d. Load OS into RAM, check settings, activate BIOS, POST test 7. When a computer is in Safe mode: a. only the esse ...
Basic Functions of the operating system
... – Allows program to run as if it was on an earlier OS • An XP only program can run in Vista/y • Use if you don’t have Virtual PC ...
... – Allows program to run as if it was on an earlier OS • An XP only program can run in Vista/y • Use if you don’t have Virtual PC ...
Services - University of Worcester
... – starts kernel-mode part of the Windows subsystem found at systemroot\System32\Win32k.sys » Windows XP Professional can now switch from text mode to graphics mode » Windows-based applications can run in the Windows subsystem » applications can now access operating system functions, such as displayi ...
... – starts kernel-mode part of the Windows subsystem found at systemroot\System32\Win32k.sys » Windows XP Professional can now switch from text mode to graphics mode » Windows-based applications can run in the Windows subsystem » applications can now access operating system functions, such as displayi ...
Windows XP Boot Process
... Detects hardware and Hardware Phase • Ntldr starts Ntdetect.com, a program that performs basic device detection. Ntldr then passes Boot.ini information, as well as hardware and software data in the registry, to Ntoskrnl.exe. Ntdetect.com detects hardware profile information (for example, docked and ...
... Detects hardware and Hardware Phase • Ntldr starts Ntdetect.com, a program that performs basic device detection. Ntldr then passes Boot.ini information, as well as hardware and software data in the registry, to Ntoskrnl.exe. Ntdetect.com detects hardware profile information (for example, docked and ...
Identify Steps in the Startup Process
... Initial startup phase—CMOS contains boot order and finds a boot device ...
... Initial startup phase—CMOS contains boot order and finds a boot device ...
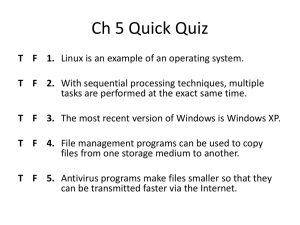
Ch 5 Quick Quiz
... T F 3. The most recent version of Windows is Windows XP. T F 4. File management programs can be used to copy files from one storage medium to another. T F 5. Antivirus programs make files smaller so that they can be transmitted faster via the Internet. ...
... T F 3. The most recent version of Windows is Windows XP. T F 4. File management programs can be used to copy files from one storage medium to another. T F 5. Antivirus programs make files smaller so that they can be transmitted faster via the Internet. ...
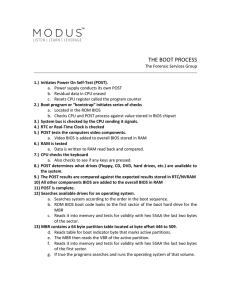
THE BOOT PROCESS The Forensic Services Group 1.) Initiates
... a. The contents of BOOT.INI for startup options and boot menu options b. If dual booting is enabled and the other OS is non-NT BOOTSEC.DOS runs. c. If SCSI drives are attached to the system NTBOOLDD.SYS runs. 15.) NTDETECT.COM executes and searches the system for installed hardware and passes data t ...
... a. The contents of BOOT.INI for startup options and boot menu options b. If dual booting is enabled and the other OS is non-NT BOOTSEC.DOS runs. c. If SCSI drives are attached to the system NTBOOLDD.SYS runs. 15.) NTDETECT.COM executes and searches the system for installed hardware and passes data t ...
Chapter 3: System Software
... – Windows 3.x over DOS – Workplace Shell for OS/2 – X – a windowing environment for many OSs especially various versions of Unix ...
... – Windows 3.x over DOS – Workplace Shell for OS/2 – X – a windowing environment for many OSs especially various versions of Unix ...
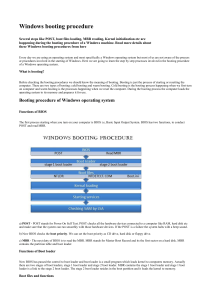
Windows booting procedure
... When kernel is loaded in the primary memory services for each process is started and the registry entry for those services can be found at HKEY_LOCAL_MACHINE - System - Current control set - Services. Winlogon.exe (C:\Windows\system32\winlogon.exe) is the last service started during this process. Wi ...
... When kernel is loaded in the primary memory services for each process is started and the registry entry for those services can be found at HKEY_LOCAL_MACHINE - System - Current control set - Services. Winlogon.exe (C:\Windows\system32\winlogon.exe) is the last service started during this process. Wi ...
Training
... Operating system - controls the use of hardware resources, External and Internal Utilities --supplement the system ...
... Operating system - controls the use of hardware resources, External and Internal Utilities --supplement the system ...
2.1 Input Output Control System
... 1. The power supply send a signal to the component s in the system unit 2. The processor finds the ROM chip(s) that contain the BIOS (basic input output system) 3. The BIOS performs the POST(power-on self test), which checks components such as mouse, keyboard and adapter cards. ...
... 1. The power supply send a signal to the component s in the system unit 2. The processor finds the ROM chip(s) that contain the BIOS (basic input output system) 3. The BIOS performs the POST(power-on self test), which checks components such as mouse, keyboard and adapter cards. ...
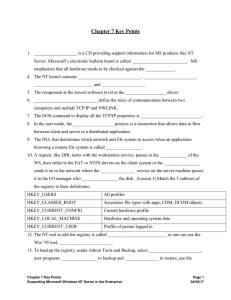
MS Word file - Maricopa Community Colleges
... 14. (Lesson 4) Following the POST test, the initial startup looks at the first sector on either the hard drive or a floppy for the _________________________ table. 15. During the boot loader process, NT uses programs ________________, the operating system loader, _____________________ a hidden syste ...
... 14. (Lesson 4) Following the POST test, the initial startup looks at the first sector on either the hard drive or a floppy for the _________________________ table. 15. During the boot loader process, NT uses programs ________________, the operating system loader, _____________________ a hidden syste ...