Windows - Part I
... How windows executes code The Windows operating system uses two modes to maintain operating system efficiency and integrity: user mode and kernel mode. The architecture of 80386 and higher processors defines four privilege levels, called rings, to protect system code and data from being overwritte ...
... How windows executes code The Windows operating system uses two modes to maintain operating system efficiency and integrity: user mode and kernel mode. The architecture of 80386 and higher processors defines four privilege levels, called rings, to protect system code and data from being overwritte ...
Netscape: System Commander in Patagonia
... host the System Oberon. Oberon is a programming language, a run-time- and operating system with an integrated development environment for object oriented or structured programming. The Oberon system is kept lean, simple and easily fits into a very small disk partition or main memory. All data is sto ...
... host the System Oberon. Oberon is a programming language, a run-time- and operating system with an integrated development environment for object oriented or structured programming. The Oberon system is kept lean, simple and easily fits into a very small disk partition or main memory. All data is sto ...
Chapter 13 Troubleshooting the Operating System
... • Test the notification processes. It should be documented who is to be notified in case of an outage. • Check the locations of any hot spare equipment or servers. • Verify that any support contracts that are on equipment are still in effect, and that all the contact numbers are available. • Test th ...
... • Test the notification processes. It should be documented who is to be notified in case of an outage. • Check the locations of any hot spare equipment or servers. • Verify that any support contracts that are on equipment are still in effect, and that all the contact numbers are available. • Test th ...
ITE-II-ch13
... • Test the notification processes. It should be documented who is to be notified in case of an outage. • Check the locations of any hot spare equipment or servers. • Verify that any support contracts that are on equipment are still in effect, and that all the contact numbers are available. • Test th ...
... • Test the notification processes. It should be documented who is to be notified in case of an outage. • Check the locations of any hot spare equipment or servers. • Verify that any support contracts that are on equipment are still in effect, and that all the contact numbers are available. • Test th ...
Operating Systems Operating System Component and Structure
... – convenient: no need for rebooting for newly added modules – efficient: no need for messaging passing unlike microkernel – flexible: any module can call any other module unlike layered model ...
... – convenient: no need for rebooting for newly added modules – efficient: no need for messaging passing unlike microkernel – flexible: any module can call any other module unlike layered model ...
Chapter 9 Linux Installation Procedures
... • Install Xfree86 by using the system package manager to install the correct package. • X server comes with many packages. • Only one of the packages will contain the actual server, the other packages will be the support libraries, fonts, utilities, and so on. ...
... • Install Xfree86 by using the system package manager to install the correct package. • X server comes with many packages. • Only one of the packages will contain the actual server, the other packages will be the support libraries, fonts, utilities, and so on. ...
FAT:
... system HPFS contained several important new features. When Microsoft created their new operating system, they borrowed many of these concepts for NTFS. When Microsoft created their new operating system, they borrowed many of these concepts for NTFS. Probably as a result of this common ancestry, HPFS ...
... system HPFS contained several important new features. When Microsoft created their new operating system, they borrowed many of these concepts for NTFS. When Microsoft created their new operating system, they borrowed many of these concepts for NTFS. Probably as a result of this common ancestry, HPFS ...
OPERATING SYSTEM FUNCTIONS
... directory hierarchy, the root directory. Such absolute path names consist of the list of directories that must be traversed from the root directory to get to the file, with slashes separating the components. In Fig. 1-6, the path for file CS101 is /Faculty/Prof.Brown/Courses/CS101. The leading slash ...
... directory hierarchy, the root directory. Such absolute path names consist of the list of directories that must be traversed from the root directory to get to the file, with slashes separating the components. In Fig. 1-6, the path for file CS101 is /Faculty/Prof.Brown/Courses/CS101. The leading slash ...
Chapter 2: System Structures
... and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code l Accounting - To keep track of which users use how much and what kinds of computer resources l Protection and security - The owners of information stored in a multiuser or netw ...
... and file storage) may have special allocation code, others (such as I/O devices) may have general request and release code l Accounting - To keep track of which users use how much and what kinds of computer resources l Protection and security - The owners of information stored in a multiuser or netw ...
Windows 2000 OS Introduction
... – Advanced tuning/configuration requires direct access • Regedt32 or Regedit ...
... – Advanced tuning/configuration requires direct access • Regedt32 or Regedit ...
chap03
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for ...
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for ...
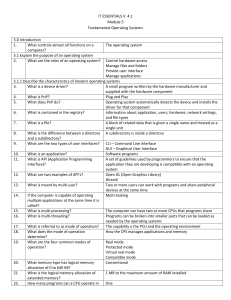
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems 5
... A partition on the disk that contains an image of the bootable partition that is created when the computer was built. Contact the manufacturer ...
... A partition on the disk that contains an image of the bootable partition that is created when the computer was built. Contact the manufacturer ...
IT ESSENTIALS V. 4.1 Module 5 Fundamental Operating Systems
... manage network resources in Windows? Worksheet: NOS certifications and jobs 5.3 Determine operating system based on customer needs 5.3.1 Identify applications and environment that are compatible with an operating system ...
... manage network resources in Windows? Worksheet: NOS certifications and jobs 5.3 Determine operating system based on customer needs 5.3.1 Identify applications and environment that are compatible with an operating system ...
Unit OS 11: Startup, Crashes, Troubleshooting
... Ntoskrnl.exe, Hal.dll, and Bootvid.dll (and Kdcom.dll for XP and later) The registry SYSTEM hive (\Windows\System32\Config\System) Later this becomes HKLM\System Based on the SYSTEM hive, the boot drivers are loaded Boot driver: critical to boot process (e.g. boot file system driver) Transfers contr ...
... Ntoskrnl.exe, Hal.dll, and Bootvid.dll (and Kdcom.dll for XP and later) The registry SYSTEM hive (\Windows\System32\Config\System) Later this becomes HKLM\System Based on the SYSTEM hive, the boot drivers are loaded Boot driver: critical to boot process (e.g. boot file system driver) Transfers contr ...
COS 318: Operating Systems Overview Kai Li Computer Science Department
... System calls: fork, exec, exit, … System calls: file open, close, read and write Control the CPU so that users won’t stuck by running ...
... System calls: fork, exec, exit, … System calls: file open, close, read and write Control the CPU so that users won’t stuck by running ...
The LINUX Operating System
... Resource Management • Use of semaphores • 1 process at a time can access to some resource • The semaphore data structure includes a count of number of processes that wish to use a resource, a waking parameter (number of processes waiting to be woken up), and a wait queue. ...
... Resource Management • Use of semaphores • 1 process at a time can access to some resource • The semaphore data structure includes a count of number of processes that wish to use a resource, a waking parameter (number of processes waiting to be woken up), and a wait queue. ...
Chapter 8 Operating Systems and Utility Programs
... Warm boot from Windows desktop Warm boot from system unit ...
... Warm boot from Windows desktop Warm boot from system unit ...
doc
... through a user interface. In older systems, a character based interface may have been used, e.g. “Copy A:assign.doc C:”. Most operating systems today use a windows like Graphical User Interface (GUI) in which graphical objects called icons represent commonly used features. Applications: these progra ...
... through a user interface. In older systems, a character based interface may have been used, e.g. “Copy A:assign.doc C:”. Most operating systems today use a windows like Graphical User Interface (GUI) in which graphical objects called icons represent commonly used features. Applications: these progra ...
Server Installation - Information Technology Gate
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for ...
... Identify a computer on the network Windows communicates the computer name to other computers on the subnet so it should be unique Name of computer is not related to how the computer is recognized on the Internet In Linux, the hostname can exist on more than computer, it only uses IP addresses for ...
Chapter 18 PowerPoint
... all objects displayed on the screen and interacts with the display system and drivers. The user interface is a 32-bit shell including file system and system service tools. The user component is the I/O manager, which receives and routes input from devices. The kernel is the core of the OS that contr ...
... all objects displayed on the screen and interacts with the display system and drivers. The user interface is a 32-bit shell including file system and system service tools. The user component is the I/O manager, which receives and routes input from devices. The kernel is the core of the OS that contr ...
PPT 02 - Mesa Community College
... The OS handles all I/O to and from storage devices, keyboards, and displays. Devices installed on each computer may be different, so the OS uses device drivers. Plug-and-Play – devices have software encoded on them (ROM), which allows them to be recognized by the OS when installed, so the device dri ...
... The OS handles all I/O to and from storage devices, keyboards, and displays. Devices installed on each computer may be different, so the OS uses device drivers. Plug-and-Play – devices have software encoded on them (ROM), which allows them to be recognized by the OS when installed, so the device dri ...
operating system
... An operating system is software installed on the computer to make it possible to use it without needing a degree in electronic engineering ...
... An operating system is software installed on the computer to make it possible to use it without needing a degree in electronic engineering ...