Inference of a Phylogenetic Tree: Hierarchical Clustering
... Agglomerative hierarchical clustering was chosen as a distance method and a genetic algorithm as an optimization method. Both applications were implemented using object-oriented design in C++ and share support classes representing a phylogenetic (binary) tree: an abstract parent TU_Node class that i ...
... Agglomerative hierarchical clustering was chosen as a distance method and a genetic algorithm as an optimization method. Both applications were implemented using object-oriented design in C++ and share support classes representing a phylogenetic (binary) tree: an abstract parent TU_Node class that i ...
Aucun titre de diapositive - Universidad Nacional De Colombia
... New ESTs are searched against existing consensus and singletons using crossmatch. Matching sequences are added to extend existing clusters and consensus. Non-matching sequences are processed using d2 cluster against the entire database and the new produces clusters are renamed)Gene Index ID change. ...
... New ESTs are searched against existing consensus and singletons using crossmatch. Matching sequences are added to extend existing clusters and consensus. Non-matching sequences are processed using d2 cluster against the entire database and the new produces clusters are renamed)Gene Index ID change. ...
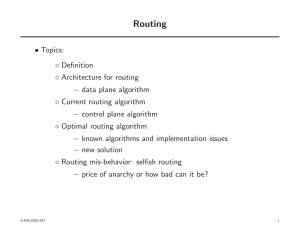
Routing
... • The Dijkstra’s algorithm is totally distributed ◦ It can also be implemented in parallel and ◦ Does not require synchronization • In the algorithm ◦ Dj can be thought of as estimate of shortest path length between 1 and j during the course of algorithm • The algorithm is one of the earliest exampl ...
... • The Dijkstra’s algorithm is totally distributed ◦ It can also be implemented in parallel and ◦ Does not require synchronization • In the algorithm ◦ Dj can be thought of as estimate of shortest path length between 1 and j during the course of algorithm • The algorithm is one of the earliest exampl ...
Algorithm to extract REP sequences Pattern
... function box. It consists of the name of a function, perhaps one or more required arguments, and optional keywords and flags. A function may be thought of as a black box: you feed it information, ...
... function box. It consists of the name of a function, perhaps one or more required arguments, and optional keywords and flags. A function may be thought of as a black box: you feed it information, ...
Presentation: Computation to Solve Problems
... function box. It consists of the name of a function, perhaps one or more required arguments, and optional keywords and flags. A function may be thought of as a black box: you feed it information, ...
... function box. It consists of the name of a function, perhaps one or more required arguments, and optional keywords and flags. A function may be thought of as a black box: you feed it information, ...
Exact discovery of length-range motifs
... larger or lower lengths and the best that could be done is NMK+. This puts a limitation on the types of distance functions that can be used. For example, Mueen et al. normalized all subsequences by subtracting the mean and dividing by the standard deviation prior to distance calculation [12]. This c ...
... larger or lower lengths and the best that could be done is NMK+. This puts a limitation on the types of distance functions that can be used. For example, Mueen et al. normalized all subsequences by subtracting the mean and dividing by the standard deviation prior to distance calculation [12]. This c ...
BLAST Exercise: Detecting and Interpreting Genetic Homology
... The Basic Local Alignment Search Tool (BLAST) is a program that reports regions of local similarity (at either the nucleotide or protein level) between a query sequence and sequences within a database. The ability to detect sequence homology allows us to determine if a gene or a protein is related t ...
... The Basic Local Alignment Search Tool (BLAST) is a program that reports regions of local similarity (at either the nucleotide or protein level) between a query sequence and sequences within a database. The ability to detect sequence homology allows us to determine if a gene or a protein is related t ...
Document
... An edge {i,j} is ambivalent if there is a minimum weight perfect matching that contains it and another that does not If minimum not unique, at least one edge is ambivalent Assign weights to all edges except {i,j} Let aij be the largest weight for which {i,j} participates in some minimum weight perfe ...
... An edge {i,j} is ambivalent if there is a minimum weight perfect matching that contains it and another that does not If minimum not unique, at least one edge is ambivalent Assign weights to all edges except {i,j} Let aij be the largest weight for which {i,j} participates in some minimum weight perfe ...
What is an Evolutionary Algorithm?
... Usually has a fixed size and is a set of genotypes Some sophisticated EAs also assert a spatial structure on the population e.g., a grid. Selection operators usually take whole population into account i.e., parent selection mechanisms are relative to current generation Diversity of a population refe ...
... Usually has a fixed size and is a set of genotypes Some sophisticated EAs also assert a spatial structure on the population e.g., a grid. Selection operators usually take whole population into account i.e., parent selection mechanisms are relative to current generation Diversity of a population refe ...
pdf
... freedom to the learner makes it much harder to prove lower bounds in this model. Concretely, it is not clear how to use standard reductions from NP hard problems in order to establish lower bounds for improper learning (moreover, Applebaum et al. [2008] give evidence that such simple reductions do n ...
... freedom to the learner makes it much harder to prove lower bounds in this model. Concretely, it is not clear how to use standard reductions from NP hard problems in order to establish lower bounds for improper learning (moreover, Applebaum et al. [2008] give evidence that such simple reductions do n ...
More data speeds up training time in learning halfspaces over sparse vectors,
... freedom to the learner makes it much harder to prove lower bounds in this model. Concretely, it is not clear how to use standard reductions from NP hard problems in order to establish lower bounds for improper learning (moreover, Applebaum et al. [2008] give evidence that such simple reductions do n ...
... freedom to the learner makes it much harder to prove lower bounds in this model. Concretely, it is not clear how to use standard reductions from NP hard problems in order to establish lower bounds for improper learning (moreover, Applebaum et al. [2008] give evidence that such simple reductions do n ...
Basic sequence analyses and submission
... Repeat the same process with the M13_R sequence. The other sequences (F1, F2, F3, R1 and R2) do not have vector because the primers were designed within the cloned segment. 5. Use BLAST 2 sequences to Align M13_F with F1 http://www.ncbi.nlm.nih.gov/blast/bl2seq/wblast2.cgi (create a bookmark for thi ...
... Repeat the same process with the M13_R sequence. The other sequences (F1, F2, F3, R1 and R2) do not have vector because the primers were designed within the cloned segment. 5. Use BLAST 2 sequences to Align M13_F with F1 http://www.ncbi.nlm.nih.gov/blast/bl2seq/wblast2.cgi (create a bookmark for thi ...
How to index Dynamic Time Warping?
... - index sequence when warping path is constrained (Boundary conditions, Continuity, Monotonicity, Global constraint) • The proposed approach is state of the art in terms of efficiency and flexibility. It may benefit the matching of 2 and 3 dimensional ...
... - index sequence when warping path is constrained (Boundary conditions, Continuity, Monotonicity, Global constraint) • The proposed approach is state of the art in terms of efficiency and flexibility. It may benefit the matching of 2 and 3 dimensional ...
Lower Bounds for the Relative Greedy Algorithm for Approximating
... The second lower bound is obtained by constructing an instance G k,l which places the instance Gk into a grid. The instance Gk,l consists of an 4k × l grid of terminals where the last terminals of each column have been identified as one terminal. For each column of terminals the graph Gk − Tb − Tc i ...
... The second lower bound is obtained by constructing an instance G k,l which places the instance Gk into a grid. The instance Gk,l consists of an 4k × l grid of terminals where the last terminals of each column have been identified as one terminal. For each column of terminals the graph Gk − Tb − Tc i ...