Lecture 9 - MyCourses
... The Private Exponent ◮ If we can compute the private exponent then we can factor n with at least probability 1/2. Repeating m times gives success probability 1 − (1/2)m . ◮ Las Vegas algorithm is a randomized algorithm which may fail to give an answer, but if it gives an answer, the answer is corre ...
... The Private Exponent ◮ If we can compute the private exponent then we can factor n with at least probability 1/2. Repeating m times gives success probability 1 − (1/2)m . ◮ Las Vegas algorithm is a randomized algorithm which may fail to give an answer, but if it gives an answer, the answer is corre ...
Data-Oblivious Data Structures
... overhead Θ(1) (and no extra space), by keeping the front of the queue at one head and the back of the queue at the other. A two-headed Turing machine tape can be implemented by a constant number of (non-oblivious) single-headed Turing machine tapes, also with linear space and only a constant factor ...
... overhead Θ(1) (and no extra space), by keeping the front of the queue at one head and the back of the queue at the other. A two-headed Turing machine tape can be implemented by a constant number of (non-oblivious) single-headed Turing machine tapes, also with linear space and only a constant factor ...
and two-dimensional arrays
... into the array before any information can be retrieved from it • These initial values can be assigned to the elements of the array as constants, or they can be read into the array from a file Simple Program Design, Fourth Edition Chapter 7 ...
... into the array before any information can be retrieved from it • These initial values can be assigned to the elements of the array as constants, or they can be read into the array from a file Simple Program Design, Fourth Edition Chapter 7 ...
21-762
... basis functions exactly, but not too much more. For example, for our piecewise linear basis functions, the 2-point Gaussian rule will do. It is important to note that the values of the basis functions at quadrature points can be precomputed and stored. ...
... basis functions exactly, but not too much more. For example, for our piecewise linear basis functions, the 2-point Gaussian rule will do. It is important to note that the values of the basis functions at quadrature points can be precomputed and stored. ...
here
... • Modularity: support heterogeneous agents. For instance, agents equipped with different types of sensors, which are either ground based or airborne should be able to interoperate in a single team. • Performance guarantees: provide a lower bound on the quality of the achieved situational awareness. ...
... • Modularity: support heterogeneous agents. For instance, agents equipped with different types of sensors, which are either ground based or airborne should be able to interoperate in a single team. • Performance guarantees: provide a lower bound on the quality of the achieved situational awareness. ...
Combinatorial Rectangles in Communication Complexity
... which are derived from the same variable. Q UESTION : Is there a truth assignment for U that satisfies all the clauses in C? MEiB, maximum edge independent biclique I NSTANCE : h(V1 ∪ V2 , E), ki where (V1 ∪ V2 , E) is a bipartite graph and k is a positive integer. Q UESTION : Does G contain an i-bi ...
... which are derived from the same variable. Q UESTION : Is there a truth assignment for U that satisfies all the clauses in C? MEiB, maximum edge independent biclique I NSTANCE : h(V1 ∪ V2 , E), ki where (V1 ∪ V2 , E) is a bipartite graph and k is a positive integer. Q UESTION : Does G contain an i-bi ...
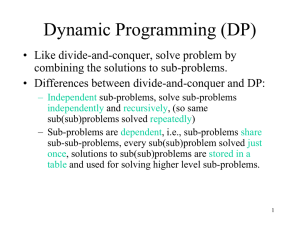
Dynamic Programming
... This divide-and-conquer recursive algorithm solves the overlapping problems over and over. In contrast, DP solves the same (overlapping) subproblems only once (at the first time), then store the result in a table, when the same subproblem is encountered later, just look up the table to get the resul ...
... This divide-and-conquer recursive algorithm solves the overlapping problems over and over. In contrast, DP solves the same (overlapping) subproblems only once (at the first time), then store the result in a table, when the same subproblem is encountered later, just look up the table to get the resul ...
A+B
... • Intractable: The situation is much worse for problems that cannot be solved using an algorithm with worst-case polynomial time complexity. The problems are called intractable. • NP problem. • NP-complete problem. • Unsolvable problem: no algorithm to solve them. ...
... • Intractable: The situation is much worse for problems that cannot be solved using an algorithm with worst-case polynomial time complexity. The problems are called intractable. • NP problem. • NP-complete problem. • Unsolvable problem: no algorithm to solve them. ...
Introduction to Computer Science
... An informal definition No generally accepted formal definition of algorithm exists yet. As the term is popularly understood, algorithm mean the way of doing sth, recipe for sth or formula for sth. More formal definition In mathematic and computer science, algorithm mean finite, ordered sequence of c ...
... An informal definition No generally accepted formal definition of algorithm exists yet. As the term is popularly understood, algorithm mean the way of doing sth, recipe for sth or formula for sth. More formal definition In mathematic and computer science, algorithm mean finite, ordered sequence of c ...
Time-Memory Trade-Off for Lattice Enumeration in a Ball
... has been improved by Ajtai et al. in [6] to 2O(n log log n/ log n) in polynomial-time. The LLL and BKZ algorithms use a lattice reduction technique that applies successive elementary transformations to the input basis in order to make them shorter and more orthogonal. In 2001, Ajtai, Kumar and Sivak ...
... has been improved by Ajtai et al. in [6] to 2O(n log log n/ log n) in polynomial-time. The LLL and BKZ algorithms use a lattice reduction technique that applies successive elementary transformations to the input basis in order to make them shorter and more orthogonal. In 2001, Ajtai, Kumar and Sivak ...
An easy treatment of hanging nodes in hp-finite elements
... An alternative approach for the treatment of hanging nodes and edges is the multi-level hp enrichment presented in [13]. The approach is based on the idea of hp-d-refinement: A high-order base mesh is superposed with a finer h-overlay mesh in the domain of interest (see [14]) rather than replaced b ...
... An alternative approach for the treatment of hanging nodes and edges is the multi-level hp enrichment presented in [13]. The approach is based on the idea of hp-d-refinement: A high-order base mesh is superposed with a finer h-overlay mesh in the domain of interest (see [14]) rather than replaced b ...
Optimal Resource Allocation for MIMO Ad Hoc Cognitive Radio
... sum-rate maximization problem should be handled using the approach in [23] when the individual link rates are not equally ...
... sum-rate maximization problem should be handled using the approach in [23] when the individual link rates are not equally ...
Slide 1
... Lets consider the general case of n disks To move n disks from A to C using B as auxiliary 1.If n==1, move single disk from A to C. 2.Move the top n-1 disks from A to B using C as auxiliary. 3.Move the remaining disk from A to C. 4.Move the n-1 disks from B to C, using A as auxiliary. • Here if n== ...
... Lets consider the general case of n disks To move n disks from A to C using B as auxiliary 1.If n==1, move single disk from A to C. 2.Move the top n-1 disks from A to B using C as auxiliary. 3.Move the remaining disk from A to C. 4.Move the n-1 disks from B to C, using A as auxiliary. • Here if n== ...
Thomas L. Magnanti and Georgia Perakis
... VI(f, K) problem, extending results from linear and nonlinear programming. 2. Using these notions, we show how to find a "near optimal" solution of the VI(f, K) problem in a polynomial number of iterations. ...
... VI(f, K) problem, extending results from linear and nonlinear programming. 2. Using these notions, we show how to find a "near optimal" solution of the VI(f, K) problem in a polynomial number of iterations. ...
V. Clustering
... The general clustering problem Clustering algorithm Clustering of textual data ...
... The general clustering problem Clustering algorithm Clustering of textual data ...
Computing intersections in a set of line segments: the Bentley
... Our task is to compute all pairs (Li , Lj ), i 6= j, of segments that intersect. ¡n¢ A trivial solution to this problem considers all 2 pairs (Li , Lj ), i 6= j, and checks for each such pair if the two segments intersect. Clearly, this algorithm has a running time of O(n2 ). This is worst-case opti ...
... Our task is to compute all pairs (Li , Lj ), i 6= j, of segments that intersect. ¡n¢ A trivial solution to this problem considers all 2 pairs (Li , Lj ), i 6= j, and checks for each such pair if the two segments intersect. Clearly, this algorithm has a running time of O(n2 ). This is worst-case opti ...
Document
... Siepel A. Exact algorithms for the reversal median problem. Master Thesis, University of New Mexico, 2001. Yancopoulos S., Attie O., Friedberg R. Efficient sorting of genomic permutations by translocation, inversion and block exchange. Bioinformatics ...
... Siepel A. Exact algorithms for the reversal median problem. Master Thesis, University of New Mexico, 2001. Yancopoulos S., Attie O., Friedberg R. Efficient sorting of genomic permutations by translocation, inversion and block exchange. Bioinformatics ...
Spaces determined by selections
... 2. Topological properties of τψ Topologies generated by weak selections were studied in [4]. In particular, the following result holds: Proposition 2.1. ([4]) Let ψ be a weak selection defined on X . Then ( X , τψ ) is a regular space. In the same paper, the authors ask if ( X , τψ ) is always normal ...
... 2. Topological properties of τψ Topologies generated by weak selections were studied in [4]. In particular, the following result holds: Proposition 2.1. ([4]) Let ψ be a weak selection defined on X . Then ( X , τψ ) is a regular space. In the same paper, the authors ask if ( X , τψ ) is always normal ...
figure 6-2 - JSNE Group
... Largest Element in an Array (cont’d.) • maximum(list[0], largest(list[1]...list[5])) • maximum(list[1], largest(list[2]...list[5]), etc. • Every time previous formula used to find largest element in a sublist – Length of sublist in next call reduced by one ...
... Largest Element in an Array (cont’d.) • maximum(list[0], largest(list[1]...list[5])) • maximum(list[1], largest(list[2]...list[5]), etc. • Every time previous formula used to find largest element in a sublist – Length of sublist in next call reduced by one ...
Pointers to Functions - CS
... program supplied with this class Run them in DDD (or gdb) set breakpoints step through program force an assert, and see what happens ...
... program supplied with this class Run them in DDD (or gdb) set breakpoints step through program force an assert, and see what happens ...
maxmin
... Two kinds of "suspicious" points (for local max or min): f′(c) = 0 f′(c) does not exists ...
... Two kinds of "suspicious" points (for local max or min): f′(c) = 0 f′(c) does not exists ...
Linear Systems
... Approach - The computation is blocked in such a way that the resulting algorithm is rich in matrix multiplication, assuming that q and n are large enough. It is sufficient to consider just the lower triangular case as the derivation of block back substitution is entirely analogous. We start by par ...
... Approach - The computation is blocked in such a way that the resulting algorithm is rich in matrix multiplication, assuming that q and n are large enough. It is sufficient to consider just the lower triangular case as the derivation of block back substitution is entirely analogous. We start by par ...
CSE 142 Python Slides - Building Java Programs
... their behavior as interactions between objects. – abstraction: Separation between concepts and details. Objects provide abstraction in programming. ...
... their behavior as interactions between objects. – abstraction: Separation between concepts and details. Objects provide abstraction in programming. ...
Slides
... What shall we do with the counter? Privacy-preserving counting is a basic building block in more complex environments General characterizations and transformations Event-level pan-private continual-output algorithm for any low sensitivity function ...
... What shall we do with the counter? Privacy-preserving counting is a basic building block in more complex environments General characterizations and transformations Event-level pan-private continual-output algorithm for any low sensitivity function ...
Unsupervised Feature Selection for the k
... Given an n × d matrix A, let Uk ∈ Rn×k (resp. Vk ∈ Rd×k ) be the matrix of the top k left (resp. right) singular vectors of A, and let Σk ∈ Rk×k be a diagonal matrix containing the top k singular values of A. If we let ρ be the rank of A, then Aρ−k is equal to A − Ak , with Ak = Uk Σk VkT . ∥A∥F and ...
... Given an n × d matrix A, let Uk ∈ Rn×k (resp. Vk ∈ Rd×k ) be the matrix of the top k left (resp. right) singular vectors of A, and let Σk ∈ Rk×k be a diagonal matrix containing the top k singular values of A. If we let ρ be the rank of A, then Aρ−k is equal to A − Ak , with Ak = Uk Σk VkT . ∥A∥F and ...