ZONES Presentation
... Virtualization is driven by the need to consolidate multiple hosts and services on a single machine. Virtualization reduces costs through the sharing of hardware, infrastructure, and administration. ...
... Virtualization is driven by the need to consolidate multiple hosts and services on a single machine. Virtualization reduces costs through the sharing of hardware, infrastructure, and administration. ...
The History of Amoeba
... are the least, allowing for an even distribution of work load. This is where the increase in speed comes from in parallelism, giving more CPUs the same job. Now the increase isn’t linear with respect to the number of CPUs given to quickness that a process is completed. The reason for this is because ...
... are the least, allowing for an even distribution of work load. This is where the increase in speed comes from in parallelism, giving more CPUs the same job. Now the increase isn’t linear with respect to the number of CPUs given to quickness that a process is completed. The reason for this is because ...
Lesson 16
... “buffer.” Then, once the CPU is freed up, the OS releases the data to continue its journey through the CPU. ...
... “buffer.” Then, once the CPU is freed up, the OS releases the data to continue its journey through the CPU. ...
An Introduction to NIST Special Publication 800
... In summary, CUI can describe any information that is not in the classified category. Its use was originally intended for federal agencies to manage their own complex world of nonclassified information. However, as federal agencies look to vendors and service providers for cost-effective support, th ...
... In summary, CUI can describe any information that is not in the classified category. Its use was originally intended for federal agencies to manage their own complex world of nonclassified information. However, as federal agencies look to vendors and service providers for cost-effective support, th ...
INF5070 – Media Storage and Distribution Systems
... high priorities for time-restrictive multimedia tasks timer support – clock with fine granularity and event scheduling with high accuracy kernel preemption – avoid long periods where low priority processes cannot be interrupted memory replacement – prevent code for real-time programs from bein ...
... high priorities for time-restrictive multimedia tasks timer support – clock with fine granularity and event scheduling with high accuracy kernel preemption – avoid long periods where low priority processes cannot be interrupted memory replacement – prevent code for real-time programs from bein ...
3_firewall_m
... NFS and RPC), which were previously immune to management by static filtering and were not uniquely identified by dynamic filtering • Application state allows a previously authenticated user to create new connections without reauthorizing, whereas connection state just maintains that authorization fo ...
... NFS and RPC), which were previously immune to management by static filtering and were not uniquely identified by dynamic filtering • Application state allows a previously authenticated user to create new connections without reauthorizing, whereas connection state just maintains that authorization fo ...
Denali: Lightweight Virtual Machines
... the VM cannot access; because of this, we can avoid physical TLB flushes on VM/VMM crossings. By default, a VM cannot virtualize its own (virtualized) physical address space: in other words, by default, there is no virtual MMU. In this configuration, a VM’s OS shares its address space with applicati ...
... the VM cannot access; because of this, we can avoid physical TLB flushes on VM/VMM crossings. By default, a VM cannot virtualize its own (virtualized) physical address space: in other words, by default, there is no virtual MMU. In this configuration, a VM’s OS shares its address space with applicati ...
Virtualization in Software Engineering
... Basis to Implement Process Duplication, Migration and Checkpoint/Restart in Linux Clusters. Parallel and Distributed Computing, 2005. ISPDC 2005. The 4th International Symposium on 04-06 July 2005. 97-104. [14] Application Virtualization. Retrieved April 2, 2007, from Wikipedia. Web site: ...
... Basis to Implement Process Duplication, Migration and Checkpoint/Restart in Linux Clusters. Parallel and Distributed Computing, 2005. ISPDC 2005. The 4th International Symposium on 04-06 July 2005. 97-104. [14] Application Virtualization. Retrieved April 2, 2007, from Wikipedia. Web site: ...
Information & Communication Technology System Maintenance Government of India
... For (i) & (ii) - One year For (iii) & (iv) - Two years For (v) - Three years after NAC/NTC ...
... For (i) & (ii) - One year For (iii) & (iv) - Two years For (v) - Three years after NAC/NTC ...
faculty.elgin.edu
... • User Account Control (UAC) • Feature implemented in Windows 7 to control malware • Prompts users when software attempts to take administrative control • Windows Defender • A real-time spyware monitor to prevent the installation of and ...
... • User Account Control (UAC) • Feature implemented in Windows 7 to control malware • Prompts users when software attempts to take administrative control • Windows Defender • A real-time spyware monitor to prevent the installation of and ...
ITE PC v4.0 Chapter 1
... Leveraging CDP CDP is a layer 2 Cisco proprietary protocol used to discover other Cisco devices that are directly connected It is designed to allow the devices to auto-configure their connections If an attacker is listening to CDP messages, it could learn important information such as device m ...
... Leveraging CDP CDP is a layer 2 Cisco proprietary protocol used to discover other Cisco devices that are directly connected It is designed to allow the devices to auto-configure their connections If an attacker is listening to CDP messages, it could learn important information such as device m ...
Proceedings of the 5th Symposium on Operating Systems Design and Implementation USENIX Association
... the VM cannot access; because of this, we can avoid physical TLB flushes on VM/VMM crossings. By default, a VM cannot virtualize its own (virtualized) physical address space: in other words, by default, there is no virtual MMU. In this configuration, a VM’s OS shares its address space with applicati ...
... the VM cannot access; because of this, we can avoid physical TLB flushes on VM/VMM crossings. By default, a VM cannot virtualize its own (virtualized) physical address space: in other words, by default, there is no virtual MMU. In this configuration, a VM’s OS shares its address space with applicati ...
Session 21
... • Opinion does not cover system description, although system description is often included in the report. But if reviewer knows that system description is misleading, s/he should not issue an opinion on the controls. • Opinion covers the reporting period of not more than one year. CSE 4482, 2009 ...
... • Opinion does not cover system description, although system description is often included in the report. But if reviewer knows that system description is misleading, s/he should not issue an opinion on the controls. • Opinion covers the reporting period of not more than one year. CSE 4482, 2009 ...
Proceedings of the FREENIX Track: 2003 USENIX Annual Technical Conference
... “footprint” in memory is not really that much larger. As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow Linux to boot another operating system. The result is that LinuxBIOS can load a kernel over any device, network, protocol, and file system that Linux supports– compellin ...
... “footprint” in memory is not really that much larger. As of 1999 there are many systems (kmonte, kexec, bootimg, LOBOS) that allow Linux to boot another operating system. The result is that LinuxBIOS can load a kernel over any device, network, protocol, and file system that Linux supports– compellin ...
ppt - Computer Science Division
... Nachos: Virtual OS Environment • You will be working with Nachos – Simulation environment – Hardware, interrupts, I/O – Execution of User Programs running on this platform ...
... Nachos: Virtual OS Environment • You will be working with Nachos – Simulation environment – Hardware, interrupts, I/O – Execution of User Programs running on this platform ...
kubi-cs162f05lec01
... Nachos: Virtual OS Environment • You will be working with Nachos – Simulation environment – Hardware, interrupts, I/O – Execution of User Programs running on this platform ...
... Nachos: Virtual OS Environment • You will be working with Nachos – Simulation environment – Hardware, interrupts, I/O – Execution of User Programs running on this platform ...
Virtualization: Architectural Considerations And Other
... which virtual machines are managed by a software layer that is installed on bare metal—has gained the greatest market acceptance. This fact has translated into rapid growth and a large and expanding customer base for VMware, which pioneered x86 hypervisors in 2001 with the launch of VMware® ESX Serv ...
... which virtual machines are managed by a software layer that is installed on bare metal—has gained the greatest market acceptance. This fact has translated into rapid growth and a large and expanding customer base for VMware, which pioneered x86 hypervisors in 2001 with the launch of VMware® ESX Serv ...
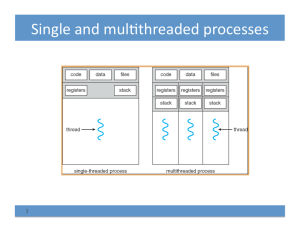
L11-thread-impl
... Other thread design issues • Seman,cs of fork() system calls – Does fork() duplicate only the calling thread or all threads? • Running threads? Threads trapped in system call? – Linux fork() copies on ...
... Other thread design issues • Seman,cs of fork() system calls – Does fork() duplicate only the calling thread or all threads? • Running threads? Threads trapped in system call? – Linux fork() copies on ...
Effective Log Management - National Cyber Security Centre
... The focus of this booklet is to identify appropriate sources of log file data within an organisation in order to facilitate intrusion detection and incident response processes. An increase in the availability and popularity of ‘cloud’ and managed services means that logging for these data sources ma ...
... The focus of this booklet is to identify appropriate sources of log file data within an organisation in order to facilitate intrusion detection and incident response processes. An increase in the availability and popularity of ‘cloud’ and managed services means that logging for these data sources ma ...
Multiuser Systems
... No performance penalty Once linked in, the object code of a module is equivalent to the object code of the statically linked kernel. Therefore, no explicit message passing is required when the functions of the module are invoked. The Process kernel Model A CPU can run in either User Mode or Kernel M ...
... No performance penalty Once linked in, the object code of a module is equivalent to the object code of the statically linked kernel. Therefore, no explicit message passing is required when the functions of the module are invoked. The Process kernel Model A CPU can run in either User Mode or Kernel M ...