Slides for chapter 12
... some of the sectors were written with the new data, and the sector being written during the failure may have been corrupted 3. Total failure - The failure occurred before the disk write started, so the previous data values on the disk remain intact ■ If failure occurs during block write, recovery pr ...
... some of the sectors were written with the new data, and the sector being written during the failure may have been corrupted 3. Total failure - The failure occurred before the disk write started, so the previous data values on the disk remain intact ■ If failure occurs during block write, recovery pr ...
Interrupts and Interrupt Handlers
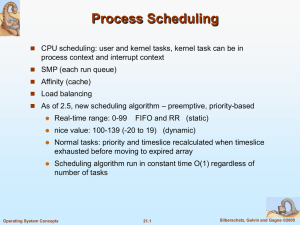
... A process does not have to use all its timeslice at once. A process with 100ms timeslice can run on 5 different reschedules for 20ms each A large time slice benefits interactive tasks: no need for large timeslice at once, remain runnable for as long as possible Timesllice runs out -> expired - ...
... A process does not have to use all its timeslice at once. A process with 100ms timeslice can run on 5 different reschedules for 20ms each A large time slice benefits interactive tasks: no need for large timeslice at once, remain runnable for as long as possible Timesllice runs out -> expired - ...
Towards a Flexible, Lightweight Virtualization Alternative,
... and that boundaries in between the extremes may combine several good properties of both. We propose abstractions to make up one such new virtualization boundary, which combines hardware-level flexibility with OS-level resource sharing. We implement and evaluate a first prototype. ...
... and that boundaries in between the extremes may combine several good properties of both. We propose abstractions to make up one such new virtualization boundary, which combines hardware-level flexibility with OS-level resource sharing. We implement and evaluate a first prototype. ...
Tessellation Space-T..
... Partitions can be virtualized and multiplexed on physical hardware by a global partition manager. Partition resources must be gang scheduled to provide application runtimes with full knowledge and control over their resources to enable them to implement optimized scheduling and resource allocation ...
... Partitions can be virtualized and multiplexed on physical hardware by a global partition manager. Partition resources must be gang scheduled to provide application runtimes with full knowledge and control over their resources to enable them to implement optimized scheduling and resource allocation ...
operating system design
... Each of the abstractions can be instantiated in the form of concrete data structures. Users can create processes, files, semaphores, etc. The primitive operations manipulate these data structures. For example, users can read and write files. The primitive operations are implemented in the form of sy ...
... Each of the abstractions can be instantiated in the form of concrete data structures. Users can create processes, files, semaphores, etc. The primitive operations manipulate these data structures. For example, users can read and write files. The primitive operations are implemented in the form of sy ...
Infoblox DHCP Fingerprinting Enabling Endpoint Discovery and
... The value of DHCP Fingerprinting is fully realized when implemented as part of Infoblox’s robust DNS, DNSSEC, DHCP and IPAM solution. When run on the Infoblox Grid with Infoblox purpose-built appliances that share a common, real-time distributed database, it guarantees that all appliances in the Gri ...
... The value of DHCP Fingerprinting is fully realized when implemented as part of Infoblox’s robust DNS, DNSSEC, DHCP and IPAM solution. When run on the Infoblox Grid with Infoblox purpose-built appliances that share a common, real-time distributed database, it guarantees that all appliances in the Gri ...
z/Auditing Essentials
... security since 1972 when I formed the SHARE Security Project and we developed the security requirements for future IBM Operating Systems. And, when I was not satisfied with the IBM response to those requirements (RACF), I developed ACF2 to prove that the requirements could be accomplished. RACF and ...
... security since 1972 when I formed the SHARE Security Project and we developed the security requirements for future IBM Operating Systems. And, when I was not satisfied with the IBM response to those requirements (RACF), I developed ACF2 to prove that the requirements could be accomplished. RACF and ...
Proceedings of the 9th USENIX Security Symposium USENIX Association Denver, Colorado, USA
... has knowledge of 21 di erent versions of Linux. Other methods of determining an operating system are generally coarse-grained because they use application-level methods. An example is the banner message a user receives when he or she uses telnet to connect to a machine. Many systems freely advertise ...
... has knowledge of 21 di erent versions of Linux. Other methods of determining an operating system are generally coarse-grained because they use application-level methods. An example is the banner message a user receives when he or she uses telnet to connect to a machine. Many systems freely advertise ...
Configuring
... Leveraging CDP CDP is a layer 2 Cisco proprietary protocol used to discover other Cisco devices that are directly connected It is designed to allow the devices to auto-configure their connections If an attacker is listening to CDP messages, it could learn important information such as device m ...
... Leveraging CDP CDP is a layer 2 Cisco proprietary protocol used to discover other Cisco devices that are directly connected It is designed to allow the devices to auto-configure their connections If an attacker is listening to CDP messages, it could learn important information such as device m ...
Methods of Attack
... form of spyware used to record information about an Internet user when they visit websites may be useful or desirable many web sites require that cookies be enabled in order to allow the user to connect ...
... form of spyware used to record information about an Internet user when they visit websites may be useful or desirable many web sites require that cookies be enabled in order to allow the user to connect ...
第五章输入输出
... causes an interrupt. The signal is detected by the interrupt controller chip on the parentboard. If no other interrupts are pending, the interrupt controller processes the interrupt immediately. To handle the interrupt, the controller puts a number on the address lines specifying which device wa ...
... causes an interrupt. The signal is detected by the interrupt controller chip on the parentboard. If no other interrupts are pending, the interrupt controller processes the interrupt immediately. To handle the interrupt, the controller puts a number on the address lines specifying which device wa ...
ra-5 vulnerability scanning control
... FedRAMP is revising the RA-5 test case language and submitting the changes for public comment. These changes address two issues. One involves the need to confirm the linkage of the scanning process with other related processes such as configuration management, patch management, and change management ...
... FedRAMP is revising the RA-5 test case language and submitting the changes for public comment. These changes address two issues. One involves the need to confirm the linkage of the scanning process with other related processes such as configuration management, patch management, and change management ...
How to test an IPS
... 2. Attack detection and mitigation: systems must be vulnerable to recent attacks, then OS and application must be completely simulated. Tools like [xen] or its commercial equivalent [vmware] make possible to simulate different systems on one single physical server. 3. Denial of Service: in this last ...
... 2. Attack detection and mitigation: systems must be vulnerable to recent attacks, then OS and application must be completely simulated. Tools like [xen] or its commercial equivalent [vmware] make possible to simulate different systems on one single physical server. 3. Denial of Service: in this last ...
12 things effective Page title appears here
... and client side attacks Fundamentally, your IPS must include comprehensive signature coverage for attacks directed at both servers and clients. All intrusion prevention systems should include application vulnerability protection, buffer overflow protection and protocol anomaly detection for a wide v ...
... and client side attacks Fundamentally, your IPS must include comprehensive signature coverage for attacks directed at both servers and clients. All intrusion prevention systems should include application vulnerability protection, buffer overflow protection and protocol anomaly detection for a wide v ...
Operating Systems - Learn IT With Davo
... Comparison to other interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
... Comparison to other interfaces . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ...
System Call - Programs in Mathematics and Computer Science
... A View of Operating System Services ...
... A View of Operating System Services ...
OS Portal: an economic approach for making an embedded kernel
... example, the VRTX (Mentor, 2000) kernel is not extensible; the Nucleus (Accelerated, 2001) and eCOS (Red, 2001) kernels are only statically extensible, which means that they are allowed to be configured at compile time only. Such extensibility is not enough. Imagine that a user plugs a disk to his em ...
... example, the VRTX (Mentor, 2000) kernel is not extensible; the Nucleus (Accelerated, 2001) and eCOS (Red, 2001) kernels are only statically extensible, which means that they are allowed to be configured at compile time only. Such extensibility is not enough. Imagine that a user plugs a disk to his em ...
Computer Organisation Operating Systems
... 1-2 second to interact with the system. The idle system can be utilised by other user. • The OS is more complicate because a job may be swapped in and out of memory to disk. ...
... 1-2 second to interact with the system. The idle system can be utilised by other user. • The OS is more complicate because a job may be swapped in and out of memory to disk. ...
Real-time operating system survey
... For small or static real-time systems, data and task dependencies are limited and therefore the task execution time can be estimated prior to execution and the resulting task schedules can be determined off-line. Periodic tasks typically arise from sensor data and control loops, however sporadic tas ...
... For small or static real-time systems, data and task dependencies are limited and therefore the task execution time can be estimated prior to execution and the resulting task schedules can be determined off-line. Periodic tasks typically arise from sensor data and control loops, however sporadic tas ...
Lecture 15
... The OS needs mechanisms to coordinate shared data. Problem 2: Kernel preemption: Suppose the kernel is preempted while updating data (e.g. I/O queues) used by other kernel functions. This could lead to chaos. UNIX solution: Wait for the system call to complete or have an I/O block take place ...
... The OS needs mechanisms to coordinate shared data. Problem 2: Kernel preemption: Suppose the kernel is preempted while updating data (e.g. I/O queues) used by other kernel functions. This could lead to chaos. UNIX solution: Wait for the system call to complete or have an I/O block take place ...
Protecting the FPGA Design From Common Threats
... This zeroization capability provides the designer with the ability to trigger corrective action in the case a tamper event is detected. The zeroization can be triggered by any design input, giving the user maximum flexibility to control the tamper response of the system, and making it difficult to d ...
... This zeroization capability provides the designer with the ability to trigger corrective action in the case a tamper event is detected. The zeroization can be triggered by any design input, giving the user maximum flexibility to control the tamper response of the system, and making it difficult to d ...
Final presentation
... A firewall is any one of several ways of protecting one network from another untrusted network. in principle, the firewall can be thought of a pair of mechanisms one exists to block traffic, and the other exist to permit traffic. Some firewall place a great emphasis on blocking traffic, while others ...
... A firewall is any one of several ways of protecting one network from another untrusted network. in principle, the firewall can be thought of a pair of mechanisms one exists to block traffic, and the other exist to permit traffic. Some firewall place a great emphasis on blocking traffic, while others ...
Lecture 28
... Methods for Handling Deadlocks Ensure that the system will never enter a deadlock state. Allow the system to enter a deadlock state and then ...
... Methods for Handling Deadlocks Ensure that the system will never enter a deadlock state. Allow the system to enter a deadlock state and then ...