Backup types and strategies
... Incremental backup only copies files that have been created or modified since the last full or incremental backup. These files will be marked as backed up by turning off their archive bit. Incremental backups are used in conjunction with full/normal backups. This allows a large full backup to be don ...
... Incremental backup only copies files that have been created or modified since the last full or incremental backup. These files will be marked as backed up by turning off their archive bit. Incremental backups are used in conjunction with full/normal backups. This allows a large full backup to be don ...
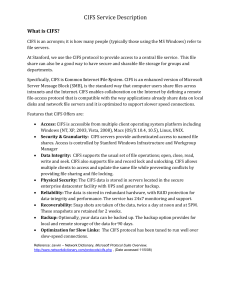
CIFS Service Description
... purpose here is not for maintain confidentiality but separating common documents. 2. The quota is counted against total usage for all the staff in the department, and not individual users. If there is a need for individual quota and confidentiality then the Individual option may be more attractive. ...
... purpose here is not for maintain confidentiality but separating common documents. 2. The quota is counted against total usage for all the staff in the department, and not individual users. If there is a need for individual quota and confidentiality then the Individual option may be more attractive. ...
Optimization Techniques for Processing Large Files in an OpenVMS
... assigned in a LIBNAME statement or an OpenVMS path that must be enclosed in single or double quotes. To prohibit SAS from using a certain sort area, use the following statement prior to sorting. OPTIONS NOSORTWORK ; SAS system is shipped with two command procedures, SORTCHK.COM and SORTSIZE.COM, whi ...
... assigned in a LIBNAME statement or an OpenVMS path that must be enclosed in single or double quotes. To prohibit SAS from using a certain sort area, use the following statement prior to sorting. OPTIONS NOSORTWORK ; SAS system is shipped with two command procedures, SORTCHK.COM and SORTSIZE.COM, whi ...
for COBOL
... can still take advantage of these indexes to retrieve records, while not using them for sorting. This is an architectural limitation, however, in practice does not have significant impact as the SQL engine is able to build temporary index files on the fly when necessary and use dynamic index techniq ...
... can still take advantage of these indexes to retrieve records, while not using them for sorting. This is an architectural limitation, however, in practice does not have significant impact as the SQL engine is able to build temporary index files on the fly when necessary and use dynamic index techniq ...
BizPro Consulting Services
... ODBC is a Microsoft spec that allows users to share information in a relational database across multiple and diverse platforms. Examples: Microsoft SQL Server, MS Access, QuickBooks, Crystal Reports, MS Visual Basic, DB2 for PCs The application must be ODBC-compliant QODBC is included with QuickBook ...
... ODBC is a Microsoft spec that allows users to share information in a relational database across multiple and diverse platforms. Examples: Microsoft SQL Server, MS Access, QuickBooks, Crystal Reports, MS Visual Basic, DB2 for PCs The application must be ODBC-compliant QODBC is included with QuickBook ...
PPT Version of Presentation Slides
... Virtual machine files • VM images & associated XML files on WS3 • Virtual hard disk files on NC User data files • User persistent data volumes on EBS • Snapshots of volumes on WS3 ...
... Virtual machine files • VM images & associated XML files on WS3 • Virtual hard disk files on NC User data files • User persistent data volumes on EBS • Snapshots of volumes on WS3 ...
Enhanced secured Hybrid ClouDedupe system for Data deduplication
... 13] is to split a task, keeping the computation on the private data within an organization’s private cloud while moving the rest to the public commercial cloud [Fig 5].Basically, the deployment of a cloud is managed in-house (Private Cloud) or over a third-party location (Public Cloud). While, for v ...
... 13] is to split a task, keeping the computation on the private data within an organization’s private cloud while moving the rest to the public commercial cloud [Fig 5].Basically, the deployment of a cloud is managed in-house (Private Cloud) or over a third-party location (Public Cloud). While, for v ...
A Unified Object Oriented Storage Architecture
... best implemented by scrapping the existing infrastructure of file systems and devices drivers. While this may be considered blasphemy within the data storage industry, not doing it has the effect of locking us into storage architectures of the 1980s. Modern storage devices have microprocessor based ...
... best implemented by scrapping the existing infrastructure of file systems and devices drivers. While this may be considered blasphemy within the data storage industry, not doing it has the effect of locking us into storage architectures of the 1980s. Modern storage devices have microprocessor based ...
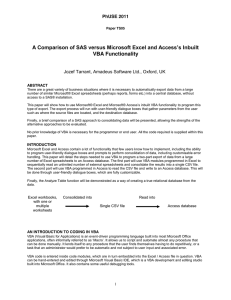
A Comparison of SAS® Versus Microsoft® Excel and Access's Inbuilt VBA Functionality
... The text field in the form, labeled Text1 by default, supplies the filename and filepath of the CSV file to import. The user can type this in manually, but to avoid error and give greater usability, we can let users browse to a file. This functionality is supplied by the code module below, which nee ...
... The text field in the form, labeled Text1 by default, supplies the filename and filepath of the CSV file to import. The user can type this in manually, but to avoid error and give greater usability, we can let users browse to a file. This functionality is supplied by the code module below, which nee ...
Distributed Applications The NetBeans IDE
... We always work in projects (NetBeans will create a project) A Project uses a project directory (use suffix .nbp (netbeans project) i.e. myproj.nbp) ...
... We always work in projects (NetBeans will create a project) A Project uses a project directory (use suffix .nbp (netbeans project) i.e. myproj.nbp) ...
Run Magic apps with Oracle, MS SQL, MySQL and PostgreSQL
... Another consideration for Magicians is creating and deleting tables on the fly during program execution. Magicians know that when they want a table it will be in the database and when they want to delete a table it will be removed. The Magic runtime handles table creation through the Btrieve Engine, ...
... Another consideration for Magicians is creating and deleting tables on the fly during program execution. Magicians know that when they want a table it will be in the database and when they want to delete a table it will be removed. The Magic runtime handles table creation through the Btrieve Engine, ...
Introduction to Unix
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
LINUX
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
... For example, an OS ensures safe access to a printer by allowing only one application program to send data directly to the printer at any one time. An OS encourages efficient use of the CPU by suspending programs that are waiting for I/O operations to complete to make way for programs that can use th ...
Have a Backup - cybersec 101
... be backed up, add them to one of these folders. ₀₀ To set up a drive for File History: • If you are going to use a new external drive, connect it to your PC. • If you see a notification asking if you want to configure the drive for File History, tap or click it, and then turn on File History on th ...
... be backed up, add them to one of these folders. ₀₀ To set up a drive for File History: • If you are going to use a new external drive, connect it to your PC. • If you see a notification asking if you want to configure the drive for File History, tap or click it, and then turn on File History on th ...
PowerPoint **
... digital binary format. • Control information indicates how data should be processed. • Applications may embed control information in user data for formatting or presentation. • Data and its associated control information is organized into discrete units as files or records. ...
... digital binary format. • Control information indicates how data should be processed. • Applications may embed control information in user data for formatting or presentation. • Data and its associated control information is organized into discrete units as files or records. ...
UI Resources
... • Defines how the UI elements in a screen is arranged. • They are XML files located in the res\layout folder. • A layout file may be associated with one or more Activities. • YOU may recall the setContentView(R.layout.activity_main) method that associates an Activity with a layout file(activity_main ...
... • Defines how the UI elements in a screen is arranged. • They are XML files located in the res\layout folder. • A layout file may be associated with one or more Activities. • YOU may recall the setContentView(R.layout.activity_main) method that associates an Activity with a layout file(activity_main ...
Lecture 1: Introduction
... Differential Backup Backs up all files that have been changed since the last full backup Incremental Backup Backs up all files that have been changed from the most recent backup (either a full or previous incremental) Delta Backup Similar to an incremental backup, but backs up only the actual ...
... Differential Backup Backs up all files that have been changed since the last full backup Incremental Backup Backs up all files that have been changed from the most recent backup (either a full or previous incremental) Delta Backup Similar to an incremental backup, but backs up only the actual ...
Chapter 21 PowerPoint
... – Users open an access channel to a device in the same way they open any other file. – Devices are protected by the same permission system as files. • Linux recognizes three classes of devices: – Block devices: allow random access to independent, fixed-size blocks of data (e.g. disks, CD-ROMs, flash ...
... – Users open an access channel to a device in the same way they open any other file. – Devices are protected by the same permission system as files. • Linux recognizes three classes of devices: – Block devices: allow random access to independent, fixed-size blocks of data (e.g. disks, CD-ROMs, flash ...
SC PE
... Files • Files are the common containers for user data, application code, and operating system executables and parameters. • A file includes data and control information – Data is information that has been converted to a machine-readable, digital binary format. – Control information indicates how da ...
... Files • Files are the common containers for user data, application code, and operating system executables and parameters. • A file includes data and control information – Data is information that has been converted to a machine-readable, digital binary format. – Control information indicates how da ...
The following paper was originally published in the
... There are several logical models for NT domain architecture, the most feasible for large organizations are the Master or Multiple-Master domain models. Since NT only provides a two dimensional namespace, security and organizational relationships must be built into the domain architecture. NT provide ...
... There are several logical models for NT domain architecture, the most feasible for large organizations are the Master or Multiple-Master domain models. Since NT only provides a two dimensional namespace, security and organizational relationships must be built into the domain architecture. NT provide ...
AdvancedUNIXDec16
... This illustrates that you can use pipe to join up unix/linux command. Many commands can be used with pipes. Also, you can redirect output from the screen to an output file. Try for example, cat file.ex1 | grep 3 | grep 6 > out.file4 ...
... This illustrates that you can use pipe to join up unix/linux command. Many commands can be used with pipes. Also, you can redirect output from the screen to an output file. Try for example, cat file.ex1 | grep 3 | grep 6 > out.file4 ...
Fundamentals of Database Systems
... Elmasri/Navathe, Fundamentals of Database Systems, Fourth Edition Copyright © 2004 Ramez Elmasri and Shamkant Navathe ...
... Elmasri/Navathe, Fundamentals of Database Systems, Fourth Edition Copyright © 2004 Ramez Elmasri and Shamkant Navathe ...
Quick UNIX Tutorial
... r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you ...
... r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the directory. This implies that you ...
Linux Tutorial
... Access rights on directories. r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the d ...
... Access rights on directories. r: allows users to list files in the directory; w: means that users may delete files from the directory or move files into it. Never give write permission to others to your home directory or any of its subdirectories. x: means the right to access files in the d ...
Computer file

A computer file is a resource for storing information, which is available to a computer program and is usually based on some kind of durable storage. A file is ""durable"" in the sense that it remains available for other programs to use after the program that created it has finished executing. Computer files can be considered as the modern counterpart of paper documents which traditionally are kept in office and library files, and this is the source of the term.