Improved Bounds for Orthogonal Point Enclosure Query and Point
... Table 1: Summary of our results for orthogonal point enclosure in R3 . log∗ n is the iterated logarithm of n. log(1) n = log n and log(i) n = log(log(i−1) n) when i > 1 is a constant integer. Existing solutions in the literature for 6-sided rectangles require Ω(n log n) space. comparison of our resu ...
... Table 1: Summary of our results for orthogonal point enclosure in R3 . log∗ n is the iterated logarithm of n. log(1) n = log n and log(i) n = log(log(i−1) n) when i > 1 is a constant integer. Existing solutions in the literature for 6-sided rectangles require Ω(n log n) space. comparison of our resu ...
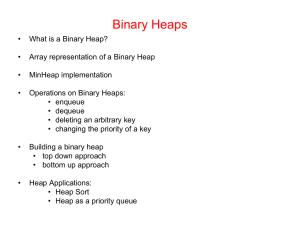
Priority Queues 1. Priority Queues 2. PQueue Specification
... • dequeue: In this case, we must also delete the root node from the tree and then restore the heap property. This can be achieved by moving the final entry in the tree to the newly-vacated root position and then calling heapify(1) to restore the heap property. This involves a few constant time opera ...
... • dequeue: In this case, we must also delete the root node from the tree and then restore the heap property. This can be achieved by moving the final entry in the tree to the newly-vacated root position and then calling heapify(1) to restore the heap property. This involves a few constant time opera ...
Multidimensional Access Methods
... multidimensional access methods to denote the large class of access methods that support searches in spatial databases and are the subject of this survey. Within this class, we distinguish between point access methods (PAMs) and spatial access methods (SAMs). Point access methods have primarily been ...
... multidimensional access methods to denote the large class of access methods that support searches in spatial databases and are the subject of this survey. Within this class, we distinguish between point access methods (PAMs) and spatial access methods (SAMs). Point access methods have primarily been ...
Linked Data Structures Linked lists
... • the root node has no parent, all others have exactly one • nodes can have multiple children • in a binary tree, each node has at most two children • a leaf node has no children • the height of a tree is the maximum possible number of nodes from the root to a leaf (inclusive) ...
... • the root node has no parent, all others have exactly one • nodes can have multiple children • in a binary tree, each node has at most two children • a leaf node has no children • the height of a tree is the maximum possible number of nodes from the root to a leaf (inclusive) ...
A Framework for Dynamizing Succinct Data Structures
... answer queries efficiently, perform updates in a reasonable amount of time, and still maintain a compressed version of the dynamically-changing data. In that vein, there have been some results on dynamic succinct bitvectors (dictionaries) [14, 8, 12]. However, these data structures either perform qu ...
... answer queries efficiently, perform updates in a reasonable amount of time, and still maintain a compressed version of the dynamically-changing data. In that vein, there have been some results on dynamic succinct bitvectors (dictionaries) [14, 8, 12]. However, these data structures either perform qu ...
Data Structures and Algorithms. Lab Guide
... data types. An abstract data type is a programming language facility for organizing programs into modules using criteria that are based on the data structures of the program. Also, an abstract data type can be defines as a set of values and a set of procedures that manipulate those values. The speci ...
... data types. An abstract data type is a programming language facility for organizing programs into modules using criteria that are based on the data structures of the program. Also, an abstract data type can be defines as a set of values and a set of procedures that manipulate those values. The speci ...
ADS@Unit-3[Priority Queues]
... ADS@Unit-3[Priority Queues] Delete Operation in Binomial tree: Step 1:First find the binomial tree with small root in the priority queue. Step 2:Let Bk be the binomial tree of binomial queue in priority queue remove Bk from H and forming another binomial queue H`. Step 3:Now remove the root of Bk , ...
... ADS@Unit-3[Priority Queues] Delete Operation in Binomial tree: Step 1:First find the binomial tree with small root in the priority queue. Step 2:Let Bk be the binomial tree of binomial queue in priority queue remove Bk from H and forming another binomial queue H`. Step 3:Now remove the root of Bk , ...
Data Structures and Analysis - Department of Computer Science
... while the computation in the if branch takes Ω(n2 ) time. This means that the worst-case running time of this algorithm is Ω(n2 ). It is not too hard to prove the matching upper bound, and so the worst-case running time is Θ(n2 ). However, the loop only executes when every number in lst is even; whe ...
... while the computation in the if branch takes Ω(n2 ) time. This means that the worst-case running time of this algorithm is Ω(n2 ). It is not too hard to prove the matching upper bound, and so the worst-case running time is Θ(n2 ). However, the loop only executes when every number in lst is even; whe ...
Self-Organizing Data Structures
... structures can be phrased as follows. The elements of a set are stored in a collection of nodes. Each node also contains O(1) pointers to other nodes and additional state data which can be used for navigation and self-organization. The elements have associated key values, which may or may not be tot ...
... structures can be phrased as follows. The elements of a set are stored in a collection of nodes. Each node also contains O(1) pointers to other nodes and additional state data which can be used for navigation and self-organization. The elements have associated key values, which may or may not be tot ...
ch13hashing
... – Guarantees O(log n) time for insert, retrieve, remove, and search – Large collection of methods ...
... – Guarantees O(log n) time for insert, retrieve, remove, and search – Large collection of methods ...
Evaluation Techniques for Generalized Path Pattern Queries on
... every node in the XML tree is encoded [15,39,4,9,23]. Further, the nodes are partitioned, and an index of inverted lists called streams is built on this partition. In order to evaluate a query, the nodes of the relevant streams are read in the preorder of their appearance in the XML tree. Every node ...
... every node in the XML tree is encoded [15,39,4,9,23]. Further, the nodes are partitioned, and an index of inverted lists called streams is built on this partition. In order to evaluate a query, the nodes of the relevant streams are read in the preorder of their appearance in the XML tree. Every node ...










![ADS@Unit-3[Priority Queues]](http://s1.studyres.com/store/data/001436107_1-e08a2e00715b31b0a0c8bb0589fdbb6e-300x300.png)