Chapter 1
... WAN Data Link Layer Concepts • FYI: • Another Data Link layer protocol is the Multiprotocol Label Switching (MPLS) protocol. • MPLS is increasingly being deployed by service providers to provide an economical solution to carry circuit-switched as well as packet-switched network traffic. • It can op ...
... WAN Data Link Layer Concepts • FYI: • Another Data Link layer protocol is the Multiprotocol Label Switching (MPLS) protocol. • MPLS is increasingly being deployed by service providers to provide an economical solution to carry circuit-switched as well as packet-switched network traffic. • It can op ...
CAN Communication Protocol - University of Wisconsin
... error and the sending node retransmits the same good frame continually as the malfunctioning node continues to report an error. Both of these situations could result in a hold up on the bus of normal messaging and thus need to be rectified. CAN detects and fixes these errors by implementing two coun ...
... error and the sending node retransmits the same good frame continually as the malfunctioning node continues to report an error. Both of these situations could result in a hold up on the bus of normal messaging and thus need to be rectified. CAN detects and fixes these errors by implementing two coun ...
Business Data Communications 4e
... • Advantage of differential encoding is that it is more reliable to detect a change in polarity than it is to accurately detect a specific level Business Data Communications, 5e ...
... • Advantage of differential encoding is that it is more reliable to detect a change in polarity than it is to accurately detect a specific level Business Data Communications, 5e ...
PPT - mrazian.com
... segment, uses CSMA/CD to access segment transparent hosts are unaware of presence of switches plug-and-play, self-learning switches do not need to be configured ...
... segment, uses CSMA/CD to access segment transparent hosts are unaware of presence of switches plug-and-play, self-learning switches do not need to be configured ...
lect22 - Computer and Information Sciences
... Ethernet frame contains A-to-B IP datagram A’s data link layer sends Ethernet frame R’s data link layer receives Ethernet frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s physical layer address R creates frame containing A-to-B IP datagram sends to B ...
... Ethernet frame contains A-to-B IP datagram A’s data link layer sends Ethernet frame R’s data link layer receives Ethernet frame R removes IP datagram from Ethernet frame, sees its destined to B R uses ARP to get B’s physical layer address R creates frame containing A-to-B IP datagram sends to B ...
VPN Networks
... The main benefit of a VPN is the potential for significant cost savings compared to traditional leased lines or dial up networking. These savings come with a certain amount of risk, however, particularly when using the public Internet as the delivery mechanism for VPN data. ...
... The main benefit of a VPN is the potential for significant cost savings compared to traditional leased lines or dial up networking. These savings come with a certain amount of risk, however, particularly when using the public Internet as the delivery mechanism for VPN data. ...
정문영
... Exposes realistic network conditions Gives control over network events Carries traffic on behalf of real users ...
... Exposes realistic network conditions Gives control over network events Carries traffic on behalf of real users ...
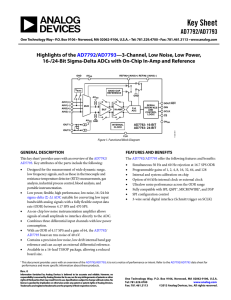
Key Sheet AD7792/AD7793
... When DOUT/RDY goes low to indicate the end of a conversion, sufficient SCLK cycles must be applied to the ADC. The data conversion is then placed on the DOUT/RDY line. When the conversion is read, DOUT/RDY returns high until the next conversion is available. In this mode, the data can be read only o ...
... When DOUT/RDY goes low to indicate the end of a conversion, sufficient SCLK cycles must be applied to the ADC. The data conversion is then placed on the DOUT/RDY line. When the conversion is read, DOUT/RDY returns high until the next conversion is available. In this mode, the data can be read only o ...
Data Communication & Network
... In addition to being represented by an analog signal, information can also be represented by a digital signal. For example, a 1 can be encoded as a positive voltage and a 0 as zero voltage. A digital signal can have more than two levels. In this case, we can send more than 1 bit for each level. ...
... In addition to being represented by an analog signal, information can also be represented by a digital signal. For example, a 1 can be encoded as a positive voltage and a 0 as zero voltage. A digital signal can have more than two levels. In this case, we can send more than 1 bit for each level. ...
TamVu_TCP_lec_DR13 - Winlab
... Network may drop messages. Deliver messages in the same order they are sent Messages may be reordered in networks and incurs a long delay. Delivers at most one copy of each message Messages may duplicate in networks. Support arbitrarily large message Network may limit message size. S ...
... Network may drop messages. Deliver messages in the same order they are sent Messages may be reordered in networks and incurs a long delay. Delivers at most one copy of each message Messages may duplicate in networks. Support arbitrarily large message Network may limit message size. S ...
inse7120-lec8
... Resource sharing to improve efficiency o If a certain management function has been defined by some MS, another MS can share its usage by observing the associated “read-only” data rows (see EntryStatus definition) o However, the MS that owns this control row may modify or delete the row at any time ...
... Resource sharing to improve efficiency o If a certain management function has been defined by some MS, another MS can share its usage by observing the associated “read-only” data rows (see EntryStatus definition) o However, the MS that owns this control row may modify or delete the row at any time ...
lecture5 - Andrew.cmu.edu
... “Switching” also happens at the network layer. » Layer 3: Internet protocol » In this case, address is an IP address » IP over SONET, IP over ATM, ... » Otherwise, operation is very similar Switching is different from SONET mux/demux. ...
... “Switching” also happens at the network layer. » Layer 3: Internet protocol » In this case, address is an IP address » IP over SONET, IP over ATM, ... » Otherwise, operation is very similar Switching is different from SONET mux/demux. ...
Lecture 1
... Data communication is the transfer of data from one device to another via some form of transmission medium. A data communications system must transmit data to the correct destination in an accurate and timely manner. The five components that make up a data communications system are the message, send ...
... Data communication is the transfer of data from one device to another via some form of transmission medium. A data communications system must transmit data to the correct destination in an accurate and timely manner. The five components that make up a data communications system are the message, send ...
The Network Interface Card
... can increase wait times for all users. After identifying the physical requirements of the NIC—the computer bus, the type of connector the card needs, and the type of network in which it will operate—it is necessary to consider several other factors that affect the capabilities of the card. Although ...
... can increase wait times for all users. After identifying the physical requirements of the NIC—the computer bus, the type of connector the card needs, and the type of network in which it will operate—it is necessary to consider several other factors that affect the capabilities of the card. Although ...
TCP, Performance and Delay
... • It is an algorithm to help the AIMD rule reach a good operating point faster on a fast network • The sender starts with a small window and every time it receives an acknowledgement before the retransmission timer goes off, it adds one to the window • So it isn’t really a slow start, it grows expon ...
... • It is an algorithm to help the AIMD rule reach a good operating point faster on a fast network • The sender starts with a small window and every time it receives an acknowledgement before the retransmission timer goes off, it adds one to the window • So it isn’t really a slow start, it grows expon ...
Module 4 Part a - Pohang University of Science and Technology
... 16-bit identifier flgs offset time to upper Internet layer live checksum ...
... 16-bit identifier flgs offset time to upper Internet layer live checksum ...
Technical Solutions for the 3G Long
... may result in a very high initial code rate, in some cases even higher than one, making it highly unlikely that such a transmission can be decoded correctly. Therefore, in combination with incremental redundancy HARQ, so-called autonomous retransmission is performed, whereby more data from this PDU ...
... may result in a very high initial code rate, in some cases even higher than one, making it highly unlikely that such a transmission can be decoded correctly. Therefore, in combination with incremental redundancy HARQ, so-called autonomous retransmission is performed, whereby more data from this PDU ...
ppt - inst.eecs.berkeley.edu
... Upon receiving message (Y, d, Z) from Z, check Y’s id If new id smaller, start viewing that switch as root Switches compute their distance from the root Add 1 to the distance received from a neighbor Identify interfaces not on shortest path to the root … and exclude them from the spanning ...
... Upon receiving message (Y, d, Z) from Z, check Y’s id If new id smaller, start viewing that switch as root Switches compute their distance from the root Add 1 to the distance received from a neighbor Identify interfaces not on shortest path to the root … and exclude them from the spanning ...
Ohm`s Law in series and parallel circuits -
... Ohm’s Law in series and parallel circuits -- Lab CLASS SET – WRITE ON YOUR OWN PAPER Each individual of a lab group will be writing down data collected so it can be taken to the computer lab, graphed, and analyzed. You will be constructing 1 resistor, 2 resistor, and 3 resistor series circuits using ...
... Ohm’s Law in series and parallel circuits -- Lab CLASS SET – WRITE ON YOUR OWN PAPER Each individual of a lab group will be writing down data collected so it can be taken to the computer lab, graphed, and analyzed. You will be constructing 1 resistor, 2 resistor, and 3 resistor series circuits using ...
How the TCP/IP Protocol Works
... • Minimal overhead, high performance – No setup/teardown, 1 datagram at a time ...
... • Minimal overhead, high performance – No setup/teardown, 1 datagram at a time ...
3rd Edition, Chapter 5
... framing, link access: encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...
... framing, link access: encapsulate datagram into frame, adding header, trailer channel access if shared medium “MAC” addresses used in frame headers to identify source, dest • different from IP address! ...