Guide to Operating System Security
... with a computer communication Shows that the source of the file or communication is legitimate Typically encrypted by a private key and decrypted by a public key Issued by a certificate authority ...
... with a computer communication Shows that the source of the file or communication is legitimate Typically encrypted by a private key and decrypted by a public key Issued by a certificate authority ...
Securing IT Assets with Linux
... • Government agencies, like the CIA and FBI, have been breached before, despite their almost unlimited resources and abilities. Lately the CIA and the FBI have been off-limits for crackers, but this is mainly because of their ability to catch crackers, not because they can prevent them from breaking ...
... • Government agencies, like the CIA and FBI, have been breached before, despite their almost unlimited resources and abilities. Lately the CIA and the FBI have been off-limits for crackers, but this is mainly because of their ability to catch crackers, not because they can prevent them from breaking ...
ISi-L - BSI
... Even today, the exchange of data in the internet is still based mainly on the communication protocols and services from the early days. Their security characteristics are no longer sufficient, though, for today’s threat level. Technical and organisational precautions absolutely must be made for secu ...
... Even today, the exchange of data in the internet is still based mainly on the communication protocols and services from the early days. Their security characteristics are no longer sufficient, though, for today’s threat level. Technical and organisational precautions absolutely must be made for secu ...
Risk Analysis - University at Albany
... • Different stakeholders have various perception of risk • Several sources of threats exist simultaneously Sanjay Goel, School of Business/Center for Information Forensics and Assurance University at Albany Proprietary Information ...
... • Different stakeholders have various perception of risk • Several sources of threats exist simultaneously Sanjay Goel, School of Business/Center for Information Forensics and Assurance University at Albany Proprietary Information ...
Lecture 8 - Faculty Web Pages
... information is collected and stored on computer systems; it also covers how the information is shared. • Personal Information – Data or information that can be directly related to an identified person – Regardless of data format and content ...
... information is collected and stored on computer systems; it also covers how the information is shared. • Personal Information – Data or information that can be directly related to an identified person – Regardless of data format and content ...
Red Hat Database
... Connection security and transmission security serve to ensure that only authorized users may connect to a database server. However, often finer grained security is required. For example, a manager from engineering might be authorized to view information about his department's budget, but should not ...
... Connection security and transmission security serve to ensure that only authorized users may connect to a database server. However, often finer grained security is required. For example, a manager from engineering might be authorized to view information about his department's budget, but should not ...
CHAPTER 1 Networking Concepts
... Business Requirements for SET over Internet Provide confidentiality of payment and order information Ensure the integrity of all transmitted data Provide authentication that a cardholder is a legitimate user of a credit card account Provide authentication that a merchant can accept credit ca ...
... Business Requirements for SET over Internet Provide confidentiality of payment and order information Ensure the integrity of all transmitted data Provide authentication that a cardholder is a legitimate user of a credit card account Provide authentication that a merchant can accept credit ca ...
InterScan Messaging Security Solutions
... and behavior analysis - Antivirus = prevents virus attacks aimed at specific organizations (for example, ransom attacks) - Anti-spyware = stops the more targeted spyware attacks sent through email. - DHA and bounced mail protection (IP Profiler) = protects against bounced mail attacks and directory ...
... and behavior analysis - Antivirus = prevents virus attacks aimed at specific organizations (for example, ransom attacks) - Anti-spyware = stops the more targeted spyware attacks sent through email. - DHA and bounced mail protection (IP Profiler) = protects against bounced mail attacks and directory ...
Managing security risks and vulnerabilities
... corrective action to patch those machines. At the same time, today’s sophisticated attackers are becoming stealthier. Recent research, for example, shows that attackers are spending long periods of time in the victim’s network—an average of 243 days—before being discovered.4 And even after an incide ...
... corrective action to patch those machines. At the same time, today’s sophisticated attackers are becoming stealthier. Recent research, for example, shows that attackers are spending long periods of time in the victim’s network—an average of 243 days—before being discovered.4 And even after an incide ...
HBA LED - Coronet Lighting
... PROPERTY OF CORONET INC., AND THE INFORMATION IT CONTAINS MAY NOT BE USED WITHOUT ANY WRITTEN CONSENT OF CORONET INC. ...
... PROPERTY OF CORONET INC., AND THE INFORMATION IT CONTAINS MAY NOT BE USED WITHOUT ANY WRITTEN CONSENT OF CORONET INC. ...
Introduction
... • Source code for Trojan horse does not appear anywhere in login or C compiler. • Only method of finding Trojan is analyzing binary. CSC 682: Advanced Computer Security ...
... • Source code for Trojan horse does not appear anywhere in login or C compiler. • Only method of finding Trojan is analyzing binary. CSC 682: Advanced Computer Security ...
IPSec
... Bump-in-stack Update OS network stack Adding software that’s binds to network stack can cause software conflicts ...
... Bump-in-stack Update OS network stack Adding software that’s binds to network stack can cause software conflicts ...
Security+ Guide to Network Security Fundamentals, Third
... Determining vulnerabilities often depends upon the background and experience of the assessor ...
... Determining vulnerabilities often depends upon the background and experience of the assessor ...
Strategies Simplified Australian Signals Directorate
... Patching operating systems and firmware significantly reduces the risks from zero-day threats which take advantage of exploits to install malware into your networks. By maintaining a streamlined patch management strategy, organisations can position themselves to act swiftly upon security bulletin or ...
... Patching operating systems and firmware significantly reduces the risks from zero-day threats which take advantage of exploits to install malware into your networks. By maintaining a streamlined patch management strategy, organisations can position themselves to act swiftly upon security bulletin or ...
POLICY Number: 0-501 Title: Information Technology Resources
... System) campuses, colleges, departments and entities. In some cases, these applications have become critical to the operation of the organization and the USF System. It is essential, therefore, that adequate measures be used to protect the integrity and reliability of those computing systems and the ...
... System) campuses, colleges, departments and entities. In some cases, these applications have become critical to the operation of the organization and the USF System. It is essential, therefore, that adequate measures be used to protect the integrity and reliability of those computing systems and the ...
Cybersecurity for Asset Managers: Shielding Your Firm
... to detect, respond to, identify, prevent and recover from an attack. To become more cyber resilient, firms should not only incorporate perimeter security, but also implement business risk/reward decision making, cyber risk management and control techniques throughout their business processes. They s ...
... to detect, respond to, identify, prevent and recover from an attack. To become more cyber resilient, firms should not only incorporate perimeter security, but also implement business risk/reward decision making, cyber risk management and control techniques throughout their business processes. They s ...
Security Without End Always-on SSL Protects Users with Persistent
... vulnerability to eavesdrop or hijack the user’s session. Companies that are serious about protecting their customers and their reputations should implement Always-on SSL. It’s a proven, vendor-neutral approach to security that protects users from start to finish. Always-on SSL gives your customers t ...
... vulnerability to eavesdrop or hijack the user’s session. Companies that are serious about protecting their customers and their reputations should implement Always-on SSL. It’s a proven, vendor-neutral approach to security that protects users from start to finish. Always-on SSL gives your customers t ...
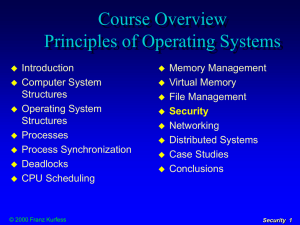
Security
... systems may be of considerable value and must be protected from damage hardware, software, and stored data may be essential for the performance of tasks and need to be available when needed system objects need to be protected from inadvertent unauthorized access or use there is the possibility ...
... systems may be of considerable value and must be protected from damage hardware, software, and stored data may be essential for the performance of tasks and need to be available when needed system objects need to be protected from inadvertent unauthorized access or use there is the possibility ...
Self-Assessment Questionnaire
... Most community banks will not be required to provide an opt-out notice to their customers. However, some organizations may still wish to give customers the right to opt-out of marketing solicitations. In general, nonpublic, personal information may not be shared with any third party that is not an a ...
... Most community banks will not be required to provide an opt-out notice to their customers. However, some organizations may still wish to give customers the right to opt-out of marketing solicitations. In general, nonpublic, personal information may not be shared with any third party that is not an a ...
các vấn đề bảo mật nổi bật trong các hệ thống quản trị dữ liệu và
... examine if there are potential security violations via inference. More discussions and references can be found in [10, 1]. As new technologies and applications emerge, such as data warehousing, data mining, e-health information systems, etc. the inference problem receives much more attention. We wil ...
... examine if there are potential security violations via inference. More discussions and references can be found in [10, 1]. As new technologies and applications emerge, such as data warehousing, data mining, e-health information systems, etc. the inference problem receives much more attention. We wil ...
Chap12 Presentation
... Internet and Network Security What is another way to protect your personal computer? ...
... Internet and Network Security What is another way to protect your personal computer? ...
Intersystems HealthShare Information Exchange V1.0
... system-software, servers, and storage requirements to be provided for each individual contract. Two options are available for deployment, either a client self-hosted solution or an InterSystems hosted solution within appropriate secure data-centre capacity within the UK. In all cases it is anticip ...
... system-software, servers, and storage requirements to be provided for each individual contract. Two options are available for deployment, either a client self-hosted solution or an InterSystems hosted solution within appropriate secure data-centre capacity within the UK. In all cases it is anticip ...
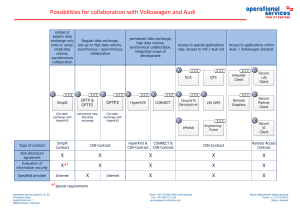
Possibilities for collaboration with Volkswagen
... The users in the partner company are the company's own internal permanent employees. In particular, no loan and temporary staff or subcontractors are deployed. All users are managed in a room reservation plan with reference to the workplace (room/ network socket) and the terminal used. Only authoriz ...
... The users in the partner company are the company's own internal permanent employees. In particular, no loan and temporary staff or subcontractors are deployed. All users are managed in a room reservation plan with reference to the workplace (room/ network socket) and the terminal used. Only authoriz ...
emerging security issues in modern data management systems and
... examine if there are potential security violations via inference. More discussions and references can be found in [10, 1]. As new technologies and applications emerge, such as data warehousing, data mining, e-health information systems, etc. the inference problem receives much more attention. We wil ...
... examine if there are potential security violations via inference. More discussions and references can be found in [10, 1]. As new technologies and applications emerge, such as data warehousing, data mining, e-health information systems, etc. the inference problem receives much more attention. We wil ...