Network Vulnerability Scanning - Texas Tech University Departments
... Attackers targeting victims by first exploiting trusted entities Shift from “Hacking for Fame” to “Hacking for Fortune” ...
... Attackers targeting victims by first exploiting trusted entities Shift from “Hacking for Fame” to “Hacking for Fortune” ...
Security of Cookies in a computer lab setting
... Where are the cookies? • Cookies exist on both major web browsers – Netscape stores all cookies in the cookies.txt file in a Netscape directory – Internet Explorer stores individual cookies as text files in a cookies directory ...
... Where are the cookies? • Cookies exist on both major web browsers – Netscape stores all cookies in the cookies.txt file in a Netscape directory – Internet Explorer stores individual cookies as text files in a cookies directory ...
PDF - IBM Redbooks
... granular level, such as read, write, append file, and chat, and must be individually controlled. Another challenge for organizations is the deployment of firewalls, intrusion prevention, URL filtering, vulnerability management, and other technologies that are not integrated. The usage of these poorl ...
... granular level, such as read, write, append file, and chat, and must be individually controlled. Another challenge for organizations is the deployment of firewalls, intrusion prevention, URL filtering, vulnerability management, and other technologies that are not integrated. The usage of these poorl ...
SNMP
... • SNMP is the prevailing standard for management of TCP/IP networks. SNMP is layered on top of UDP, the User Datagram Protocol. • An SNMP management station monitors and controls a managed node by issuing requests directed to the agent residing in the managed node. The agent interprets the request a ...
... • SNMP is the prevailing standard for management of TCP/IP networks. SNMP is layered on top of UDP, the User Datagram Protocol. • An SNMP management station monitors and controls a managed node by issuing requests directed to the agent residing in the managed node. The agent interprets the request a ...
slides [pdf]
... 2. Vivek Haldar, Deepak Chandra, and Michael Franz, “Semantic Remote attestation: A Virtual Machine Directed Approach to Trusted Computing”, USENIX Virtual Machine Research and Technology Symposium, May 2004; Winner of Best Paper Award (also Technical Report No. 03-20, School of Information and Comp ...
... 2. Vivek Haldar, Deepak Chandra, and Michael Franz, “Semantic Remote attestation: A Virtual Machine Directed Approach to Trusted Computing”, USENIX Virtual Machine Research and Technology Symposium, May 2004; Winner of Best Paper Award (also Technical Report No. 03-20, School of Information and Comp ...
Malicious Threats - The University of Texas at Dallas
... Computer is slow starting or slow running Unexpected or frequent system failures Change of system date/time Low computer memory or increased bad blocks on disks ...
... Computer is slow starting or slow running Unexpected or frequent system failures Change of system date/time Low computer memory or increased bad blocks on disks ...
Malicious Threats - The University of Texas at Dallas
... Computer is slow starting or slow running Unexpected or frequent system failures Change of system date/time Low computer memory or increased bad blocks on disks ...
... Computer is slow starting or slow running Unexpected or frequent system failures Change of system date/time Low computer memory or increased bad blocks on disks ...
Supplier Check List and Certification
... Will you hold or process the personal data of RAC customers while performing the services (including data held under 'white labelled' arrangements)? ...
... Will you hold or process the personal data of RAC customers while performing the services (including data held under 'white labelled' arrangements)? ...
111 opsec - Fleet Weather Center, Norfolk, VA
... • The OPSEC process, also known as the OPSEC five-step process, is the enabling vehicle for OPSEC planning. It provides the required information for the OPSEC portion of any plan or activity. • STEP ONE: IDENTIFY CRITICAL INFORMATION: CI is defined as information about friendly (U.S., allied and/or ...
... • The OPSEC process, also known as the OPSEC five-step process, is the enabling vehicle for OPSEC planning. It provides the required information for the OPSEC portion of any plan or activity. • STEP ONE: IDENTIFY CRITICAL INFORMATION: CI is defined as information about friendly (U.S., allied and/or ...
Title Size 30PT
... and nearly 400,000 registered users, Snort has become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
... and nearly 400,000 registered users, Snort has become the de facto standard for IPS. See more at http://www.snort.org. Never designed to be application aware Presentation_ID ...
Click for PDF - Cyber Security Services
... The Strategies to Mitigate Targeted Cyber Intrusions – Mitigation Details document includes an annex of key changes for 2014. A summary of the most significant changes are as follows. 10. Mitigation strategy #4 ‘Restrict administrative privileges’ has been amended to clarify that the ...
... The Strategies to Mitigate Targeted Cyber Intrusions – Mitigation Details document includes an annex of key changes for 2014. A summary of the most significant changes are as follows. 10. Mitigation strategy #4 ‘Restrict administrative privileges’ has been amended to clarify that the ...
CWNA Guide to Wireless LANs,Third Edition
... • One of the greatest risk that organizations face today are social engineering which involve manipulating human nature in order to persuade the victim to provide information or take actions • A security policy is a document that states how an organization plans to protect the company’s information ...
... • One of the greatest risk that organizations face today are social engineering which involve manipulating human nature in order to persuade the victim to provide information or take actions • A security policy is a document that states how an organization plans to protect the company’s information ...
ra-5 vulnerability scanning control
... Examine risk assessment policy, procedures addressing vulnerability scanning, security plan, or other relevant documents for the frequency for conducting vulnerability scans on the information system and hosted applications and/or; the process for conducting vulnerability scans on the information sy ...
... Examine risk assessment policy, procedures addressing vulnerability scanning, security plan, or other relevant documents for the frequency for conducting vulnerability scans on the information system and hosted applications and/or; the process for conducting vulnerability scans on the information sy ...
Aspects of Biological Evolution and Their
... the rights that these users have access to are based on the position of the .rhost file in the directory structure. For example, if a .rhost file in the home directory of “jill” on the machine “chilili” contains the line “zuzax jake” the user “jake” on the machine “zuzax” can use the rutilities to l ...
... the rights that these users have access to are based on the position of the .rhost file in the directory structure. For example, if a .rhost file in the home directory of “jill” on the machine “chilili” contains the line “zuzax jake” the user “jake” on the machine “zuzax” can use the rutilities to l ...
CH10
... – Calls Web bugs “clear GIFs” or “1-by-1 GIFs” • Graphics created in GIF format • Color value of “transparent,” small as 1 pixel by 1 pixel E-Business, Ninth Edition ...
... – Calls Web bugs “clear GIFs” or “1-by-1 GIFs” • Graphics created in GIF format • Color value of “transparent,” small as 1 pixel by 1 pixel E-Business, Ninth Edition ...
Tenable Malware Detection
... Utilizes Whitelist, Blacklist and Grey-list Intelligence In every organization there are many software components in use that are neither categorized as “good applications”, nor as “malicious software”. This is particularly true for organizations that allow self-provisioned machines and mobile devic ...
... Utilizes Whitelist, Blacklist and Grey-list Intelligence In every organization there are many software components in use that are neither categorized as “good applications”, nor as “malicious software”. This is particularly true for organizations that allow self-provisioned machines and mobile devic ...
Step 5: Securing Routing Protocols
... Why is Network Security Important? Computer networks have grown in both size and importance in a very short time. –If the security of the network is compromised, there could be serious consequences, such as loss of privacy, theft of information, and even legal liability. ...
... Why is Network Security Important? Computer networks have grown in both size and importance in a very short time. –If the security of the network is compromised, there could be serious consequences, such as loss of privacy, theft of information, and even legal liability. ...
Exploration CCNA4
... Why is Network Security Important? Computer networks have grown in both size and importance in a very short time. –If the security of the network is compromised, there could be serious consequences, such as loss of privacy, theft of information, and even legal liability. ...
... Why is Network Security Important? Computer networks have grown in both size and importance in a very short time. –If the security of the network is compromised, there could be serious consequences, such as loss of privacy, theft of information, and even legal liability. ...
Organizations That Use TLS/SSL
... or Medicaid, is covered by the Health Insurance Portability and Accountability Act (HIPAA) and must meet certain security standards. Additionally, any organization that stores or transmits user login or patient information may need to be compliant with the HIPAA Security Standard, even if it is not ...
... or Medicaid, is covered by the Health Insurance Portability and Accountability Act (HIPAA) and must meet certain security standards. Additionally, any organization that stores or transmits user login or patient information may need to be compliant with the HIPAA Security Standard, even if it is not ...
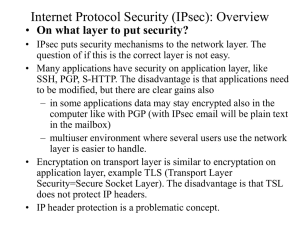
IPSec: Cryptography basics
... • IPsec is preferably implemented in the operating system level (OS) and merged with the IP level. This is called IPsec stack method. All IPsec options can be implemented and the implementation can be very efficient. IP fragmentation can be handled with the same code as IP uses. • If it is not possi ...
... • IPsec is preferably implemented in the operating system level (OS) and merged with the IP level. This is called IPsec stack method. All IPsec options can be implemented and the implementation can be very efficient. IP fragmentation can be handled with the same code as IP uses. • If it is not possi ...
SSH - Information Services and Technology
... IP and TCP Attacks: SSH operates on top of TCP, therefore some of its weaknesses come from TCP/IP problems. of the SSH connection. ...
... IP and TCP Attacks: SSH operates on top of TCP, therefore some of its weaknesses come from TCP/IP problems. of the SSH connection. ...
![slides [pdf]](http://s1.studyres.com/store/data/003737230_1-2696b7865b4160afff3b6862ae017bef-300x300.png)