Integrated Design Techniques Ltd www .idtuk.com Communications
... This is achieved by defining a clear interface between "layers" within the PC. At the top is the layer in which Microsoft Word resides (the Application Layer); lower down is the layer which decides that the dial-up or optical fibre link is to be used (the Physical Layer). The protocol explicitly def ...
... This is achieved by defining a clear interface between "layers" within the PC. At the top is the layer in which Microsoft Word resides (the Application Layer); lower down is the layer which decides that the dial-up or optical fibre link is to be used (the Physical Layer). The protocol explicitly def ...
01-intro
... Routing Addressing/naming (locating peers) Reliability Flow control Fragmentation Etc…. ...
... Routing Addressing/naming (locating peers) Reliability Flow control Fragmentation Etc…. ...
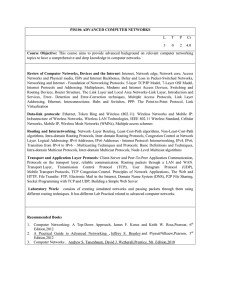
PIS106 ADVANCED COMPUTER NETWORKS Course Objective:
... Routing and Internetworking: Network–Layer Routing, Least-Cost-Path algorithms, Non-Least-Cost-Path algorithms, Intra-domain Routing Protocols, Inter-domain Routing Protocols, Congestion Control at Network Layer. Logical Addressing: IPv4 Addresses, IPv6 Addresses - Internet Protocol: Internetworking ...
... Routing and Internetworking: Network–Layer Routing, Least-Cost-Path algorithms, Non-Least-Cost-Path algorithms, Intra-domain Routing Protocols, Inter-domain Routing Protocols, Congestion Control at Network Layer. Logical Addressing: IPv4 Addresses, IPv6 Addresses - Internet Protocol: Internetworking ...
Chapter 9
... – TCP/IP combines the OSI data link and physical layers into one layer – TCP/IP appears simpler because it has fewer layers – TCP/IP transport layer using UDP does not always guarantee reliable delivery of packets as the transport layer in the OSI model does ...
... – TCP/IP combines the OSI data link and physical layers into one layer – TCP/IP appears simpler because it has fewer layers – TCP/IP transport layer using UDP does not always guarantee reliable delivery of packets as the transport layer in the OSI model does ...
Presentation 10
... Physical: how to transmit bits Data link: how to transmit frames Network: how to route packets Transport: how to send packets end2end Session: how to tie flows together ...
... Physical: how to transmit bits Data link: how to transmit frames Network: how to route packets Transport: how to send packets end2end Session: how to tie flows together ...
Chapter 5 : The Internet: Addressing & Services
... Domain Name System 32-bit IP addresses have two drawbacks Routers can’t keep track of every network path Users can’t remember dotted decimals easily ...
... Domain Name System 32-bit IP addresses have two drawbacks Routers can’t keep track of every network path Users can’t remember dotted decimals easily ...
Moving beyond TCP
... data could be passed between two points, a connection had to be set up. What differed from the connection oriented telephone network was that the actual network capacity was only consumed on demand, not merely by having a connection present. But NCP was also a very rigid protocol, designed to ensur ...
... data could be passed between two points, a connection had to be set up. What differed from the connection oriented telephone network was that the actual network capacity was only consumed on demand, not merely by having a connection present. But NCP was also a very rigid protocol, designed to ensur ...
HyperText Transfer Protocol
... Controls the dialogues/connections (sessions) between computers. It establishes, manages and terminates the connections between the local and remote application. ...
... Controls the dialogues/connections (sessions) between computers. It establishes, manages and terminates the connections between the local and remote application. ...
Chapter17 - Website Staff UI
... • Distributed operating system – Common operating system shared by a network of computers ...
... • Distributed operating system – Common operating system shared by a network of computers ...
Packet switching
... Advanced Research Projects Agency task was to create communication network for military purpose ...
... Advanced Research Projects Agency task was to create communication network for military purpose ...
The Network Layer
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
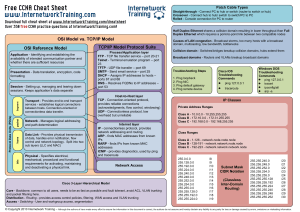
CCNA cheat sheet - Internetwork Training
... Cisco 3-Layer Hierarchical Model Core - Backbone, common to all users, needs to be as fast as possible and fault tolerant, avoid ACL, VLAN trunking and packet filtering here. Distribution - Routing - provides access control policies, filtering, WAN access and VLAN trunking Access - Switching - User ...
... Cisco 3-Layer Hierarchical Model Core - Backbone, common to all users, needs to be as fast as possible and fault tolerant, avoid ACL, VLAN trunking and packet filtering here. Distribution - Routing - provides access control policies, filtering, WAN access and VLAN trunking Access - Switching - User ...
IRIS Project
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
1-up PPT
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
... • The system is broken into a vertical hierarchy of protocols • The service provided by one layer is based solely on the service provided by layer below ...
Fundamentals of Computer Networks ECE 478/578
... fragmentation and re-assembly. Transport Layer: Flow (congestion) control, error control, transparent transport to upper layers Session Layer: Establishes connection among hosts, duplex, halfduplex, graceful connection termination, combination of streams Presentation Layer: Negotiation of format of ...
... fragmentation and re-assembly. Transport Layer: Flow (congestion) control, error control, transparent transport to upper layers Session Layer: Establishes connection among hosts, duplex, halfduplex, graceful connection termination, combination of streams Presentation Layer: Negotiation of format of ...
15-744: Computer Networking
... • Module in layered structure • Set of rules governing communication between network elements (applications, hosts, routers) • Protocols define: • Interface to higher layers (API) • Interface to peer • Format and order of messages • Actions taken on receipt of a message ...
... • Module in layered structure • Set of rules governing communication between network elements (applications, hosts, routers) • Protocols define: • Interface to higher layers (API) • Interface to peer • Format and order of messages • Actions taken on receipt of a message ...
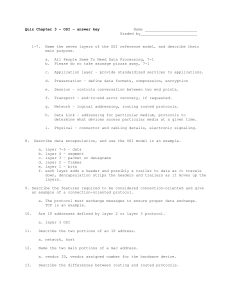
Quiz on ICND chapter 3
... Name the seven layers of the OSI reference model, and describe their main purpose. a. b. ...
... Name the seven layers of the OSI reference model, and describe their main purpose. a. b. ...
Introduction to Distributed Systems & Networking
... Network Layer:” routing packets to the destination Transport Layer: reliable transmission of messages, disassembly/assembly, ordering, retransmission of lost packets • Session Layer; really part of transport, typ. Not impl. • Presentation Layer: data representation in the message • Application: high ...
... Network Layer:” routing packets to the destination Transport Layer: reliable transmission of messages, disassembly/assembly, ordering, retransmission of lost packets • Session Layer; really part of transport, typ. Not impl. • Presentation Layer: data representation in the message • Application: high ...
Midterm Review - UTK-EECS
... Delay, loss and throughput: simple calculations using the 4 types of delay, bandwidth, link capacity, packet loss rate, and throughput Protocol layers: rationale behind layering design, the Internet 5-layer protocol stack, difference between Internet and OSI protocol stacks, encapsulation ...
... Delay, loss and throughput: simple calculations using the 4 types of delay, bandwidth, link capacity, packet loss rate, and throughput Protocol layers: rationale behind layering design, the Internet 5-layer protocol stack, difference between Internet and OSI protocol stacks, encapsulation ...
Why Internetworking? - California State University, Long Beach
... To create a "virtual" network: Invent -- An addressing scheme -- A naming scheme • Implement with the scheme with protocol software ...
... To create a "virtual" network: Invent -- An addressing scheme -- A naming scheme • Implement with the scheme with protocol software ...
The Network Layer
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
... Fragmentation when the elementary data size is 1 byte. (a) Original packet, containing 10 data bytes. (b) Fragments after passing through a network with maximum packet size of 8 payload bytes plus header. (c) Fragments after passing through a size 5 gateway. ...
61765 Computer Networks I
... Course Description This is an introductory course in computer networks and data communication methods. The TCP/IP layers are presented using a top-down approach, from the application to the physical layer. The course focuses on Internet protocols, with the addition of some application and line proto ...
... Course Description This is an introductory course in computer networks and data communication methods. The TCP/IP layers are presented using a top-down approach, from the application to the physical layer. The course focuses on Internet protocols, with the addition of some application and line proto ...
The Next Generation of IP
... The Next Generation of IP Router: This router can store and manage the state information of data flows. ...
... The Next Generation of IP Router: This router can store and manage the state information of data flows. ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.