Com811: Building The Mobile Internet
... • User can switch networks seamlessly • However, sessions will not necessarily ‘stay up’ ...
... • User can switch networks seamlessly • However, sessions will not necessarily ‘stay up’ ...
Cisco certified network associate
... • Application – HTTP, everything • Presentation – Human to computer (Layer 6) • Session – Build and tear down of session (Layer 5) • Transport – TCP/UDP (Layer 4) – a.ka. segment • Network – IP Address (Layer 3) – a.k.a. packet • Data Link – MAC (Layer 2) – a.k.a. frame ...
... • Application – HTTP, everything • Presentation – Human to computer (Layer 6) • Session – Build and tear down of session (Layer 5) • Transport – TCP/UDP (Layer 4) – a.ka. segment • Network – IP Address (Layer 3) – a.k.a. packet • Data Link – MAC (Layer 2) – a.k.a. frame ...
ppt
... “embed internetwork packets in local packet format or extract them” route (at internetwork level) to next gateway ...
... “embed internetwork packets in local packet format or extract them” route (at internetwork level) to next gateway ...
CSC 335 Data Communications and Networking I
... pieces all arrive correctly at the other end. • The transport layer also determines the type of services, connection-oriented or connectionless. ...
... pieces all arrive correctly at the other end. • The transport layer also determines the type of services, connection-oriented or connectionless. ...
Lecture 4a: Communication and Networking
... The physical path that is used to carry a signal between a signal transmitter and a signal receiver is called the "transmission medium" ...
... The physical path that is used to carry a signal between a signal transmitter and a signal receiver is called the "transmission medium" ...
The network layer
... countries use the Internet. Millions of people are users. It is difficult to give an accurate representation of the Internet, because it is continually changing. Today, most end users who want an Internet connection use the services of Internet service providers (ISPs). ...
... countries use the Internet. Millions of people are users. It is difficult to give an accurate representation of the Internet, because it is continually changing. Today, most end users who want an Internet connection use the services of Internet service providers (ISPs). ...
05. Reference Models and Example Networks
... flexible routing - tolerant to loss of network nodes, subnets, route[r]s, connections, etc. ...
... flexible routing - tolerant to loss of network nodes, subnets, route[r]s, connections, etc. ...
ITEC 370 Midterm
... ____ 13. ____ is a nonroutable protocol. a. NetBEUI c. IPX b. IP d. SPX ____ 14. ____ is a name-to-address resolution protocol that functionally operates at the Session layer of the OSI model. a. DNS c. ICMP b. ARP d. DHCP ____ 15. An IP address is divided into two distinct parts: one part designate ...
... ____ 13. ____ is a nonroutable protocol. a. NetBEUI c. IPX b. IP d. SPX ____ 14. ____ is a name-to-address resolution protocol that functionally operates at the Session layer of the OSI model. a. DNS c. ICMP b. ARP d. DHCP ____ 15. An IP address is divided into two distinct parts: one part designate ...
Document
... • To improve the efficiency of transferring information over a shared communication line, messages are divided into fixedsized, numbered packets • Network devices called routers are used to direct packets between networks Figure 15.4 Messages sent by packet switching ...
... • To improve the efficiency of transferring information over a shared communication line, messages are divided into fixedsized, numbered packets • Network devices called routers are used to direct packets between networks Figure 15.4 Messages sent by packet switching ...
Figure 2.1 Communication requires a message, a transmitter, a
... The bottom two layers work with packets and control the network. Network access layer ...
... The bottom two layers work with packets and control the network. Network access layer ...
2.2 2-1 LAYERED TASKS We use the concept of layers in our daily
... The layers in the TCP/IP protocol suite do not exactly match those in the OSI model. The original TCP/IP protocol suite was defined as having four layers: host-tonetwork, internet, transport, and application. However, when TCP/IP is compared to OSI, we can say that the TCP/IP protocol suite is made ...
... The layers in the TCP/IP protocol suite do not exactly match those in the OSI model. The original TCP/IP protocol suite was defined as having four layers: host-tonetwork, internet, transport, and application. However, when TCP/IP is compared to OSI, we can say that the TCP/IP protocol suite is made ...
No Slide Title - Institute of Technology Sligo
... The distribution layer of the network is the demarcation point between the access and core layers and helps to define and differentiate the core. The distribution layer would include the campus backbone with all its connecting routers. Because policy is typically implemented at this level, we can sa ...
... The distribution layer of the network is the demarcation point between the access and core layers and helps to define and differentiate the core. The distribution layer would include the campus backbone with all its connecting routers. Because policy is typically implemented at this level, we can sa ...
WB_intro
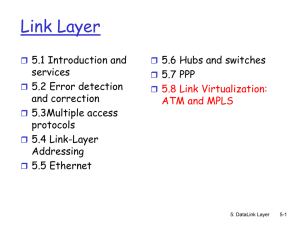
... 7 layer model for networks -1. physical - moves a bit from a to b using a physical(electrical, optical, etc.) signal 2. data link - groups bits into frames, or messages, for error control and information 3. network - routing function ...
... 7 layer model for networks -1. physical - moves a bit from a to b using a physical(electrical, optical, etc.) signal 2. data link - groups bits into frames, or messages, for error control and information 3. network - routing function ...
Application Layer - Teknik Elektro UGM
... P2P network allow computers to act as both clients and servers during the same communication. Each of them is called ‘peer’ because they can perform both tasks. Each user is in charge of his own access policies Disadvantage: ...
... P2P network allow computers to act as both clients and servers during the same communication. Each of them is called ‘peer’ because they can perform both tasks. Each user is in charge of his own access policies Disadvantage: ...
Document
... • Many Wide Area Networks and Local Area Networks exist. –Cannot connect a WAN to a ...
... • Many Wide Area Networks and Local Area Networks exist. –Cannot connect a WAN to a ...
Distributed Systems3. Protocol Hierarchies, OSI and TCP/IP
... OSI – Interaction Modalities • Connectionless: every SDU managed independently from the others – No guaranteed QoS – No memory nor negotiation, just isolated ...
... OSI – Interaction Modalities • Connectionless: every SDU managed independently from the others – No guaranteed QoS – No memory nor negotiation, just isolated ...
Some Network Commands - Texas Tech University
... receives a message, it needs to know which application layer software package should receive the message. ...
... receives a message, it needs to know which application layer software package should receive the message. ...
Internet Protocols
... browser while viewing this article. They are located at the beginning of the address and are used to tell the browser how to properly process the data on the page and display the data to a computer user. The word hyper in the acronym is used to specify that the text is not linear and can actually be ...
... browser while viewing this article. They are located at the beginning of the address and are used to tell the browser how to properly process the data on the page and display the data to a computer user. The word hyper in the acronym is used to specify that the text is not linear and can actually be ...
Chapter 2
... (OSI) reference model was created by the International Organization for Standardization (ISO) to break through this barrier. • The OSI model was meant to help vendors create interoperable network devices and software in the form of protocols so that different vendor networks could work with each oth ...
... (OSI) reference model was created by the International Organization for Standardization (ISO) to break through this barrier. • The OSI model was meant to help vendors create interoperable network devices and software in the form of protocols so that different vendor networks could work with each oth ...
1.7 The history of Computer Networking and the Internet
... In 1995 NSFNET is decomissioned and Internet Service Providers serves as the new backbones in its ...
... In 1995 NSFNET is decomissioned and Internet Service Providers serves as the new backbones in its ...
Transport Protocols
... • Transport-layer protocols in the Internet – User Datagram Protocol (UDP) – Transmission Control Protocol (TCP) ...
... • Transport-layer protocols in the Internet – User Datagram Protocol (UDP) – Transmission Control Protocol (TCP) ...
Networking Components
... What is Networking? Most people use the internet nowadays but did you ask ...
... What is Networking? Most people use the internet nowadays but did you ask ...
Recursive InterNetwork Architecture (RINA)

The Recursive InterNetwork Architecture (RINA) is a computer network architecture that unifies distributed computing and telecommunications. RINA's fundamental principle is that computer networking is just Inter-Process Communication or IPC. RINA reconstructs the overall structure of the Internet, forming a model that comprises a single repeating layer, the DIF (Distributed IPC Facility), which is the minimal set of components required to allow distributed IPC between application processes. RINA inherently supports mobility, multi-homing and Quality of Service without the need for extra mechanisms, provides a secure and programmable environment, motivates for a more competitive marketplace, and allows for a seamless adoption.