SwitchPlusIP Advanced Maintenance Training Presentation
... - In this situation, should any piece of equipment’s connection to a switch fail, its resources are not lost as it will still have a network connection. Audio may be lost temporarily as the equipment switches from using LAN A to LAN B. The impact is minimal. Note that in order to maintain a dual-red ...
... - In this situation, should any piece of equipment’s connection to a switch fail, its resources are not lost as it will still have a network connection. Audio may be lost temporarily as the equipment switches from using LAN A to LAN B. The impact is minimal. Note that in order to maintain a dual-red ...
Sun EnterpriseTM 420R Server Just the Facts
... • The Sun Enterprise 420R server runs Sun’s • The Solaris Operating Environment, recognized as an powerful and dependable SolarisTM industry-leading enterprise network operating system, Operating Environment and is 100 percent runs over 12,000 of the most extensively tested, binary compatible with a ...
... • The Sun Enterprise 420R server runs Sun’s • The Solaris Operating Environment, recognized as an powerful and dependable SolarisTM industry-leading enterprise network operating system, Operating Environment and is 100 percent runs over 12,000 of the most extensively tested, binary compatible with a ...
Sun EnterpriseTM 220R Server Just the Facts
... Sun Enterprise 220R Servers The Sun Enterprise 220R server supports up to two 450-MHz UltraSPARC-II 64-bit RISC microprocessors with 4 MB of Ecache (L2) each, 2 GB of main memory, two internal 9.1-GB or 18.2-GB hot-swap UltraSCSI disk drives, four PCI slots connected to two high-performance PCI I/O ...
... Sun Enterprise 220R Servers The Sun Enterprise 220R server supports up to two 450-MHz UltraSPARC-II 64-bit RISC microprocessors with 4 MB of Ecache (L2) each, 2 GB of main memory, two internal 9.1-GB or 18.2-GB hot-swap UltraSCSI disk drives, four PCI slots connected to two high-performance PCI I/O ...
Installation Documentation for Always Available™ Infrastructure
... The messaging server is a built-in function of the ZeroNines messaging system for delivering transactions reliably between the switches and nodes. Transactions are buffered to the messaging server's memory, paged memory and/or disk. Typically, the messaging server can hold 30 minutes worth of transa ...
... The messaging server is a built-in function of the ZeroNines messaging system for delivering transactions reliably between the switches and nodes. Transactions are buffered to the messaging server's memory, paged memory and/or disk. Typically, the messaging server can hold 30 minutes worth of transa ...
McGraw-Hill
... Computers are required to perform many different tasks at once—to do task management Task: An operation such as storing, printing, or calculating Multitasking: Handling more than one program concurrently ...
... Computers are required to perform many different tasks at once—to do task management Task: An operation such as storing, printing, or calculating Multitasking: Handling more than one program concurrently ...
SDN End Hosts and Storage
... Security as a Service • Clouds are large, complicated, and dynamic • How do tenants deploy security devices/functions? • Tenant can use some pre-installed fixed-location security devices – Not able to keep up with the high dynamisms in network configurations ...
... Security as a Service • Clouds are large, complicated, and dynamic • How do tenants deploy security devices/functions? • Tenant can use some pre-installed fixed-location security devices – Not able to keep up with the high dynamisms in network configurations ...
Rudimentary NMS Software Components (Chapter 7)
... MsgID used between two entities for msg correlation ...
... MsgID used between two entities for msg correlation ...
NWA Presentation - AMS supported meetings
... Combining the full testing resources of the FAA and NWS for the software going into both AWOS and ASOS will bring together a fuller and more diverse set of capabilities, resulting in improved quality of the software releases. ...
... Combining the full testing resources of the FAA and NWS for the software going into both AWOS and ASOS will bring together a fuller and more diverse set of capabilities, resulting in improved quality of the software releases. ...
PDF
... or bug fixes via SMU. From June 18, 2011 until June 18, 2012, maintenance rebuilds and software fix via SMU support for Cisco IOS XR Software 3.9.x will be provided only through migration to rebuilds of Cisco IOS XR Software 4.0.x. After June 19, 2012, Cisco Engineering will no longer develop, repai ...
... or bug fixes via SMU. From June 18, 2011 until June 18, 2012, maintenance rebuilds and software fix via SMU support for Cisco IOS XR Software 3.9.x will be provided only through migration to rebuilds of Cisco IOS XR Software 4.0.x. After June 19, 2012, Cisco Engineering will no longer develop, repai ...
Rudimentary NMS Software Components (Chapter 7)
... Performance Bottlenecks in FCAPS applications due to congestion on the network. Client Applications crashing from time to time MIB Table Corruption SNMP Agent Exceptions ...
... Performance Bottlenecks in FCAPS applications due to congestion on the network. Client Applications crashing from time to time MIB Table Corruption SNMP Agent Exceptions ...
Rudimentary NMS Software Components
... Performance Bottlenecks in FCAPS applications due to congestion on the network. Client Applications crashing from time to time MIB Table Corruption SNMP Agent Exceptions ...
... Performance Bottlenecks in FCAPS applications due to congestion on the network. Client Applications crashing from time to time MIB Table Corruption SNMP Agent Exceptions ...
Style Guide - Surescripts
... The Connected logo may not be used by software vendors that have certified their products for connectivity to the Surescripts network. Surescripts’ ‘certified’, ‘Solution Provider’, and ‘Gold Certified’ marks are reserved for this use. Logo Requirements Use of the “Surescripts Connected” logo must f ...
... The Connected logo may not be used by software vendors that have certified their products for connectivity to the Surescripts network. Surescripts’ ‘certified’, ‘Solution Provider’, and ‘Gold Certified’ marks are reserved for this use. Logo Requirements Use of the “Surescripts Connected” logo must f ...
20100713 Boyd IRIS DyGIR - International Networks at IU
... – Partner with interested IRNC PRONET awardees in order to support their success ...
... – Partner with interested IRNC PRONET awardees in order to support their success ...
A+ Guide to Managing and Troubleshooting Software 2e
... Generally you should use the most current version to get the latest features and fixes to known problems With an older computer or OS, you may not want the latest version Check http://support.microsoft.com Download updates and patches from http://windowsupdate.microsoft.com ...
... Generally you should use the most current version to get the latest features and fixes to known problems With an older computer or OS, you may not want the latest version Check http://support.microsoft.com Download updates and patches from http://windowsupdate.microsoft.com ...
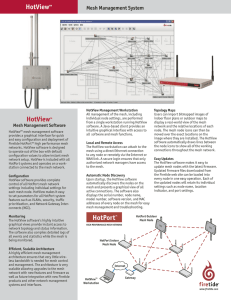
HotViewTM HotView™
... display a real-world view of the mesh network and the relative locations of each node. The mesh node icons can then be moved over the exact locations on the image where they are installed. The HotView software automatically draws lines between the node icons to show all of the working connections th ...
... display a real-world view of the mesh network and the relative locations of each node. The mesh node icons can then be moved over the exact locations on the image where they are installed. The HotView software automatically draws lines between the node icons to show all of the working connections th ...
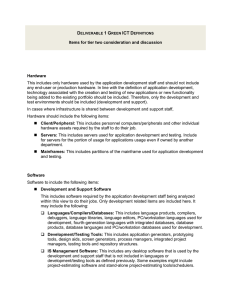
Deliverable 1 Green ICT Definitions
... communications software specific to the mainframe, midrange servers and/or data center (but not including the storage area network [SAN]). Security: Include all software used to provide access security and protection against attacks (for example, anti-spam, anti-malware, antivirus, Web filtering, ...
... communications software specific to the mainframe, midrange servers and/or data center (but not including the storage area network [SAN]). Security: Include all software used to provide access security and protection against attacks (for example, anti-spam, anti-malware, antivirus, Web filtering, ...
Slide 1
... Can Home Devices turn against us, spy on our Network? Privacy and trust issues raised by technology, New hardware & Cool devices ...
... Can Home Devices turn against us, spy on our Network? Privacy and trust issues raised by technology, New hardware & Cool devices ...
Document
... For network applications, a domain name must be mapped to its corresponding Internet address. Processes known as domain name system servers provide the mapping service, based on a distributed database of the mapping scheme. The mapping service is offered by thousands of DNS servers on the Internet, ...
... For network applications, a domain name must be mapped to its corresponding Internet address. Processes known as domain name system servers provide the mapping service, based on a distributed database of the mapping scheme. The mapping service is offered by thousands of DNS servers on the Internet, ...
Top 10 Database tuning tips
... student name every time they take a new test • We don’t want to repeat the test_name for every student that takes it • We don’t want the “repeating group” of answers – Also, we might not know how many questions there will be in future tests ...
... student name every time they take a new test • We don’t want to repeat the test_name for every student that takes it • We don’t want the “repeating group” of answers – Also, we might not know how many questions there will be in future tests ...
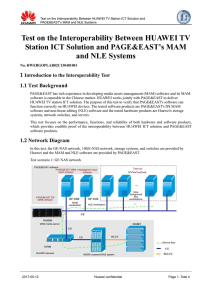
Test on the Interoperability Between HUAWEI TV Station ICT
... PAGE&EAST has rich experience in developing media assets management (MAM) software and its MAM software is reputable in the Chinese market. HUAWEI works jointly with PAGE&EAST to deliver HUAWEI TV station ICT solution. The purpose of this test to verify that PAGE&EAST's software can function correct ...
... PAGE&EAST has rich experience in developing media assets management (MAM) software and its MAM software is reputable in the Chinese market. HUAWEI works jointly with PAGE&EAST to deliver HUAWEI TV station ICT solution. The purpose of this test to verify that PAGE&EAST's software can function correct ...
Providing Real-Time Services for COTS
... lead to unbounded response times. If the duration of I/O activity in a given period can be characterized, it may be possible to compute the response times conservatively. One should not depend on the Windows NT scheduler to achieve correct “fair sharing” behavior in cases where screen, keyboard ...
... lead to unbounded response times. If the duration of I/O activity in a given period can be characterized, it may be possible to compute the response times conservatively. One should not depend on the Windows NT scheduler to achieve correct “fair sharing” behavior in cases where screen, keyboard ...
NetLight SNMP Management
... NL100-880, NL/G-2300. When no license is supplied, you can order the Basic or Extended license (see part numbers in the table above). When the Basic license is supplied by default, you can order the Extended version. Upgrading can be carried out at any time, even after the NetLight has been installe ...
... NL100-880, NL/G-2300. When no license is supplied, you can order the Basic or Extended license (see part numbers in the table above). When the Basic license is supplied by default, you can order the Extended version. Upgrading can be carried out at any time, even after the NetLight has been installe ...
Introducing Hardware and Software Required for Video
... If any agency which wants to sale DVcommXP outside of Japan is coming up. And it researches violations of intellectual property rights and the problem will become clear. They will discussion about to sale overseas. ...
... If any agency which wants to sale DVcommXP outside of Japan is coming up. And it researches violations of intellectual property rights and the problem will become clear. They will discussion about to sale overseas. ...
10_sw - Lyle School of Engineering
... An object is an entity that has • State -- the value of all the attributes at a given time • Behavior -- the actions and reactions of the object in response to external input • Identity -- distinguishes object from other objects an object is an instantiation of a class ...
... An object is an entity that has • State -- the value of all the attributes at a given time • Behavior -- the actions and reactions of the object in response to external input • Identity -- distinguishes object from other objects an object is an instantiation of a class ...