Computer Networks, Tanenbaum 2
... along the path as a continuous stream of bits. This path is maintained for the duration of communication between A and B, and is then released. In packet switching, data is divided into packets (chunks of specific length and characteristics) which are sent from A to B via intermediate nodes. Each in ...
... along the path as a continuous stream of bits. This path is maintained for the duration of communication between A and B, and is then released. In packet switching, data is divided into packets (chunks of specific length and characteristics) which are sent from A to B via intermediate nodes. Each in ...
Unit E - Home - KSU Faculty Member websites
... Network Topology: configuration Packet Switching Technology: determines how data is broken up Protocols: rules for successful and accurate data transmission ...
... Network Topology: configuration Packet Switching Technology: determines how data is broken up Protocols: rules for successful and accurate data transmission ...
Distributed Monitoring of Mesh Networks
... essential for evolving network technologies critical last piece in the product conceptiondesign-development-improvement loop helps bridge the gap between the expected (simulations) and the unexpected (real-world) ...
... essential for evolving network technologies critical last piece in the product conceptiondesign-development-improvement loop helps bridge the gap between the expected (simulations) and the unexpected (real-world) ...
IP / MPLS - IDG Communications
... • Network has full QoS feature support with Service Level Guarantees to support lower latency, packet loss and jitter • 100% Powered by Cisco Systems – Single vendor platform • Infrastructure is SOUL owned and operated, and independent of Telstra • In excess of 900 employees in offices throughout Au ...
... • Network has full QoS feature support with Service Level Guarantees to support lower latency, packet loss and jitter • 100% Powered by Cisco Systems – Single vendor platform • Infrastructure is SOUL owned and operated, and independent of Telstra • In excess of 900 employees in offices throughout Au ...
CST125 - Suffolk County Community College
... Introduction to Data Communication and Networking. Basic Concepts. Protocols and Standards. Line Configurations, topology Network transmission modes, Categories of networks, Internetworking. The OSI model. TCP/IP protocol suite. Signals, Encoding and Modulating. Transmission media, Data link control ...
... Introduction to Data Communication and Networking. Basic Concepts. Protocols and Standards. Line Configurations, topology Network transmission modes, Categories of networks, Internetworking. The OSI model. TCP/IP protocol suite. Signals, Encoding and Modulating. Transmission media, Data link control ...
MESH NETWORK SIMULAION Pei Ping Belarusian National
... meetings are held here every year. If there is high-speed wireless network coverage, it could support a lot of school activities. An open area in class room provides a good environmental condition for mesh network. There are two AP – 4900M devices in classroom offering the wireless coverage indoor. ...
... meetings are held here every year. If there is high-speed wireless network coverage, it could support a lot of school activities. An open area in class room provides a good environmental condition for mesh network. There are two AP – 4900M devices in classroom offering the wireless coverage indoor. ...
02-design
... should have minimum performance impact on the applications that do not use the functionality ...
... should have minimum performance impact on the applications that do not use the functionality ...
NETWORKING I
... the browser, which web server software should be used to serve the web pages, what operating system the software runs on, or the hardware requirements necessary to display the browser. It also does not describe how the server should detect errors, although it does describe what the server should do ...
... the browser, which web server software should be used to serve the web pages, what operating system the software runs on, or the hardware requirements necessary to display the browser. It also does not describe how the server should detect errors, although it does describe what the server should do ...
csci5211: Computer Networks and Data Communications
... Fundamental Problems in Networking … What can go wrong? • Bit-level errors: due to electrical interferences • Packet-level errors: packet loss due to buffer overflow/congestion • Out of order delivery: packets may takes ...
... Fundamental Problems in Networking … What can go wrong? • Bit-level errors: due to electrical interferences • Packet-level errors: packet loss due to buffer overflow/congestion • Out of order delivery: packets may takes ...
Networks and Networking - INASP
... networks together • Firewalls: Firewalls are the most important aspect of a network with respect to security. A firewalled system ...
... networks together • Firewalls: Firewalls are the most important aspect of a network with respect to security. A firewalled system ...
ITGS
... where a server is too expensive/ not necessary • Each computer shares the files from its own hard disk, and other machines are able to access them • With more than a few users, the lack of a server to aid in security and storage becomes a problem ...
... where a server is too expensive/ not necessary • Each computer shares the files from its own hard disk, and other machines are able to access them • With more than a few users, the lack of a server to aid in security and storage becomes a problem ...
MobileMAN Architecture and Protocols
... Inter-layer coordination (cont.) Example: Forwarding/Cooperation/Transport coordination (cont.) The transport layer might use a redundant coding technique (see, e.g., FEC): a message is coded into n blocks but only k (k
... Inter-layer coordination (cont.) Example: Forwarding/Cooperation/Transport coordination (cont.) The transport layer might use a redundant coding technique (see, e.g., FEC): a message is coded into n blocks but only k (k
02-design
... should have minimum performance impact on the applications that do not use the functionality ...
... should have minimum performance impact on the applications that do not use the functionality ...
CHAP10 - Lyle School of Engineering
... • Can’t Replace Large TPS Programs (e.g.: Payroll; Accounting; Production / Operations; Marketing) • Too Slow for High-Speed Data Transfer • Not yet as Functional as Groupware • Require Tight Security Control and Careful Management Planning ...
... • Can’t Replace Large TPS Programs (e.g.: Payroll; Accounting; Production / Operations; Marketing) • Too Slow for High-Speed Data Transfer • Not yet as Functional as Groupware • Require Tight Security Control and Careful Management Planning ...
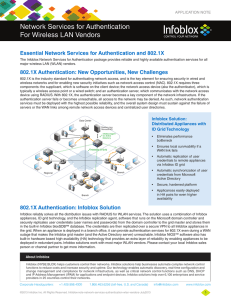
Network Services for Authentication For Wireless LAN
... appliances, ID grid technology, and the Infoblox replication agent, software that runs on the Microsoft domain controller and securely replicates user credentials (user names and passwords) from the domain controller to the grid master and stores them in the built-in Infoblox bloxSDB™ database. The ...
... appliances, ID grid technology, and the Infoblox replication agent, software that runs on the Microsoft domain controller and securely replicates user credentials (user names and passwords) from the domain controller to the grid master and stores them in the built-in Infoblox bloxSDB™ database. The ...
Basic LAN Devices Repeaters There are many types of media, and
... of network addresses (Classes) as opposed to individual Layer 2 MAC addresses. Routers can also connect different Layer 2 technologies, such as Ethernet, Token-ring, and FDDI. However, because of their ability to route packets based on Layer 3 information, routers have become the backbone of the Int ...
... of network addresses (Classes) as opposed to individual Layer 2 MAC addresses. Routers can also connect different Layer 2 technologies, such as Ethernet, Token-ring, and FDDI. However, because of their ability to route packets based on Layer 3 information, routers have become the backbone of the Int ...
CA Performance Management for Enterprises
... To help enterprise NOCs meet their challenges and align with their businesses’ priorities, CA Technologies offers CA Performance Management, a solution based on a modern architecture built for large, complex and growing network infrastructure. The centralized, multi-tiered/multi-threaded architectur ...
... To help enterprise NOCs meet their challenges and align with their businesses’ priorities, CA Technologies offers CA Performance Management, a solution based on a modern architecture built for large, complex and growing network infrastructure. The centralized, multi-tiered/multi-threaded architectur ...
Computer Networks BITS ZC481
... packets (Packet Switching) from one node to other towards destination host can be routers or switches. ...
... packets (Packet Switching) from one node to other towards destination host can be routers or switches. ...
Assignment3-LeonardEhalt
... • A Network Interface Card (NIC) is installed in your computer to connect, or interface, your computer to the network. • It provides the physical, electrical, and electronic connections to the network media. • A NIC either is an expansion card or is built right into the computer’s motherboard. • The ...
... • A Network Interface Card (NIC) is installed in your computer to connect, or interface, your computer to the network. • It provides the physical, electrical, and electronic connections to the network media. • A NIC either is an expansion card or is built right into the computer’s motherboard. • The ...
Kuliah Komunikasi Data
... defines the way in which computers, printers, and other devices are connected. A network topology describes the layout of the wire and devices as well as the paths used by data transmissions. ...
... defines the way in which computers, printers, and other devices are connected. A network topology describes the layout of the wire and devices as well as the paths used by data transmissions. ...
Lec_2
... A mesh offers several advantages over other network • topologies. First, the use of dedicated links guarantees that each connection can carry its own data load, thus eliminating the traffic problems that can occur when links must be shared by multiple devices. Second, a mesh topology is robust. If ...
... A mesh offers several advantages over other network • topologies. First, the use of dedicated links guarantees that each connection can carry its own data load, thus eliminating the traffic problems that can occur when links must be shared by multiple devices. Second, a mesh topology is robust. If ...
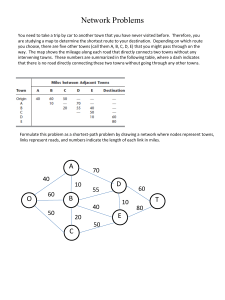
Hwk 5 Soln
... Network Problems You need to take a trip by car to another town that you have never visited before. Therefore, you are studying a map to determine the shortest route to your destination. Depending on which route you choose, there are five other towns (call them A, B, C, D, E) that you might pass thr ...
... Network Problems You need to take a trip by car to another town that you have never visited before. Therefore, you are studying a map to determine the shortest route to your destination. Depending on which route you choose, there are five other towns (call them A, B, C, D, E) that you might pass thr ...
TIA Test 2
... Actual data throughput is usually higher on wired networks than on wireless networks All computers have operating systems An operating system facilitates the communication between a device and its device driver Android 3.0 runs on laptops, desk-tops and all-in-ones Bandwidth is always greater than d ...
... Actual data throughput is usually higher on wired networks than on wireless networks All computers have operating systems An operating system facilitates the communication between a device and its device driver Android 3.0 runs on laptops, desk-tops and all-in-ones Bandwidth is always greater than d ...
vocab-network-poch-11
... PROTOCOL Protocol is the special set of rules that end points in a telecommunication connection use when they communicate. Protocols specify interactions between the communicating entities. ...
... PROTOCOL Protocol is the special set of rules that end points in a telecommunication connection use when they communicate. Protocols specify interactions between the communicating entities. ...
APP-G
... Automatic configuration to assign a dynamically allocated IP address Assignment may be temporary: Address “leased” to a client for a limited time. SENS supports DHCP client, server and relay agent operation ...
... Automatic configuration to assign a dynamically allocated IP address Assignment may be temporary: Address “leased” to a client for a limited time. SENS supports DHCP client, server and relay agent operation ...