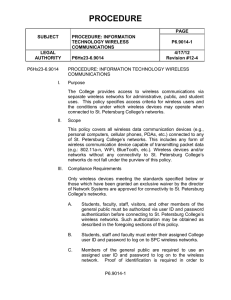
P6Hx23-6.9014 - St. Petersburg College
... The College’s Network Systems staff will scan the College network periodically for unauthorized wireless devices. Any such devices will be disconnected from the St. Petersburg College Network and/or impounded to a secure location pending an assessment of an incident by the campus provost or vice pre ...
... The College’s Network Systems staff will scan the College network periodically for unauthorized wireless devices. Any such devices will be disconnected from the St. Petersburg College Network and/or impounded to a secure location pending an assessment of an incident by the campus provost or vice pre ...
- Free Documents
... Communication and Networking Vol. Assess the robustness of the link between nodes. In most cases a wireless sensors network can be modelled as a unit graph G V. Connectivity Strategy In this section we will consider methods used for predicting the partitioning of the network. Theorem Menger. x. then ...
... Communication and Networking Vol. Assess the robustness of the link between nodes. In most cases a wireless sensors network can be modelled as a unit graph G V. Connectivity Strategy In this section we will consider methods used for predicting the partitioning of the network. Theorem Menger. x. then ...
Week10_2
... • When an IP packet arrives, the router checks its routing table to find the longest match. • Match means anding the IP address with the network address mask (1111…10000), and check if the result is the same as the network address. ...
... • When an IP packet arrives, the router checks its routing table to find the longest match. • Match means anding the IP address with the network address mask (1111…10000), and check if the result is the same as the network address. ...
network
... computers can be used in such case. One can also design a storage server on the network in order to have a huge storage capacity. Increased Cost Efficiency : There are many software's available in the market which are costly and take time for installation. Computer networks resolve this issue as the ...
... computers can be used in such case. One can also design a storage server on the network in order to have a huge storage capacity. Increased Cost Efficiency : There are many software's available in the market which are costly and take time for installation. Computer networks resolve this issue as the ...
Lecture 01
... Internetworking across multiple networks using routers Segmentation and reassembly of messages into packets at the ingress to and egress from a network or internetwork End-to-end transport protocols for process-to-process communications Applications that build on the transfer of messages between com ...
... Internetworking across multiple networks using routers Segmentation and reassembly of messages into packets at the ingress to and egress from a network or internetwork End-to-end transport protocols for process-to-process communications Applications that build on the transfer of messages between com ...
Text S1. Network analysis of sporulation sigma factor regulatory
... Given the importance of the conclusion that the expression data does not support a linear network topology we felt it appropriate to consider alternative statistical methods. This analysis is presented as supplementary material rather than in the main body because we did not want its technical natur ...
... Given the importance of the conclusion that the expression data does not support a linear network topology we felt it appropriate to consider alternative statistical methods. This analysis is presented as supplementary material rather than in the main body because we did not want its technical natur ...
topology - Meta-Knowledge Engineering and Management Server
... Development of a set of aggregated high level models… - Granular, as the observables can be studied at different scales/dimensions. ...
... Development of a set of aggregated high level models… - Granular, as the observables can be studied at different scales/dimensions. ...
cos440-Intro
... • May move frames from one network architecture to another This may involve addressing issues Physical addresses may vary between architectures Data frame sizes may vary between architectures ...
... • May move frames from one network architecture to another This may involve addressing issues Physical addresses may vary between architectures Data frame sizes may vary between architectures ...
Networks, Communities and Kronecker Products
... that they follow a range of properties also found in real networks: heavy tails for in- and out-degrees, clustering coefficient, powerlaw spectrum. They also densify and have shrinking diameter. One can interpret the diagonal values of the initiator matrix as the proportion of edges inside each of t ...
... that they follow a range of properties also found in real networks: heavy tails for in- and out-degrees, clustering coefficient, powerlaw spectrum. They also densify and have shrinking diameter. One can interpret the diagonal values of the initiator matrix as the proportion of edges inside each of t ...
Analysis of Active Measurements
... “Do measurement tools actually detect significant network events?” Goal-2: To analyze long-term network performance trends via statistical analysis of active and passive measurement data collected at strategic points on an ongoing basis “What can be understood from long-term network measurements?” G ...
... “Do measurement tools actually detect significant network events?” Goal-2: To analyze long-term network performance trends via statistical analysis of active and passive measurement data collected at strategic points on an ongoing basis “What can be understood from long-term network measurements?” G ...
Presentation Title
... • Only system to successfully deliver high-speed seamless hand-off along fixed wireless infrastructure • Real-time video streaming from station’s cameras to monitor on a train moving @50mph, with zero packet loss ...
... • Only system to successfully deliver high-speed seamless hand-off along fixed wireless infrastructure • Real-time video streaming from station’s cameras to monitor on a train moving @50mph, with zero packet loss ...
What are the Advantages and Disadvantages of a Policy
... loopback interface. At this stage, it was found through testing, the access switches could not ping the loopback but it could be pinged from the core switch. DESIRABLE FEATURES ...
... loopback interface. At this stage, it was found through testing, the access switches could not ping the loopback but it could be pinged from the core switch. DESIRABLE FEATURES ...
1. DIGISCENT 2. TYPES OF NETWORK 3. NETWORK
... straight from its origin to its proper destination, with no wandering in between. Switches remember the address of every node on the network, and anticipate where data needs to go. It only operates with the computers on the same LAN. It isn't smart enough to send data out to the internet, or across ...
... straight from its origin to its proper destination, with no wandering in between. Switches remember the address of every node on the network, and anticipate where data needs to go. It only operates with the computers on the same LAN. It isn't smart enough to send data out to the internet, or across ...
CIDR - TomBrett.ie
... • Each node on the same network must have a unique IP address. • Today, the most commonly used version of IP is IP version 4 (IPv4), • Its addresses are in such high demand that supply has started to run out. • IP version 6 (IPv6) was created to address this shortage. – (IPv6 also has many security ...
... • Each node on the same network must have a unique IP address. • Today, the most commonly used version of IP is IP version 4 (IPv4), • Its addresses are in such high demand that supply has started to run out. • IP version 6 (IPv6) was created to address this shortage. – (IPv6 also has many security ...
DBA 102:NOW WHAT
... Connection to storage via Host Bus Adapter Fibre channel dedicated hardware iSCSI over LAN Behaves more like on-board attached storage ...
... Connection to storage via Host Bus Adapter Fibre channel dedicated hardware iSCSI over LAN Behaves more like on-board attached storage ...
15-744: Computer Networking
... • Inspired many degree-based topology generators • Compared properties of generated graphs with those of measured graphs to validate generator • What is wrong with these topologies? Li et al [SIGCOMM04] • Many graphs with similar distribution have different properties • Random graph generation model ...
... • Inspired many degree-based topology generators • Compared properties of generated graphs with those of measured graphs to validate generator • What is wrong with these topologies? Li et al [SIGCOMM04] • Many graphs with similar distribution have different properties • Random graph generation model ...
Downlaod File
... A. There are four connection methods for transmission media: 1. Optical fiber: An optical fiber is used for communication in a single direction. STC uses the optical fiber when transmitting telephone. 2. Wired: waves are guided along a solid medium such as a transmission line. STC offered wired serv ...
... A. There are four connection methods for transmission media: 1. Optical fiber: An optical fiber is used for communication in a single direction. STC uses the optical fiber when transmitting telephone. 2. Wired: waves are guided along a solid medium such as a transmission line. STC offered wired serv ...
Topic Overview
... • If multiple processors access memory, bus will become saturated, thus long delays • A fairly large cache • Due to limited bandwidth of a bus, do not scale to large number of processors. ...
... • If multiple processors access memory, bus will become saturated, thus long delays • A fairly large cache • Due to limited bandwidth of a bus, do not scale to large number of processors. ...
Resume - Trelco Limited Company
... May 2001- Dec. 28th 2004-Technical Support Analyst – Sprint Corporation – Kansas City, M0. Responsible for troubleshooting over 2,500 applications within a global network consisting of 77,000 employees and 10,000 servers. The network was a combination of AD, NT, UNIX, Mainframe, Novell, and Windows ...
... May 2001- Dec. 28th 2004-Technical Support Analyst – Sprint Corporation – Kansas City, M0. Responsible for troubleshooting over 2,500 applications within a global network consisting of 77,000 employees and 10,000 servers. The network was a combination of AD, NT, UNIX, Mainframe, Novell, and Windows ...
Turkish lottery agents move to 3G wireless mobile
... SNMP network management, NTP support Local & remote firmware update Local & remote log check Supports DNS proxy and Dynamic DNS (DDNS) ...
... SNMP network management, NTP support Local & remote firmware update Local & remote log check Supports DNS proxy and Dynamic DNS (DDNS) ...
Yee-Ting Li
... Focusing actually implementing what the NMWG document says… and doesn’t say… Note: We are also tackling this from a pure OO design too – however, due to technical differences between objects in C++, Java and SOAP/XML then there may be issues to overcome… ...
... Focusing actually implementing what the NMWG document says… and doesn’t say… Note: We are also tackling this from a pure OO design too – however, due to technical differences between objects in C++, Java and SOAP/XML then there may be issues to overcome… ...
slides
... • Vision: Extreme DC network architecture – Fully Steerable, No core switches, All-wireless inter-rack ...
... • Vision: Extreme DC network architecture – Fully Steerable, No core switches, All-wireless inter-rack ...