New Network Topologies
... Each computer communicate with each other by a central HUB. So, hub provide a central connection point for all computers across a network. ...
... Each computer communicate with each other by a central HUB. So, hub provide a central connection point for all computers across a network. ...
Follow this link to Network
... compete. AnyLAN brings increased overall bandwidth (many users need to exchange a lot of information), brings individual increased bandwidth (an application exchanging very large amounts of information, e.g. database, imaging, desktop publishing applications or network printing) and allows time-sens ...
... compete. AnyLAN brings increased overall bandwidth (many users need to exchange a lot of information), brings individual increased bandwidth (an application exchanging very large amounts of information, e.g. database, imaging, desktop publishing applications or network printing) and allows time-sens ...
Week One
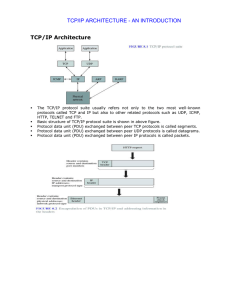
... • Dominant commercial protocol architecture • Specified and extensively used before OSI • Developed by research funded US Department of Defense • Used by the Internet ...
... • Dominant commercial protocol architecture • Specified and extensively used before OSI • Developed by research funded US Department of Defense • Used by the Internet ...
Text S1 Supplement Methods Construction of brain network
... corresponding regions. For each subject, a temporal correlation matrix ( N × N , where N 90 is the number of regions of interest) was obtained by computing the Pearson correlation coefficients between the processed time series of every pair of regions. In order to avoid loss of information, we con ...
... corresponding regions. For each subject, a temporal correlation matrix ( N × N , where N 90 is the number of regions of interest) was obtained by computing the Pearson correlation coefficients between the processed time series of every pair of regions. In order to avoid loss of information, we con ...
GPSR: Greedy Perimeter Stateless Routing for Wireless Networks
... voids in regions where edges of the graph cross. However, this algorithm doesn’t always find routes when they exist. The no-crossing heuristic blindly removes whichever edge it encounters second in a pair of crossing edges and by doing so can partition the network. If it does, the algorithm will not ...
... voids in regions where edges of the graph cross. However, this algorithm doesn’t always find routes when they exist. The no-crossing heuristic blindly removes whichever edge it encounters second in a pair of crossing edges and by doing so can partition the network. If it does, the algorithm will not ...
The Challenge in Developing an SCA Compliant Security
... software, radio parameter files Integrity of keys, software, files Transmission security to protect the communications channel Protection of network topology ...
... software, radio parameter files Integrity of keys, software, files Transmission security to protect the communications channel Protection of network topology ...
TCP/IP Support Protocols
... Network Time Protocol Clock synchronization across all network computers make() utility must have consistent times when directories are cross-mounted. Management of the system demands seeing when activities occur ...
... Network Time Protocol Clock synchronization across all network computers make() utility must have consistent times when directories are cross-mounted. Management of the system demands seeing when activities occur ...
William Stallings Data and Computer Communications
... Protocol Architecture • Framework about how a set of protocols work together to finish the communication task between source and destination • Three Protocol Architectures: - Three-Layer Model - TCP/IP Protocol Architecture - OSI Model ...
... Protocol Architecture • Framework about how a set of protocols work together to finish the communication task between source and destination • Three Protocol Architectures: - Three-Layer Model - TCP/IP Protocol Architecture - OSI Model ...
Review of Researches in Controller Area Networks Evolution and
... This paper presents a brief overview of CAN. This network is emerging and gaining high ground in many applications from automobile industry to automation and factory industries. CAN is a multi-master serial bus that allows an efficient transmission of data between different nodes. With its flexibili ...
... This paper presents a brief overview of CAN. This network is emerging and gaining high ground in many applications from automobile industry to automation and factory industries. CAN is a multi-master serial bus that allows an efficient transmission of data between different nodes. With its flexibili ...
The Network Management Problem
... A virtual circuit (switched, permanent, or soft) spanning one or more nodes A set of interfaces and links A set of locally significant labels used for addressing An optional route or designated transit list A bandwidth contract Traffic engineering settings QoS details ...
... A virtual circuit (switched, permanent, or soft) spanning one or more nodes A set of interfaces and links A set of locally significant labels used for addressing An optional route or designated transit list A bandwidth contract Traffic engineering settings QoS details ...
slides 1
... • Http (hyper-text transport protocol) sets up a connection – TCP connection (transmission control protocol) – between the host and cnn.com to transfer the page ...
... • Http (hyper-text transport protocol) sets up a connection – TCP connection (transmission control protocol) – between the host and cnn.com to transfer the page ...
Dynamic Network Selection for Robust Communications – Why Disruption Tolerance Matters
... Actually, a large amount of this potential is wasted. Users have to choose from the available communication systems by themselves and in general they are only connected to one access network at a time, not making use of the existing heterogeneity. Besides, most users will be overstrained in selectin ...
... Actually, a large amount of this potential is wasted. Users have to choose from the available communication systems by themselves and in general they are only connected to one access network at a time, not making use of the existing heterogeneity. Besides, most users will be overstrained in selectin ...
Tuesday, February 7, 2007 (Intro to the Network
... Ethernet switches are a type of bridge that have a many-to-one point-to-point relationship. Many low-bandwidth legs share a high-bandwidth common bus. Typically one leg, has a very high bandwidth – consider it to be the uplink. Imagine several floors or departments, each of which has its own leg, an ...
... Ethernet switches are a type of bridge that have a many-to-one point-to-point relationship. Many low-bandwidth legs share a high-bandwidth common bus. Typically one leg, has a very high bandwidth – consider it to be the uplink. Imagine several floors or departments, each of which has its own leg, an ...
IETF55 presentation on OSPF congestion control 11/21/02
... boxes need a few, critical, standard protocol mechanisms to address problem have gotten vendors to make proprietary changes to fix problem require standard protocol extensions – for uniform implementation – for multi-vendor interoperability user requirements need to drive solution to problem ...
... boxes need a few, critical, standard protocol mechanisms to address problem have gotten vendors to make proprietary changes to fix problem require standard protocol extensions – for uniform implementation – for multi-vendor interoperability user requirements need to drive solution to problem ...
industrial ethernet white paper
... first-served basis. This characteristic is called best-effort service. There is no differentiation between time critical data such as VoIP and other traffic on the network. To eliminate the best-effort problem, Quality of Service (QoS) tools can be used at points in the network to control the behavi ...
... first-served basis. This characteristic is called best-effort service. There is no differentiation between time critical data such as VoIP and other traffic on the network. To eliminate the best-effort problem, Quality of Service (QoS) tools can be used at points in the network to control the behavi ...
Tutorial 3 Selected Answers Question 13
... chunks to Alice in this same interval? Why or why not? It is not necessary that Bob will also provide chunks to Alice. Alice has to be in the top 4 neighbors of Bob for Bob to send out chunks to her; this might not occur even if Alice provides chunks to Bob throughout a 30second interval. ...
... chunks to Alice in this same interval? Why or why not? It is not necessary that Bob will also provide chunks to Alice. Alice has to be in the top 4 neighbors of Bob for Bob to send out chunks to her; this might not occur even if Alice provides chunks to Bob throughout a 30second interval. ...
IP_tec - iptel.org
... Moved from 4 sites in 1968 to around 200 M hosts today Flat addressing and routing architecture Based on packet switching (the) Internet: “collection of networks and routers that spans x countries and uses the TCP/IP protocols to form a single, cooperative virtual network”. (Comer) • intranet: conne ...
... Moved from 4 sites in 1968 to around 200 M hosts today Flat addressing and routing architecture Based on packet switching (the) Internet: “collection of networks and routers that spans x countries and uses the TCP/IP protocols to form a single, cooperative virtual network”. (Comer) • intranet: conne ...
MM_Introduction
... Moved from 4 sites in 1968 to around 200 M hosts today Flat addressing and routing architecture Based on packet switching (the) Internet: “collection of networks and routers that spans x countries and uses the TCP/IP protocols to form a single, cooperative virtual network”. (Comer) • intranet: conne ...
... Moved from 4 sites in 1968 to around 200 M hosts today Flat addressing and routing architecture Based on packet switching (the) Internet: “collection of networks and routers that spans x countries and uses the TCP/IP protocols to form a single, cooperative virtual network”. (Comer) • intranet: conne ...
TCP/IP Architecture TCP/IP ARCHITECTURE
... o First 24 bits identify NIC manufacturer; second 24 bits are serial number o 00:90:27:96:68:07 12 hex numbers ...
... o First 24 bits identify NIC manufacturer; second 24 bits are serial number o 00:90:27:96:68:07 12 hex numbers ...
Lecture 1: Course Introduction and Overview
... – Local Area Networks (Ethernet): 10-1000 nodes; ~ 1-2 kilometers – System/Storage Area Networks (FC-AL): 10-100s nodes; ~ 0.025 to 0.1 kilometers per link a.k.a. end systems, hosts ...
... – Local Area Networks (Ethernet): 10-1000 nodes; ~ 1-2 kilometers – System/Storage Area Networks (FC-AL): 10-100s nodes; ~ 0.025 to 0.1 kilometers per link a.k.a. end systems, hosts ...
Social-network-worksheet
... NodexL can automatically identify clusters based on the network structure. An algorithm will look for groups of densely clustered vertices that are only loosely connected to vertices in another cluster. The number of clusters is not predetermined; instead the algorithm dynamically determines t ...
... NodexL can automatically identify clusters based on the network structure. An algorithm will look for groups of densely clustered vertices that are only loosely connected to vertices in another cluster. The number of clusters is not predetermined; instead the algorithm dynamically determines t ...
Ethernet, IP and TCP
... on a host machine sends out a request on the LAN it is attached to. • A dhcp server will answer and lease an IP address to the host, sending it the network mask and the gateway address as well. • Internet providers work like that to save address space. • Problem: some services require IP addresses t ...
... on a host machine sends out a request on the LAN it is attached to. • A dhcp server will answer and lease an IP address to the host, sending it the network mask and the gateway address as well. • Internet providers work like that to save address space. • Problem: some services require IP addresses t ...
Networking
... Transport Layer (Contd….): Responsibilities of Transport Layer are as follows: Service Point Addressing. Segmentation and Reassembly. Connection Control. Flow Control. Error Control. ...
... Transport Layer (Contd….): Responsibilities of Transport Layer are as follows: Service Point Addressing. Segmentation and Reassembly. Connection Control. Flow Control. Error Control. ...