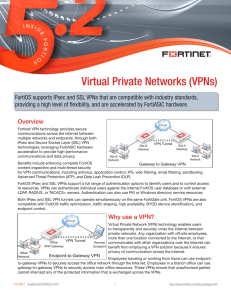
Virtual Private Networks (VPNs)
... the FortiOS SSL VPN web portal, and logging in. From the web portal, users can securely access resources on the protected network. The portal can also automatically install and invoke extended SSL VPN features, such as tunneling and virtual desktop protection, without user intervention or the need t ...
... the FortiOS SSL VPN web portal, and logging in. From the web portal, users can securely access resources on the protected network. The portal can also automatically install and invoke extended SSL VPN features, such as tunneling and virtual desktop protection, without user intervention or the need t ...
4.2 TCP Handoff implementation - The Linux Virtual Server Project
... the connection to user application. In Linux, for each packet, before it is copied to user buffer, it is placed in a kernel buffer, traverses the network stack, and a ‘sk_buff’ structure is allocated to record control information. Each protocol layer operates the packet through the ‘sk_buff’ structu ...
... the connection to user application. In Linux, for each packet, before it is copied to user buffer, it is placed in a kernel buffer, traverses the network stack, and a ‘sk_buff’ structure is allocated to record control information. Each protocol layer operates the packet through the ‘sk_buff’ structu ...
Slide presentation with simulation results - OSPF
... originates/floods a new LSA (with a larger sequence number) when the contents change (subject to MinLSInterval = 5 sec). OSPF allows multiple areas (clusters) for hierarchical routing. Each router in an area is provided with the full topology for the area, and Dijkstra’s algorithm is used to compute ...
... originates/floods a new LSA (with a larger sequence number) when the contents change (subject to MinLSInterval = 5 sec). OSPF allows multiple areas (clusters) for hierarchical routing. Each router in an area is provided with the full topology for the area, and Dijkstra’s algorithm is used to compute ...
J045055560
... project will consist of a number of performance and some performance can be started, only after ultimate some other behavior. There may be some behavior which is self-determining of others. Network analysis is a practice which determines the various sequences of behavior in relation to a project and ...
... project will consist of a number of performance and some performance can be started, only after ultimate some other behavior. There may be some behavior which is self-determining of others. Network analysis is a practice which determines the various sequences of behavior in relation to a project and ...
Basics of network lab - PolyU
... An IP address is a unique network layer numbering system that end systems use in order to identify and communicate with each other. It is a dotted decimal notation with four numbers ranging from 0 to 255 separated by periods. The numbers currently used in IP addresses range from 1.0.0.0 to 255. 255. ...
... An IP address is a unique network layer numbering system that end systems use in order to identify and communicate with each other. It is a dotted decimal notation with four numbers ranging from 0 to 255 separated by periods. The numbers currently used in IP addresses range from 1.0.0.0 to 255. 255. ...
IPV6 Essentials - AFCEA International
... • MTU - The Maximum Transmission Unit, or largest size ...
... • MTU - The Maximum Transmission Unit, or largest size ...
22101-660
... Technical Specification Group Services and System Aspects Service aspects; Service principles (Release 6) ...
... Technical Specification Group Services and System Aspects Service aspects; Service principles (Release 6) ...
DualAligner: a dual alignment-based strategy to align protein
... alignment. MI-GRAAL (Kuchaiev and Przulj, 2011) is an alignment framework that could integrate multiple similarity measures to construct a global alignment. Zaslavskiy et al. (2009) model global network alignment as a graph matching problem with hard constraints given by a set of must-link pairs of ...
... alignment. MI-GRAAL (Kuchaiev and Przulj, 2011) is an alignment framework that could integrate multiple similarity measures to construct a global alignment. Zaslavskiy et al. (2009) model global network alignment as a graph matching problem with hard constraints given by a set of must-link pairs of ...
Product Manual - KORE Telematics
... expressly approved by BlueTree Wireless Data, Inc. could void compliance with regulatory rules, and thereby your authority to use this equipment. This equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with the manufacturer's instructions, m ...
... expressly approved by BlueTree Wireless Data, Inc. could void compliance with regulatory rules, and thereby your authority to use this equipment. This equipment generates, uses and can radiate radio frequency energy and, if not installed and used in accordance with the manufacturer's instructions, m ...
Handbuch – Sunrise Internet Box
... which gives users broadband Internet access from their computer, tablet, smartphone or game console by various Ethernet (10, 100 or 1000 BASE-T) or Wi-Fi (IEEE 802.11n or 802.11ac) interfaces via an ADSL/ADSL2/ ADSL2+/VDSL2/G.Fast network. One Ethernet port of the Sunrise Internet Box is dedicated t ...
... which gives users broadband Internet access from their computer, tablet, smartphone or game console by various Ethernet (10, 100 or 1000 BASE-T) or Wi-Fi (IEEE 802.11n or 802.11ac) interfaces via an ADSL/ADSL2/ ADSL2+/VDSL2/G.Fast network. One Ethernet port of the Sunrise Internet Box is dedicated t ...
VINEA: A Policy-based Virtual Network Embedding Architecture
... matching such constrained virtual networks onto a physical network, owned by a single provider, or by multiple federated providers. In particular, we identify three interacting mechanisms in the embedding problem: resource discovery, virtual network mapping, and allocation. Resource discovery is the ...
... matching such constrained virtual networks onto a physical network, owned by a single provider, or by multiple federated providers. In particular, we identify three interacting mechanisms in the embedding problem: resource discovery, virtual network mapping, and allocation. Resource discovery is the ...
MEF Global Interconnect Briefing
... Pair failover capability ensures fiber service level agreements are met or exceeded ...
... Pair failover capability ensures fiber service level agreements are met or exceeded ...
Cisco 110 Series Unmanaged Switches Data Sheet
... Give your office network a boost of speed and performance at a low price that takes almost no time to set up. Easily build a highly reliable network to connect your computers, printers, copiers, and other office equipment. If your business is like most small companies, you do not have an IT staff to ...
... Give your office network a boost of speed and performance at a low price that takes almost no time to set up. Easily build a highly reliable network to connect your computers, printers, copiers, and other office equipment. If your business is like most small companies, you do not have an IT staff to ...
投影片 1
... net.link.ether.bridge_cfg: ed2:1,rl0:1 Set of interfaces for which bridging is enabled, and cluster they belong to net.link.ether.bridge: 0 Enable bridging net.link.ether.bridge_ipfw: 0 Enable ipfw for bridging ...
... net.link.ether.bridge_cfg: ed2:1,rl0:1 Set of interfaces for which bridging is enabled, and cluster they belong to net.link.ether.bridge: 0 Enable bridging net.link.ether.bridge_ipfw: 0 Enable ipfw for bridging ...
5 Requirements - ISO/IEC JTC 1/SC 25/WG 1 Home Page
... ISO/IEC 15045-1 (part 1) specifies the functional requirements and basic architecture for the residential gateway. This part, ISO/IEC 15045-2 (part 2), specifies a residential gateway modular structure and an internal protocol and language that may be used to implement a conforming gateway system fo ...
... ISO/IEC 15045-1 (part 1) specifies the functional requirements and basic architecture for the residential gateway. This part, ISO/IEC 15045-2 (part 2), specifies a residential gateway modular structure and an internal protocol and language that may be used to implement a conforming gateway system fo ...
Probability Model Based Energy Efficient and Reliable
... Wireless sensor networks (WSNs) have become more and more widely used and important in recent years. The properties of WSNs—which contain hundreds or thousands of sensors—are limited by the energy, the bandwidth, the capability of computing, etc. Moreover, in most applications, the WSNs are arranged ...
... Wireless sensor networks (WSNs) have become more and more widely used and important in recent years. The properties of WSNs—which contain hundreds or thousands of sensors—are limited by the energy, the bandwidth, the capability of computing, etc. Moreover, in most applications, the WSNs are arranged ...
IOSR Journal of Electronics and Communication Engineering (IOSR-JECE)
... Using HSRP, a set of routers work in concert to present the illusion of a single virtual router to the hosts on the LAN. This set is known as an HSRP group or a standby group. A single router elected from the group is responsible for forwarding the packets that hosts send to the virtual router. This ...
... Using HSRP, a set of routers work in concert to present the illusion of a single virtual router to the hosts on the LAN. This set is known as an HSRP group or a standby group. A single router elected from the group is responsible for forwarding the packets that hosts send to the virtual router. This ...
Internet Control Message Protocol
... More about Message Types The DESTINATION UNREACHABLE message is used when the subnet or a router cannot locate the destination. The TIME EXCEEDED message is sent when a packet is dropped because its counter has reached zero. This event is symptom that packets are looping, that there is enormous c ...
... More about Message Types The DESTINATION UNREACHABLE message is used when the subnet or a router cannot locate the destination. The TIME EXCEEDED message is sent when a packet is dropped because its counter has reached zero. This event is symptom that packets are looping, that there is enormous c ...
Network Training 2008-05-25
... Managed switching (the heart of a managed network) has been around for a long time, and as with everything to do with computers, has become much more affordable. One of the best things (among many other fun stuff) about a managed switch is that you can create “Virtual Local Area Networks” or VLANs. ...
... Managed switching (the heart of a managed network) has been around for a long time, and as with everything to do with computers, has become much more affordable. One of the best things (among many other fun stuff) about a managed switch is that you can create “Virtual Local Area Networks” or VLANs. ...
ORiNOCO 802.11a/b/g/n USB Adapter
... 802.11n wireless products as well as legacy products. The ORiNOCO® 11n USB Adapter can be used with other 802.11n devices to form a stand-alone wireless Peer-to-Peer Group or used in conjunction with an Access Point infrastructure to provide mobile clients with wireless access. ...
... 802.11n wireless products as well as legacy products. The ORiNOCO® 11n USB Adapter can be used with other 802.11n devices to form a stand-alone wireless Peer-to-Peer Group or used in conjunction with an Access Point infrastructure to provide mobile clients with wireless access. ...
On Supporting Mobility and Multihoming in Recursive Internet
... If an application process in RINA needs to communicate with another application process, it requests service from the underlying Distributed IPC Facility (DIF). This DIF maps the destination application name to a node (process) address. A DIF in RINA can (recursively) provide transport services betw ...
... If an application process in RINA needs to communicate with another application process, it requests service from the underlying Distributed IPC Facility (DIF). This DIF maps the destination application name to a node (process) address. A DIF in RINA can (recursively) provide transport services betw ...
Congestion Control Without a Startup Phase
... distributed with an average size of 50 msec. The time interval between web sessions is set to 5 msec. Figure 4 shows the distribution of connection duration and per-connection drop rates for the Web traffic experiments. Similar to the scoping employed above, these plots are winnowed to connections t ...
... distributed with an average size of 50 msec. The time interval between web sessions is set to 5 msec. Figure 4 shows the distribution of connection duration and per-connection drop rates for the Web traffic experiments. Similar to the scoping employed above, these plots are winnowed to connections t ...