Dynamic addressing
... • When the Internet was small, mapping was done using a host file • Today is impossible to have a single host file to relate every address to a name and vice versa. The host file would be too large to store in every host • One solution is to store the entire host file in a single computer and allow ...
... • When the Internet was small, mapping was done using a host file • Today is impossible to have a single host file to relate every address to a name and vice versa. The host file would be too large to store in every host • One solution is to store the entire host file in a single computer and allow ...
Patch Management Integration November 11, 2014 (Revision 20)
... scans, or scan with credentials for more accurate results with less network bandwidth utilization. Nessus and SecurityCenter now leverage credentials for the Red Hat Network Satellite, IBM TEM (formerly BigFix), Dell KACE 1000, and Microsoft WSUS and SCCM patch management systems to perform patch au ...
... scans, or scan with credentials for more accurate results with less network bandwidth utilization. Nessus and SecurityCenter now leverage credentials for the Red Hat Network Satellite, IBM TEM (formerly BigFix), Dell KACE 1000, and Microsoft WSUS and SCCM patch management systems to perform patch au ...
Slide 1
... groups or users can be billed correctly for snarfing up resources – Yes, it’s all about money – Data can be collected using various tools, such as NetFlow, IP Accounting, Evident Software ...
... groups or users can be billed correctly for snarfing up resources – Yes, it’s all about money – Data can be collected using various tools, such as NetFlow, IP Accounting, Evident Software ...
CCNA 2 FINAL 2012 EXAM – V1 Mục lục: giữ nút CTRL sau đó click
... and are running the OSPF routing protocol. The network is fully converged. A host on the 192.168.3.0/24 network is communicating with a host on the 192.168.2.0/24 network.Which path will be used to transmit the data? The data will be transmitted via R3-R2. The data will be transmitted via R3-R1-R2. ...
... and are running the OSPF routing protocol. The network is fully converged. A host on the 192.168.3.0/24 network is communicating with a host on the 192.168.2.0/24 network.Which path will be used to transmit the data? The data will be transmitted via R3-R2. The data will be transmitted via R3-R1-R2. ...
Mobile Internet charging: prepaid vs. postpaid
... – Resource Registry. Listing of available information source. – Local Service Container. Information collection and analysis entities located within the platform. – Remote Source Container. Offers facilities to hook-in external and legacy information sources to the platform. – Container Services. Su ...
... – Resource Registry. Listing of available information source. – Local Service Container. Information collection and analysis entities located within the platform. – Remote Source Container. Offers facilities to hook-in external and legacy information sources to the platform. – Container Services. Su ...
start slide: headline arial bold 38 pt, 0 pt leading
... – CCA from PHY and Virtual Carrier Sense state. Direct access when medium is sensed free longer then DIFS, otherwise defer and backoff. Receiver of directed frames to return an ACK immediately when CRC correct. – When no ACK received then retransmit frame after a ...
... – CCA from PHY and Virtual Carrier Sense state. Direct access when medium is sensed free longer then DIFS, otherwise defer and backoff. Receiver of directed frames to return an ACK immediately when CRC correct. – When no ACK received then retransmit frame after a ...
Secure routing for structured peer-to-peer overlay networks
... Structured peer-to-peer overlay networks provide a substrate for the construction of large-scale, decentralized applications, including distributed storage, group communication, and content distribution. These overlays are highly resilient; they can route messages correctly even when a large fractio ...
... Structured peer-to-peer overlay networks provide a substrate for the construction of large-scale, decentralized applications, including distributed storage, group communication, and content distribution. These overlays are highly resilient; they can route messages correctly even when a large fractio ...
Executive Summary
... have experienced by travelling to a Cisco Media Network studio. Reduced production costs. Using the Cisco intranet for the event eliminated the need to procure and provision satellite connections, saving approximately US$25,000. Revenue protection. Cisco’s immediate response to a direct competitive ...
... have experienced by travelling to a Cisco Media Network studio. Reduced production costs. Using the Cisco intranet for the event eliminated the need to procure and provision satellite connections, saving approximately US$25,000. Revenue protection. Cisco’s immediate response to a direct competitive ...
DSL-G624T Wireless ADSL Router User Guide
... will be stored in its memory. For some users, only their account information (Username and Password) is required. For others, various parameters that control and define the Internet connection will be required. You can print out the two pages below and use the tables to list this information. This w ...
... will be stored in its memory. For some users, only their account information (Username and Password) is required. For others, various parameters that control and define the Internet connection will be required. You can print out the two pages below and use the tables to list this information. This w ...
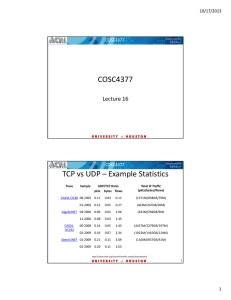
COSC4377 TCP vs UDP – Example Statistics
... growth ia coming from major ISPs within the U.S., as they roll out production IPv6 support to their end‐users, including Verizon Wireless, AT&T, and Comcast. This is on top of some ISPs in Europe and Asia that have had IPv6 deployed in production for a few years, as well as a long tail of thousan ...
... growth ia coming from major ISPs within the U.S., as they roll out production IPv6 support to their end‐users, including Verizon Wireless, AT&T, and Comcast. This is on top of some ISPs in Europe and Asia that have had IPv6 deployed in production for a few years, as well as a long tail of thousan ...
TD-W8951ND 150Mbps Wireless N ADSL2+ Modem Router Rev: 3.0.1
... any other antenna or transmitter. “To comply with FCC RF exposure compliance requirements, this grant is applicable to only Mobile Configurations. The antennas used for this transmitter must be installed to provide a separation distance of at least 20 cm from all persons and must not be co-located o ...
... any other antenna or transmitter. “To comply with FCC RF exposure compliance requirements, this grant is applicable to only Mobile Configurations. The antennas used for this transmitter must be installed to provide a separation distance of at least 20 cm from all persons and must not be co-located o ...
QU-RPL: Queue Utilization based RPL for Load
... herding effect by always removing the congested parent from the parent candidate set. More importantly, both of these work evaluated their proposed schemes using NS-2 simulations, and neither conduct experiments in a real LLN nor implement their schemes on real embedded devices. III. S YSTEM MODEL C ...
... herding effect by always removing the congested parent from the parent candidate set. More importantly, both of these work evaluated their proposed schemes using NS-2 simulations, and neither conduct experiments in a real LLN nor implement their schemes on real embedded devices. III. S YSTEM MODEL C ...
Slide 1
... Neighbor routers will process the updates. What will other devices on that link do if they receive a routing update but are not running that routing protocol including hosts? They will process the update up to Layer 3 (Multicast update) or Layer 4 (Broadcast update) before discarding it. ...
... Neighbor routers will process the updates. What will other devices on that link do if they receive a routing update but are not running that routing protocol including hosts? They will process the update up to Layer 3 (Multicast update) or Layer 4 (Broadcast update) before discarding it. ...
Chapter 3 Accessing the GV
... output live images and recognition results immediately. When the unit is installed at the place where the Internet is not accessible, the TV-Out port can be used for camera adjustment to make sure the image of license plate is captured properly. Select the frame rate and text overlay. The default se ...
... output live images and recognition results immediately. When the unit is installed at the place where the Internet is not accessible, the TV-Out port can be used for camera adjustment to make sure the image of license plate is captured properly. Select the frame rate and text overlay. The default se ...
abstract - Douglas Reeves
... desired content in the network. Then, after having discovered a servent sharing the above content, it establishes a direct connection and transfers the resource from the provider. Peer-to-peer networks can be broadly classified into two categories: 1. Centralized networks such as Napster, 2. Decentr ...
... desired content in the network. Then, after having discovered a servent sharing the above content, it establishes a direct connection and transfers the resource from the provider. Peer-to-peer networks can be broadly classified into two categories: 1. Centralized networks such as Napster, 2. Decentr ...
Slides
... Websites(including Top100 commercial websites, government’s websites) are gradually upgraded to support IPv6 ...
... Websites(including Top100 commercial websites, government’s websites) are gradually upgraded to support IPv6 ...
Chapter 27 PPT
... Router R1 knows about networks 1 and 3 Router R1 does not know about network 2 (no direct connection) Router R2 knows about networks 2 and 3 Router R2 does not know about network 1 (no direct connection) ...
... Router R1 knows about networks 1 and 3 Router R1 does not know about network 2 (no direct connection) Router R2 knows about networks 2 and 3 Router R2 does not know about network 1 (no direct connection) ...
Chapter 1 - Introduction
... Router R1 knows about networks 1 and 3 Router R1 does not know about network 2 (no direct connection) Router R2 knows about networks 2 and 3 Router R2 does not know about network 1 (no direct connection) ...
... Router R1 knows about networks 1 and 3 Router R1 does not know about network 2 (no direct connection) Router R2 knows about networks 2 and 3 Router R2 does not know about network 1 (no direct connection) ...
TD-W8961NB 300Mbps Wireless N ADSL2+ Modem Router - TP-Link
... any other antenna or transmitter. “To comply with FCC RF exposure compliance requirements, this grant is applicable to only Mobile Configurations. The antennas used for this transmitter must be installed to provide a separation distance of at least 20 cm from all persons and must not be co-located o ...
... any other antenna or transmitter. “To comply with FCC RF exposure compliance requirements, this grant is applicable to only Mobile Configurations. The antennas used for this transmitter must be installed to provide a separation distance of at least 20 cm from all persons and must not be co-located o ...