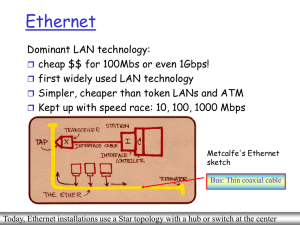
Ethernet Switches
... operating at bit levels: repeat received bits on one interface to all other interfaces Hubs can be arranged in a hierarchy (or multi-tier design), with backbone hub at its top ...
... operating at bit levels: repeat received bits on one interface to all other interfaces Hubs can be arranged in a hierarchy (or multi-tier design), with backbone hub at its top ...
Split-TCP for Mobile Ad Hoc Networks
... We want to choose solutions which maintain close connection to TCP Upper layers in the OSI model affected by choice of transport layer protocol Modifications may affect interactions with the Internet Alternative methods only useful for isolated networks ...
... We want to choose solutions which maintain close connection to TCP Upper layers in the OSI model affected by choice of transport layer protocol Modifications may affect interactions with the Internet Alternative methods only useful for isolated networks ...
ppt - Northwestern Networks Group
... Finding a feasible path using Dijkstra’s algorithm is NP-Complete Randomized and approximation algorithms Single composite metric derived from multiple metrics Paths might not meet individual QoS constraints ...
... Finding a feasible path using Dijkstra’s algorithm is NP-Complete Randomized and approximation algorithms Single composite metric derived from multiple metrics Paths might not meet individual QoS constraints ...
AirLink Raven XE - Sierra Wireless Source
... Do not operate the Sierra Wireless AirLink Raven XE in areas where blasting is in progress, where explosive atmospheres may be present, near medical equipment, near life support equipment, or any equipment which may be susceptible to any form of radio interference. In such areas, the Sierra Wireless ...
... Do not operate the Sierra Wireless AirLink Raven XE in areas where blasting is in progress, where explosive atmospheres may be present, near medical equipment, near life support equipment, or any equipment which may be susceptible to any form of radio interference. In such areas, the Sierra Wireless ...
Glossary for Fundamentals of Network Security
... electromagnetic interference (EMI)—A degradation to networked message traffic caused by electrical signals radiating outward as the traffic travels through wires. (Chapter 2) e-mail—An electronic means of communicating that is similar to mail but written using computer applications and sent over net ...
... electromagnetic interference (EMI)—A degradation to networked message traffic caused by electrical signals radiating outward as the traffic travels through wires. (Chapter 2) e-mail—An electronic means of communicating that is similar to mail but written using computer applications and sent over net ...
Chapter 5 Advanced Configuration
... to recognize some of these applications and to work properly with them, but there are other applications that may not function well. In some cases, one local computer can run the application properly if that computer’s IP address is entered as the default DMZ server. Incoming traffic from the Intern ...
... to recognize some of these applications and to work properly with them, but there are other applications that may not function well. In some cases, one local computer can run the application properly if that computer’s IP address is entered as the default DMZ server. Incoming traffic from the Intern ...
Broadband Reference Guide
... Despite new technology and learning tools, effective learning continues to be about content, curricula, and the most effective methods used to teach children or adults. Online classes and learning opportunities are being offered more frequently and provide access to advanced information geared towar ...
... Despite new technology and learning tools, effective learning continues to be about content, curricula, and the most effective methods used to teach children or adults. Online classes and learning opportunities are being offered more frequently and provide access to advanced information geared towar ...
The Tenet Architecture for Tiered Sensor Networks
... view of sensor networking, the principle constrains the processing of data received from multiple sensors to be placed at the master tier, regardless of whether that processing is specific to an application or can be expressed as a generic fusion service. (It might, for example, be possible to cast ...
... view of sensor networking, the principle constrains the processing of data received from multiple sensors to be placed at the master tier, regardless of whether that processing is specific to an application or can be expressed as a generic fusion service. (It might, for example, be possible to cast ...
Chord: A Scalable Peer-to-peer Lookup Service for Internet
... be used to find data objects that are not tied to particular machines. The Freenet peer-to-peer storage system [4, 5], like Chord, is decentralized and symmetric and automatically adapts when hosts leave and join. Freenet does not assign responsibility for documents to specific servers; instead, its ...
... be used to find data objects that are not tied to particular machines. The Freenet peer-to-peer storage system [4, 5], like Chord, is decentralized and symmetric and automatically adapts when hosts leave and join. Freenet does not assign responsibility for documents to specific servers; instead, its ...
SCCP user adaptation layer(SUA)
... SUA has better knowledge of the underlying network than SCCP on top of M3UA, I.e. the Routing Contexts can be more fine-tuned. Management should be simpler as only one layer (SUA ASP management) has to be administered versus 2 (M3UA ASP management + SCCP management). Can use extended addressing capa ...
... SUA has better knowledge of the underlying network than SCCP on top of M3UA, I.e. the Routing Contexts can be more fine-tuned. Management should be simpler as only one layer (SUA ASP management) has to be administered versus 2 (M3UA ASP management + SCCP management). Can use extended addressing capa ...
Manual
... This full rate Wireless ADSL2+ router is an all-in-one gateway for Home and SOHO applications. This gateway is with full-featured ADSL router that provides high-speed Internet access, 4-port Ethernet switch direct connections to individual PCs or local area network with 10/100 Base-T Ethernet and 54 ...
... This full rate Wireless ADSL2+ router is an all-in-one gateway for Home and SOHO applications. This gateway is with full-featured ADSL router that provides high-speed Internet access, 4-port Ethernet switch direct connections to individual PCs or local area network with 10/100 Base-T Ethernet and 54 ...
... Skype can go through port-restricted NAT directly with the help of relay nodes to start connections. When Skype goes across a UDP-restricted NAT, one of the super nodes will help relay voice packets via a TCP session. In MSN, when the client behind a firewall wants to set up a voice connection, the ...
Connection-oriented internetworking
... • Examples: MPLS switch with PoS link and GbE link. For the PoS link, LSP encoding should be SONET while switching type: PSC-1 and for the GbE link, LSP encoding should be Ethernet and switching type: PSC-1. Vijay says that MPLS specs don’t allow this sort of LSP to be set up. Both switching and LSP ...
... • Examples: MPLS switch with PoS link and GbE link. For the PoS link, LSP encoding should be SONET while switching type: PSC-1 and for the GbE link, LSP encoding should be Ethernet and switching type: PSC-1. Vijay says that MPLS specs don’t allow this sort of LSP to be set up. Both switching and LSP ...
Packet Tracer Network Simulator
... network topologies, and configuring them with Cisco commands. After testing the connectivity with complex PDUs, users will also use the simulation mode to analyze the packet flow. Chapter 5, Navigating and Modifying the Physical Workspace, introduces the physical workspace in Packet Tracer. After re ...
... network topologies, and configuring them with Cisco commands. After testing the connectivity with complex PDUs, users will also use the simulation mode to analyze the packet flow. Chapter 5, Navigating and Modifying the Physical Workspace, introduces the physical workspace in Packet Tracer. After re ...
File - Advanced Wireless
... access network interface. Service may accommodate special routing access requests by the Customer and/or by ADVANCED WIRELESS. 1.2 DIA Equipment and Maintenance: Service must terminate into a ADVANCED WIRELESS approved router on the customer premises (CPE). A CPE router is required for the exchange ...
... access network interface. Service may accommodate special routing access requests by the Customer and/or by ADVANCED WIRELESS. 1.2 DIA Equipment and Maintenance: Service must terminate into a ADVANCED WIRELESS approved router on the customer premises (CPE). A CPE router is required for the exchange ...
CLOUDBAND WITH OPENSTACK AS NFV PLATFORM
... • The ability to manage high performance data plane network functions on commercial off-the-shelf servers It is likely that OpenStack’s support of at least some of these requirements will improve over time. In some areas, however, it is unclear if that will ever happen. The OpenStack community is d ...
... • The ability to manage high performance data plane network functions on commercial off-the-shelf servers It is likely that OpenStack’s support of at least some of these requirements will improve over time. In some areas, however, it is unclear if that will ever happen. The OpenStack community is d ...
Network and Service Discovery in Distributed Environments
... a) employing converters b) employing photonic switches ...
... a) employing converters b) employing photonic switches ...
Registration Steps
... Billing information (past credit, current charges, chronological (依年代順序) order of calls made, timings of each call) ...
... Billing information (past credit, current charges, chronological (依年代順序) order of calls made, timings of each call) ...
TCP, IGP, EGP etc. - La Salle University
... tables within an autonomous system. It is based on the “shortest path first” or “link-state” algorithm. Routers do not send tables, instead they send information about their nearest neighbors and the cost thereto. The shortest path to each node is then calculated (e.g. using Dijkstra’s algorithm). ...
... tables within an autonomous system. It is based on the “shortest path first” or “link-state” algorithm. Routers do not send tables, instead they send information about their nearest neighbors and the cost thereto. The shortest path to each node is then calculated (e.g. using Dijkstra’s algorithm). ...
Networking 101
... Physical location of ISP’s equipment Sometimes called a “node” To the end user, it looks like an ISP location In reality a back hauled access point Used mainly for consumer access networks ...
... Physical location of ISP’s equipment Sometimes called a “node” To the end user, it looks like an ISP location In reality a back hauled access point Used mainly for consumer access networks ...
IP Addressing - Austin Community College
... • IPv6 addresses are expressed as hexadecimal numbers – Example: 3FFE:0501:0008:0000:0260:97FF:FE40:EFAB ...
... • IPv6 addresses are expressed as hexadecimal numbers – Example: 3FFE:0501:0008:0000:0260:97FF:FE40:EFAB ...
NOTI-FIRE-NEt
... The network architecture shall be based on a Local Area Network (LAN), a firmware package that utilizes a peer-to-peer, inherently regenerative communication format and protocol. The protocol shall be based on ARCNET or equivalent. The network shall use a deterministic token-passing method. Collisio ...
... The network architecture shall be based on a Local Area Network (LAN), a firmware package that utilizes a peer-to-peer, inherently regenerative communication format and protocol. The protocol shall be based on ARCNET or equivalent. The network shall use a deterministic token-passing method. Collisio ...
Powerpoint
... • routers compute routing tables dynamically based on information provided by other routers in the network • routers communicate topology to each other via different protocols • routers then compute one or more next hops for each destination - trying to calculate the most optimal path ...
... • routers compute routing tables dynamically based on information provided by other routers in the network • routers communicate topology to each other via different protocols • routers then compute one or more next hops for each destination - trying to calculate the most optimal path ...