The 2016 SNIA Dictionary
... In the case that more text is required or deemed helpful, it is contained in one or more separate paragraphs after the definition itself. This text is informative in nature, and while intended to be accurate, is not technically part of the definition itself. ...
... In the case that more text is required or deemed helpful, it is contained in one or more separate paragraphs after the definition itself. This text is informative in nature, and while intended to be accurate, is not technically part of the definition itself. ...
Wireless Cable Voice Gateway CG3000/CG3100 User
... (2) this device must accept any interference received, including interference that may cause undesired operation. This equipment has been tested and found to comply with the limits for a class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable pro ...
... (2) this device must accept any interference received, including interference that may cause undesired operation. This equipment has been tested and found to comply with the limits for a class B digital device, pursuant to part 15 of the FCC Rules. These limits are designed to provide reasonable pro ...
NETGEAR Wireless Router Setup Manual
... Network, Routing, and Firewall Basics Related Publications ...................................................................................................... B-1 Basic Router Concepts .................................................................................................. B-1 What is a ...
... Network, Routing, and Firewall Basics Related Publications ...................................................................................................... B-1 Basic Router Concepts .................................................................................................. B-1 What is a ...
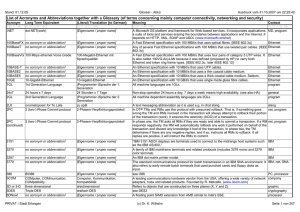
List of Acronyms and Abbreviations together with a Glossary (of
... has blended the support for NetBIOS, DNS, and LDAP namespaces, and integrated Windows 2000 domain security. Andorra The country code TLD and the ISO 3166-1 alpha-2 code for this country. [Eigenname / proper name] A complex, Pascal-descended, high-level programming language developed for the US DoD. ...
... has blended the support for NetBIOS, DNS, and LDAP namespaces, and integrated Windows 2000 domain security. Andorra The country code TLD and the ISO 3166-1 alpha-2 code for this country. [Eigenname / proper name] A complex, Pascal-descended, high-level programming language developed for the US DoD. ...
SonicWALL TZ 170 Getting Started Guide Page 7
... • Is your computer running pop-up blocking software? • Are the Local Area Connection settings on your computer set to obtain an IP address dynamically (DHCP) or set to a static IP of 192.168.168.20? See “Configuring Computers for Your Network with DHCP” on page 20 for instructions on changing your L ...
... • Is your computer running pop-up blocking software? • Are the Local Area Connection settings on your computer set to obtain an IP address dynamically (DHCP) or set to a static IP of 192.168.168.20? See “Configuring Computers for Your Network with DHCP” on page 20 for instructions on changing your L ...
Reference - Network Security Administrator/Specialist
... malicious code, unveiling corporate spyware, and extracting application vulnerabilities, but until this book it has received sparse coverage in the printed literature. This book is not married to a particular operating system, since many of you are responsible for protecting mixed networks. We have ...
... malicious code, unveiling corporate spyware, and extracting application vulnerabilities, but until this book it has received sparse coverage in the printed literature. This book is not married to a particular operating system, since many of you are responsible for protecting mixed networks. We have ...
Access your control systems via the Internet
... simply by pointing and clicking in a web page. You can even open your curtains, switch your pool filter or sprinkler system to water the garden. Power circuits controlling pumps, motors hot water systems etc. can be remotely switched. ...
... simply by pointing and clicking in a web page. You can even open your curtains, switch your pool filter or sprinkler system to water the garden. Power circuits controlling pumps, motors hot water systems etc. can be remotely switched. ...
A Review of Recent Trends and Issues in Visualization
... items of probable value, and helps in restructuring the evidence and setting up relationship between them[4041]. Haggerty [140] presents E-mail Extraction Tool (EET) that is helpful for displaying the client-based emails and exploring the social networks. B. Visualization in Network Security Network ...
... items of probable value, and helps in restructuring the evidence and setting up relationship between them[4041]. Haggerty [140] presents E-mail Extraction Tool (EET) that is helpful for displaying the client-based emails and exploring the social networks. B. Visualization in Network Security Network ...
Firewall/VPN PDF
... With the proliferation of bring your own devices (BYOD), companies must find a way to accommodate employees who use their personal phones and tablets for both work and personal use. One method is to maintain a separate WiFi for BYOD use. The WiFi network might be seen by the Web Security Service as ...
... With the proliferation of bring your own devices (BYOD), companies must find a way to accommodate employees who use their personal phones and tablets for both work and personal use. One method is to maintain a separate WiFi for BYOD use. The WiFi network might be seen by the Web Security Service as ...
Sample Title Slide Standard Template
... • Symantec Advanced Threat Research (ATR) conducted a project looking at “network attack surface” of Vista • We examined the security-relevant aspects of Vista, from the point of view of the network • Huge potential scope, actual scope was defined by time ...
... • Symantec Advanced Threat Research (ATR) conducted a project looking at “network attack surface” of Vista • We examined the security-relevant aspects of Vista, from the point of view of the network • Huge potential scope, actual scope was defined by time ...
KillerBee: Practical ZigBee Exploitation Framework or "Hacking the
... • Nature of ZigBee and IEEE 802.15.4 networks is to have lots of small, distributed devices • Unless OTA key delivery is used, all devices must have key stored in flash • When device boots, key is moved to RAM • Leverage device to retrieve encryption key, access network or decrypt all traffic This i ...
... • Nature of ZigBee and IEEE 802.15.4 networks is to have lots of small, distributed devices • Unless OTA key delivery is used, all devices must have key stored in flash • When device boots, key is moved to RAM • Leverage device to retrieve encryption key, access network or decrypt all traffic This i ...
SpeedStream Router
... The following describes your license to use the software (the “Software”) that has been provided with your SSN DSL customer premises equipment (“Hardware”) and the limited warranty that SSN provides on its Software and Hardware. Software License The Software is protected by copyright laws and intern ...
... The following describes your license to use the software (the “Software”) that has been provided with your SSN DSL customer premises equipment (“Hardware”) and the limited warranty that SSN provides on its Software and Hardware. Software License The Software is protected by copyright laws and intern ...
HMC 840 Connectivity Security White Paper
... For Power remote service over a modem, the modem must be set up to accept incoming phone calls. An IBM representative then logs into a special server and uses that to dial directly into the client's modem. After the modem answers, a PPP session is initiated, and the IBM representative must authentic ...
... For Power remote service over a modem, the modem must be set up to accept incoming phone calls. An IBM representative then logs into a special server and uses that to dial directly into the client's modem. After the modem answers, a PPP session is initiated, and the IBM representative must authentic ...
Virtual Private Networks (VPNs)
... functions to create private communication channels over the Internet. They also define and deploy network access and firewall policies using a single management tool. Furthermore, both technologies support a simple client/user authentication process. While you have the freedom to use either VPN tech ...
... functions to create private communication channels over the Internet. They also define and deploy network access and firewall policies using a single management tool. Furthermore, both technologies support a simple client/user authentication process. While you have the freedom to use either VPN tech ...
PDF
... SoBGP speakers can confirm the feasibility of a path even if that path has non-soBGP speakers on it. The soBGP speakers immediately before and after a nonsoBGP speaker can verify that they each have a peering relationship with the non-soBGP speaker, which would make an UPDATE path through the non-so ...
... SoBGP speakers can confirm the feasibility of a path even if that path has non-soBGP speakers on it. The soBGP speakers immediately before and after a nonsoBGP speaker can verify that they each have a peering relationship with the non-soBGP speaker, which would make an UPDATE path through the non-so ...
Valet and Valet Plus User Guide
... only; it does not provide access to your local network and its resources or your personal information. For example, the guest computer cannot print to a printer on the local network or access files on a computer on the local network. Guest access helps minimize exposure of your local network and you ...
... only; it does not provide access to your local network and its resources or your personal information. For example, the guest computer cannot print to a printer on the local network or access files on a computer on the local network. Guest access helps minimize exposure of your local network and you ...
Successfully Implementing the Information System
... Wireless Local Area Network (WLAN) (Continued) • Concerns • Security • Signal integrity • WEP has many flaws, but used in conjunction with traditional LAN security measures is thought to be adequate for many home and business purposes ...
... Wireless Local Area Network (WLAN) (Continued) • Concerns • Security • Signal integrity • WEP has many flaws, but used in conjunction with traditional LAN security measures is thought to be adequate for many home and business purposes ...
- Webcollage.net
... SonicWALL Application Intelligence, Control and Visualization extends control over nonproductive applications like online trading, instant messaging/chat, peer-to-peer sharing and streaming video sites. SonicWALL Email Security completes the offering with effective protection against spam and phishi ...
... SonicWALL Application Intelligence, Control and Visualization extends control over nonproductive applications like online trading, instant messaging/chat, peer-to-peer sharing and streaming video sites. SonicWALL Email Security completes the offering with effective protection against spam and phishi ...
Passport: Secure and Adoptable Source Authentication
... Passport is plausible for gigabit links, and can mitigate reflector attacks even without separate denial-of-service defenses. Our adoptability modeling shows that Passport provides stronger security and deployment incentives than alternatives such as ingress filtering. This is because the ISPs that ...
... Passport is plausible for gigabit links, and can mitigate reflector attacks even without separate denial-of-service defenses. Our adoptability modeling shows that Passport provides stronger security and deployment incentives than alternatives such as ingress filtering. This is because the ISPs that ...
Virtual Private Networks (VPN`s)
... Extranet-based - When a company has a close relationship with another company (for example, a partner, supplier or customer), they can build an extranet VPN that connects LAN to LAN, and that allows all of the various companies to work in a ...
... Extranet-based - When a company has a close relationship with another company (for example, a partner, supplier or customer), they can build an extranet VPN that connects LAN to LAN, and that allows all of the various companies to work in a ...
Clavister E5
... effort of making it easy to use. For example, our highly acclaimed centralized security management system, Clavister InControl uses color-coded attribute groups to provide a clear overview over dependencies that the firewall rules have to each other, making human errors less likely to occur. By comb ...
... effort of making it easy to use. For example, our highly acclaimed centralized security management system, Clavister InControl uses color-coded attribute groups to provide a clear overview over dependencies that the firewall rules have to each other, making human errors less likely to occur. By comb ...