(DTN) Program
... • DTN makes applications over disrupted networks robust • DTN is also an Opportunity to solve Fundamental Problems we’ve never before had a handle on, using Network-Managed Persistence ...
... • DTN makes applications over disrupted networks robust • DTN is also an Opportunity to solve Fundamental Problems we’ve never before had a handle on, using Network-Managed Persistence ...
II - Computer Science - University of Virginia
... [GAO96]. The report further estimated that as many as 65 percent of those attacks were successful in gaining access to sensitive information. More than 99 percent of all respondents reported at least one security incident in one recent survey [Pow99], while 78 percent of organizations responding to ...
... [GAO96]. The report further estimated that as many as 65 percent of those attacks were successful in gaining access to sensitive information. More than 99 percent of all respondents reported at least one security incident in one recent survey [Pow99], while 78 percent of organizations responding to ...
BGP
... Stub: an AS that has only a single connection to one other AS - carries only local traffic. Multi-homed: an AS that has connections to more than one AS, but does not carry transit traffic Transit: an AS that has connections to more than one AS, and carries both transit and local traffic (under certa ...
... Stub: an AS that has only a single connection to one other AS - carries only local traffic. Multi-homed: an AS that has connections to more than one AS, but does not carry transit traffic Transit: an AS that has connections to more than one AS, and carries both transit and local traffic (under certa ...
Slides
... • Detection of both low and high volume anomalies – (DoS, DDoS, host and Network scans, worms, phishing sites, etc.) • Automatic classification, collection of evidence • Detection of anomaly entry points, suggestion of ACLs • Give correct indications also in presence of sudden traffic shifts due to ...
... • Detection of both low and high volume anomalies – (DoS, DDoS, host and Network scans, worms, phishing sites, etc.) • Automatic classification, collection of evidence • Detection of anomaly entry points, suggestion of ACLs • Give correct indications also in presence of sudden traffic shifts due to ...
An Overview of the Wireless Intrusion Detection System
... networking has been installed in many businesses, even in preference to the wired networks that have been commonplace for many years. By just about any measure, WLAN usage is growing at a rapid pace worldwide. However, this has also created an environment where there is great chance for intrusion, s ...
... networking has been installed in many businesses, even in preference to the wired networks that have been commonplace for many years. By just about any measure, WLAN usage is growing at a rapid pace worldwide. However, this has also created an environment where there is great chance for intrusion, s ...
Detecting and Preventing Rogue Devices on the Network
... The access point is outside the control of IT personnel and serves as a gateway for attackers to enter the enterprise. The other type of rogue access point is more difficult to control. The external rogue access point is one that is controlled by an attacker and designed to spoof legitimate clients ...
... The access point is outside the control of IT personnel and serves as a gateway for attackers to enter the enterprise. The other type of rogue access point is more difficult to control. The external rogue access point is one that is controlled by an attacker and designed to spoof legitimate clients ...
Lecture 11
... • A collection of honeypots on a single network – Maybe on a single machine with multiple addresses – More often using virtualization • Typically, no other machines are on the network • Since whole network is phony, all incoming traffic is probably attack traffic CS 136, Fall 2012 ...
... • A collection of honeypots on a single network – Maybe on a single machine with multiple addresses – More often using virtualization • Typically, no other machines are on the network • Since whole network is phony, all incoming traffic is probably attack traffic CS 136, Fall 2012 ...
NP5400 UG
... Wireless networks can be vulnerable to an outsider gaining access if the encryption settings are not set adequately. Some of the default security settings on some wireless hardware, and in Microsoft Windows, may allow access to your wireless network from other wireless devices. The concepts that are ...
... Wireless networks can be vulnerable to an outsider gaining access if the encryption settings are not set adequately. Some of the default security settings on some wireless hardware, and in Microsoft Windows, may allow access to your wireless network from other wireless devices. The concepts that are ...
OWASP Web Application Security
... App. Responds differently to a valid user name with an invalid password, then to a invalid user name Web Application discloses which logins are valid vs. which are invalid, and allows accounts to be guessed and harvested. Provides the attacker with an important initial piece of information, which ...
... App. Responds differently to a valid user name with an invalid password, then to a invalid user name Web Application discloses which logins are valid vs. which are invalid, and allows accounts to be guessed and harvested. Provides the attacker with an important initial piece of information, which ...
AT12264: ATWINC1500 Wi-Fi Network Controller - Station
... STA may be fixed, mobile, or portable. Generally in wireless networking terminology, a station also calls wireless client and node. With a station also being referred as transmitter or receiver based on its transmission characteristics. IEEE 802.11-2007 formally defines station as: Any device that c ...
... STA may be fixed, mobile, or portable. Generally in wireless networking terminology, a station also calls wireless client and node. With a station also being referred as transmitter or receiver based on its transmission characteristics. IEEE 802.11-2007 formally defines station as: Any device that c ...
3.3 Link spoofing attack
... consistency. To help alleviate the potentially large amount of network traffic that such updates can generate, route updates can employ two possible types of packets: full dump and smaller incremental packets. Each of these broadcasts should fit into a standard-size of network protocol data unit (NP ...
... consistency. To help alleviate the potentially large amount of network traffic that such updates can generate, route updates can employ two possible types of packets: full dump and smaller incremental packets. Each of these broadcasts should fit into a standard-size of network protocol data unit (NP ...
Acceptable Use Policy
... port scans, flood pings, email‐bombing, packet spoofing, IP spoofing, and forged routing information. c) Executing any form of network activity that will intercept data not intended for the Client's server. d) Evading or circumventing user authentication or security of any host, network or account, ...
... port scans, flood pings, email‐bombing, packet spoofing, IP spoofing, and forged routing information. c) Executing any form of network activity that will intercept data not intended for the Client's server. d) Evading or circumventing user authentication or security of any host, network or account, ...
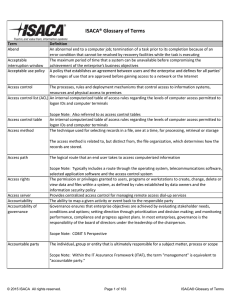
ISACA® Glossary of Terms
... perceptions of others and can be influenced by improper actions or associations. A program written in a portable, platform‐independent computer language, such as Java, JavaScript or Visual Basic Scope Note: An applet is usually embedded in an HyperText Markup Language (HTML) page downloaded from ...
... perceptions of others and can be influenced by improper actions or associations. A program written in a portable, platform‐independent computer language, such as Java, JavaScript or Visual Basic Scope Note: An applet is usually embedded in an HyperText Markup Language (HTML) page downloaded from ...
Windows Wireless Scenarios and Strategies
... Bluetooth Extended Service Discovery Protocols Bluetooth Local Positioning Bluetooth UDI ...
... Bluetooth Extended Service Discovery Protocols Bluetooth Local Positioning Bluetooth UDI ...
3 Assumption on the firewall architecture
... simplicity. But, each component system of the firewall needs to implement only a specific task, making the systems less complex to configure. ...
... simplicity. But, each component system of the firewall needs to implement only a specific task, making the systems less complex to configure. ...
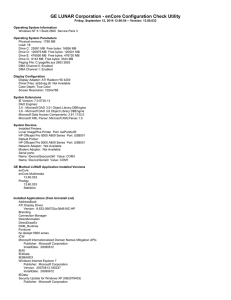
GE LUNAR Corporation
... Description: Enables support for NetBIOS over TCP/IP (NetBT) service and NetBIOS name resolution. Group: TDI [Net Driver HPZ12] Not Available [PlugPlay] Plug and Play Description: Enables a computer to recognize and adapt to hardware changes with little or no user input. Stopping or disabling this s ...
... Description: Enables support for NetBIOS over TCP/IP (NetBT) service and NetBIOS name resolution. Group: TDI [Net Driver HPZ12] Not Available [PlugPlay] Plug and Play Description: Enables a computer to recognize and adapt to hardware changes with little or no user input. Stopping or disabling this s ...
Incident Response
... Creating a set of procedures to deal with the incident efficiently. Obtaining the resources and personnel to deal with the problem. Establish an infrastructure to support incident response activity. ...
... Creating a set of procedures to deal with the incident efficiently. Obtaining the resources and personnel to deal with the problem. Establish an infrastructure to support incident response activity. ...
Defense-in-Depth: Foundations for Secure and - News
... Use of any trademarks in this report is not intended in any way to infringe on the rights of the trademark holder. Internal use. Permission to reproduce this document and to prepare derivative works from this document for internal use is granted, provided the copyright and "No Warranty" statements a ...
... Use of any trademarks in this report is not intended in any way to infringe on the rights of the trademark holder. Internal use. Permission to reproduce this document and to prepare derivative works from this document for internal use is granted, provided the copyright and "No Warranty" statements a ...
MCITP Guide to Microsoft Windows Server 2008 Server Administration
... – Uses security capabilities such as encryption, user authentication, and security certificates MCITP Guide to Microsoft Windows Server 2008, Server Administration (Exam #70-646) ...
... – Uses security capabilities such as encryption, user authentication, and security certificates MCITP Guide to Microsoft Windows Server 2008, Server Administration (Exam #70-646) ...
Document
... IEEE 802 series The 802 series of specifications was named after the date when the IEEE Computer Society “Local Network Standards Committee,” Project 802, held their first meeting, which was in February (2) of 1980(80) The 802 series of specifications define the physical media for each specifica ...
... IEEE 802 series The 802 series of specifications was named after the date when the IEEE Computer Society “Local Network Standards Committee,” Project 802, held their first meeting, which was in February (2) of 1980(80) The 802 series of specifications define the physical media for each specifica ...
Presentation Title Size 30PT
... from the first attempt with 75% or higher they are eligible either the two or one exam offer, but not both 26 ...
... from the first attempt with 75% or higher they are eligible either the two or one exam offer, but not both 26 ...
Introducing Network Design Concepts
... can support new applications without impacting the level of service delivered to existing users. Availability: A network designed for availability is one that delivers consistent, reliable performance, 24 hours a day, 7 days a week. In addition, the failure of a single link or piece of equipment sho ...
... can support new applications without impacting the level of service delivered to existing users. Availability: A network designed for availability is one that delivers consistent, reliable performance, 24 hours a day, 7 days a week. In addition, the failure of a single link or piece of equipment sho ...
Case Studies - Huawei Enterprise
... following challenges: • Outdated network The legacy network had a limited capacity that could not fully meet the Ancheng Insurance's service requirements. The company's production center had an Ethernet-based network that did not support virtualization and automatic distribution of network resource ...
... following challenges: • Outdated network The legacy network had a limited capacity that could not fully meet the Ancheng Insurance's service requirements. The company's production center had an Ethernet-based network that did not support virtualization and automatic distribution of network resource ...
Dell SonicWALL SuperMassive Firewalls
... Application traffic analytics enable the identification of productive and unproductive application traffic in real time, and traffic can then be controlled through powerful application-level policies. Application control can be exercised on both a per-user and pergroup basis, along with schedules an ...
... Application traffic analytics enable the identification of productive and unproductive application traffic in real time, and traffic can then be controlled through powerful application-level policies. Application control can be exercised on both a per-user and pergroup basis, along with schedules an ...
CCNA Concentrations
... Cisco customers seeking knowledge, community, training, information, and support as they start or enhance their careers through Cisco certifications. ...
... Cisco customers seeking knowledge, community, training, information, and support as they start or enhance their careers through Cisco certifications. ...