Governance Guidance - Top Actions
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
... Does management know where the enterprise is most vulnerable within the IT infrastructure? ...
Slide 1
... – Similar to a Trojan, but on a network – Travels from machine to machine through the network ...
... – Similar to a Trojan, but on a network – Travels from machine to machine through the network ...
Virtual Services Platform 4000 Series
... Simplify your network with the Avaya Virtual Services Platform (VSP) 4000. Designed to extend the reach of Avaya Fabric Connect technology to the network edge, the VSP 4000 delivers fully featured network virtualization capabilities in a low-cost 1/10 Gigabit platform optimized for small locations. ...
... Simplify your network with the Avaya Virtual Services Platform (VSP) 4000. Designed to extend the reach of Avaya Fabric Connect technology to the network edge, the VSP 4000 delivers fully featured network virtualization capabilities in a low-cost 1/10 Gigabit platform optimized for small locations. ...
topological database - YSU Computer Science & Information Systems
... The DR could represent a single point of failure, so a second router is elected as the BDR to provide fault tolerance. Thus, the BDR must also become adjacent to all routers on the network and must serve as a second focal point for LSAs. But, unlike the DR, the BDR is not responsible for updating th ...
... The DR could represent a single point of failure, so a second router is elected as the BDR to provide fault tolerance. Thus, the BDR must also become adjacent to all routers on the network and must serve as a second focal point for LSAs. But, unlike the DR, the BDR is not responsible for updating th ...
Chapter 26 Securing Computers
... – Similar to a Trojan, but on a network – Travels from machine to machine through the network ...
... – Similar to a Trojan, but on a network – Travels from machine to machine through the network ...
Towards Efficient and Robust Multihop Wireless Networks
... • Must be supported by Internet access technology • Strict requirements – Minimum required throughput – Maximum tolerable delay and jitter ...
... • Must be supported by Internet access technology • Strict requirements – Minimum required throughput – Maximum tolerable delay and jitter ...
nsa 100sx
... bytes except when VLAN tagged (more on that later) • Frame overhead of 18 bytes (min) results in overhead of 28% - ouch – for small data payloads ...
... bytes except when VLAN tagged (more on that later) • Frame overhead of 18 bytes (min) results in overhead of 28% - ouch – for small data payloads ...
PPT Version
... 1. The packet is not Teredo if it is not UDP over IPv4. 2. Set T to the UDP payload offset. 3. Set E to the end of the packet plus one. 4. If E-T < 40 (the length of an IPv6 base header), the packet is not Teredo. 5. If the octets starting with T are 0x0001 (an indication of authentication data), T= ...
... 1. The packet is not Teredo if it is not UDP over IPv4. 2. Set T to the UDP payload offset. 3. Set E to the end of the packet plus one. 4. If E-T < 40 (the length of an IPv6 base header), the packet is not Teredo. 5. If the octets starting with T are 0x0001 (an indication of authentication data), T= ...
Packets and Protocols - St. Clair County Community College
... Packets and Protocols Transparent Bridges perform three functions: 1. Learn MAC addresses by examining the source MAC address of each frame received by the bridge 2. Deciding when to forward a frame or when to filter (not forward) a frame, based on the destination MAC address 3. Create a loop-free ...
... Packets and Protocols Transparent Bridges perform three functions: 1. Learn MAC addresses by examining the source MAC address of each frame received by the bridge 2. Deciding when to forward a frame or when to filter (not forward) a frame, based on the destination MAC address 3. Create a loop-free ...
Designing an LTE Network Using EDX SignalPro
... (the eNodeB’s) are known. This is not the case for uplink interference, which is based on the location and usage of the subscribers’ terminals (UE’s). Predictions of uplink interference can be made based on statistical studies or Monte Carlo simulations, but it is important to understand the advanta ...
... (the eNodeB’s) are known. This is not the case for uplink interference, which is based on the location and usage of the subscribers’ terminals (UE’s). Predictions of uplink interference can be made based on statistical studies or Monte Carlo simulations, but it is important to understand the advanta ...
FDS manual File Delivery Services SFTP and FTP file transfer
... new generation. The FDS-SSH service became obsolete as a result and, as of mid-2010, was no longer continued. ...
... new generation. The FDS-SSH service became obsolete as a result and, as of mid-2010, was no longer continued. ...
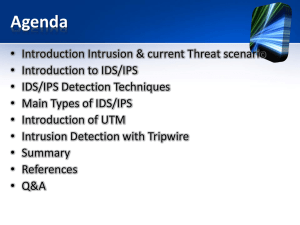
IPS/IDS - SudeeraJ.com
... • Ability to update all the security functions or programs concurrently • Eliminates the need for systems administrators to maintain multiple security programs over time ...
... • Ability to update all the security functions or programs concurrently • Eliminates the need for systems administrators to maintain multiple security programs over time ...
ZXHN H108N - Movistar.
... auto-negotiation capability for different standards (G.dmt, T1.413 Issue 2) according to the settings on the central office Digital Subscriber Line Access Multiplexer (DSLAM). It provides four 10/100Base-T Ethernet interfaces and one Universal Serial Bus (USB) 2.0 Host interface. It supports Institu ...
... auto-negotiation capability for different standards (G.dmt, T1.413 Issue 2) according to the settings on the central office Digital Subscriber Line Access Multiplexer (DSLAM). It provides four 10/100Base-T Ethernet interfaces and one Universal Serial Bus (USB) 2.0 Host interface. It supports Institu ...
CryptoGuard VPN
... based on the security policy the user defines. The definition of the security policy has to be done centrally at the Security Management Station. After defining the security policy at the SMS, the ...
... based on the security policy the user defines. The definition of the security policy has to be done centrally at the Security Management Station. After defining the security policy at the SMS, the ...
Implementing L2 at the Data Center Access Layer
... across multiple access elements. The list starts by describing the connectivity requirements at the server level, and walks through the network elements all the way to the network core. Additionally, the list illustrates some of the capabilities of a network implemented according to this guide. The ...
... across multiple access elements. The list starts by describing the connectivity requirements at the server level, and walks through the network elements all the way to the network core. Additionally, the list illustrates some of the capabilities of a network implemented according to this guide. The ...
More on the IP
... – But this is not bad – First, errors are caught--at the next-higher layer (transport) if TCP is used – Second, avoiding error checking at each hop between routers lowers router costs ...
... – But this is not bad – First, errors are caught--at the next-higher layer (transport) if TCP is used – Second, avoiding error checking at each hop between routers lowers router costs ...
paper
... a short period. As a result, a router can XOR two packets and deliver them to two different neighbors in a single transmission whenever it knows that each of the two neighbors has overheard the packet destined to the other. Snooping not only extends the benefits of coding beyond duplex flows, but al ...
... a short period. As a result, a router can XOR two packets and deliver them to two different neighbors in a single transmission whenever it knows that each of the two neighbors has overheard the packet destined to the other. Snooping not only extends the benefits of coding beyond duplex flows, but al ...
Update a postal address for your broadband bill
... 1. Connect the supplied PC/LAN cable to any of the four LAN ports on the rear panel of your Vodafone Broadband Complete and plug the other end into the Ethernet port on your computer. 2. The Ethernet indicator on your computer and the DSL indicator on the front of your Broadband Complete device will ...
... 1. Connect the supplied PC/LAN cable to any of the four LAN ports on the rear panel of your Vodafone Broadband Complete and plug the other end into the Ethernet port on your computer. 2. The Ethernet indicator on your computer and the DSL indicator on the front of your Broadband Complete device will ...
mir
... Introduction: In this presentation, I will present a solution to the Problem of running TCP in Ad hoc wireless network The solution is to implement a thin layer between IP And TCP called ATCP that ensures correct TCP Behavior while maintaining high throughput. ...
... Introduction: In this presentation, I will present a solution to the Problem of running TCP in Ad hoc wireless network The solution is to implement a thin layer between IP And TCP called ATCP that ensures correct TCP Behavior while maintaining high throughput. ...
CCNA 1: Chapter 11 Exam Answer v4.0 100%
... and connectivity testing of the network shown in the graphic. A ping from host B to host C results in a destination unreachable but a ping from host B to host A was successful. What two reasons could account for this failure based on the graphic and partial router output for the Dallas router? (Choo ...
... and connectivity testing of the network shown in the graphic. A ping from host B to host C results in a destination unreachable but a ping from host B to host A was successful. What two reasons could account for this failure based on the graphic and partial router output for the Dallas router? (Choo ...
Ganjali
... Which flows need to be sampled Inside a given flow how samples are selected What part of each packet is selected Where the samples are sent to ...
... Which flows need to be sampled Inside a given flow how samples are selected What part of each packet is selected Where the samples are sent to ...
ECE/CS 4984: Lecture 11
... ● Delay is often very high ■ Round-trip time can be very long and variable ■ TCP’s timeout mechanisms may not work well ■ Problem exacerbated by link-level retransmission ● Links may be asymmetric ■ Delayed ACKs in the slow direction can limit throughput in the fast direction ...
... ● Delay is often very high ■ Round-trip time can be very long and variable ■ TCP’s timeout mechanisms may not work well ■ Problem exacerbated by link-level retransmission ● Links may be asymmetric ■ Delayed ACKs in the slow direction can limit throughput in the fast direction ...
Selective and Early Threat Detection in Large Networked
... database and the NIDS alert. The alert ranking process is initiated when the alert ranking server receives an alert ranking request, including two mandatory fields: the IP address of the machine targeted by the attack, and an identifier of the vulnerability that the attack tried to exploit. These in ...
... database and the NIDS alert. The alert ranking process is initiated when the alert ranking server receives an alert ranking request, including two mandatory fields: the IP address of the machine targeted by the attack, and an identifier of the vulnerability that the attack tried to exploit. These in ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.