Hands-On Ethical Hacking and Network Security
... • Several different platforms and technologies can be used to develop Web applications • Attacks differ depending on the platform and technology used to develop the application – Footprinting is used to find out as much information as possible about a target system – The more you know about a system ...
... • Several different platforms and technologies can be used to develop Web applications • Attacks differ depending on the platform and technology used to develop the application – Footprinting is used to find out as much information as possible about a target system – The more you know about a system ...
RangeMax Dual Band Wireless-N Modem Router Setup
... Manual Setup: If you cannot or prefer not to use the Smart Wizard, see “Installing Your Router Manually (Advanced, Mac, and Linux Users)” on page 13. For example, if you are connecting to a Mac, are using a Linux operating system, or are technically knowledgeable, select this option. If you choose t ...
... Manual Setup: If you cannot or prefer not to use the Smart Wizard, see “Installing Your Router Manually (Advanced, Mac, and Linux Users)” on page 13. For example, if you are connecting to a Mac, are using a Linux operating system, or are technically knowledgeable, select this option. If you choose t ...
CloudSync Network Drive
... If typing STORAGE in the address field of your web browser does not work, use the Nettool application to locate the network drive instead. 1. The Nettool application requires the Java Runtime Environment (JRE). If JRE is not already installed on your computer, go to www.sun.com and download it. 2. D ...
... If typing STORAGE in the address field of your web browser does not work, use the Nettool application to locate the network drive instead. 1. The Nettool application requires the Java Runtime Environment (JRE). If JRE is not already installed on your computer, go to www.sun.com and download it. 2. D ...
Approximate Server Selection Algorithms in Content Distribution
... increasing availability of fast Internet access to the enduser, have turned centralized web servers into a performance bottleneck. Popular web sites (e.g., news sites) receive tens of millions of requests per day, which may easily overload a state-of-the-art web server and increase significantly the ...
... increasing availability of fast Internet access to the enduser, have turned centralized web servers into a performance bottleneck. Popular web sites (e.g., news sites) receive tens of millions of requests per day, which may easily overload a state-of-the-art web server and increase significantly the ...
Page | 1
... information technology and methods of transmitting information and data between local and global networks, there are some security gaps that can cause serious problems. This is a fact that can not be denied. For instance, according to Olzak (2007) NetBIOS (Network Basic Input Output System) is almos ...
... information technology and methods of transmitting information and data between local and global networks, there are some security gaps that can cause serious problems. This is a fact that can not be denied. For instance, according to Olzak (2007) NetBIOS (Network Basic Input Output System) is almos ...
High Performance Networks for High Performance
... • Detects threats that other solutions miss Compliance-driven capabilities • Enables IT best practices that support compliance initiatives Scalable distributed log collection and archival • Network security management scales to any sized organization ...
... • Detects threats that other solutions miss Compliance-driven capabilities • Enables IT best practices that support compliance initiatives Scalable distributed log collection and archival • Network security management scales to any sized organization ...
Rudimentary NMS Software Components (Chapter 7)
... Network Operators problems with the growth of traffic types and volumes. Operational increase due to Multiple NMS growth. There is a strong need to reduce the cost of ownership and improve the return on investment (ROI) for network ...
... Network Operators problems with the growth of traffic types and volumes. Operational increase due to Multiple NMS growth. There is a strong need to reduce the cost of ownership and improve the return on investment (ROI) for network ...
C Spire Wireless
... Connecting to Your 4G LTE Mobile Hotspot Now, you’re ready to connect your computer or other Wi-Fi capable devices to your 4G LTE Mobile Hotspot using a Wi-Fi connection. 1. Power on your computer, tablet or Wi-Fi device and power on your 4G LTE Mobile Hotspot. The C Spire power-on animation will ap ...
... Connecting to Your 4G LTE Mobile Hotspot Now, you’re ready to connect your computer or other Wi-Fi capable devices to your 4G LTE Mobile Hotspot using a Wi-Fi connection. 1. Power on your computer, tablet or Wi-Fi device and power on your 4G LTE Mobile Hotspot. The C Spire power-on animation will ap ...
ppt
... • Scale through NAK suppression – If received a NAK or NCF, don’t NAK yourself – Add random delays before NAK’ing ...
... • Scale through NAK suppression – If received a NAK or NCF, don’t NAK yourself – Add random delays before NAK’ing ...
BBSM Services
... interfaces: Bell Hobic, Xiox, Fidelio 6.x, 7.x, Express, and Opera, and H1/H2. – 2-way IP and serial interface for Fidelio NOTE: These protocols cover a majority of the PMS systems, but it is essential to ask your customer what PMS protocol/vendor they utilize. If their system uses a different proto ...
... interfaces: Bell Hobic, Xiox, Fidelio 6.x, 7.x, Express, and Opera, and H1/H2. – 2-way IP and serial interface for Fidelio NOTE: These protocols cover a majority of the PMS systems, but it is essential to ask your customer what PMS protocol/vendor they utilize. If their system uses a different proto ...
Slides - TERENA> Events> tnc2006
... – WAN interface gets an /64 prefix -instead of specific IPv6 address- by using IPCPv6. If there is a need for a static address assignment to the school router, the Frame-Interface-ID* should also be provided. – Internal LAN interfaces are automatically configured using DHCP-PD (prefix delegation). T ...
... – WAN interface gets an /64 prefix -instead of specific IPv6 address- by using IPCPv6. If there is a need for a static address assignment to the school router, the Frame-Interface-ID* should also be provided. – Internal LAN interfaces are automatically configured using DHCP-PD (prefix delegation). T ...
Review, UTRAN Interfaces
... Gb —GPRS interface not suitable for RT transmission —LLC+RLC both ARQ protocols —IP instead of FR Iu-ps —UTRAN PS, IP, QoS, AAL5/ATM , possibly IP over SDH ...
... Gb —GPRS interface not suitable for RT transmission —LLC+RLC both ARQ protocols —IP instead of FR Iu-ps —UTRAN PS, IP, QoS, AAL5/ATM , possibly IP over SDH ...
COEN 252 Computer Forensics - Santa Clara University's
... Do not duplicate all error information. Copying process has lower priority and some packets might not be mirrored. Misses out on traffic on the local link. ...
... Do not duplicate all error information. Copying process has lower priority and some packets might not be mirrored. Misses out on traffic on the local link. ...
Corinex AV200 CableLAN Adapter
... COMMUNICATIONS CORPORATION (“CORINEX”) with regard to the copyrighted Software provided with this EULA. Use of any software and related documentation (“Software”) provided with a CORINEX hardware product, or made available to you by CORINEX via download or otherwise, in whatever form or media, will ...
... COMMUNICATIONS CORPORATION (“CORINEX”) with regard to the copyrighted Software provided with this EULA. Use of any software and related documentation (“Software”) provided with a CORINEX hardware product, or made available to you by CORINEX via download or otherwise, in whatever form or media, will ...
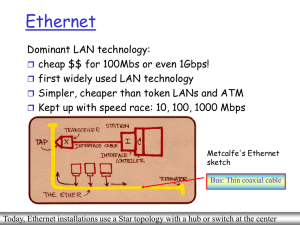
Computer Networking I
... Define the term network. List some of the more common networks we use in everyday life. Define communication protocols. Describe how communication occurs across a local Ethernet network. List the main high-level components of an information network. Identify when a computer plays the role of a clien ...
... Define the term network. List some of the more common networks we use in everyday life. Define communication protocols. Describe how communication occurs across a local Ethernet network. List the main high-level components of an information network. Identify when a computer plays the role of a clien ...
t0 sub-station \`/1%
... and able to communicate With the poWer grid server, a human authorization detector input device connected to the electric meter and the poWer grid server. The human authorization detector is able to receive an input from a user physically located at the structure and capable of communicating With th ...
... and able to communicate With the poWer grid server, a human authorization detector input device connected to the electric meter and the poWer grid server. The human authorization detector is able to receive an input from a user physically located at the structure and capable of communicating With th ...
FIREWALL DEPLOYMENT AND CONFIGURATION
... As Figure 3-2 shows, two hosts below are in a private network. The host with IP address 10.1.2.1 is Target one, the other with IP address 10.1.2.2 is a trusted system. Access list is 10.1.2.2. The host with 172.16.42.5 is used by a hacker in the Internet. The hacker would send a client request to th ...
... As Figure 3-2 shows, two hosts below are in a private network. The host with IP address 10.1.2.1 is Target one, the other with IP address 10.1.2.2 is a trusted system. Access list is 10.1.2.2. The host with 172.16.42.5 is used by a hacker in the Internet. The hacker would send a client request to th ...
Designing AirPort Extreme Networks
... wireless network have WPA support. It provides a high level of data protection and (when used in Enterprise mode) requires user authentication. The main standards-based technologies that comprise WPA include Temporal Key Integrity Protocol (TKIP), 802.1X, Message Integrity Check (MIC), and Extensibl ...
... wireless network have WPA support. It provides a high level of data protection and (when used in Enterprise mode) requires user authentication. The main standards-based technologies that comprise WPA include Temporal Key Integrity Protocol (TKIP), 802.1X, Message Integrity Check (MIC), and Extensibl ...
about this guide - CVS Caremark Online Applications
... To use this connectivity option, the client network and host-operating environment must be based on the IBM SNA network architecture and support NJE. Caremark has the necessary software — SNA Network Interconnection (SNI) — to allow SNA networks to interface. If the client also has SNI installed the ...
... To use this connectivity option, the client network and host-operating environment must be based on the IBM SNA network architecture and support NJE. Caremark has the necessary software — SNA Network Interconnection (SNI) — to allow SNA networks to interface. If the client also has SNI installed the ...
Ethernet Switches
... • connects hosts to base station or another wireless host • e.g. 802.11a, 802.11g, 802.11b, UMTS/WCDMA, GSM, etc. Base Station • sends/receives packets to and from a wireless host associated with base station; coordinates multiple transmissions of hosts • e.g. cell towers (cellular networks), Access ...
... • connects hosts to base station or another wireless host • e.g. 802.11a, 802.11g, 802.11b, UMTS/WCDMA, GSM, etc. Base Station • sends/receives packets to and from a wireless host associated with base station; coordinates multiple transmissions of hosts • e.g. cell towers (cellular networks), Access ...
Microsoft Windows 2000? Router Configuration Guide
... placed on the deterrence of these type activities. Using the Windows 2000 Server Routing features is recommended as a possible solution to this ongoing network concern for small organizations already within a DoD domain or remote locations. It is important to have a basic understanding of routing be ...
... placed on the deterrence of these type activities. Using the Windows 2000 Server Routing features is recommended as a possible solution to this ongoing network concern for small organizations already within a DoD domain or remote locations. It is important to have a basic understanding of routing be ...
Getting the NAC of Network Security
... Hardware-based attestation of hypervisor integrity Secure BIOS update mechanisms should be mandatory Understand the level at which your hypervisor provider hosts drivers. (Drivers are a weak link in any server security model.) Security policies that define the configuration of the hypervisor, access ...
... Hardware-based attestation of hypervisor integrity Secure BIOS update mechanisms should be mandatory Understand the level at which your hypervisor provider hosts drivers. (Drivers are a weak link in any server security model.) Security policies that define the configuration of the hypervisor, access ...
FIREWALLS
... it enables the outside world to reach and interact with local network assets. This creates a threat to the organization. While it is possible to equip each workstation and server on the premises network with strong security features, such as intrusion protection, this may not be sufficient and in so ...
... it enables the outside world to reach and interact with local network assets. This creates a threat to the organization. While it is possible to equip each workstation and server on the premises network with strong security features, such as intrusion protection, this may not be sufficient and in so ...
SNMP Simple Network Management Protocol - CS-UCY
... • SNMP manager and an SNMP agent communicate using the SNMP protocol – Generally: Manager sends queries and agent responds – Exception: Traps are initiated by agent. ...
... • SNMP manager and an SNMP agent communicate using the SNMP protocol – Generally: Manager sends queries and agent responds – Exception: Traps are initiated by agent. ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.