Chapter 15
... – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer digital data to and from the phone company’s ...
... – A phone modem converts computer data into an analog audio signal for transfer over a telephone line, and then a modem at the destination converts it back again into data – A digital subscriber line (DSL) uses regular copper phone lines to transfer digital data to and from the phone company’s ...
Overview of Nomadix` RADIUS Implementation Solution Outline
... network efficiency. Idle-timeouts can be effectively used to ensure accurate billing for users that either turn off their laptop or lose network access for any other reason (e.g. AP becomes inoperable). Alternatively, in many Wi-Fi networks, environmentally caused radio interferences are not uncommo ...
... network efficiency. Idle-timeouts can be effectively used to ensure accurate billing for users that either turn off their laptop or lose network access for any other reason (e.g. AP becomes inoperable). Alternatively, in many Wi-Fi networks, environmentally caused radio interferences are not uncommo ...
Information System Security
... • no single mechanism that will support all functions required • however one particular element underlies many of the security mechanisms in use: cryptographic techniques • hence our focus on this area ...
... • no single mechanism that will support all functions required • however one particular element underlies many of the security mechanisms in use: cryptographic techniques • hence our focus on this area ...
IP / MPLS - IDG Communications
... • Network has full QoS feature support with Service Level Guarantees to support lower latency, packet loss and jitter • 100% Powered by Cisco Systems – Single vendor platform • Infrastructure is SOUL owned and operated, and independent of Telstra • In excess of 900 employees in offices throughout Au ...
... • Network has full QoS feature support with Service Level Guarantees to support lower latency, packet loss and jitter • 100% Powered by Cisco Systems – Single vendor platform • Infrastructure is SOUL owned and operated, and independent of Telstra • In excess of 900 employees in offices throughout Au ...
Chapter 3 - Network Protocols
... on ports in this range. These ports are defined and allocated to commonly used services. For each protocol on the next page, you should know the ports numbers they use as well as the ...
... on ports in this range. These ports are defined and allocated to commonly used services. For each protocol on the next page, you should know the ports numbers they use as well as the ...
GEPS Programming Tutorial
... The process of joining a Wi-Fi-based network is summarized in Figure 2. The node must first discover what suitable networks can be heard. In 802.11, access points send special beacon packets at regular intervals, containing the information required by a Station that wishes to associate with their ne ...
... The process of joining a Wi-Fi-based network is summarized in Figure 2. The node must first discover what suitable networks can be heard. In 802.11, access points send special beacon packets at regular intervals, containing the information required by a Station that wishes to associate with their ne ...
Networks - PEGSnet
... server computer that is used to access websites on behalf of other computers; hence it acts as a proxy for the actual Internet. When a computer wants a website, it is retrieved by the proxy server and then sent to the requesting computer after it has passed the firewall program. ...
... server computer that is used to access websites on behalf of other computers; hence it acts as a proxy for the actual Internet. When a computer wants a website, it is retrieved by the proxy server and then sent to the requesting computer after it has passed the firewall program. ...
wave relay® android™ kit
... TO MAINTAIN CONNECTIVITY ON THE MOVE. It is a scalable, peer-to-peer wireless network which provides data, video, and voice even in the most challenging applications. With user throughput of 41 Mbps UDP and 31.1 Mbps TCP, Wave Relay® provides a dynamic, reliable, and secure wireless networking solut ...
... TO MAINTAIN CONNECTIVITY ON THE MOVE. It is a scalable, peer-to-peer wireless network which provides data, video, and voice even in the most challenging applications. With user throughput of 41 Mbps UDP and 31.1 Mbps TCP, Wave Relay® provides a dynamic, reliable, and secure wireless networking solut ...
Portfolio - Department of Electrical Communication Engineering
... Ethernet LAN, a WiFi, and an Internet access link. Such networks are now common in enterprises, campuses and homes, and carry the traffic generated by variety of end-user applications, with each application imposing its own performance requirements. ADWISER has been developed on off-the-self hardwar ...
... Ethernet LAN, a WiFi, and an Internet access link. Such networks are now common in enterprises, campuses and homes, and carry the traffic generated by variety of end-user applications, with each application imposing its own performance requirements. ADWISER has been developed on off-the-self hardwar ...
Shouting from the Rooftops: Improving Email
... Keys are stored, encrypted, on your computer, and used by your email software Keys can be distributed by owner on disk, by email or via access to repository (key server) ...
... Keys are stored, encrypted, on your computer, and used by your email software Keys can be distributed by owner on disk, by email or via access to repository (key server) ...
Ethernet - Mt. Hood Community College
... Security – anyone with receiver within range can pick up signals Regulations differ in different countries ...
... Security – anyone with receiver within range can pick up signals Regulations differ in different countries ...
Import Settings:
... Section Reference: Identifying Types of LANs Explanation: The wireless access point (WAP) acts as the central connecting device for the network. Today, such networks can consist of many types of devices other than traditional PCs, including smart phones, PDAs, tablet computers, and microcomputers. 1 ...
... Section Reference: Identifying Types of LANs Explanation: The wireless access point (WAP) acts as the central connecting device for the network. Today, such networks can consist of many types of devices other than traditional PCs, including smart phones, PDAs, tablet computers, and microcomputers. 1 ...
Wireless (In)Security or Why You Will WEEP When You Learn
... broadcasted out over the wireless network. ARP spoofing technique can trick switch into passing data from backbone of subnet and route it through attacker’s wireless client. Attacker can trick wireless client into using unauthorized AP with stronger ...
... broadcasted out over the wireless network. ARP spoofing technique can trick switch into passing data from backbone of subnet and route it through attacker’s wireless client. Attacker can trick wireless client into using unauthorized AP with stronger ...
PPT - University of Surrey
... − It’s usually powered by battery. This implies limited source of energy. − It’s generally small in size and low in cost. This limits their computing capability. − It doesn’t usually perform complicated tasks. ...
... − It’s usually powered by battery. This implies limited source of energy. − It’s generally small in size and low in cost. This limits their computing capability. − It doesn’t usually perform complicated tasks. ...
bestcom wireless
... (1) To ensure non-stop service for wireless users in case of single point failure. (2) The backup of AP and user data is required. (3) Fast failure detection and fast switching are required (4) Support hot backup of plain text or certificate authentication users. ...
... (1) To ensure non-stop service for wireless users in case of single point failure. (2) The backup of AP and user data is required. (3) Fast failure detection and fast switching are required (4) Support hot backup of plain text or certificate authentication users. ...
presentation - NORDUnet Networking Conferences
... – done through service platform (network or content provider), based on .xml/MPEG-7 content description, – done in end-user terminal ...
... – done through service platform (network or content provider), based on .xml/MPEG-7 content description, – done in end-user terminal ...
Ethics, Privacy and Computer Forensics
... An FDDI network with primary and secondary token rings. During normal conditions, only one of the rings is used and data travels in one direction. When a station or a cable segment fails, the traffic loops to form a closed ring, moving data in the opposite direction. ...
... An FDDI network with primary and secondary token rings. During normal conditions, only one of the rings is used and data travels in one direction. When a station or a cable segment fails, the traffic loops to form a closed ring, moving data in the opposite direction. ...
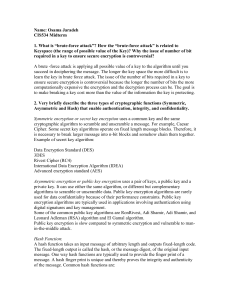
Three challenges with secret key encryption
... corporate infrastructure, information authentication mechanism and access privileges. This will vary depending on how the corporate resources are accessed. 10. What is NAT, why it is used, and what is its security issue? NAT stands for Network Address Translation which is often used in environments ...
... corporate infrastructure, information authentication mechanism and access privileges. This will vary depending on how the corporate resources are accessed. 10. What is NAT, why it is used, and what is its security issue? NAT stands for Network Address Translation which is often used in environments ...
Access Control Policies
... – Use strong (and different) passwords – Change passwords periodically – Do not introduce passwords where not sure if legitimate – For extra security: use multi-factor authentication methods ...
... – Use strong (and different) passwords – Change passwords periodically – Do not introduce passwords where not sure if legitimate – For extra security: use multi-factor authentication methods ...
lecture1
... They are cheaper and easier to implement than client/server networks, making them an ideal solution for environments in which budgets are a concern ...
... They are cheaper and easier to implement than client/server networks, making them an ideal solution for environments in which budgets are a concern ...
Week_Three_Network_ppt
... • IP addressing for major network devices, client, server, and private. • Any addressing oddities, such as discontinuous subnets? • Any strategies for addressing and naming? – Route summarization reduces routes in a router – For example, sites may be named using airport codes • San Francisco = SFO, ...
... • IP addressing for major network devices, client, server, and private. • Any addressing oddities, such as discontinuous subnets? • Any strategies for addressing and naming? – Route summarization reduces routes in a router – For example, sites may be named using airport codes • San Francisco = SFO, ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.