CSCI6268L18 - Computer Science
... • Our local routing table (on host of user1) is not going to have a route to IP of user2 – Routing table will therefore send our packet to the gateway – Gateway is the machine/router on the “edge” of the network responsible for processing all incoming/outgoing traffic from/to the LAN • NAT boxing, f ...
... • Our local routing table (on host of user1) is not going to have a route to IP of user2 – Routing table will therefore send our packet to the gateway – Gateway is the machine/router on the “edge” of the network responsible for processing all incoming/outgoing traffic from/to the LAN • NAT boxing, f ...
- NetComm Wireless
... What can you do with VPNs? The benefits of using a VPN include: Security – All traffic in and out of the router is encrypted (except when using GRE) ensuring the integrity of your network. Common network – the devices can be placed in the same subnet meaning that they can be more easily administere ...
... What can you do with VPNs? The benefits of using a VPN include: Security – All traffic in and out of the router is encrypted (except when using GRE) ensuring the integrity of your network. Common network – the devices can be placed in the same subnet meaning that they can be more easily administere ...
Chapter 5 Overview of Network Services
... • To use Active Directory, at least one server must be configured as a Domain Controller (DC). • It is recommended that there be at least two DCs in each domain, for fault tolerance. • Replication is the process of copying data from one computer to one or more other computers and synchronizing that ...
... • To use Active Directory, at least one server must be configured as a Domain Controller (DC). • It is recommended that there be at least two DCs in each domain, for fault tolerance. • Replication is the process of copying data from one computer to one or more other computers and synchronizing that ...
The Application of Wireless Sensor Network on Regional Environmental Protection
... to tracking crop growth conditions; research the impact of environment change on crops, to provide real-time decision-making. The volume of data on farmland is very large, using the network can be a lot more convenient to achieve the long-distance data transmission, but if laying cable networks in t ...
... to tracking crop growth conditions; research the impact of environment change on crops, to provide real-time decision-making. The volume of data on farmland is very large, using the network can be a lot more convenient to achieve the long-distance data transmission, but if laying cable networks in t ...
Computer and System Logging Policy
... 3. Scope This policy applies to all [LEP] staff that create, deploy, or support application and system software. ...
... 3. Scope This policy applies to all [LEP] staff that create, deploy, or support application and system software. ...
TOC 6 - University of Hawaii at Hilo
... Virus – software written with malicious intent to cause annoyance or damage Worm – spreads itself from computer to computer via e-mail and other network traffic Spyware – collects information about you and reports it to someone else without your ...
... Virus – software written with malicious intent to cause annoyance or damage Worm – spreads itself from computer to computer via e-mail and other network traffic Spyware – collects information about you and reports it to someone else without your ...
Top-Ten Web Security Vulnerabilities
... All session tokens should be user unique, non-predictable, and resistant to reverse engineering Use a trusted random number generator Map session tokens in some way to a specific HTTP client instance to prevent hijacking and replay attacks ...
... All session tokens should be user unique, non-predictable, and resistant to reverse engineering Use a trusted random number generator Map session tokens in some way to a specific HTTP client instance to prevent hijacking and replay attacks ...
CLOUD FASTPATH ACCEPTABLE USE POLICY Tervela, Inc
... bombs, cancelbots or any other computer programming routines that may damage, interfere with, surreptitiously intercept or expropriate the Services; access or search the Services by any means other than our publicly supported interfaces (for example, ...
... bombs, cancelbots or any other computer programming routines that may damage, interfere with, surreptitiously intercept or expropriate the Services; access or search the Services by any means other than our publicly supported interfaces (for example, ...
Out-of-Band Networking Solutions Access, Manage, Simplify www.mrv.com
... Out-of-Band Network equipment connects to service ports protecting them from unauthorized, undetected access. Disconnecting Out-ofBand equipment from a service port can cause an immediate alarm report, increasing overall security. Like any other network, an Out-of-Band Network must implement secure ...
... Out-of-Band Network equipment connects to service ports protecting them from unauthorized, undetected access. Disconnecting Out-ofBand equipment from a service port can cause an immediate alarm report, increasing overall security. Like any other network, an Out-of-Band Network must implement secure ...
Wireless LAN technology is being recognized and accepted or
... and adopted by many organizations worldwide. Many companies and government entities are realizing the competitive advantage of deploying wireless technology in the workplace. Wireless technologies are continually evolving and providing advancements in speed, bandwidth, and security. However, large e ...
... and adopted by many organizations worldwide. Many companies and government entities are realizing the competitive advantage of deploying wireless technology in the workplace. Wireless technologies are continually evolving and providing advancements in speed, bandwidth, and security. However, large e ...
Intrusion Detection Systems
... • A buffer zone between the Internet, where no controls exist, and the inner secure network, where an organization has security policies in place. • The idea behind the use of the DMZ topology is to force a user to make at least one hop in the DMZ before accessing information inside the trusted netw ...
... • A buffer zone between the Internet, where no controls exist, and the inner secure network, where an organization has security policies in place. • The idea behind the use of the DMZ topology is to force a user to make at least one hop in the DMZ before accessing information inside the trusted netw ...
Formal Methods for Intrusion Detection - MSU CSE
... unique pair of users and a third time stamp will be reported. This is an example of a good choice. This class will resist the choking attack, and will report all completed instances of an attack. Having the final timestamp means that the last part of the attack occurred, thus only a completed attack ...
... unique pair of users and a third time stamp will be reported. This is an example of a good choice. This class will resist the choking attack, and will report all completed instances of an attack. Having the final timestamp means that the last part of the attack occurred, thus only a completed attack ...
Chapter 10 - SaigonTech
... • Virus protection for servers and desktop computers is a must • There should be policies aimed at preventing viruses from being downloaded or spread • Backup procedures for all data that can’t be easily reproduced should be in place, and a disaster recovery procedure must be devised • Security is a ...
... • Virus protection for servers and desktop computers is a must • There should be policies aimed at preventing viruses from being downloaded or spread • Backup procedures for all data that can’t be easily reproduced should be in place, and a disaster recovery procedure must be devised • Security is a ...
Introduction - SNS Courseware
... • Neighbors keep silent until see ACK. • Collisions • There is no collision detection. • The senders know collision when they don’t receive CTS. • They each wait for the exponential backoff time. ...
... • Neighbors keep silent until see ACK. • Collisions • There is no collision detection. • The senders know collision when they don’t receive CTS. • They each wait for the exponential backoff time. ...
Cross-layer Performance Optimization in wireless Local Area Network
... Analysis of existing schemes under 3 different scenarios ...
... Analysis of existing schemes under 3 different scenarios ...
Document
... connect client systems into an existing WAN infrastructure • Point-to-Point Tunneling Protocol (PPTP) is most often used when connecting users using virtual private networks (VPNs) • Layer 2 Tunneling Protocol (L2TP) is the next generation of tunneling and is similar in function to PPTP ...
... connect client systems into an existing WAN infrastructure • Point-to-Point Tunneling Protocol (PPTP) is most often used when connecting users using virtual private networks (VPNs) • Layer 2 Tunneling Protocol (L2TP) is the next generation of tunneling and is similar in function to PPTP ...
Packet switching
... • Also on some networking devices, like routers and switches • Runs on port 23 • Allows clients access to a more powerful computer, or a computer without screen (like a router) ...
... • Also on some networking devices, like routers and switches • Runs on port 23 • Allows clients access to a more powerful computer, or a computer without screen (like a router) ...
A Network is - Personal.psu.edu
... Client. A computer on the network that requests resources or services from another computer on a network. In some cases, a client could also act as a server. he term “client” may also refer to the human user of a client workstation Server. A computer on the network that manages shared resources and ...
... Client. A computer on the network that requests resources or services from another computer on a network. In some cases, a client could also act as a server. he term “client” may also refer to the human user of a client workstation Server. A computer on the network that manages shared resources and ...
Network Firewall Technologies By: David W Chadwick
... • Multiple hosts and gateways could be added to handle more traffic at a time • Two packet filtering routers are placed on each side of the DMZ • Very secure ...
... • Multiple hosts and gateways could be added to handle more traffic at a time • Two packet filtering routers are placed on each side of the DMZ • Very secure ...
Chapter 7: Networking
... • Using wireless media is critical when portable computing devices need to be connected to a network. • Data transfer rate (also known as bandwidth) is the maximum speed at which data can be transmitted between two nodes on a network. • Throughput is the actual speed of data transfer that is ...
... • Using wireless media is critical when portable computing devices need to be connected to a network. • Data transfer rate (also known as bandwidth) is the maximum speed at which data can be transmitted between two nodes on a network. • Throughput is the actual speed of data transfer that is ...
Paper Title (use style: paper title) - International Journal of Advanced
... developed as guidelines to ensure compatibility and bring about uniform standard in systems using different hardware and software platforms and can communicate with one another. The OSI and DoD models are layered to define specific tasks to be performed by protocols at different layers in the networ ...
... developed as guidelines to ensure compatibility and bring about uniform standard in systems using different hardware and software platforms and can communicate with one another. The OSI and DoD models are layered to define specific tasks to be performed by protocols at different layers in the networ ...
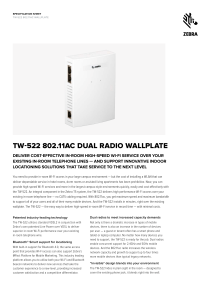
TW-522 802.11ac Dual Radio Wallplate Specification Sheet
... provide high-speed Wi-Fi services and more in the largest campus-style environments quickly, easily and cost-effectively with the TW-522. An integral component in the Zebra T5 system, the TW-522 delivers high performance Wi-Fi access over your existing in-room telephone line — no CAT5 cabling requir ...
... provide high-speed Wi-Fi services and more in the largest campus-style environments quickly, easily and cost-effectively with the TW-522. An integral component in the Zebra T5 system, the TW-522 delivers high performance Wi-Fi access over your existing in-room telephone line — no CAT5 cabling requir ...
No Slide Title
... •Potential security issues; physical access not required. •802.11 wireless communications cannot be received nor decoded by simple scanners or short wave receivers. •However, eavesdropping is possible using special equipment. •802.11 WLAN have a function called WEP (Wired Equivalent Privacy); a for ...
... •Potential security issues; physical access not required. •802.11 wireless communications cannot be received nor decoded by simple scanners or short wave receivers. •However, eavesdropping is possible using special equipment. •802.11 WLAN have a function called WEP (Wired Equivalent Privacy); a for ...
hi! i`m firoz cherapulikkal
... Administering regular activities like troubleshooting various hardware & software related faults at exchange card level fault finding Managing the troubleshooting performance related issues, user support for windows clients, hardware, printers and LAN Monitoring system & verifying the integrity and ...
... Administering regular activities like troubleshooting various hardware & software related faults at exchange card level fault finding Managing the troubleshooting performance related issues, user support for windows clients, hardware, printers and LAN Monitoring system & verifying the integrity and ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.