IOSR Journal of Electronics & Communication Engineering (IOSR-JECE)
... routers and mesh clients. A multihop routing reserve path need to be established, as the range of the routers are greater than that of the mesh clients. There are three basic handshake operations in our approach. RTS/CTS/DATA is used to handle normal data transmission. When a node needs to send DATA ...
... routers and mesh clients. A multihop routing reserve path need to be established, as the range of the routers are greater than that of the mesh clients. There are three basic handshake operations in our approach. RTS/CTS/DATA is used to handle normal data transmission. When a node needs to send DATA ...
Wireless Networks
... IEEE 802.16e introduces “Handover” schemes to migrate a mobile station from the air-interface of one base station to another to provide mobility • Pre-handover process has been designed • The entire Handover process consists of the following five stages: ...
... IEEE 802.16e introduces “Handover” schemes to migrate a mobile station from the air-interface of one base station to another to provide mobility • Pre-handover process has been designed • The entire Handover process consists of the following five stages: ...
Slide 1
... States that a user should have only the privileges needed to do his job. Least privilege is enforced using a network device, such as a router with an access control list (ACL) which tells a computer operating system which access rights each user has to a particular object. ...
... States that a user should have only the privileges needed to do his job. Least privilege is enforced using a network device, such as a router with an access control list (ACL) which tells a computer operating system which access rights each user has to a particular object. ...
Multi-Aspect Security Configuration Assessment
... attacks. The goal of the evaluation is to consider the effects that malicious users can have on the system when they take advantage of known exploits and misconfigurations. The assessment is not able to identify previously unknown ways of violating the system security. However, it is able to verify ...
... attacks. The goal of the evaluation is to consider the effects that malicious users can have on the system when they take advantage of known exploits and misconfigurations. The assessment is not able to identify previously unknown ways of violating the system security. However, it is able to verify ...
Change Control Management
... Privileges of System Administrators • These individuals are assigned to ensure that the system is functioning properly for system users. • The two primary activities of administrator tasks are maintenance and monitoring. • System components requiring regular maintenance and monitoring include works ...
... Privileges of System Administrators • These individuals are assigned to ensure that the system is functioning properly for system users. • The two primary activities of administrator tasks are maintenance and monitoring. • System components requiring regular maintenance and monitoring include works ...
User Manual PowerLine AV500 Wireless N Mini Extender Starter Kit
... wiring1 to create a network or extend your existing network. It turns every power outlet into a potential network connection to access digital media devices, game consoles, print servers, computers, and network storage devices throughout your home. Additionally, Wireless N provides high speed transf ...
... wiring1 to create a network or extend your existing network. It turns every power outlet into a potential network connection to access digital media devices, game consoles, print servers, computers, and network storage devices throughout your home. Additionally, Wireless N provides high speed transf ...
Case Study - Korea Opportunities for BB Connectivity in APAC Ki-young, Ko |
... Circuit Switched Network & IP Multimedia Sub System ...
... Circuit Switched Network & IP Multimedia Sub System ...
Type of Networks (Continued)
... • To avoid this problem, IEEE 802.11 provides for the optional use of a Request To Send (RTS) and Clear To Send (CTS) exchange of frames before the data transmission − Before a sender transmits its data frame, it sends a RTS frame to the receiver indicating the entire duration of the transmission in ...
... • To avoid this problem, IEEE 802.11 provides for the optional use of a Request To Send (RTS) and Clear To Send (CTS) exchange of frames before the data transmission − Before a sender transmits its data frame, it sends a RTS frame to the receiver indicating the entire duration of the transmission in ...
1-ITN-chap-4g
... communicate by using the same shared media. “Data from only one node can be placed on the medium at any one time.” (This is only true when using CSMA/CD (hubs), NOT true with switches. Wireless uses CSMA/CA) Every node “may” see all the frames that are on the medium. Data Link Destination Ad ...
... communicate by using the same shared media. “Data from only one node can be placed on the medium at any one time.” (This is only true when using CSMA/CD (hubs), NOT true with switches. Wireless uses CSMA/CA) Every node “may” see all the frames that are on the medium. Data Link Destination Ad ...
Lecture5_IP_NAT
... To optimize packet lengths for various communication links, IP offers network elements (routers and firewalls) the ability to slice up packets into smaller pieces, a process called fragmentation. The end system’s IP layer is responsible for reassembling all fragments Hackers use packet fragmentation ...
... To optimize packet lengths for various communication links, IP offers network elements (routers and firewalls) the ability to slice up packets into smaller pieces, a process called fragmentation. The end system’s IP layer is responsible for reassembling all fragments Hackers use packet fragmentation ...
Understand Computer Network V
... responsible for locating a host on a LAN; RARP (Reverse Address Resolution Protocol), responsible for discovering the Internet address of a host on a LAN; and ICMP (Internet Control Message Protocol), responsible for communicating problems with transmission to devices that need to know about these p ...
... responsible for locating a host on a LAN; RARP (Reverse Address Resolution Protocol), responsible for discovering the Internet address of a host on a LAN; and ICMP (Internet Control Message Protocol), responsible for communicating problems with transmission to devices that need to know about these p ...
Standardization areas for securing Ad hoc networks
... of routing protocol but only try to discover the information over the link. Defending against such attacks is difficult but nevertheless routing information can reveal relationships between nodes or disclose their IP addresses. If a route to a particular node is requested more often than to other no ...
... of routing protocol but only try to discover the information over the link. Defending against such attacks is difficult but nevertheless routing information can reveal relationships between nodes or disclose their IP addresses. If a route to a particular node is requested more often than to other no ...
LinkStar® Pro System
... quality of service (QoS), security, data acceleration, and compression in one single platform. The system ensures for your IP applications to seamlessly integrate via satellite by using industry standards in our network designs. With the constant change in markets and customer requirements, we under ...
... quality of service (QoS), security, data acceleration, and compression in one single platform. The system ensures for your IP applications to seamlessly integrate via satellite by using industry standards in our network designs. With the constant change in markets and customer requirements, we under ...
Cutting Edge VoIP Security Issues Color
... anti-spyware, are ubiquitously deployed Average losses due to security breaches are up, but down significantly from 2001 and 2002 (*) The number of incidents is down (*) Incidents are being reported at a greater rate (*) ...
... anti-spyware, are ubiquitously deployed Average losses due to security breaches are up, but down significantly from 2001 and 2002 (*) The number of incidents is down (*) Incidents are being reported at a greater rate (*) ...
Mainline How Secure Are You K12 Security Preseo Rev 1
... Is designed to provide a variety of solutions to enhance clients’ existing security posture, help prevent viruses, and spam, and control unwanted content in e-mail. ...
... Is designed to provide a variety of solutions to enhance clients’ existing security posture, help prevent viruses, and spam, and control unwanted content in e-mail. ...
WL-5460AP v2
... Access Point. The Wireless Access Point is equipped with two 10/100 M Auto-sensing Ethernet ports for connecting to LAN and also for cascading to next Wireless Access Point. AirLive WL-5460AP provides 64/128bit WEP encryption, WPA and IEEE802.1x which ensures a high level of security to protect user ...
... Access Point. The Wireless Access Point is equipped with two 10/100 M Auto-sensing Ethernet ports for connecting to LAN and also for cascading to next Wireless Access Point. AirLive WL-5460AP provides 64/128bit WEP encryption, WPA and IEEE802.1x which ensures a high level of security to protect user ...
PowerPoint Lesson 23 - ICT-IAT
... Most networks have a server that manages the network resources. Most networks have multiple clients, which are computers that access the server. An endpoint of a network connection, such as a computer terminal, server, or printer, is called a ...
... Most networks have a server that manages the network resources. Most networks have multiple clients, which are computers that access the server. An endpoint of a network connection, such as a computer terminal, server, or printer, is called a ...
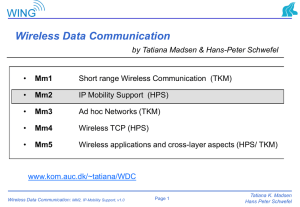
Network Security: Internet Mobility
... Could a SIP INVITE specify a false destination for a data stream? How could this be prevented? Design a more efficient binding-update protocol for Mobile IPv6 assuming a global PKI is available How could the return-routability test for the care-of address (CoA RR) be optimized if the mobile is openi ...
... Could a SIP INVITE specify a false destination for a data stream? How could this be prevented? Design a more efficient binding-update protocol for Mobile IPv6 assuming a global PKI is available How could the return-routability test for the care-of address (CoA RR) be optimized if the mobile is openi ...
Guide to Firewalls and Network Security with Intrusion Detection and
... Basis of digital certificates and signatures Enable holders of digital certificates to encrypt communications (using their private key) or decrypt communications (using sender’s public key) ...
... Basis of digital certificates and signatures Enable holders of digital certificates to encrypt communications (using their private key) or decrypt communications (using sender’s public key) ...
Course Overview - Cyber Security Lab
... improving revenue growth than spending time and money on better techniques to identify and remove vulnerabilities. More people are using computers without knowing well how to protect their computers. Even protocols used to manage your network can be a source of vulnerability themselves. All too ofte ...
... improving revenue growth than spending time and money on better techniques to identify and remove vulnerabilities. More people are using computers without knowing well how to protect their computers. Even protocols used to manage your network can be a source of vulnerability themselves. All too ofte ...
Aalborg Universitet Ramjee
... A WSN consists of small sensor nodes, each one equipped with limited battery, a microprocessor, a small amount of memory and a transducer. WSNs are versatile networks with a very wide domain of applications and their resource-constrained nature is an important research challenge. Like all other netw ...
... A WSN consists of small sensor nodes, each one equipped with limited battery, a microprocessor, a small amount of memory and a transducer. WSNs are versatile networks with a very wide domain of applications and their resource-constrained nature is an important research challenge. Like all other netw ...
07-Servers - dolinski.co.uk | home
... Help you understand different types of servers commonly found on a network including: ...
... Help you understand different types of servers commonly found on a network including: ...
OPERATING-SYSTEM STRUCTURES
... The monitor will assess which packets it needs to copy The monitor will request that all the computers send it a copy of the packets received All the packets that arrive in the network will be sent to the monitor That the network card will make a copy of every packet that it receives regardless of t ...
... The monitor will assess which packets it needs to copy The monitor will request that all the computers send it a copy of the packets received All the packets that arrive in the network will be sent to the monitor That the network card will make a copy of every packet that it receives regardless of t ...
Document
... Using Passwords • Strong passwords: – Sufficient length – Variety of characters – Upper and lowercase letters – Numbers – Special characters Computing Concepts – Part 2 ...
... Using Passwords • Strong passwords: – Sufficient length – Variety of characters – Upper and lowercase letters – Numbers – Special characters Computing Concepts – Part 2 ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.