A Preparing And Networking Of Virtual Network - Eagle
... vulnerabilities of desktop Operating System will help in the successful completion of this project. Section 1 Port Scanning: Port scanning is one of the most popular techniques used by hackers to find loop holes in the services they can use to attack. All of the computer machines that are connected ...
... vulnerabilities of desktop Operating System will help in the successful completion of this project. Section 1 Port Scanning: Port scanning is one of the most popular techniques used by hackers to find loop holes in the services they can use to attack. All of the computer machines that are connected ...
ppt 2
... • Security problems for embedded systems often make them counterproductive • Security very important in many embedded systems ...
... • Security problems for embedded systems often make them counterproductive • Security very important in many embedded systems ...
DCE - WordPress.com
... and hardware dependencies. It can automatically handle data type conversions between the client and the server without considering whether they run on the same or different architecture, or have same or different byte ordering. ...
... and hardware dependencies. It can automatically handle data type conversions between the client and the server without considering whether they run on the same or different architecture, or have same or different byte ordering. ...
“To Filter or to Authorize: Network
... solutions in all types of DoS attacks. Neither solution, filter or capability, has shown a definitive edge over the other. The best solution maybe a hybrid design. ...
... solutions in all types of DoS attacks. Neither solution, filter or capability, has shown a definitive edge over the other. The best solution maybe a hybrid design. ...
Defense in Depth / Firewalls Presentation
... system administration. Demilitarized zone. Security is low, since not protected by firewall. Locate webservers and other services there that generate potentially unsafe traffic. ...
... system administration. Demilitarized zone. Security is low, since not protected by firewall. Locate webservers and other services there that generate potentially unsafe traffic. ...
IEEE Paper Template in A4 (V1)
... However, ZigBee and 6LoWPAN are simply networklayer protocols which connect nodes together. With rapidly growing number of sensors, how to efficiently manage devices in WSN has become an important topics which receives a lot of attention in recent year. Currently there is still no universal network ...
... However, ZigBee and 6LoWPAN are simply networklayer protocols which connect nodes together. With rapidly growing number of sensors, how to efficiently manage devices in WSN has become an important topics which receives a lot of attention in recent year. Currently there is still no universal network ...
Concerns in networking
... • Downloading of executables that run on the fly • Problems – Convenient use may require redesign of web systems in any case – Travel-through time can be difficult to hide – Proxy? ...
... • Downloading of executables that run on the fly • Problems – Convenient use may require redesign of web systems in any case – Travel-through time can be difficult to hide – Proxy? ...
Defense in Depth / Firewalls Presentation
... system administration. Demilitarized zone. Security is low, since not protected by firewall. Locate webservers and other services there that generate potentially unsafe traffic. ...
... system administration. Demilitarized zone. Security is low, since not protected by firewall. Locate webservers and other services there that generate potentially unsafe traffic. ...
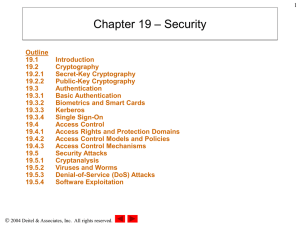
Chapter 19: Security
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
Whitepaper: Network Penetration Testing
... Discovery involves using the automated tools and manual techniques to identify the live hosts present in the network, determining the target system’s operating system through banner grabbing, presence of open ports, services running, & versions of the services, technology information, protocols and ...
... Discovery involves using the automated tools and manual techniques to identify the live hosts present in the network, determining the target system’s operating system through banner grabbing, presence of open ports, services running, & versions of the services, technology information, protocols and ...
Chapter 19: Security
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
Chapter 19: Security - Murray State University
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
... – Can push the additional data into adjacent buffers, corrupting or overwriting existing data – A well-designed buffer overflow attack can replace executable code in an application’s stack to alter its behavior – May contain malicious code that will then be able to execute with the same access right ...
Firewalls
... • Treats packets as pieces of a connection – Maintains data about legitimate open connections that packets belong to – Keeps identity of ports being used for a connection – Traffic is allowed to pass until connection is closed or ...
... • Treats packets as pieces of a connection – Maintains data about legitimate open connections that packets belong to – Keeps identity of ports being used for a connection – Traffic is allowed to pass until connection is closed or ...
HotView ControllerTM
... cameras, Wi-Fi access points, RFID readers, and laptop computers maintain network connectivity while traveling at high speeds across multiple HotPort mesh networks and IP domains. This enables a variety of exciting new applications not possible with static Ethernet networks. • Continuous video secur ...
... cameras, Wi-Fi access points, RFID readers, and laptop computers maintain network connectivity while traveling at high speeds across multiple HotPort mesh networks and IP domains. This enables a variety of exciting new applications not possible with static Ethernet networks. • Continuous video secur ...
Windows 7 and Windows Server 2008 R2 Networking
... Because of these concerns, many users avoid connecting to a VPN. Instead, they use technologies such as Microsoft Office Outlook® Web Access (OWA) to connect to internal resources. With OWA, users can retrieve internal e-mail without establishing a VPN connection. However, if a user tries to open a ...
... Because of these concerns, many users avoid connecting to a VPN. Instead, they use technologies such as Microsoft Office Outlook® Web Access (OWA) to connect to internal resources. With OWA, users can retrieve internal e-mail without establishing a VPN connection. However, if a user tries to open a ...
IF3614251429
... Tor is a form of Anonymzing networks comprised of virtual tunnels that allows people and groups to improve their privacy and security on the Internet. Individuals use Tor to keep websites from tracking them. Anonymzing networks provide users with anonymous browsing capabilities over the web using a ...
... Tor is a form of Anonymzing networks comprised of virtual tunnels that allows people and groups to improve their privacy and security on the Internet. Individuals use Tor to keep websites from tracking them. Anonymzing networks provide users with anonymous browsing capabilities over the web using a ...
Unified Services Routers - D-Link
... Wi-Fi Protected Access – Personal (WPA-PSK) Wi-Fi Protected Access – Enterprise (WPA-EAP) Wi-Fi Protected Access version 2 – Personal (WPA-PSK) Wi-Fi Protected Access version 2 – Enterprise (WPA-EAP) ...
... Wi-Fi Protected Access – Personal (WPA-PSK) Wi-Fi Protected Access – Enterprise (WPA-EAP) Wi-Fi Protected Access version 2 – Personal (WPA-PSK) Wi-Fi Protected Access version 2 – Enterprise (WPA-EAP) ...
network_admin_data
... FireFox and all other Mozilla-based products are generally more secure than IE Reasons: It is not integrated with Windows, which helps prevent viruses and hackers from causing damage if they somehow manage to compromise FireFox. There is no support for VBScript and ActiveX, two technologies which ar ...
... FireFox and all other Mozilla-based products are generally more secure than IE Reasons: It is not integrated with Windows, which helps prevent viruses and hackers from causing damage if they somehow manage to compromise FireFox. There is no support for VBScript and ActiveX, two technologies which ar ...
zhang-slides
... on the one hand, packet filtering in hardware, immunity from ARP attacks in hardware, monitoring and transmitting with hardware acceleration are designed and implemented on the NetFPGA to protect the subnet from network attacks. On the other hand, AES and DES encryption modules in hardware, immunity ...
... on the one hand, packet filtering in hardware, immunity from ARP attacks in hardware, monitoring and transmitting with hardware acceleration are designed and implemented on the NetFPGA to protect the subnet from network attacks. On the other hand, AES and DES encryption modules in hardware, immunity ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.