slides
... Should drop packets before the bottleneck, i.e., at ISP But ISPs are not willing to deploy complex filters for each client ISPs have no strong incentive; they charge clients for traffic Big companies defend themselves by using very high bandwidth access links ...
... Should drop packets before the bottleneck, i.e., at ISP But ISPs are not willing to deploy complex filters for each client ISPs have no strong incentive; they charge clients for traffic Big companies defend themselves by using very high bandwidth access links ...
AR530 Industrial Switching Router Datasheet
... Compared with enterprise routers, industrial routers are more applicable to harsh industrial environments because their components are more strictly selected. The AR530 uses a wider temperature range and a fan-less design and provides Ingress Protection 51 (IP51). With these key technologies, the AR ...
... Compared with enterprise routers, industrial routers are more applicable to harsh industrial environments because their components are more strictly selected. The AR530 uses a wider temperature range and a fan-less design and provides Ingress Protection 51 (IP51). With these key technologies, the AR ...
IP spoofing
... spoofed server, which cannot respond as it is already DoS’d. Queue’s quickly fill, as each connection request will have to go through a process of sending several SYN ACKs before it times out ...
... spoofed server, which cannot respond as it is already DoS’d. Queue’s quickly fill, as each connection request will have to go through a process of sending several SYN ACKs before it times out ...
Remote Control - Windows IT Pro
... its own set of requirements. Although a particular product might not support dial-up or dial-up with dial-back support, you might be able to run the software through a RAS connection. You also need to examine the types of systems you plan to connect to. If you’re running in a heterogeneous environme ...
... its own set of requirements. Although a particular product might not support dial-up or dial-up with dial-back support, you might be able to run the software through a RAS connection. You also need to examine the types of systems you plan to connect to. If you’re running in a heterogeneous environme ...
Blueprint For Security Chapter 6
... Can provide network administrator with valuable information for diagnosing and resolving networking issues In the wrong hands, a sniffer can be used to eavesdrop on network traffic To use packet sniffer legally, administrator must be on network that organization owns, be under direct authoriza ...
... Can provide network administrator with valuable information for diagnosing and resolving networking issues In the wrong hands, a sniffer can be used to eavesdrop on network traffic To use packet sniffer legally, administrator must be on network that organization owns, be under direct authoriza ...
chap07.ppt
... Can provide network administrator with valuable information for diagnosing and resolving networking issues In the wrong hands, a sniffer can be used to eavesdrop on network traffic To use packet sniffer legally, administrator must be on network that organization owns, be under direct authoriza ...
... Can provide network administrator with valuable information for diagnosing and resolving networking issues In the wrong hands, a sniffer can be used to eavesdrop on network traffic To use packet sniffer legally, administrator must be on network that organization owns, be under direct authoriza ...
Dynamic Time-domain Duplexing for Self
... each RN subtree with the initial X. This tests the case where the current configuration is optimal for links adjacent to the root but possibly not for subtrees rooted at a lower level. We then reschedule a UL subframe in the DL (i.e. xnew = +1) at the BS by calling Realloc in line 13. We naturally s ...
... each RN subtree with the initial X. This tests the case where the current configuration is optimal for links adjacent to the root but possibly not for subtrees rooted at a lower level. We then reschedule a UL subframe in the DL (i.e. xnew = +1) at the BS by calling Realloc in line 13. We naturally s ...
Security and Availability of Client Data
... local power interruption. Notifications are monitored by our 24x7 Network Operations Center, who will escalate to the appropriate on-call staff or management until the issue is resolved. Additionally, Adobe employs multiple independent monitoring services to provide several layers of monitoring redu ...
... local power interruption. Notifications are monitored by our 24x7 Network Operations Center, who will escalate to the appropriate on-call staff or management until the issue is resolved. Additionally, Adobe employs multiple independent monitoring services to provide several layers of monitoring redu ...
Security Criteria for Service Delivery Network
... parties to a transaction. Consists of identity management (establishing who you are) and logon management (confirming who you are). For this document, authentication is used in the commonly understood sense of logging on with a username and authentication key (e.g., password). ...
... parties to a transaction. Consists of identity management (establishing who you are) and logon management (confirming who you are). For this document, authentication is used in the commonly understood sense of logging on with a username and authentication key (e.g., password). ...
Top-Down Network Design
... The availability and security of these services are crucial to the success of a business. Managing and securing numerous distributed servers at various locations within a business network is difficult. Recommended practice centralised servers in server farms. Server farms are typically located in co ...
... The availability and security of these services are crucial to the success of a business. Managing and securing numerous distributed servers at various locations within a business network is difficult. Recommended practice centralised servers in server farms. Server farms are typically located in co ...
Notes as Powerpoint Presentation
... – Local Network uses a range of Private IP Addresses • ISP allocates one Global IP Address for each WAN connection • NAT used to Translate Address from Local to Global ...
... – Local Network uses a range of Private IP Addresses • ISP allocates one Global IP Address for each WAN connection • NAT used to Translate Address from Local to Global ...
Blueprint For Security Chapter 6
... and assist the administrator in analyzing the rules Administrators who feel wary of using the same tools that attackers use should remember: It is intent of user that will dictate how information gathered will be used In order to defend a computer or network well, it is necessary to understand ...
... and assist the administrator in analyzing the rules Administrators who feel wary of using the same tools that attackers use should remember: It is intent of user that will dictate how information gathered will be used In order to defend a computer or network well, it is necessary to understand ...
Document
... A contracted security solution that can reach into hosts Providing remote workers with secure access to their employer's internal network Other security and management services are sometimes included as part of the package ...
... A contracted security solution that can reach into hosts Providing remote workers with secure access to their employer's internal network Other security and management services are sometimes included as part of the package ...
6 - Kuroski
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
Performance Analysis of Topological Variation in Personal Area
... Modeler, Throughput, Load, Delay, No. of Hop I. Introduction ZigBee is based on the IEEE 802.15.4 standard along with other protocols like Wi-Fi and Bluetooth. ZigBee is a specification for a suite of high level communication protocols based on an IEEE 802 standard for personal area networks. The Zi ...
... Modeler, Throughput, Load, Delay, No. of Hop I. Introduction ZigBee is based on the IEEE 802.15.4 standard along with other protocols like Wi-Fi and Bluetooth. ZigBee is a specification for a suite of high level communication protocols based on an IEEE 802 standard for personal area networks. The Zi ...
Chapter4b
... Mobility between different networks • Done at the network layer via new protocols such as Mobile IP ...
... Mobility between different networks • Done at the network layer via new protocols such as Mobile IP ...
Firewalls
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
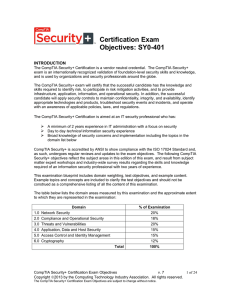
CompTIA Security (SY0-401)
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
... Risks associated with Cloud Computing and Virtualization Recovery time objective and recovery point objective 2.2 Summarize the security implications of integrating systems and data with third ...
Firewall and VPNs - Ohio State Computer Science and Engineering
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
DS35676681
... networks. The multi hop support makes communication between nodes outside the direct range of each other possible. 1.2 Some Issues in MANET Network An ad hoc network is a dynamic type of network with similarities and great differences to its parent fixed communication network. The properties of an a ...
... networks. The multi hop support makes communication between nodes outside the direct range of each other possible. 1.2 Some Issues in MANET Network An ad hoc network is a dynamic type of network with similarities and great differences to its parent fixed communication network. The properties of an a ...
Citrix Technical Overview
... Protecting back-end web applications and data • Better Data Protection and Better User Experience • Real-time protection for application and application logic • Accelerated Secure access and delivery of data ...
... Protecting back-end web applications and data • Better Data Protection and Better User Experience • Real-time protection for application and application logic • Accelerated Secure access and delivery of data ...
6 - Computer Science and Engineering
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
... Circuit Gateways Circuit gateway firewall operates at transport layer Like filtering firewalls, do not usually look at data traffic flowing between two networks, but prevent direct connections between one network and another Accomplished by creating tunnels connecting specific processes or sy ...
Slide 1
... – almost impossible to find a mobile system, DNS updates take long time – TCP connections break, security problems ...
... – almost impossible to find a mobile system, DNS updates take long time – TCP connections break, security problems ...
IP Addresses
... – Well known ports range from 0 to 1023. – Registered ports range from 1024 to 49151. – Dynamic or private ports range from 49152 to 65535. – For a complete listing, go to www.iana.org/assignments/port-numbers ...
... – Well known ports range from 0 to 1023. – Registered ports range from 1024 to 49151. – Dynamic or private ports range from 49152 to 65535. – For a complete listing, go to www.iana.org/assignments/port-numbers ...
Wireless security
.jpg?width=300)
Wireless security is the prevention of unauthorized access or damage to computers using wireless networks. The most common types of wireless security are Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA). WEP is a notoriously weak security standard. The password it uses can often be cracked in a few minutes with a basic laptop computer and widely available software tools. WEP is an old IEEE 802.11 standard from 1999, which was outdated in 2003 by WPA, or Wi-Fi Protected Access. WPA was a quick alternative to improve security over WEP. The current standard is WPA2; some hardware cannot support WPA2 without firmware upgrade or replacement. WPA2 uses an encryption device that encrypts the network with a 256-bit key; the longer key length improves security over WEP.Many laptop computers have wireless cards pre-installed. The ability to enter a network while mobile has great benefits. However, wireless networking is prone to some security issues. Hackers have found wireless networks relatively easy to break into, and even use wireless technology to hack into wired networks. As a result, it is very important that enterprises define effective wireless security policies that guard against unauthorized access to important resources. Wireless Intrusion Prevention Systems (WIPS) or Wireless Intrusion Detection Systems (WIDS) are commonly used to enforce wireless security policies.The risks to users of wireless technology have increased as the service has become more popular. There were relatively few dangers when wireless technology was first introduced. Hackers had not yet had time to latch on to the new technology, and wireless networks were not commonly found in the work place. However, there are many security risks associated with the current wireless protocols and encryption methods, and in the carelessness and ignorance that exists at the user and corporate IT level. Hacking methods have become much more sophisticated and innovative with wireless access. Hacking has also become much easier and more accessible with easy-to-use Windows- or Linux-based tools being made available on the web at no charge.Some organizations that have no wireless access points installed do not feel that they need to address wireless security concerns. In-Stat MDR and META Group have estimated that 95% of all corporate laptop computers that were planned to be purchased in 2005 were equipped with wireless cards. Issues can arise in a supposedly non-wireless organization when a wireless laptop is plugged into the corporate network. A hacker could sit out in the parking lot and gather information from it through laptops and/or other devices, or even break in through this wireless card–equipped laptop and gain access to the wired network.